Latest News
July 05, 2017 | Research
The IT Security Status at a Glance: The AV-TEST Security Report 2016/2017
No cause for concern due to the declining malware statistics? Far off target. Because the formula of the newly-developed attack strategies in 2016 is based on: Quality, not quantity! Whether it be even more sophisticated ransomware such as WannaCry and, most recently, Petya as well as banking Trojans or targeted attacks on the practically unprotected Internet of Things: Cyber criminals are up to speed with technology – and in the field of IoT, even way ahead.
The AV-TEST Security Report provides information on these and other threats.
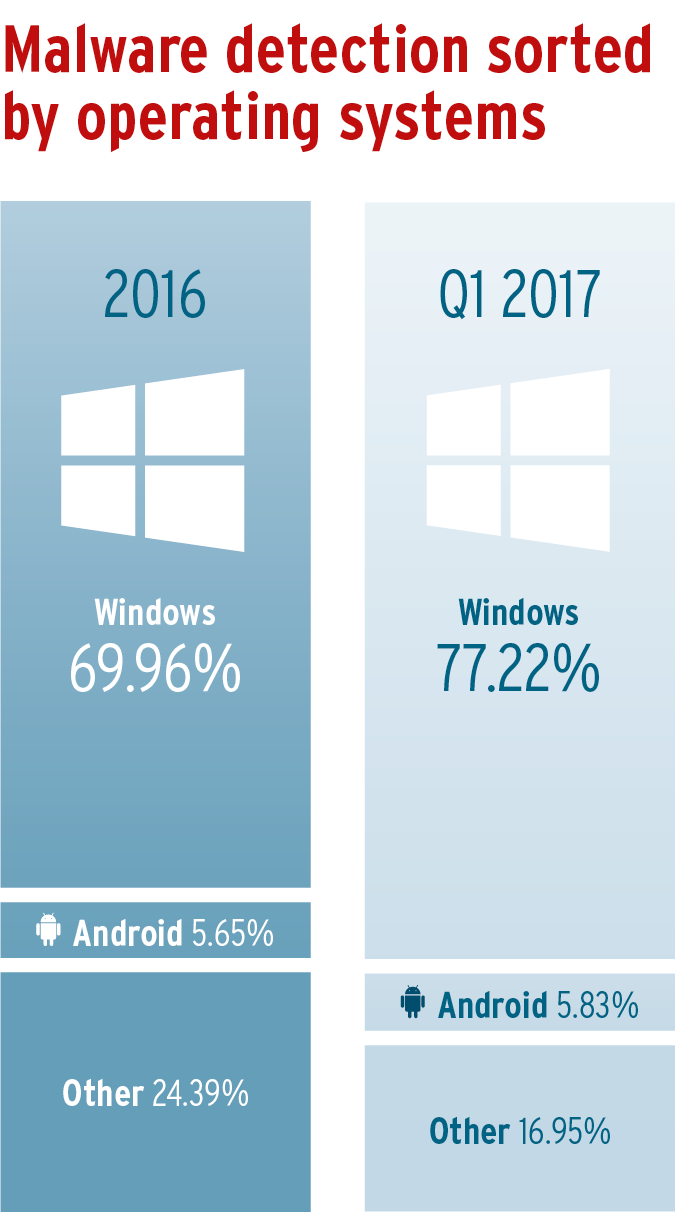
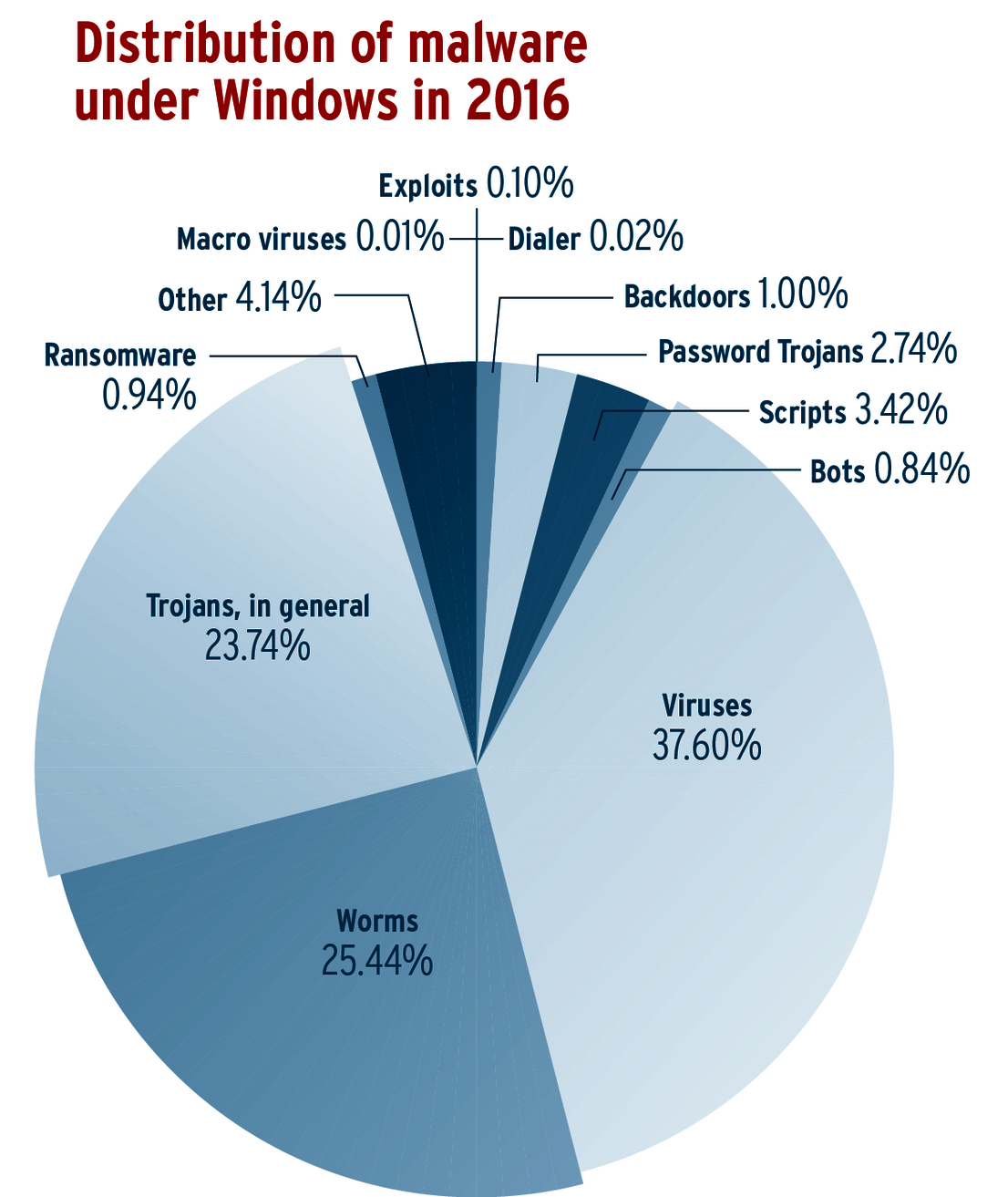
In 2016, the declining malware trend provided some relief, at least quantitatively. Thus, detection systems were required to seek out and defend against 14% fewer malware samples than in the previous year. The overall number of malware programs for all operating systems is nonetheless enormous and currently exceeds 640 million. In this, Windows remains the most widely attacked operating system. In the year 2016, seven out of ten newly programmed malware programs targeted the Microsoft platform.
Ransomware: High-tech attacks on Windows
There is no indication based on proliferation statistics that 2016 was the "year of ransomware". Comprising not even 1% of the overall share of malware for Windows, the blackmail Trojans appear at first glance to be a marginal phenomenon. The fact that this type of assessment is incorrect can be explained via the mode of action and damage created by this class of Trojans. A level of distribution comparable to traditional viruses is not required to reap the greatest possible profit. Ransomware involves "high-tech malware", which seeks its victims above all in a targeted business environment. For instance, emails infected with ransomware are sent out almost exclusively on weekdays, as proven by the measurement results of the AV-TEST systems.
However, ransomware is also suitable for mass infections. This was stunningly proven by the WannaCry attacks in May of this year with more than 230,000 infected Windows computers in over 150 countries. This case shows the level of development standards such malware has reached, which criminals lease as a service. Thus, WannaCry infected computers via zero-day exploits, which the US intelligence agency NSA previously used to eavesdrop on computers worldwide. While Microsoft promptly offered patches, they were often not installed. Moreover, large sections of the British healthcare system, including several hospitals, the Spanish provider Telefonica, as well as the German railway company, Deutsche Bahn, did not pursue any meaningful backup strategy. As a result, they turned out to be easy prey for WannaCry attacks. The fact that despite these attacks, even large corporations still hadn’t shored up their systems with the Microsoft patches, long since available, and thus fell prey to Petya through the same “Eternal Blue“ exploit, is baffling to security experts. What’s more, it raises fundamental questions concerning the IT security strategy of many companies.
Trojan roulette: Security you can’t always bank on!
Password and banking Trojans were also a topic of debate in 2016. Already in February, the Bangladesh Central Bank lost over $81 million through a malware attack. Also in February, a similar attack was launched against the New York Federal Reserve. AV-TEST systems pointed out relevant proliferation statistics of password and banking Trojans: In the first quarter of last year, there were extremely many samples of similar malicious codes active. Some of them were most certainly used for attacks on the SWIFT (Society of Worldwide Interbank Financial Telecommunication) banking network. Using special malware, criminals gained access to banking computers connected to the payment system. The Belgian service provider later confirmed the number of 3,000 financial institutions around that globe that had been subject to attacks. The Brussels company, however, declined to disclose which banks were involved and how high the financial losses were. At the end of April, SWIFT issued a relevant security update.
macOS: Cyber criminals in the development phase
Compared to the previous year, the malware sector for macOS is experiencing 370% percent growth. However, it is also important to keep an eye on the overall number of malware programs: Whereas in 2015 there were still a moderate 819 different malware threats targeting macOS, Apple users in 2016 already had to protect their devices from 3033 malware samples.
The growth began in December 2016. Prior to that, the number of malware threats was practically at the previous year's level. This means that since then, cyber criminals have been in the experimental phase, trying out which malware and how much time and effort are worthwhile for infecting the operating system from Cupertino. This assumption is also confirmed by the distribution of various malware samples and their development, as the new Security Report demonstrates.
Android: Attacks doubled
In examining the malware development from 2015 to 2016, one thing becomes clear – in addition to the doubling of the detected sample volume of over 4 million new malware programs: From the beginning of 2016, criminals pushed malware onto the market in waves. This indicates tests of new malware or new proliferation paths. The peaks of this trend in 2016 were in January, August and October. The largest spike, however, occurred mid-year in June. In that month, AV-TEST systems measured extreme activity and exactly 643,476 new malware programs for Android, representing the highest number since the Google operating system was published.
Indeed, at that time, Android offered criminals numerous vulnerabilities through which malware could be infiltrated. Accordingly, Google was forced to respond. The patch day in July exceeded all previous updates by far: With two brief successive security updates, Google fixed over 100 flaws, roughly one-third of the leaks were security-critical. With the largest Android patch up to now, Google did indeed close a multitude of known vulnerability gaps; for June 2016, however, the protection systems of AV-TEST revealed a total 9217 exploits for all Android versions overall, also an impressive peak number. Further information is available in the chapter "Android Security Status" in the new Security Report.
IoT Security Billions of devices without basic protection
Instead of paying attention to the security on the Web when developing Internet-based devices, the focus is on quick market penetration. Thus far, Internet security has frequently not been part of the product design, instead it is often perceived as an impediment of rapid go-to-market strategies. This is also due to the fact that more and more non-IT manufacturers without any understanding of online risks are producing devices connected to the Internet.
Toward the end of last year, the worldwide attacks by the Mirai botnet were surely an eye-opener. Detected in August 2016 for the first time by the detection systems of AV-TEST, attacks of the IoT malware in October already caused major online services in the United States and Europe to crash by flooding their servers with address queries. For the DDoS attacks, the bundled computing power of hundreds of thousands of captured routers, printers, webcams and video recorders were harnessed via a botnet. At the end of November, criminals with other variants of the same Linux malware unleashed devastating attacks against DSL routers of Telekom customers. 900,000 devices were taken down. In October, the Mirai code appeared freely available on the Internet. Since then, the AV-TEST systems have been investigating an increasing number of samples with spikes at the end of October, November and beginning of December.
Without wanting to spread fear unnecessarily: The attacks by the Mirai botnet were surely only the beginning and relatively easy to pinpoint. Yet virtually none of the IoT devices offered any effective protection. And that is why the devices attacked continue to be on the hit list of other IoT malware that existed long before Mirai. The AV-TEST Security Report reveals which systems they are and how long they have been known.
Download the complete report for free
Additional information and detailed metrics on the proliferation of malware and other malicious applications are provided in the comprehensive Security Report by the AV-TEST Institute. You can download the report here free of charge.
DOWNLOAD SECURITY REPORT 2016/17
Regular tests of smart home products and information on IoT devices with certified security can be found in our IoT Security Blog.
Would you like to know which protection program and which security app offers the best possible protection for your devices? AV-TEST offers you information on detection rates, usability and performance of all known security solutions, also free of charge. You can look up the results of the tests carried out monthly.
If you would like to regularly keep up to date on information from our institute concerning all aspects surrounding the topic of IT security, such as tests on smart home products, wearables, fitness trackers or health apps and parental control applications, you can receive prompt and current information via our monthly security newsletter.