Latest News
May 12, 2021 | More tests
New Lines of Defense: EPPs and EDRs Put to the Test Against APT and Ransomware Attacks
Security leaks, like the recently discovered Microsoft Exchange vulnerability, underscore the dangers facing companies, government agencies and critical infrastructure worldwide. It took only a few days following the news of the massive hack by Hafnium with DearCry for the first ransomware to be unleashed, exploiting the Exchange vulnerability. Following the completion of comprehensive tests, AV-TEST has now released the initial test report of EPP and EDR products, placing a special focus on their detection and threat prevention against APT attacks where ransomware is deployed. In the labs of the IT security institute, 6 endpoint protection platform and 3 endpoint detection & response solutions were put under the microscope.
APT & Ransomware – tactical sabotage attacks are rapidly increasing
Complex technical and targeted strategic cyberattacks are no longer a celestial event, but have rather become part of the everyday life of companies and public agencies. So the question is not if an APT attack will occur, but when. Accordingly, cyberattacks on companies, public agencies, and critical infrastructure, with Hafnium exploiting security leaks and the use of ransomware such as DearCry, already reached a dramatic high point last year. The lion's share of APT attacks identified and analyzed were aimed at espionage, targeting both confidential as well as financially exploitable information. At the same time, there was a rise in the number of APT attacks seeking to block IT infrastructure and to blackmail its owners, to damage or even to destroy data for tactical reasons. In the last quarter of 2020 alone, both government IT structures as well as the networks of important and system-relevant companies increasingly came into the crosshairs of digital acts of sabotage.
Thus, in November the renowned Center for Strategic and International Studies (CSIS) detected an attack on the electronics conglomerate Foxconn. In the course of a sophisticated ransomware attack, the hackers encrypted 1,200 servers, deleted 30 TB of backups, and took credit for making off with 100 GB of confidential corporate data. In September 2020, the US healthcare provider Universal Health Services, the French shipping company CMA CGM, the largest Pakistani energy utility, along with several government organizations in the Middle East, became the victims of targeted APT attacks deploying ransomware.
APT & Ransomware – encryption as a weapon
APT attacks deploying ransomware are not only aimed at blackmail and raking in as much ransom money as possible, but are also used for targeted tactical sabotage. Through strategic ransomware attacks, hackers not only encrypt data on target systems, in the worst case, they cut off the availability of vital system and network resources. The objective of attacks like these is to make stored data or complete systems temporarily or permanently inaccessible in order to achieve a financial or tactical advantage. This threat was confirmed by the assessment of companies, published in the latest Allianz Risk Barometer 2021: Named 41% of the time, the risk of business interruption ranks number one among the corporate threats most feared, followed by breakouts of pandemics (40%) and the fear of cyber incidents (40%).
These concerns are justified, as not only state-backed players such as the North Korean APT38 Group, or the APT41 attacks attributed to China, deployed the strategy of "Data Encrypted for Impact" (MITRE ID: T1486). In October 2020, the US government brought charges against six officers of the Russian GRU military intelligence agency due to potential involvement in the attacks on critical infrastructure in the Ukraine in the years 2015 and 2016, and also accused them of being behind the deployment of NotPetya ransomware in the year 2017. State-backed malware deployments ultimately led to cybercriminals' access to their variants in the form of ransomware such as Maze, NotPetya, REvil, and WannaCry. Since 2018, the Russian hacker unit Wizard Spider, by operating the ransomware Ryuk, has become notorious, staging ransomware attacks mostly targeting large corporations.
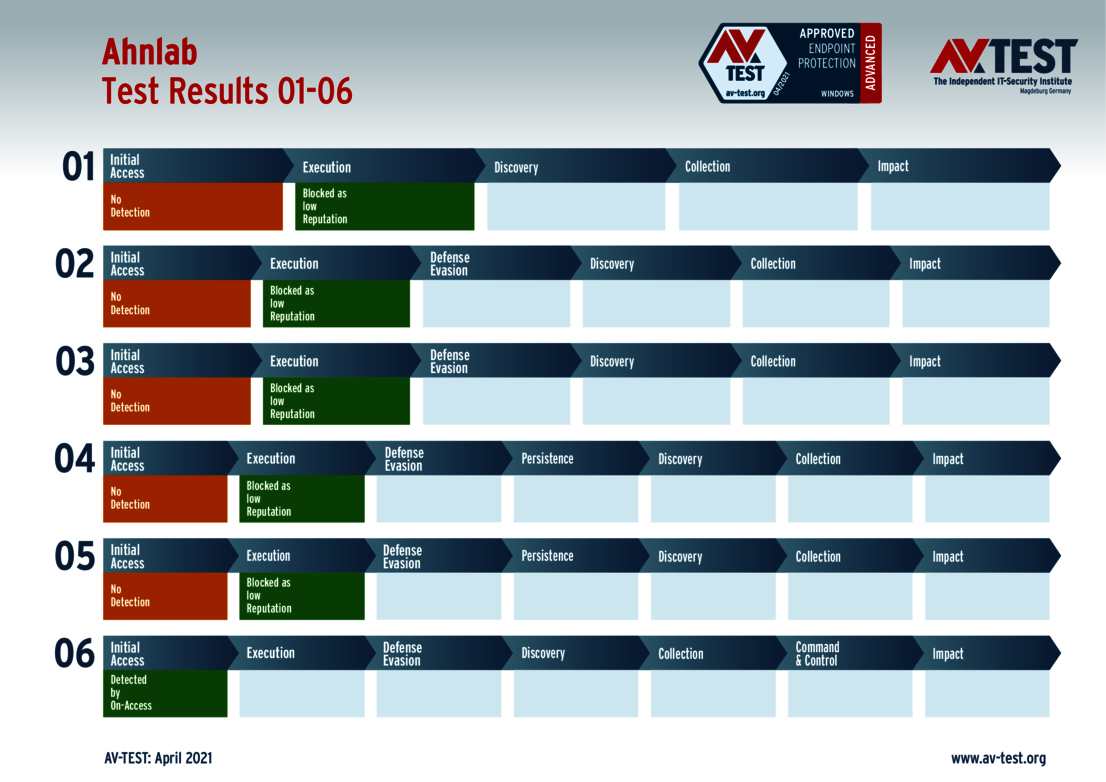
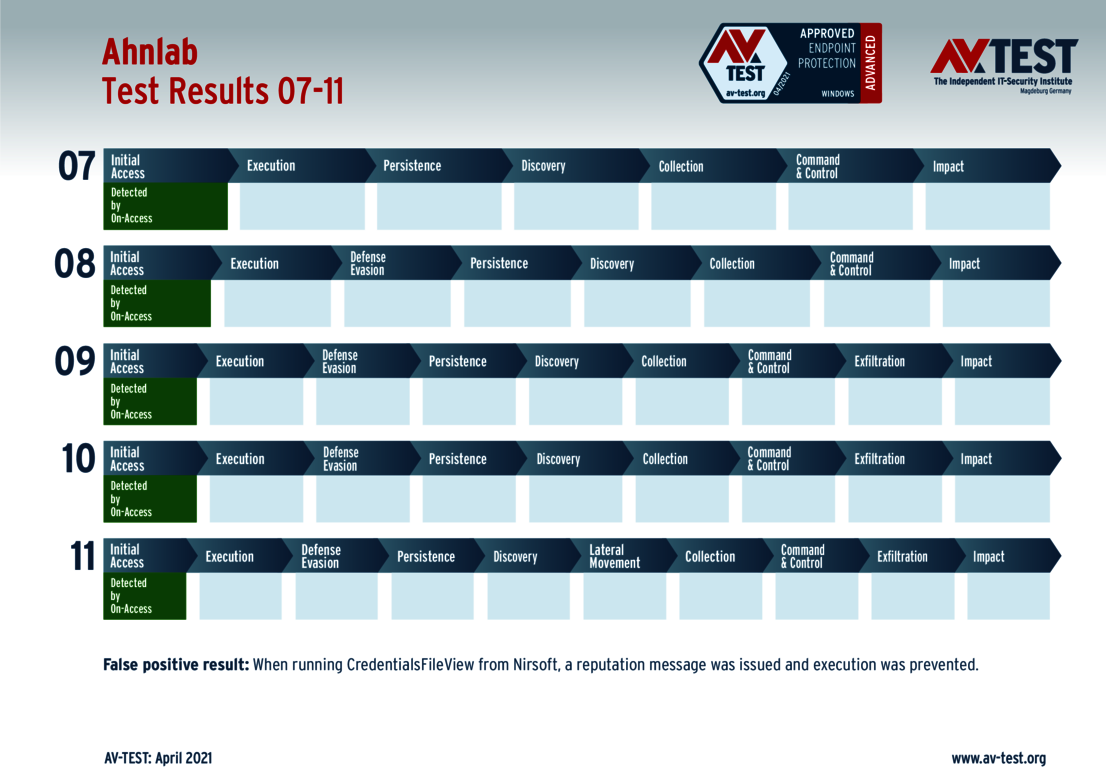
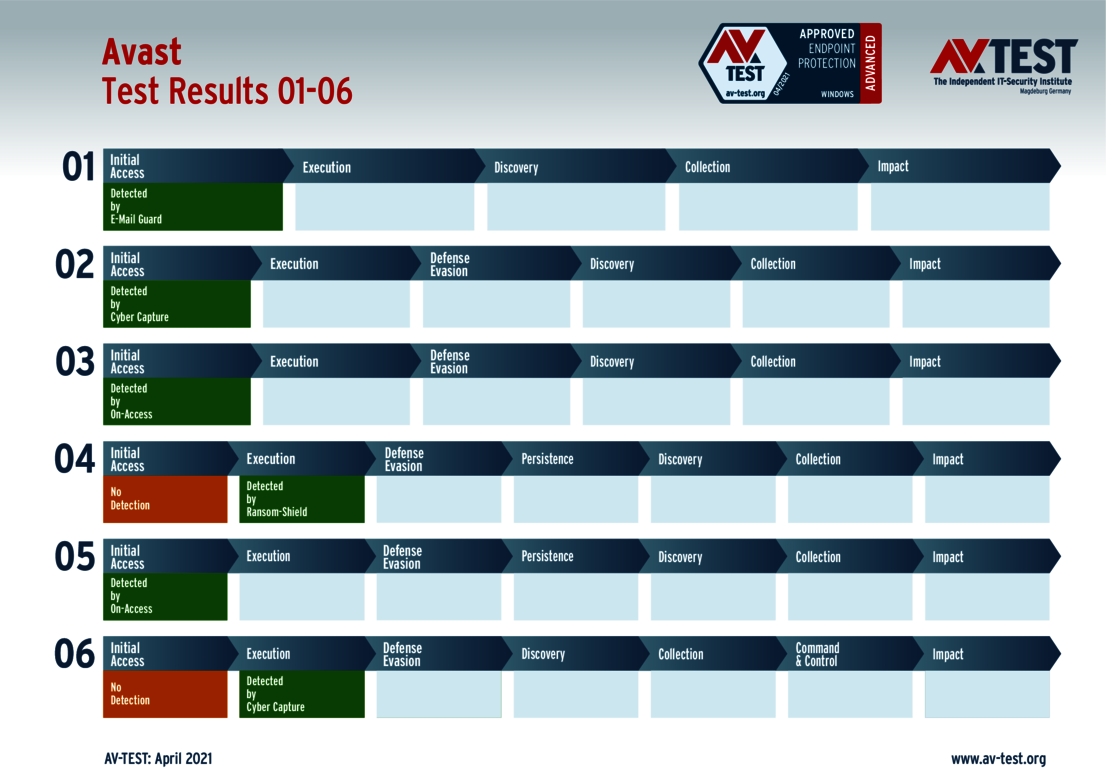
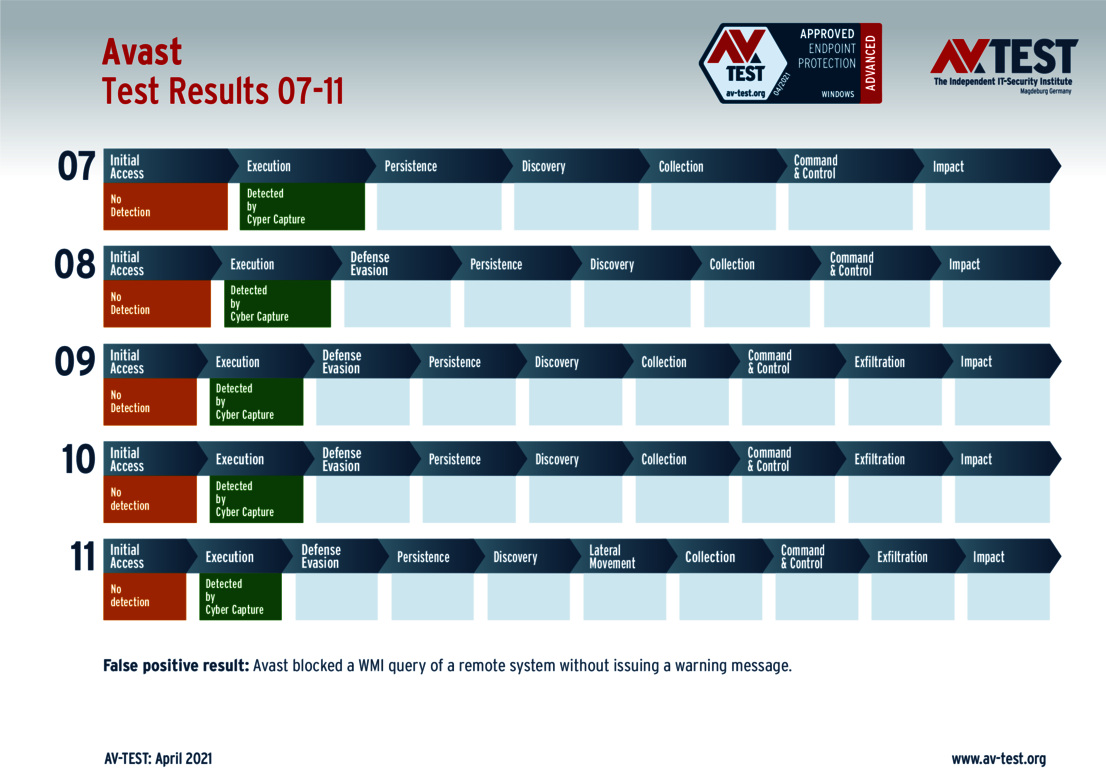
Advanced EEP & EDR tests: dedicated attack scenarios according to the MITRE ATT&CK Matrix
It is due to scenarios such as these that the AV-Test Institute, within the scope of the initial comprehensive test series, decided to test the detection and threat prevention of 6 EEP and 3 EDR products against APT attacks deploying ransomware using the "Data Encrypted for Impact" technique (MITRE ID: T1486). The Institute evaluated the EPP solutions from the manufacturers AhnLab, Avast, Avira, Bitdefender, G Data, and McAfee, as well as the EDR systems from Bitdefender, McAfee, and VMware. All 11 tests in the test series were conducted on the Windows 10 Professional (64 bit) operating system version typically found in corporate computing environments. The attack simulations were carried out based on the tactics and techniques of the MITRE ATT&CK Matrix for Enterprise.
One such APT attack simulation chosen in this test series begins with an email containing a spearphishing attachment (T1193); this attachment, infected with malware, is sent to a previously determined user account of the target system. By means of a prior social engineering campaign, it is ensured that the target person of interest will launch the attached file and activate the malware on the target system. The malicious e-mail attachment involves a standard archive format containing a file which, upon unzipping and opening, launches the actual attack code. In the attack simulation, the infected attachment, as is customary upon receipt of e-mails such as these, is saved by the user on their Windows 10 system and unzipped using standard file compression software. Afterwards, the user typically launches the file, thus executing the code contained in it (T1061 and T1204).
The malicious code launched with the file establishes an Internet connection and begins secretly downloading an executable file from the system of the attacker. The file automatically launches immediately after download, creating a registry key in the infected target system, thus gaining persistence (T1060). In order to elude detection and to defeat network filters, connectivity is established via a standard user application layer to a C2 server controlled by the attacker (T1071). In order to obfuscate the network traffic and to prevent parsing, an unusual port is used for online communication (T1065). Upon establishing the connection, the C2 server begins exfiltration over the C2 channel (T1020 and T1041), searching through the databases of the local system (T1083) and connected networks (T1016 and T1135). Subsequently, the attackers encrypt identified data and any available system and network resources of the target system (T1490, T1486 as well as T1491).
Multilevel detection in the advanced EPP & EDR test
The evaluation of the detection and threat prevention of the tested EPP and EDR solutions occurs in a three-phase model:
1. In the "attack simulation", the testers evaluate how well the EPP solutions are able to detect and stop APT attacks deploying various ransomware samples, and how well EDR solutions detect and report these attacks.
2. In the "sanity check", the evaluated EPP solutions, put through false-positive checks, are required to prove whether they are capable of distinguishing between normal user behavior and detected attack patterns, or whether they wrongly block normal operations. This phase evaluates whether the operability of the system is impaired, whereby the testers test from both the user and admin perspective, according to the following schemas:
a) User perspective
- Use of browsers (Edge and Chrome)
- Installation of software
- Use of Office documents with and without macros
- Use of Outlook (sending and receiving e-mails, checking, saving, and opening e-mail attachments)
- Access to Windows and Samba shares, internal/external FTP, use of cloud storage such as Google Drive
b) Admin perspective
- Enabling scripting (evaluating various languages such as PowerShell or VBS)
- Enabling changes to user rights
- Enabling changes to network configurations
3. In the "noise check", it is examined which normal operations (techniques), that can be exploited by attackers, can be carried out and are logged by the EDR solutions. Above all, the test uses techniques that are also deployed within the scope of the tested attacks (e.g. unzipping an archive with the help of the GUI).
The tests record how well EDR products consider the context in classifying certain operations according to the following pattern:
- Harmless operations are simply logged if no potentially malicious context is detected.
- Harmless operations are flagged as suspicious if a potentially malicious context is detected.
This approach also helps in the evaluation of the attack detection:
- If the type of detection is identical in the attack test and the noise check (making detection more difficult from an admin perspective).
- If different reports or types of detection are used (improving detection from an admin perspective).
Evaluation and findings in the advanced EPP and EDR test
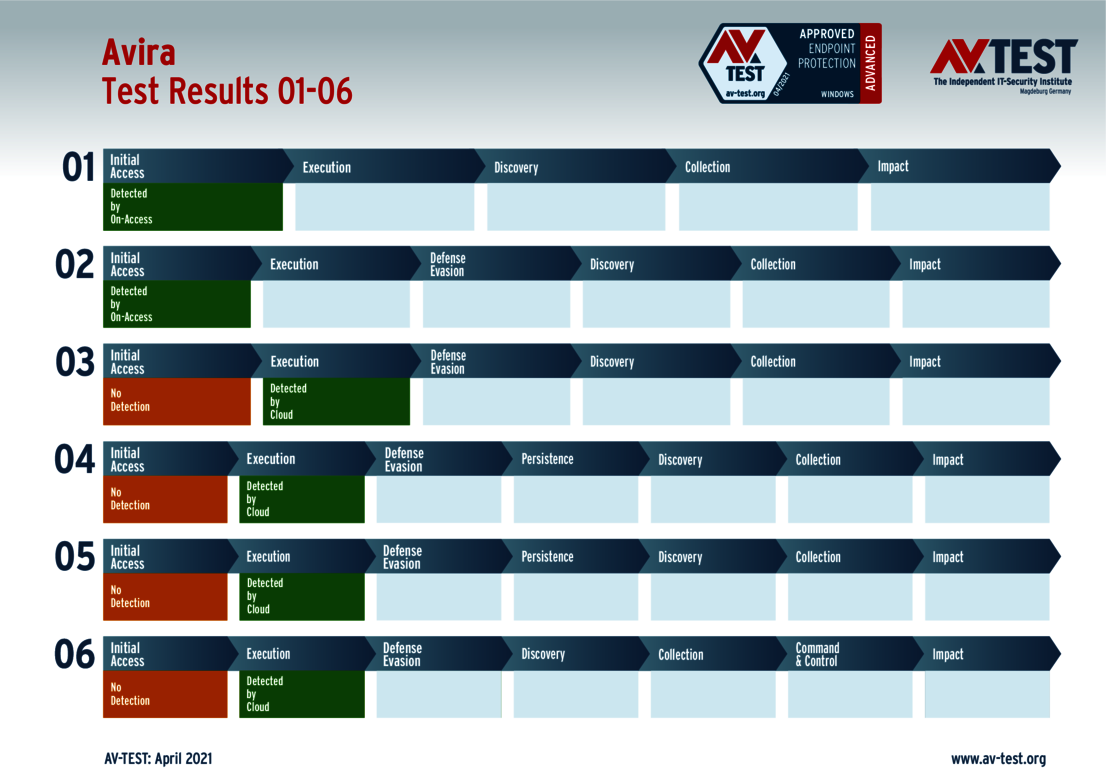
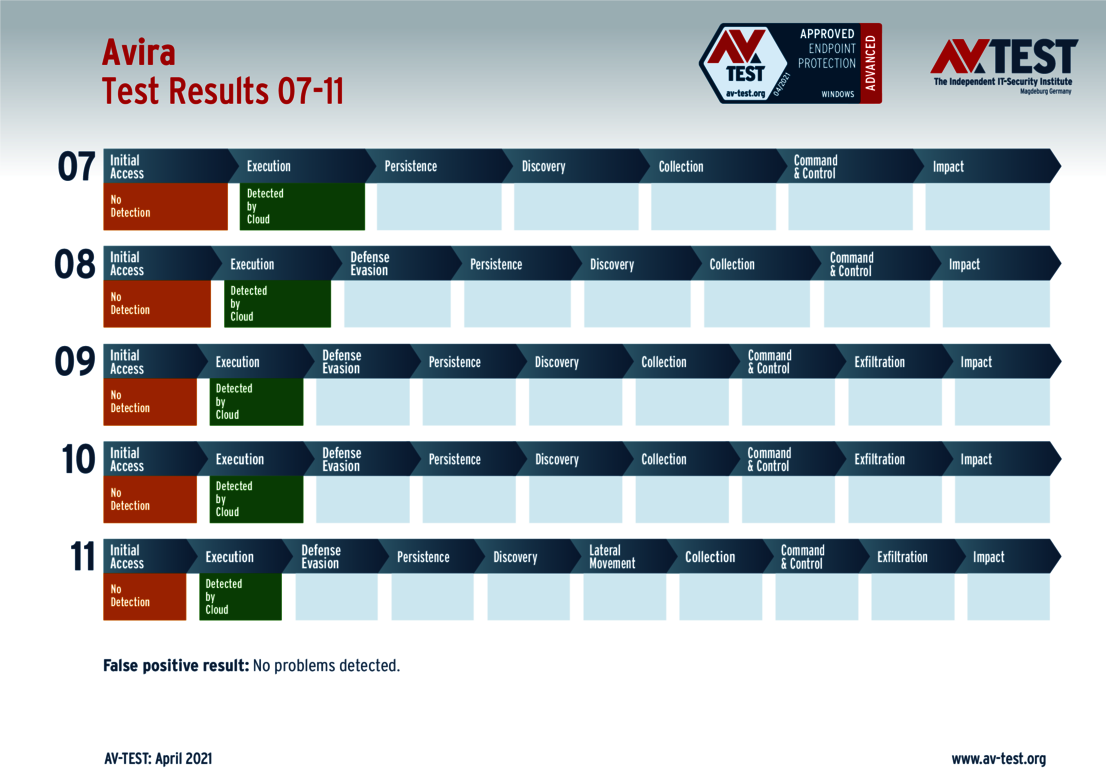
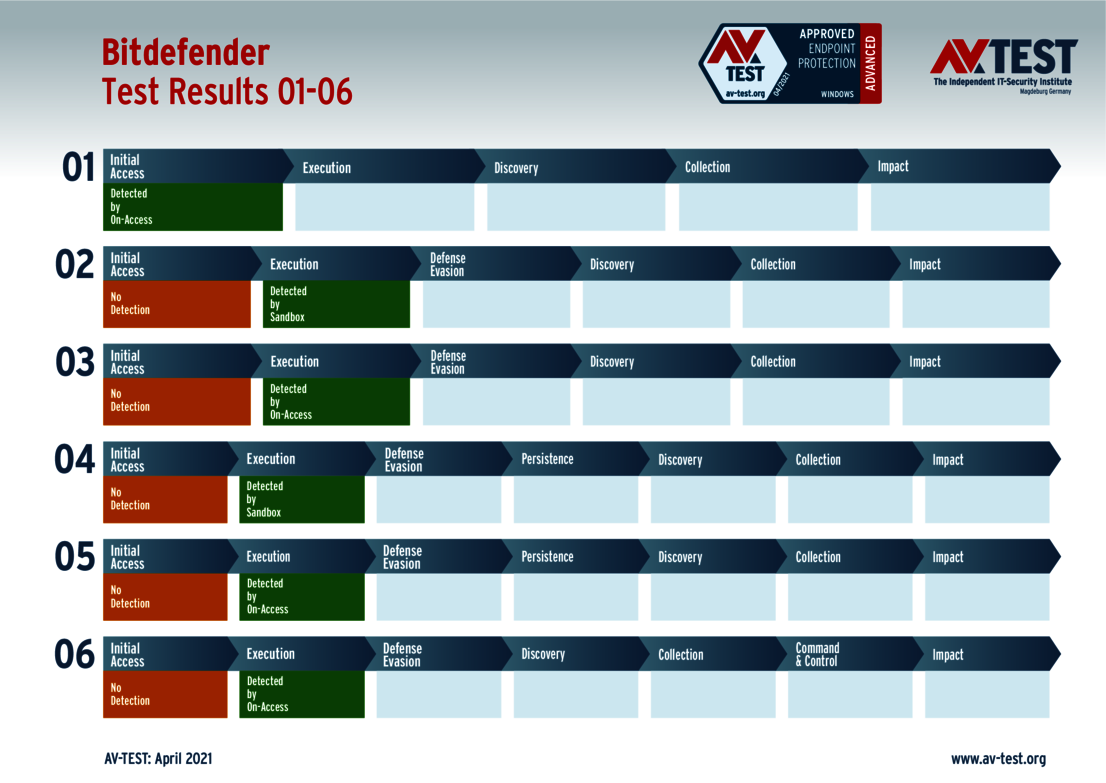
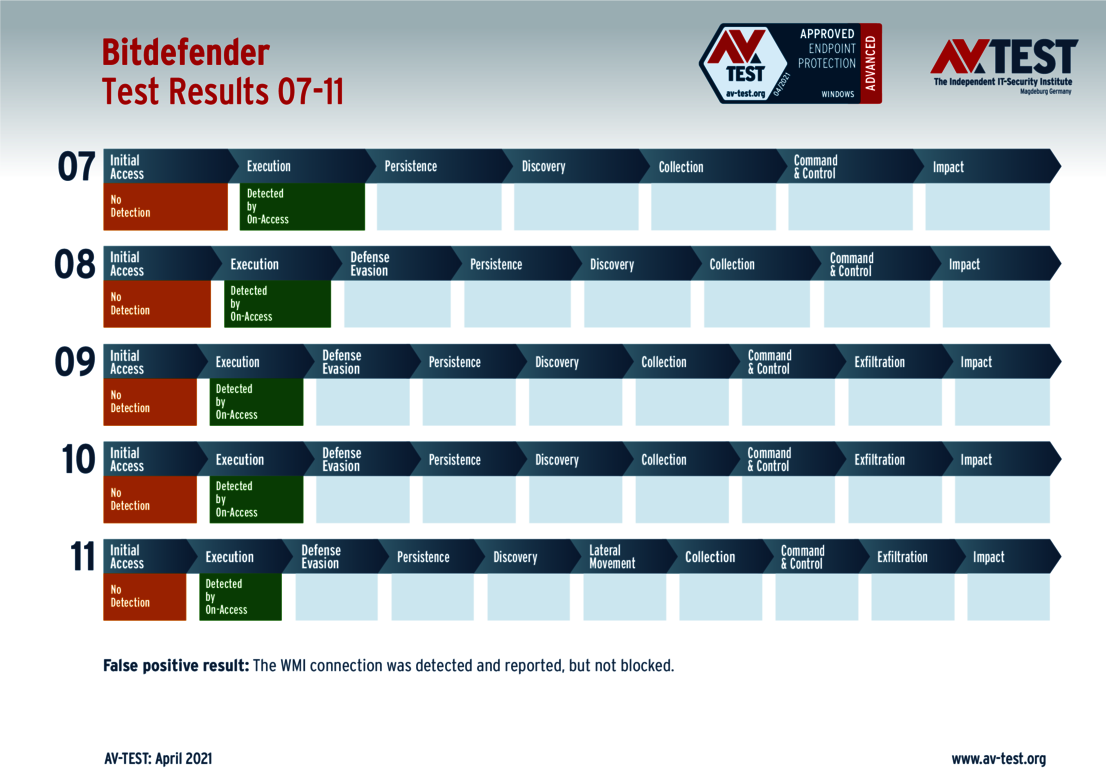
How well EPP and EDR solutions fared in the AV-TEST lab, which products reported and fended off the targeted APT attacks and thus were able to prevent encryption of the attacked test systems, are indicated in the following charts in connection with each of the solutions tested.
In order to successfully complete this test and to receive an AV-TEST certificate, EPP solutions were required to block 50% of the test attacks, and the EDR solutions had to detect and report 50 percent of the techniques used in the attacks. The evaluation of the test attacks was divided up into two segments according to the range of capabilities of the solutions evaluated.
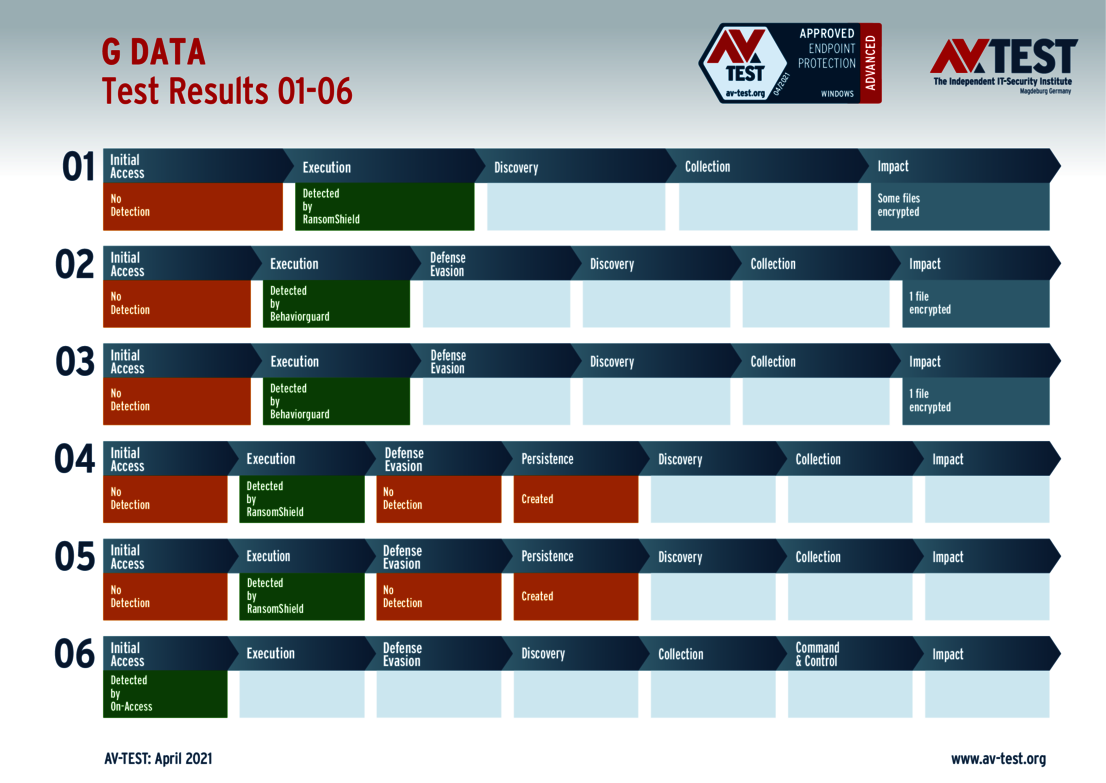
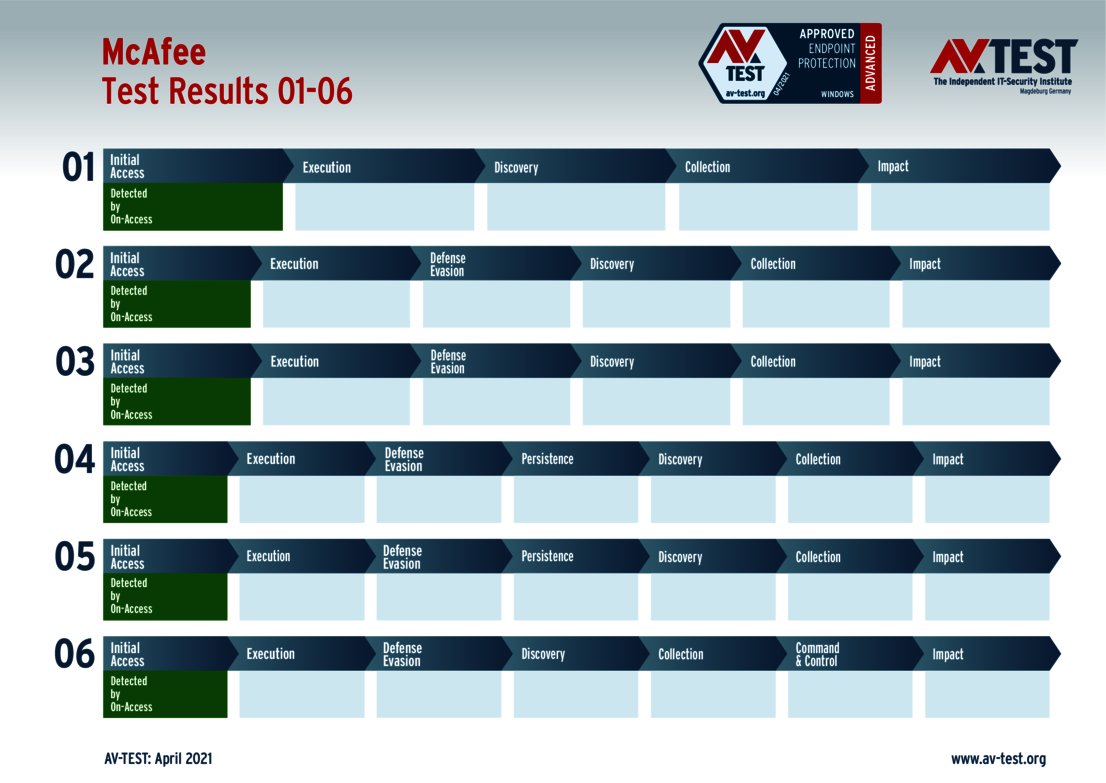
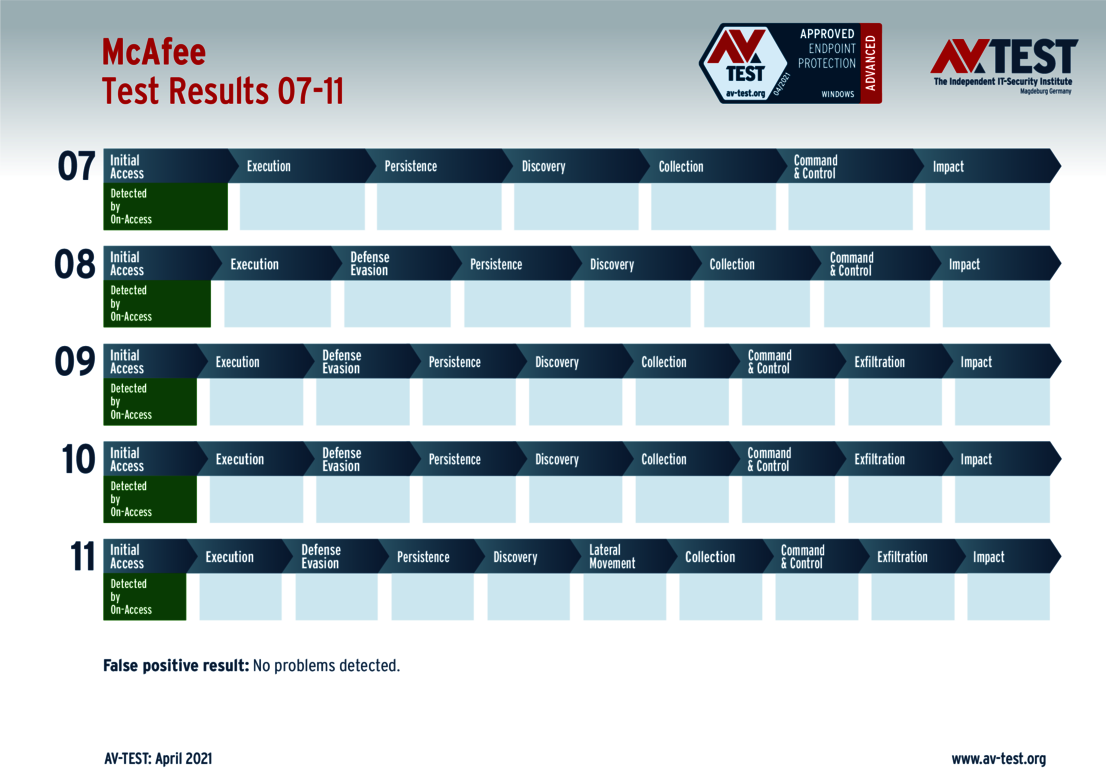
1. EPP evaluation: In which phase was the attack detected and blocked? What kind of damage occurred up to the time the attack was blocked? The charts highlighting the results on the individual attacks indicate how far each attack progressed and at which point it was blocked by the EPP solution. In addition, the respective charts show which module of the EPP solution detected and blocked the test attack, as well as what kind of damage occurred up to that point on the test systems.
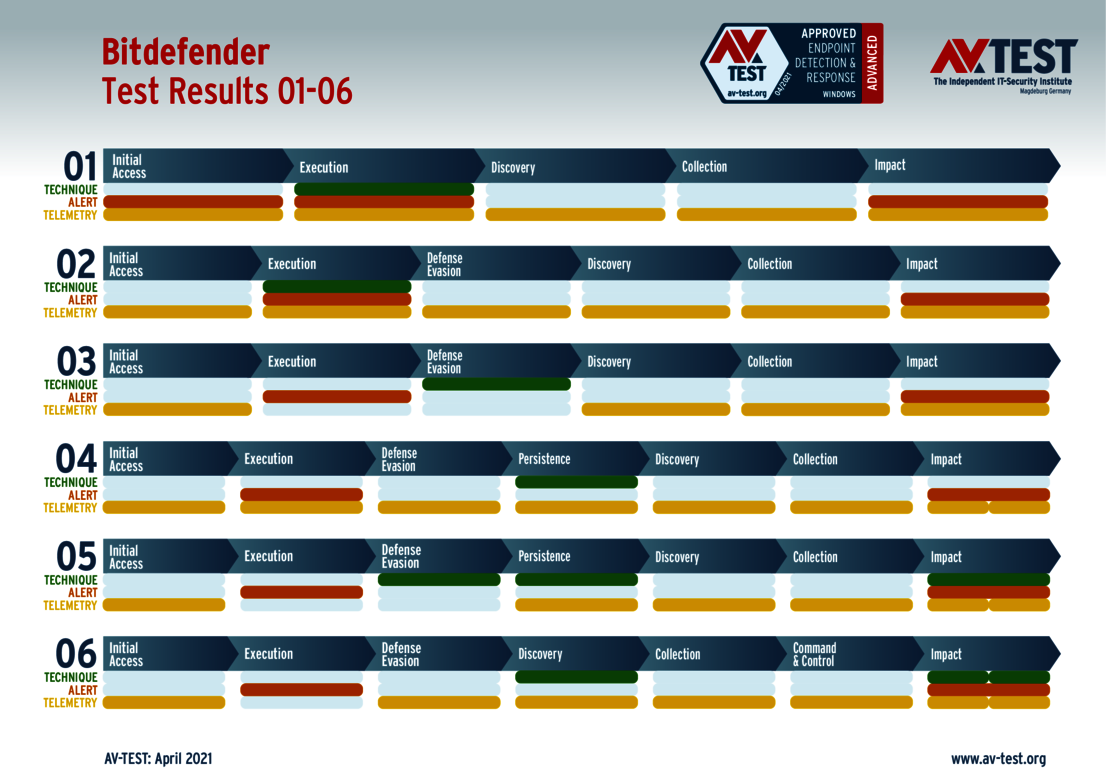
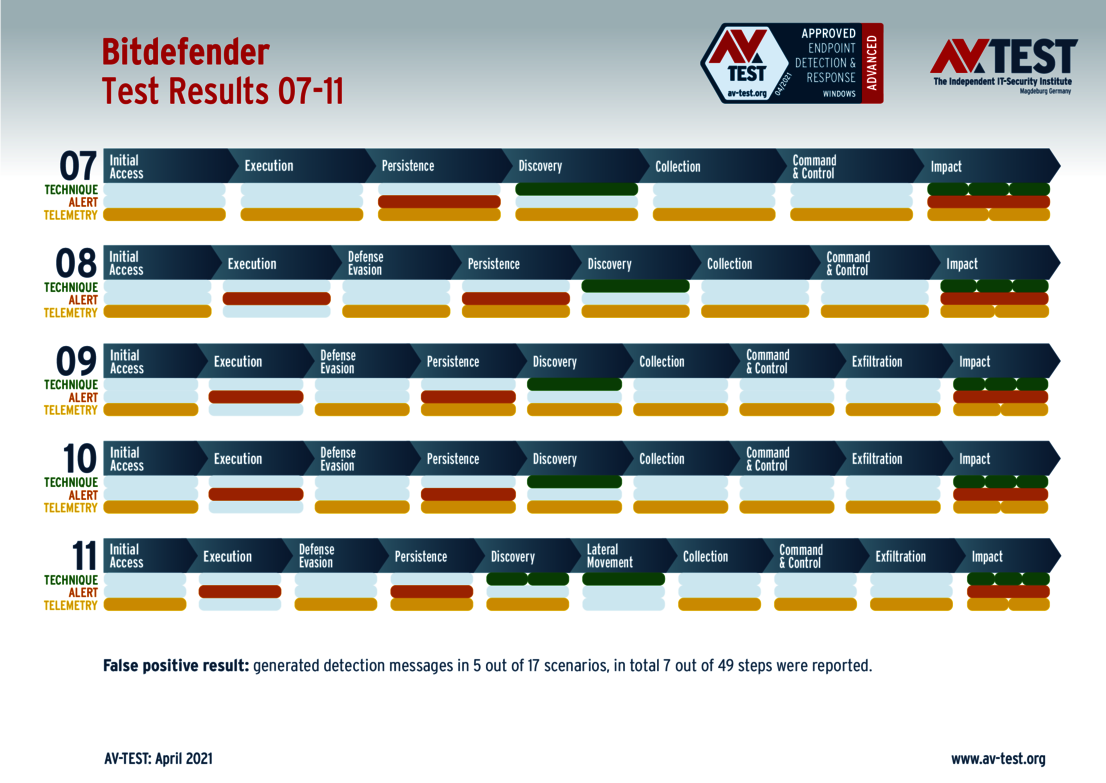
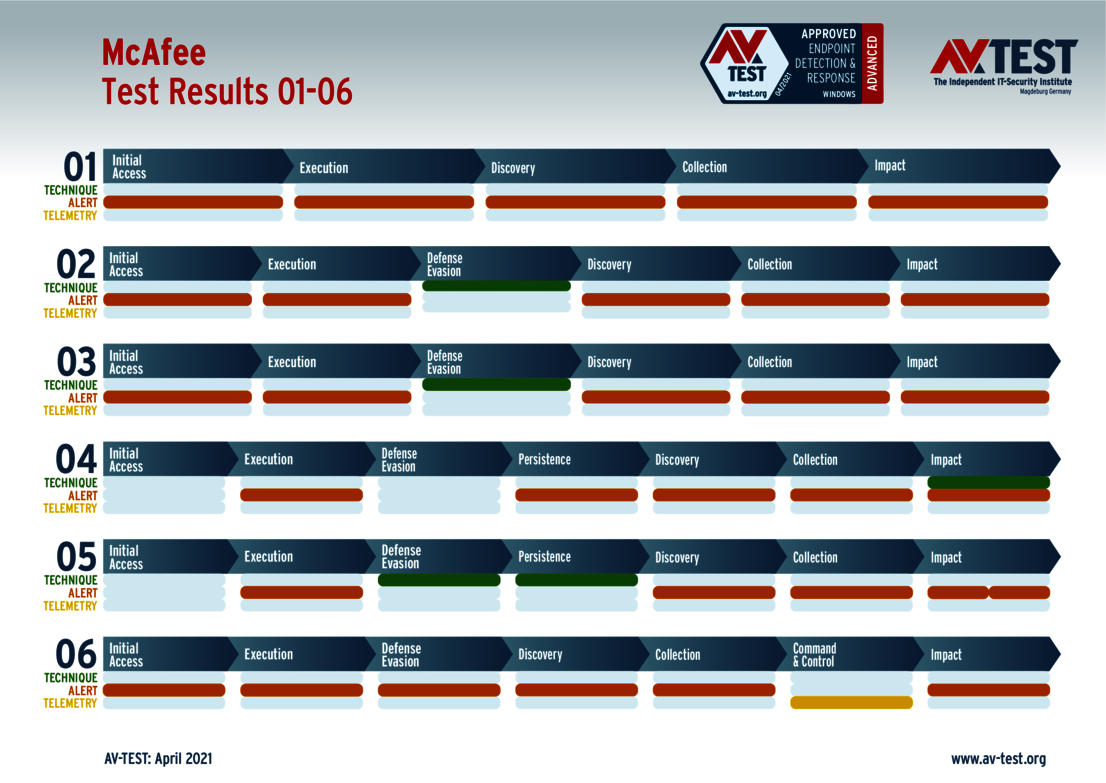
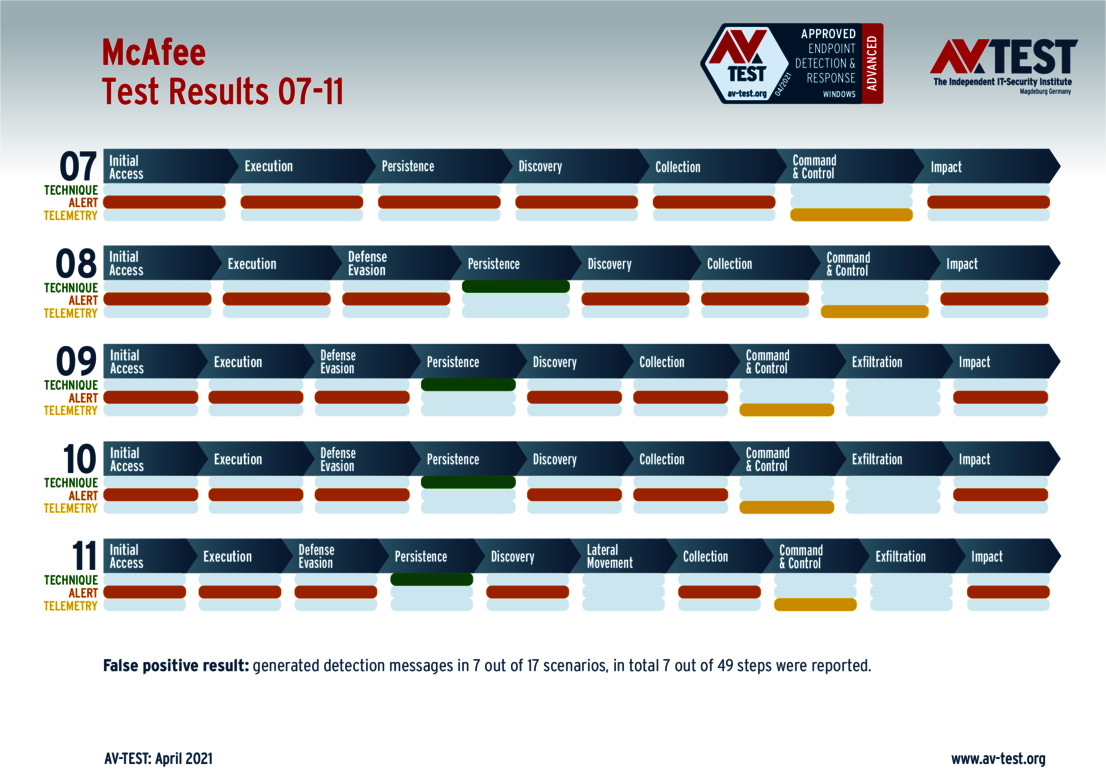
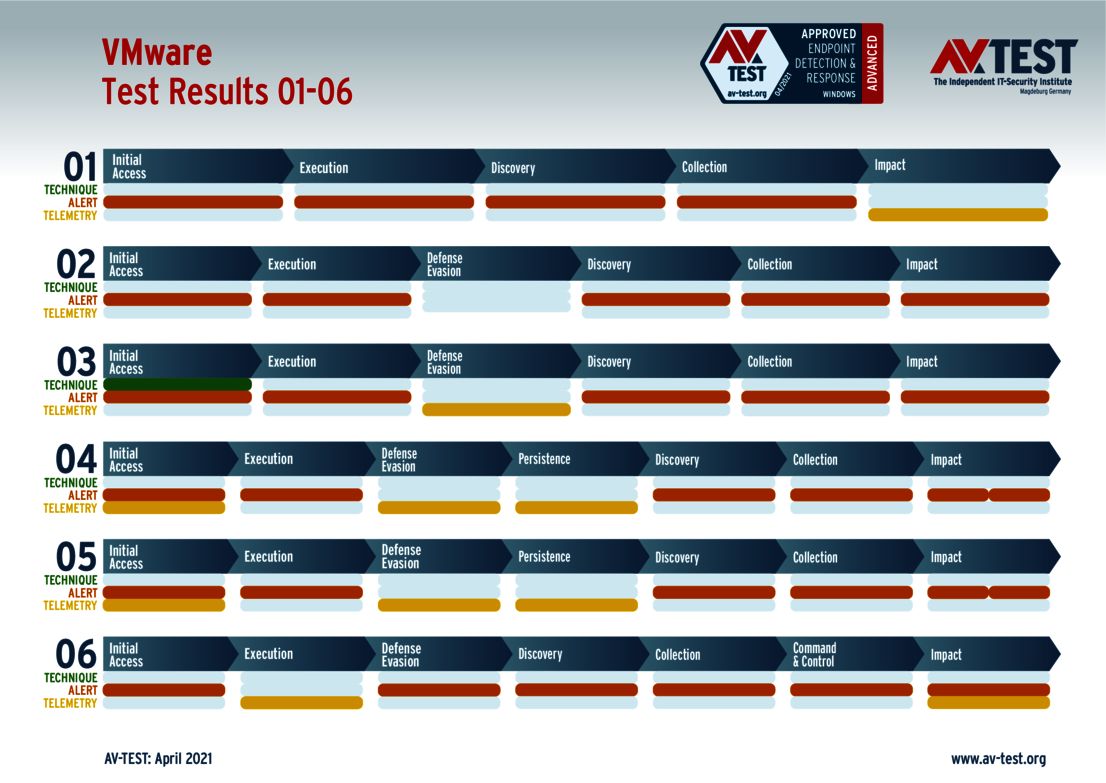
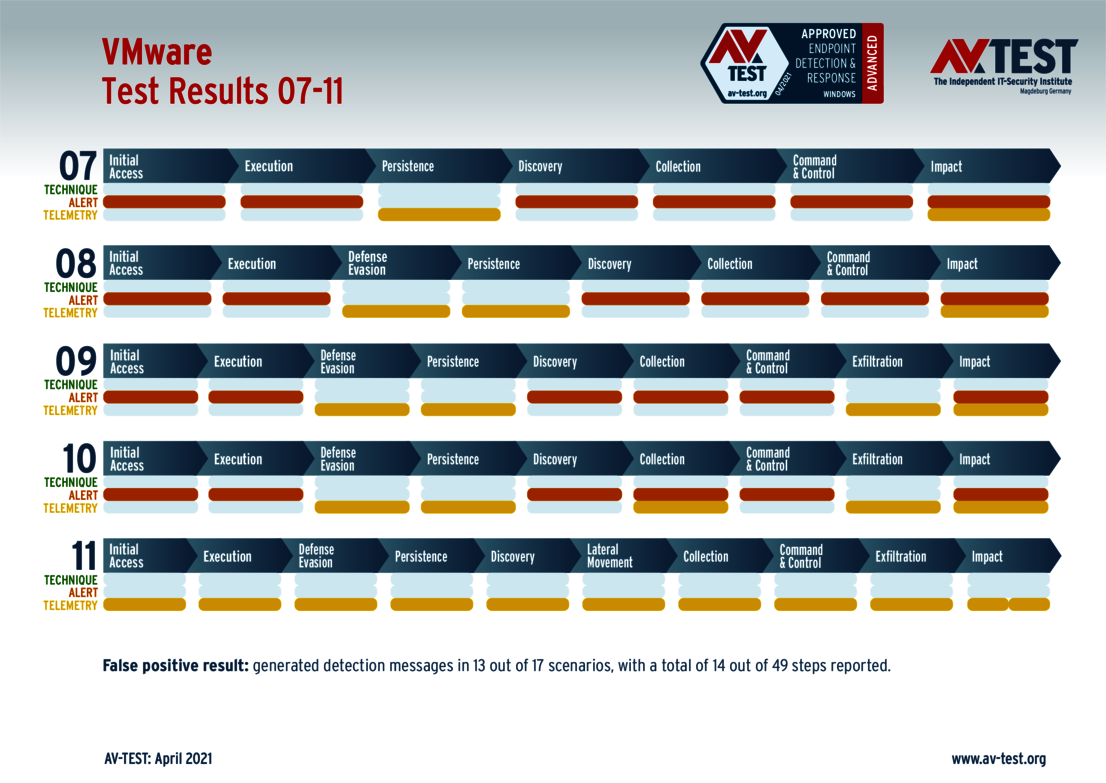
2. EDR evaluation: Which steps of the launched attack were detected and how detailed was the reporting? The charts highlighting the results of the EDR solutions document what type of detection occurred by the products in the individual phases of the test attacks:
- Technique reporting: Ideally, an EDR solution ought to detect and report on the respective technique for each attack phase according to the MITRE ATT&CK Matrix. This affords security analysts precise insights and helps them make the right decisions.
- Alert reporting: One level below this are alert reports. They classify the operation as malicious and thus notify the user that intervention is necessary. However, the level of detail here is much lower than with the relevant technique reports.
- Telemetry reporting: Finally, there are telemetry reports, which are not to be read outright as warnings; instead, they only provide certain findings without any security evaluation. At the least, experienced analysts are able to identify attacks based on these reports and utilize the knowledge gained to later reconstruct the attacks.
• AhnLab V3 Endpoint Security
• Avast Premium Security
• Avira Antivirus Security
• Bitdefender Endpoint Security Tools
• G DATA Security Client
• McAfee Endpoint Security
• Bitdefender Endpoint Security Tools
• McAfee MVision EDR + McAfee Endpoint Security
• VMware Carbon Black Cloud
Are you interested in detailed results?
The interpretation of the detailed results of this test is dependent on the respective environment utilized, the configuration and the use of the relevant products. That is why AV-TEST makes individual results for this test available within the scope of an individual consultation and can also offer you tests adapted to your infrastructure. Please don't hesitate to use our contact form to get in touch with us: