Latest News
May 19, 2021 | Research
AV-ATLAS: The Research Platform for Spam, Malware, and Threat Trends
On the Internet, you may find many statistical surveys, but rarely open sources for the research. AV-ATLAS is different in that respect: there you can call up live data, free of charge, on the latest malware and spam, or you can conveniently analyze threat trends. Interested professionals can even subscribe to entire data flows for analysis.
The AV-ATLAS platform serves many needs at once: Those interested in latest spam statistics, but having no specialized knowledge, can call up the prepared charts in real time. Knowledgeable users who want to dig a little deeper can customize the data set and receive their own individual chart. Absolute pros will tend to click past the charts and subscribe to entire data flows for their own database analysis.
AV-ATLAS – data source in real time
Over the past 15 years, the AV-TEST lab has developed many data sources and analyzes them on its own. This is also necessary, because an independent test institute could never rely on data from manufacturers whose products it is subsequently testing. That is why the lab at AV-TEST utilizes as a lure for cyber-gangsters many of its own honeypots, servers, mail accounts, websites, or other data traps, collecting infected e- mails, data, scripts and much more, and examines everything in analysis machines developed in-house. This constant data flow is then broken down logically into smaller flows, which form the data backbone of AV-ATLAS. To ensure that the platform will not become unmanageable, given the plethora of data, it always reflects a data collection of the past 14 days. After all, AV-ATLAS shows current data and does not necessarily want to be known as an archive for evaluating data of the past several years. Retrospective analysis is possible, however, for customers wanting to subscribe to entire analysis channels and evaluating them over a longer term.
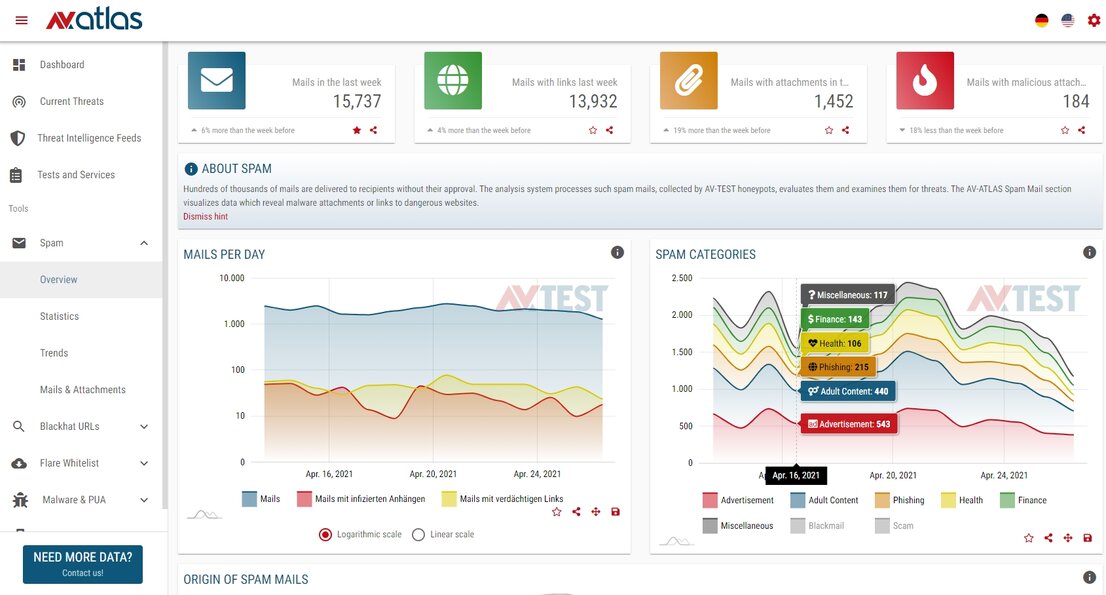
Spam evaluation with roughly 2,000 e-mails per day
AV-ATLAS quickly shows the content in spam e-mails, and how dangerous existing attachments are
Current threats at a glance
As already mentioned at the outset, AV-ATLAS also seeks to help journalists or academic staffers without previous expert knowledge to quickly arrive at substantive research findings. The "Current Threats" section, for instance, offers an overview of all the security areas covered by the platform, e.g.: spam trends, mail attachments, mail content, and subject lines, phishing mails, malware, and affected platforms such as Windows, Android, Linux, or Mac. A click on "phishing e-mails" shows an overview of all countries of origin for spam mails. In dispelling anticipated clichés, the findings show that the United States was No. 1 in spam in April 2021, and Russia only came in second.
The "Current Threats" section is thus a trend thermometer showing special hotspots. For greater clarity, the Institute has created six additional evaluation sections: Spam, Blackhat URLs, Flare Whitelist, Malware & PUA, IoT and Android Flare. Whereas some of the buzzwords, e.g. spam, are largely known, many people would be puzzled by the term Flare Whitelist. We explain to you below which popular evaluations are behind the special terms.
Spam: understanding and evaluating analyses
Even people having no specialized knowledge ought to be familiar with the nuisance of spam. How dangerous spam can be, however, is underscored by the term known as phishing, as it is a subheading for specialized spam e-mails for luring in or "phishing" for users. The overview quickly shows the volume of the spam and the percentage of e-mails with harmless, yet forwarding or infected attachments. Another interesting feature is the automatically generated world map: it clearly shows the current countries of origin for most spam.
To enable user groups quick access to important evaluations, the "Spam Statistics" section offers ready-made charts. They can be shared with others or saved for own use. Likewise, the "Trends" section shows a total of seven pre-evaluated lists of spam countries of origin, languages, attachments and more. Those who want to delve deeper into the data can click the "Mails & Attachments" section. In that section, the individual spam e-mails can be manually sorted and compared according to subject or attachments. Selection criteria such as "Seen 15 minutes ago" are a testimony to just how up-to-date the platform is.
A few additional facts: AV-ATLAS analyzes, scans, and classifies roughly 2,000 e-mails per day. The spam volume is not always relevant, which is why e-mails already recorded multiple times are not considered in the analysis, yet they are reflected in a rising trend barometer.
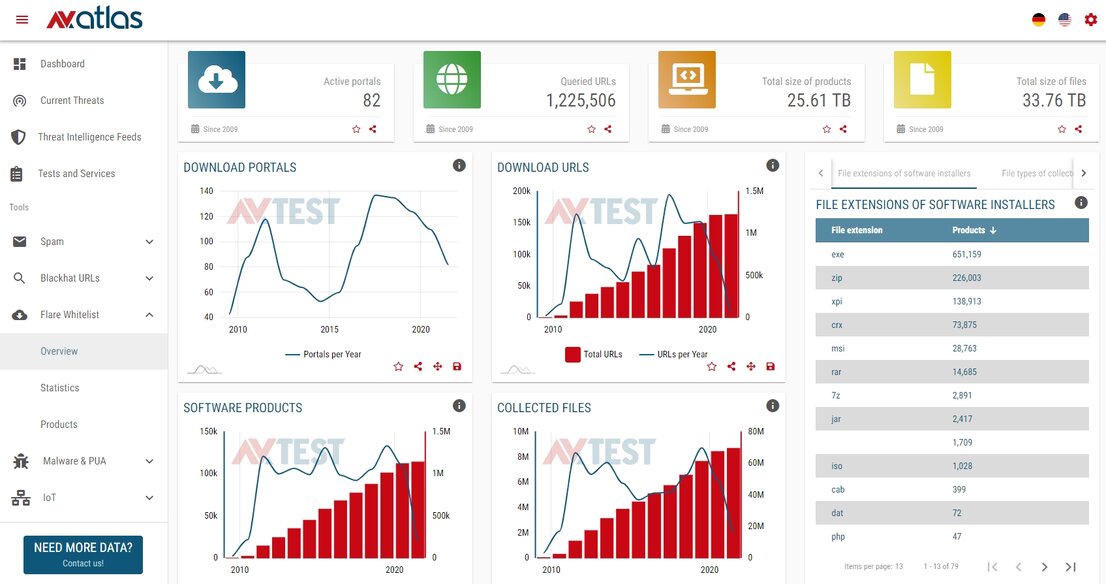
Flare Whitelist checks software and updates
Every day, the machines scan 50 to 250,000 individual files from hundreds of software products and updates
Blackhat URLs: simply dangerous links
Experts tend to use complicated terms, as they often wish to broaden a topic with additional subcategories. In basic terms, the category of "Blackhat URLs" stands for dangerous links found in the Web, indexed, and evaluated.
Depending upon the volume, the platform analyzes between 100,000 and 300,000 identified links per day. These are further subdivided into "Suspicious URLs" and "Dangerous Trends". Because some links may lead to a suspicious website and to advertising software (PUA, potentially unwanted application), but that is not really dangerous. Yet another link, under the guise of promising a free game, immediately offers the download of a Trojan.
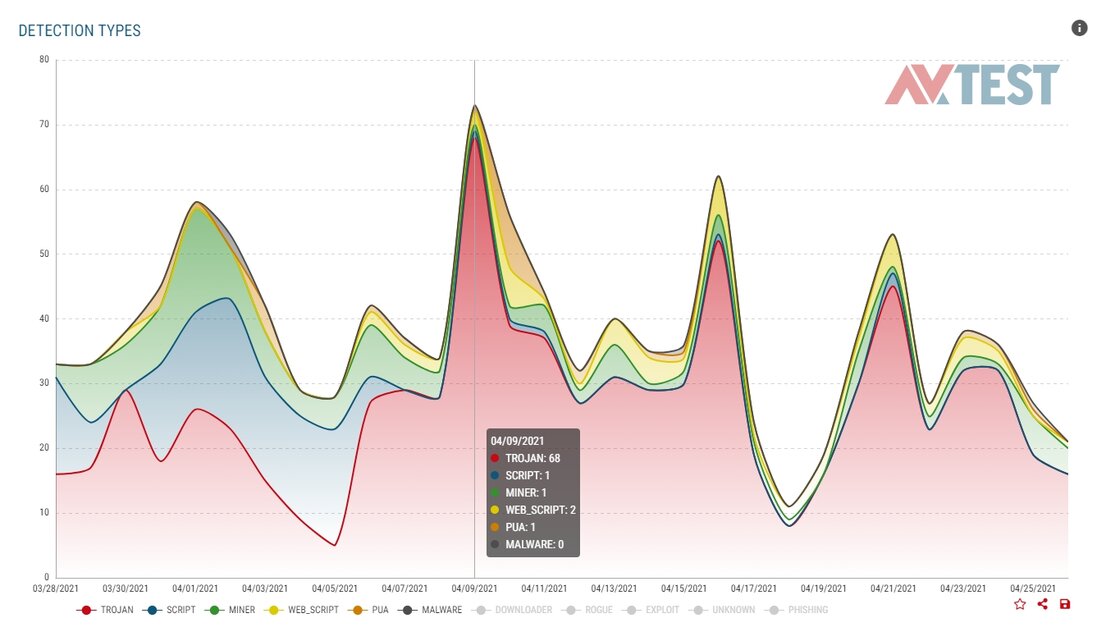
Extremely interesting pre-set evaluations can be found in the "Statistics" section. In addition to the number of dangerous URLs, i.e. Web addresses, sorted by time, a comparison is also shown between PUAs and malware, or trend sources of many URLs, e.g. from Steam, IMDB or Google. If we also examine the "detection types", we quickly see that the majority of infected links contain a Trojan.
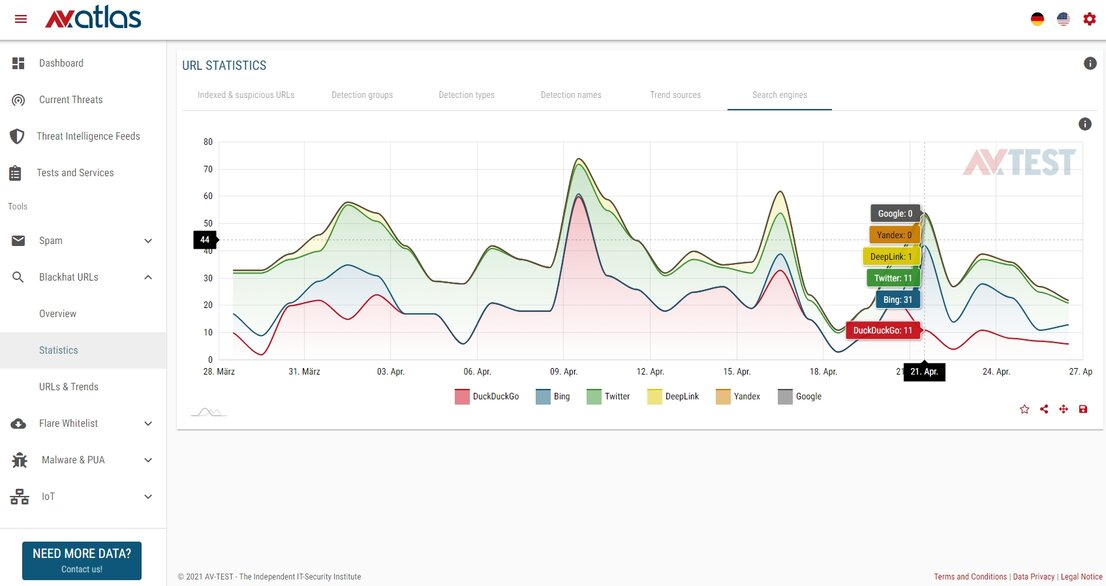
The "Search Engines" chart tucked away in the "Statistics" section is the truly fascinating feature: there you can see which search engine delivers the most dangerous links to its users. In addition to Google and Bing, the list also includes DuckDuckGo, Deeplink, Twitter and Yandex. A cursory look indicates that in the time period between March 28 and April 27, 2021, the alternative search engine DuckDuckGo delivered infected links daily, and that Bing has also repeatedly had difficulties in this area. Google was a model citizen during that period, offering no infected links.
Flare Whitelist: good or dangerous software
Another special term is "Flare Whitelist". In this section, the lab at AV-TEST examines software and updates circulating over the Internet. Every day, the machines scan hundreds of software products, or updates and the 50,000 to 250,000 individual files distributed with them. The evaluation looks at popular software, such as the Chrome browser or the WinRAR compression tool, along with the lesser-known software WYSIWYG Web Builder.
This section provides little data that can be immediately used for research. It is all the more important for download portals, however. Because they may distribute lots of software applications or updates not containing revisions but rather Trojans or something else. A notorious example is the CCleaner from Piriform: some time ago, an update server was hacked and an update infected with malware was distributed. That is why some download portals use the scan service from AV-TEST. The most well-known here is Heise, a publishing company based in Germany, which has all files in the download portal tested by AV-TEST technology.
Malware & PUAs: annoying or dangerous applications
While the term malware describes definitely harmful software, the term PUA (potentially unwanted application) is defined differently among experts. While PUAs do not pose any direct threat, they can annoy users and usually put a load on the network and devices. Some manufacturers, along with the lab, already classify some PUAs as malware, while other manufacturers list them as annoying but harmless.
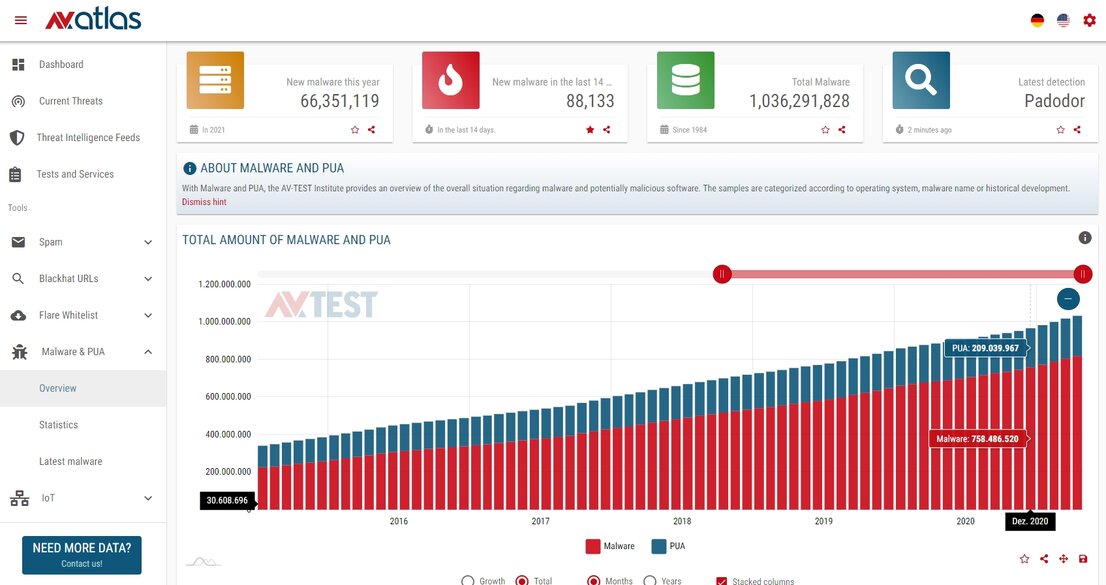
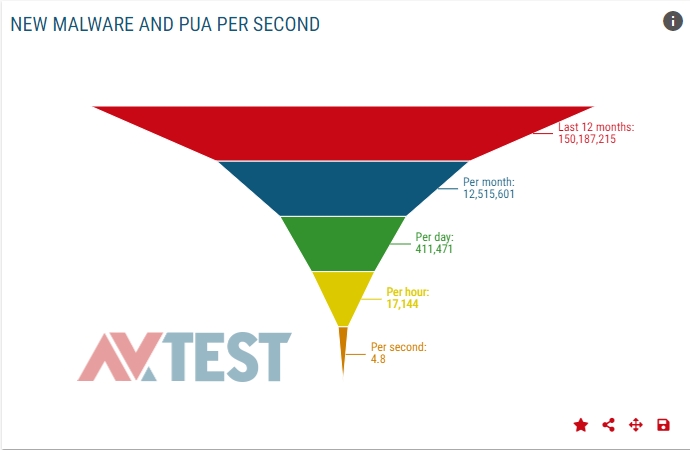
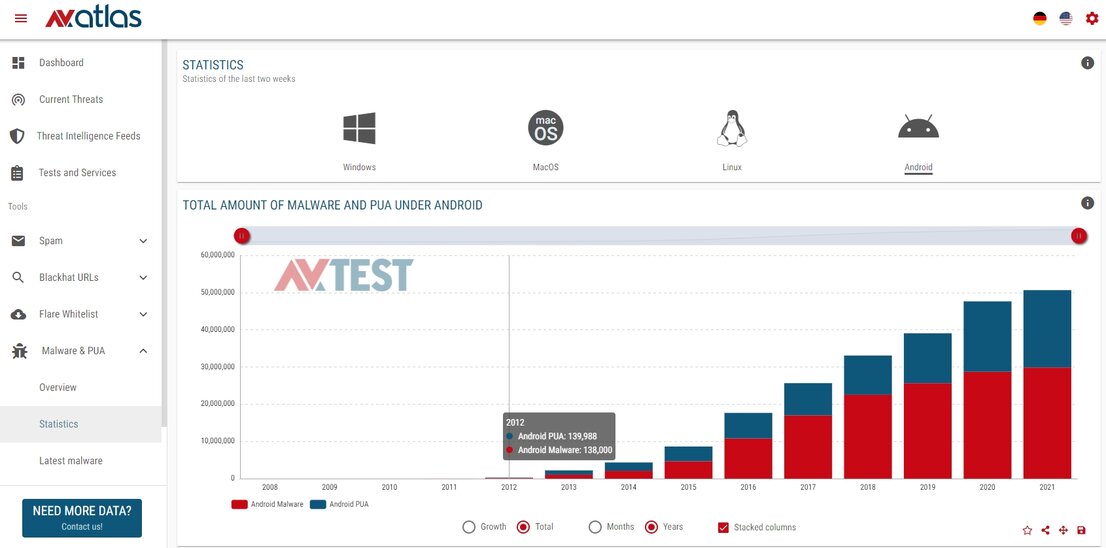
The Overview of this section indicates the current status of malware and PUAs. The counter for "total malware", registered since 1984, has already reached one billion samples and continues to tick away. Before the end of April 2021, just under 70 million samples had already been added. A freely definable timeline can be used to display data from 2008 to the present. This means that an analysis of malware growth over the past 5 years requires only a few mouse clicks, which can generate a chart that can be shared or saved.
The section of greatest interest here is "Statistics", because PUAs and malware can be evaluated separately there. Operating systems such as Windows, Mac, Linux, and Android can also be used as criteria, along with a time parameter according to months and years, also expressed in terms of an increment or the total. If we evaluate the malware growth of Android in the first 4 months in 2021, a statistic also shows the in-depth breakdown. Thus, a distinction is made between PUAs and the type of malware, as well as between malware types such as Trojan, password, dropper or other. In addition, it is possible to drill down according to the type of file where the malware samples or PUAs may be lurking. They are mostly APKs, the installation packages for Android. The evaluation gets even more in-depth: it even lists the names of the malware families in a graphic and also evaluates the development of password Trojans, droppers, or ransomware. A vast trove of material.
IoT: nobody knows it, but everyone has it
Many users have already heard the term IoT – Internet of Things – but are often uncertain about what it means exactly. It's only when you make the connection between IoT and remote-control lights or smart speakers like Amazon's Alexa that it begins to dawn on everyone. IoT is an extremely rapidly-expanding area of devices, but some manufacturers are neglecting the issue of security. Many a poorly secured device has been harnessed as a gateway into a bot network.
Attackers have also taken notice that IoT devices, sometimes high performance components available 24/7, make them interesting targets for a botnet. That is another reason why IoT devices are on the short list for attack, as seen by AV-ATLAS statistics. Because the lab is not able to monitor the devices of users, it offers many of its own devices as honeypots on the Internet. Anyone wanting to gain a better instinct for how extreme things are in the IoT field need only take a casual glance at the overview. AV-TEST's honeypots alone received roughly 18 million commands over the Web in 14 days! These also include login attempts. In the process, the lab registers the login word lists, where names such as Admin, Root or User rank among the top places. Here is another interesting tidbit: From which country do most command requests originate? Currently in April 2021, the most requests came from Switzerland. This is also illustrated by the world map, which also has a zoom function via mouse wheel.
In addition to logins, the experts also register attempted data uploads, logging the type of files that are involved. The malware used is immediately analyzed and indexed. All additional data, however, is more suited to specialists, as it specifies the protocols, IP addresses, programming languages, interfaces or ports being exploited. The in-depth explanations about the technology of the honeypots used, along with the list of current malware with hash values is only recommended for experts.
Flare Android: everything the Google Play Store doesn't have
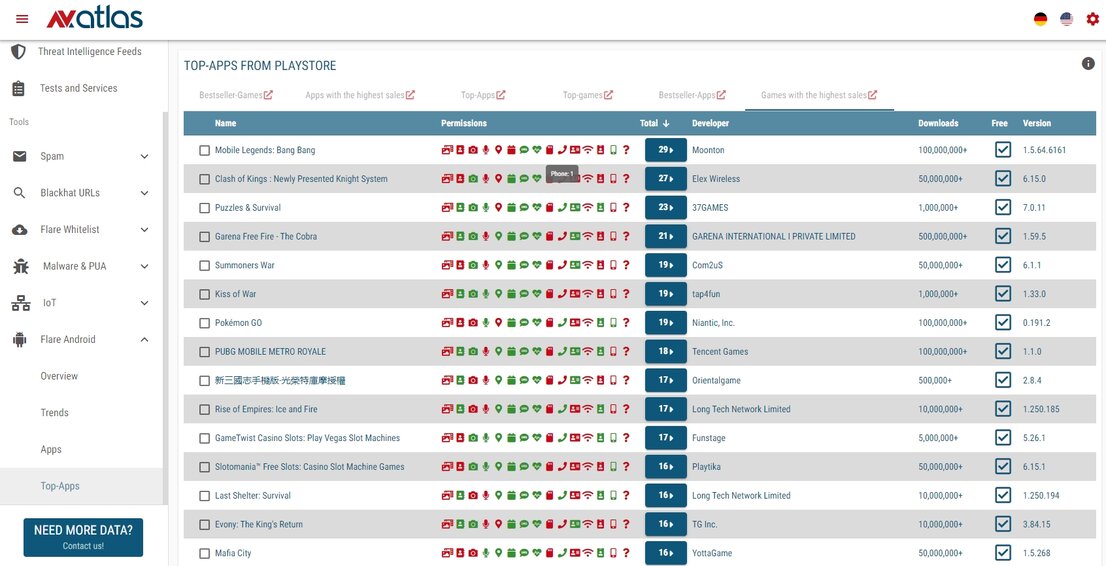
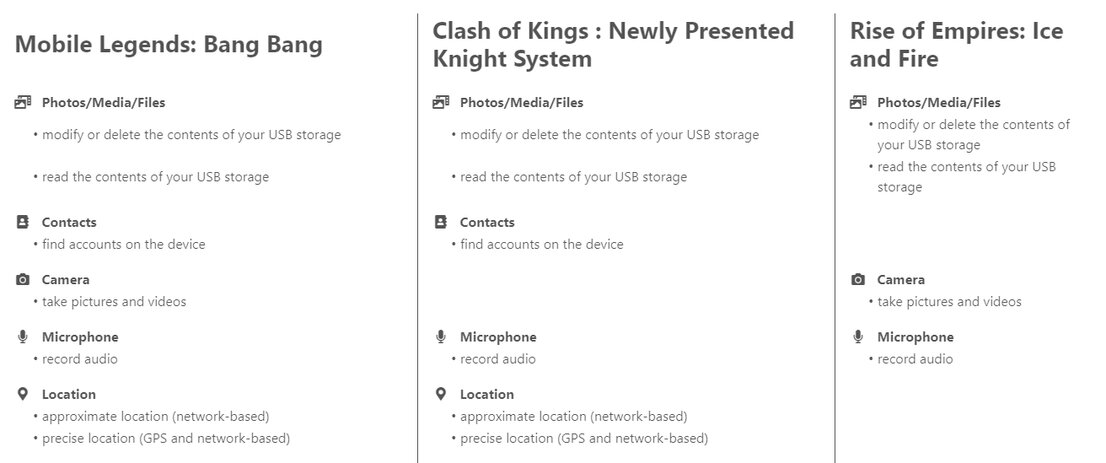
In addition to the Google Play Store, there are many other stores for downloading Android apps. The "Flare Android" section currently analyzes over 5,000 apps per month, examining the source code and keeping track of the permissions that are actually being requested by each app. Between 1 and 20 percent of the apps examined per day are suspect. This means they contain strange or malicious code. This info stream is mostly tapped by antivirus manufacturers on a subscription basis, as it offers a wealth of additional information on how to identify malware apps on Android devices that do not originate from the Google Play Store. Moreover, the data is also used for the so-called app whitelist, i.e. a "good guys list", which thus guarantees less analysis work and also prevents false alarms.
For Android apps, permissions are especially important for users and their security. For example, in the past, there was a flashlight app that requested access to memory, contacts, phone or text messages. In the first few months, everything appeared to be harmless. Later, the app began siphoning off data and sending premium text messages.
For research purposes, the section on "Top Apps from Play Stores" is extremely well organized. It features lists of the top apps or games, bestsellers, or apps currently with the highest sales. For each app, it is possible to call up the permissions requested. Thus, it is easy to discover that the app "Mobile Legends: Bang Bang", for example, in addition to 28 other permissions, also requests access to the phone status and identity. Only the provider knows why.
AV-ATLAS Threat Intelligence Feeds for Pros
The AV-ATLAS platform always evaluates only a small slice of available threat intelligence data. Professionals and corporate users can subscribe to unlimited data feeds and evaluate them for their purposes.
The Analysis Data as Feeds can be used by professionals for a variety of purposes. On the one hand, they can train existing mail systems or upgrade prevention and detection systems with the latest developments. SOCs, developers or IT security teams can thus fortify their products or enhance the protection for their company. The feed offers the analysis of more than 5,000 evaluated e-mails per day, analyzed, indexed, and divided up into various potential threat levels.
The threat scenario at a glance
The attacks on companies can be evaluated, but attacks averted beforehand are a definitive boost to security. The "Blackhat URLs" section analyzes more than 300,000 Internet addresses per day in terms of threats, already delivering the attack trends prior to an attack. Prevention is better than only responding to incidents. That is why it is worthwhile for security services in companies to always keep an eye on the threat scenario.
Improving development and service
It is difficult to fathom the damage sustained to a company's reputation when it releases infected software or updates. The AV-TEST service "Flare Whitelist" helps developers, corporate users or download portals in the distribution of error-free software by scanning existing applications and files. In addition, the software scan helps in checking for false alarms by protection programs, such as antivirus software. Because false alarms expend the precious trust of users. In the development, testing and use of software, Flare Softwarescan is of help in minimizing, or ideally preventing altogether, any false alarms (false positives) triggered by antivirus software.



![AV-ATLAS – the research platform [Translate to English:]](/fileadmin/_processed_/e/9/csm_Aufmacher_AV_atlas_artikel_f4cebc6571.jpg)