Latest News
March 15, 2021 | Research
Emotet – Never Let Your Guard Down
Through worldwide cooperation of cyber specialists, one of the largest botnets of Emotet threats has been shut down. Unfortunately, however, this network was only one of many, which means that attacks with Emotet still remain a major threat. AV-TEST provides background and explanations.
Emotet botnet destroyed:
at the end of January 2021, law enforcement authorities scored a major success
Admittedly, it was one of the best items of news at the end of January 2021: following in-depth preparation, an action planned by international police and law enforcement agencies led to the intended success. They were able to take down one of the key botnets that was instrumental in coordinating the use of malware attacks with Emotet. The first erroneous interpretation of the press release: it was not the botnet of Emotet that was destroyed but rather one of the largest networks mainly using Emotet as a weapon of attack. While this resulted in a temporary reduction in the number of attacks, in the meantime the gap has been closed by other competing botnets using the same weapons. This is also evidenced by the status of data on registered phishing and malware e-mails recorded in the AV-Atlas.org threat portal.
In order to understand how to be prepared and defend against Emotet and its attacks, it is important to know the strategies deployed by the attackers and how an Emotet attack works.
Behind the scenes of Emotet
The Emotet malware describes an entire malware family and is considered a macro virus. Many mutant specimens have been cropping up for years on the Internet, preying on consumers and corporate users. Emotet is structurally very small and has no arsenal of coded weapons of attack in its quiver. Rather, it is a clever door opener, which then ushers the big-gun attack specialists into the systems.
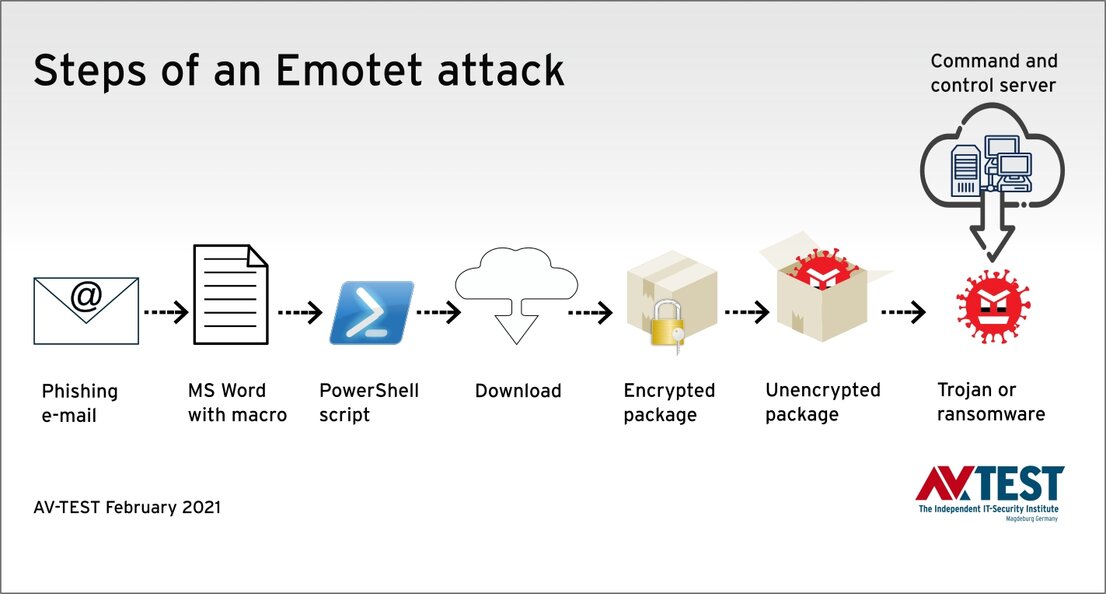
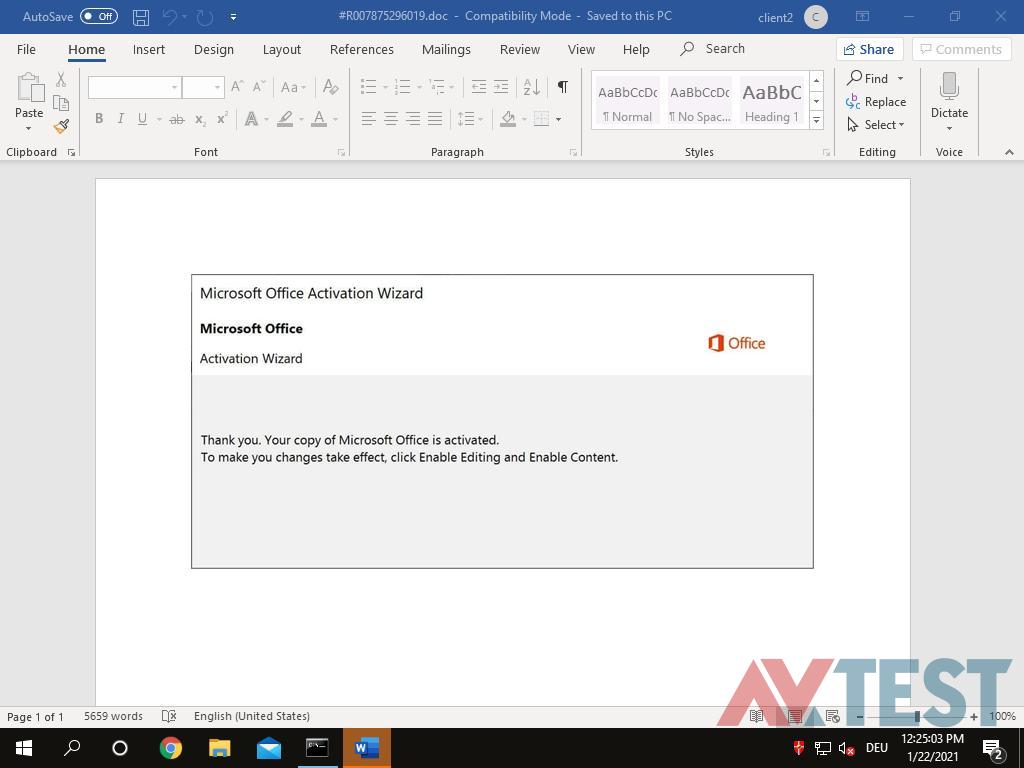
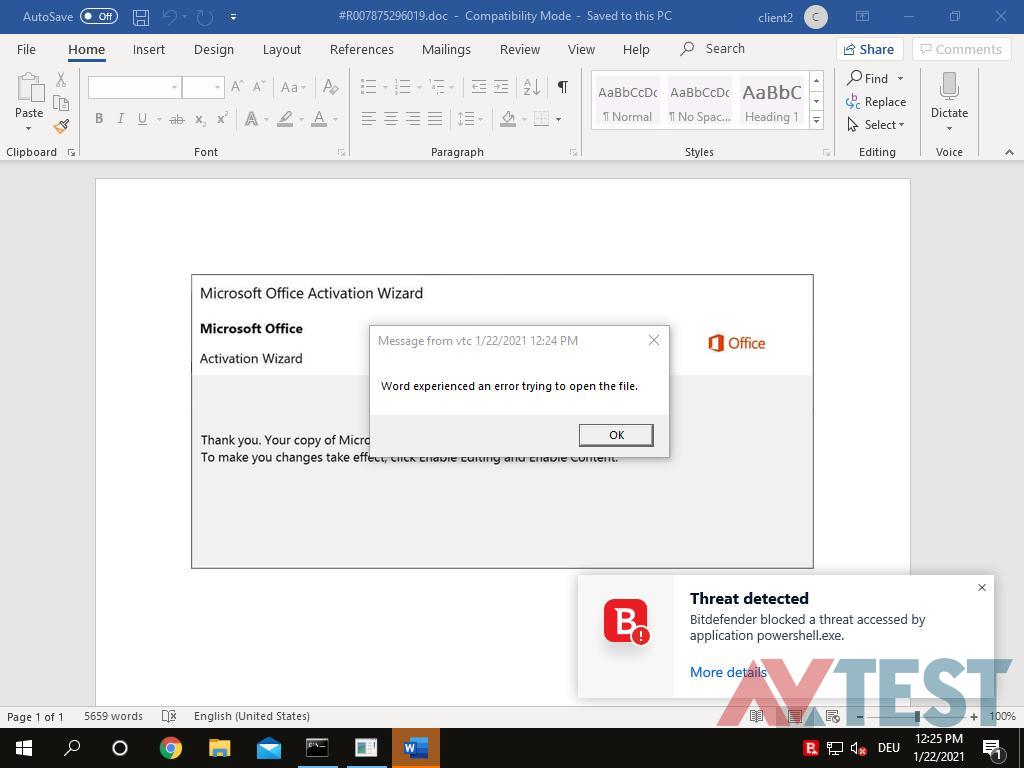
Typical Emotet attack step-by-step
The attacks usually proceed according to the same pattern: If an infected and macro-embedded Word file is opened, instructions per PowerShell summon additional attackers like crypto miners or ransomware from the Internet and activate them
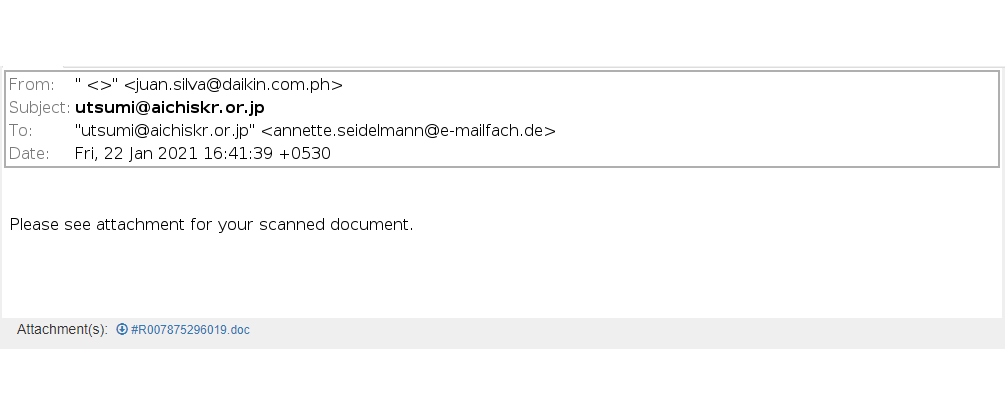
Spam mail with *.doc file as an attachment
The Emotet macro, concealed inside the *.doc file, is not always detected
The Emotet attack step-by-step
In general terms, this is how an attack works: first the recipient receives a sophisticated fake e-mail in the name of a known customer or telecom provider, for example. The e-mail either directly contains a word file attachment in *.doc format or links to a malicious file. In the e-mail, the user is informed that it is absolutely necessary to allow active content in the *.doc file (enable macros). The code is so small that analysis is a challenge for security systems.
As soon as the macro code is launched and the PC is infected in this way, Emotet opens the doors and allows access to dangerous threats like malware heavyweights such as Trickbot or Ryuk. Trickbot is a notorious banking Trojan or crypto miner. So it steals log-on details and passwords or launches crypto miner workloads on PCs or servers, and mines for cryptocurrencies. With Ryuk, a known ransomware is introduced into the system, which encrypts the data and starts a classic round of blackmail: those who pay quickly will purportedly receive the respective decryption tool. Emotet continues to hijack the e-mail program, along with the address book, proliferating further. Unfortunately, this is very effective, as the sender is known to the receivers of the new infected e-mail and considered trustworthy.
Thus, the attacks or their consequences are not always the same. What's more, the exact types of Emotet, Trickbot or Ryuk, for instance, often vary. Through analysis with the help of the servers controlling the botnet, Emotet can also find out whether it has landed on a private PC or on a workstation in a corporate network. This also influences how the attacker will further proceed. Once Emotet is in a network, it attempts to directly spread out among additional corporate PCs.
The future of Emotet
Naturally, no one can accurately predict just what the future of Emotet and all its variants will look like. But if we look at comparable cases, a trendline becomes apparent. It would seem to develop the same way as Carbanak malware, with which banks were attacked per phishing and more than one billion dollars were stolen. While the malware was identified and the network was taken down, the highly-efficient code of the malware served as a blueprint for new malware for many years. Experts assume that the technology and parts of the Emotet code will continue to be used for a long time.
Which means that the problem of extremely difficult detection of Emotet will still be with us. As long as that is the case, there will be further botnets directly relying on Emotet and its variants and launching attacks. Add to this the fact that many companies currently still vastly underestimate the existing danger. Put in basic terms, some of them simply got off lucky.
The attacks, however, are still continuing. This can also be easily gleaned on AV-Atlas.org, the Threat Intelligence Platform, a real-time platform for cyber threats. Because Emotet mainly proliferates via phishing e-mails, the experts from AV-TEST paid special attention to the category of spam e-mail after the takedown of the botnet at the end of January 2021. While the traffic of phishing e-mails containing Emotet samples dipped slightly, it already resumed its previous level after two or three weeks. This supports the theory that the attacks were taken over by other botnets.
More protection against all forms of Emotet
Consumers, along with corporate users, have an entire bundle of options to protect against malware like Emotet or other ransomware, for example. The first step is to use a good and up-to-date protection solution on a PC or on clients and servers. In this area, the AV-TEST examines in its certification test which solutions can be recommended, making test results freely available:
- Tests of Windows protection software for consumer users
- Tests of Windows protection software for corporate users
This initial filtering greatly lowers the risk, as not only files from the Internet, but also e-mail attachments, are examined and end up in the quarantine, where necessary.
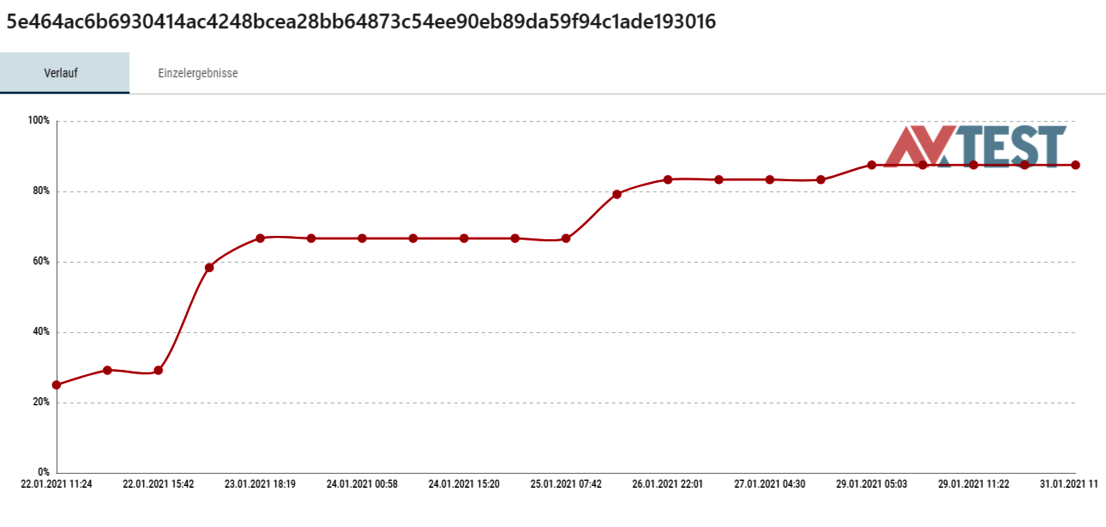
Detection history of an Emotet signature
Initial detection is only 25 percent – within 7 days, the number of signature-based detections increases to some 90 percent
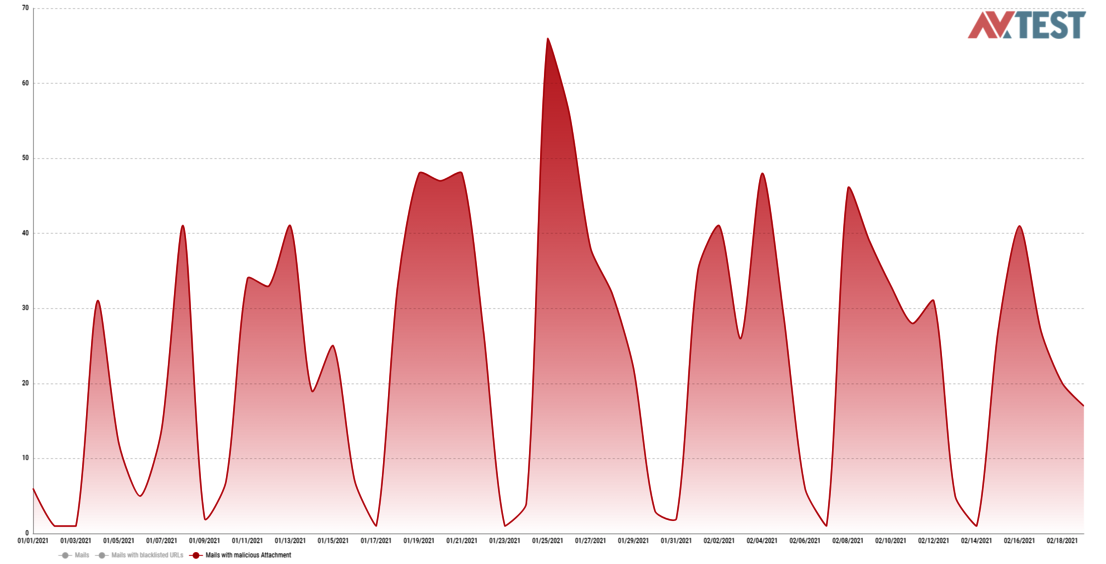
Botnet taken down – malicious e-mails remain
Over a period of roughly 6 weeks, the scanners of AV-TEST registered only slightly fewer e-mails with malicious attachments than normal, ebbing on the weekends
Blocking macros
As the Emotet code is executed via macros in documents, consumers and corporate users should strictly refrain from enabling macros in applications. This is a default feature in Office, for instance, but it is often defeated by users themselves. Often, it is not possible for corporate users to forbid the use of macros, as otherwise workflows would be disturbed. Modern network management can offer a remedy in this regard by providing rules that enable macros certified by the IT department per code signature. Even Microsoft explains and recommends the use of signed macros.
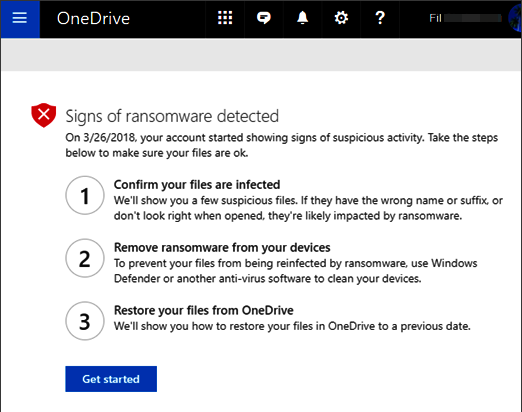
Data backup in the cloud
In the event that ransomware like Ryuk strikes with the help of Emotet, then the subsequent encryption generally cannot be cracked without the matching code. Normally this doesn't involve the Windows systems themselves, but rather the data partitions with constantly changing work data. Even continuously connected backup drives are of little help, as these are encrypted as well. Cloud services can provide a remedy here.
A cloud solution is normally already included in large enterprise solutions. Small and medium-sized companies, for example, can rely on solutions such as OneDrive for Business. In this case, cloud-based stored data which has been completely encrypted can be restored to any time within the previous 30 days. Solutions such as these are also offered by other business clouds, e.g. Dropbox. Consumer users can also take advantage of such clouds, because there as well, the changes per file are always stored – often up to 10 versions. Restoring data is somewhat more complex, however. But in case a PC is infected, it is straightforward and only takes a bit more time and effort.
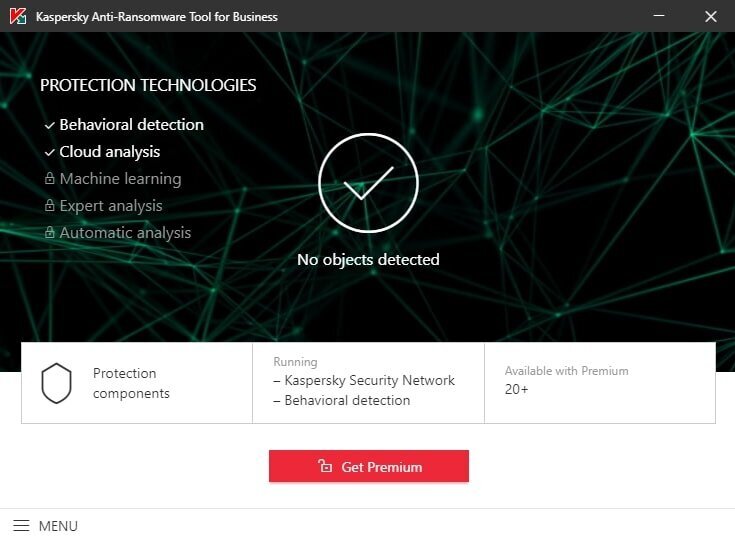
Additional protection software
For an endpoint security package, major corporate users normally rely not only on one solution but also use additional security modules, also from other manufacturers. This is a good strategy, and it could also be used in the SME sector or by consumers.
Small and medium-sized enterprises, for instance, can use the free Kaspersky anti-ransomware tool for business for their clients alongside their security solution. It monitors the processes on a PC and based on a database, detects actively operating ransomware, and processes its uses. If an encryption process has been launched, the tool blocks it, in the event that the security solution has not triggered already. The tool is helpful on home PCs as well. Consumer users, however, also have the option of using combined backup software, also featuring an anti-ransomware tool, such as Acronis Backup. In that application, there is an additional process monitor to check whether ransomware is involved. If this is the case, the process is terminated and the modified data is restored from the backup.
Known Emotet victims
Over the past few years, Emotet has carried out successful attacks, wreaking havoc in some cases, e.g. in hospitals.
If the victim is a consumer PC user, the PC computing power is often hijacked to mine for cryptocurrencies. If a corporate user is affected, the ransomware variant is normally activated, encrypting the PCs and data, only to be released in exchange for ransom. Well-known victims of Emotet include the following:
- In November 2018, the Fürstenfeldbruck hospital in Germany shut down all 450 computers in the aftermath of an Emotet infection and had to log off from the rescue coordination center.
- At the end of 2018, the engineering group Krauss Maffei was struck by an attack.
- In March 2019, an Emotet attack cost the Norwegian aluminum manufacturer Hydro Norsk an estimated EUR 40 million.
- In May 2019, Emotet struck the Heise Group (publishers of the c’t computer magazine).
- The Higher Regional Court of Berlin was unable to complete any hearings from September 2019 due to an Emotet attack.
- In October 2019, the automation company, Pilz, with global operations, was hit.
The list goes on and on, and cases have presumably been made public only thanks to the GDPR, recent European data protection legislation. Worldwide, it is certain that a high number of attacks on companies go unreported, as they fear for their image.