Latest News
November 08, 2022 | Text: Markus Selinger | Antivirus for Windows
29 Protection Solutions in a Defense Test against Ransomware
A successful ransomware attack always has disastrous consequences. While only individual PCs may become infected in a private environment, ransomware can quickly spread via a corporate network to all available PCs and drives. In its Advanced Threat Protection test, AV-TEST evaluated how well security solutions can protect consumer PCs and workstations in corporate environments against ransomware. In each of the 10 scenarios, several solutions had their work cut out for them.
"Disastrous" is the best term to describe a successful ransomware attack. Just how disastrous the situation can be, is something many companies have already had to learn. In Germany, leading companies such as Hipp, dpa or the Chamber of Industry and Commerce were affected, and in Europe and around the world, victims included Energias de Portugal, Rockstar Games or Colonial Pipeline. With nearly all the victims, production PCs, servers and drives were encrypted, and ransom was demanded. As a result, production often came to a standstill, and the companies suffered additional daily losses.
Many consumers and corporate users install a security solution for their Windows systems to defend against ransomware. In its Advanced Threat Protection tests, AV-TEST examined just how well 29 of these products offered protection against a ransomware attack. In doing so, each security solution was required to successfully hold up against the attackers in 10 practical scenarios. Most of the products performed very well, but there were a few missteps here and there, dampening the result.
29 products put to a practical test
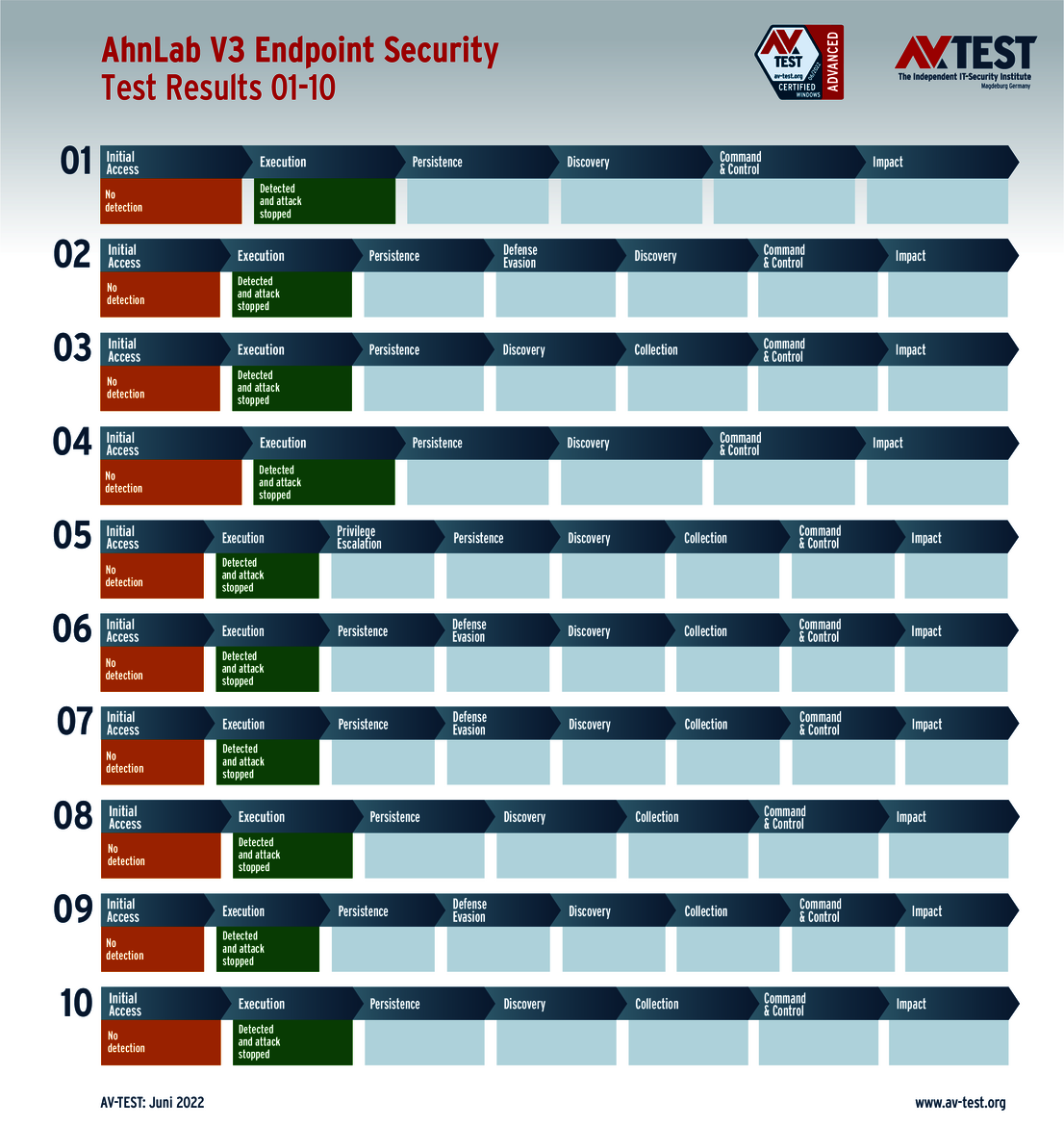
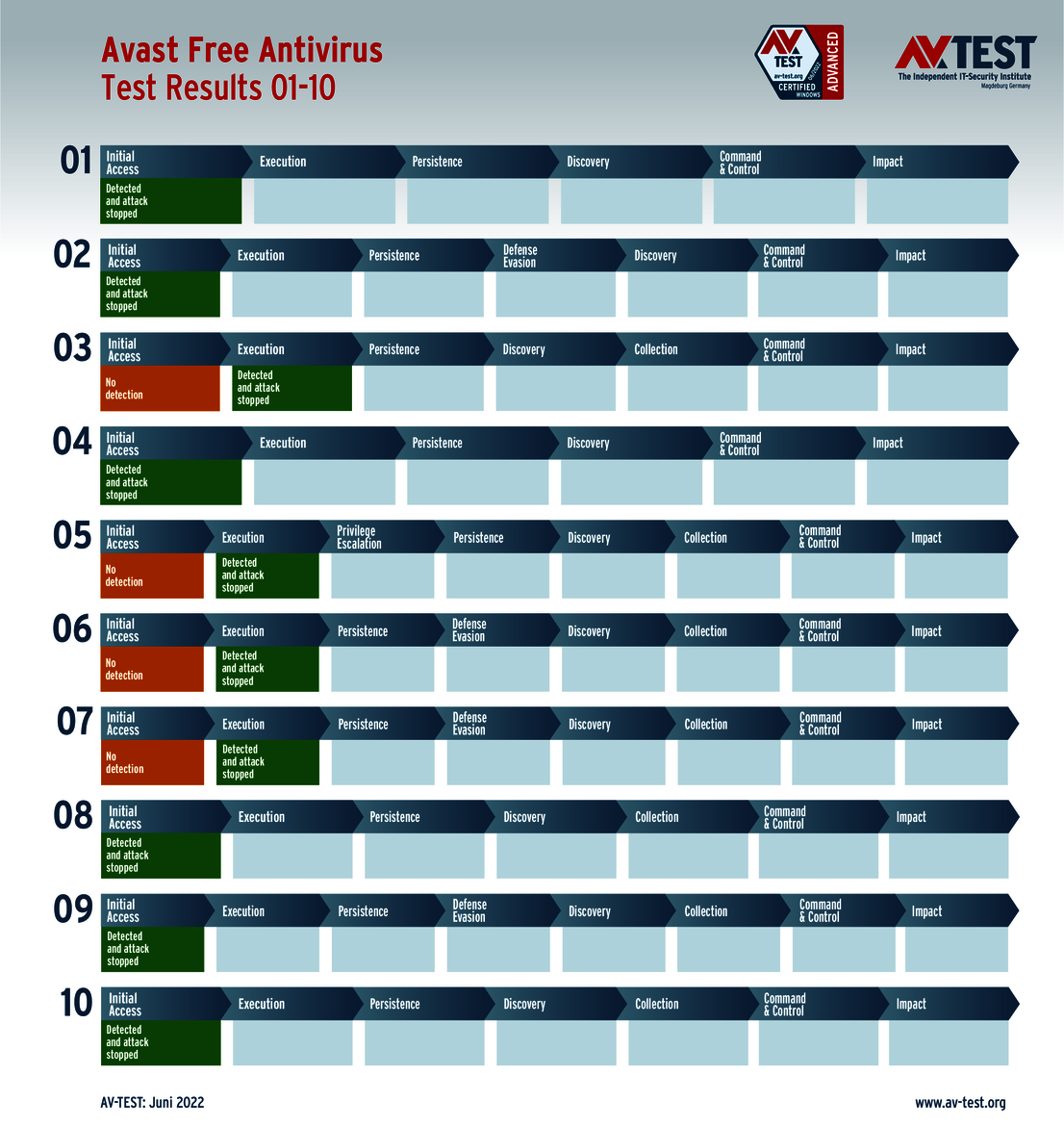
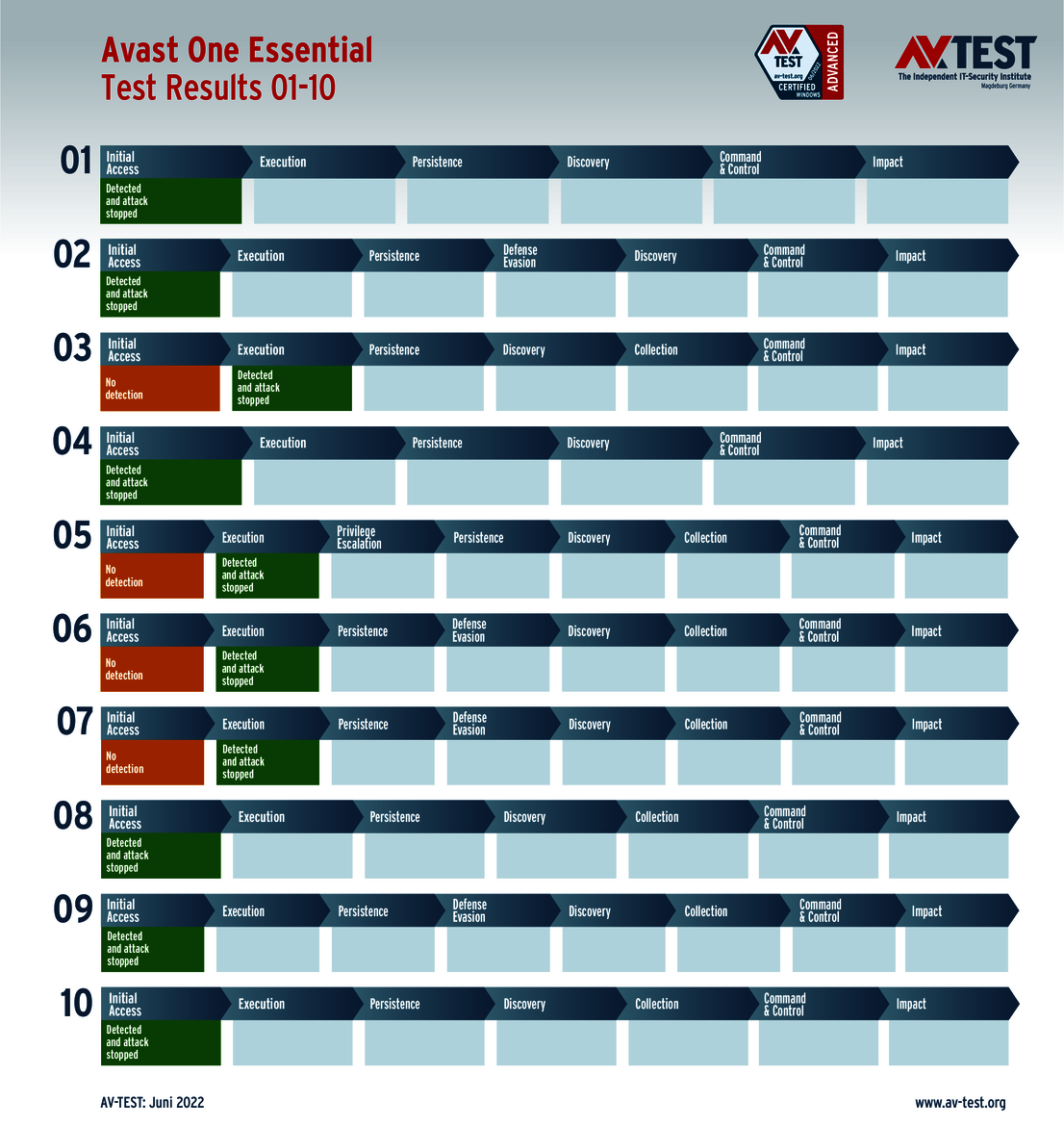
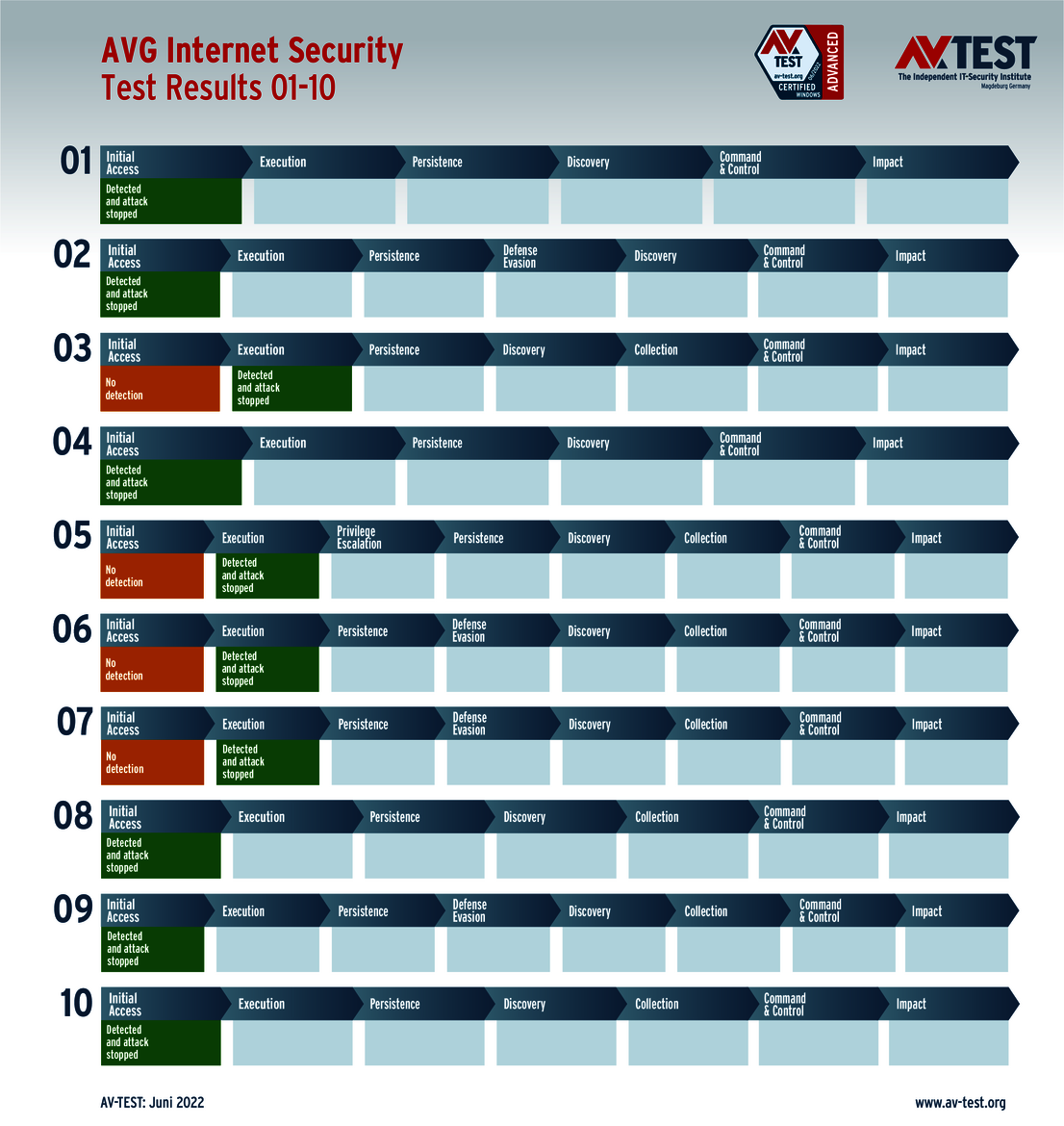
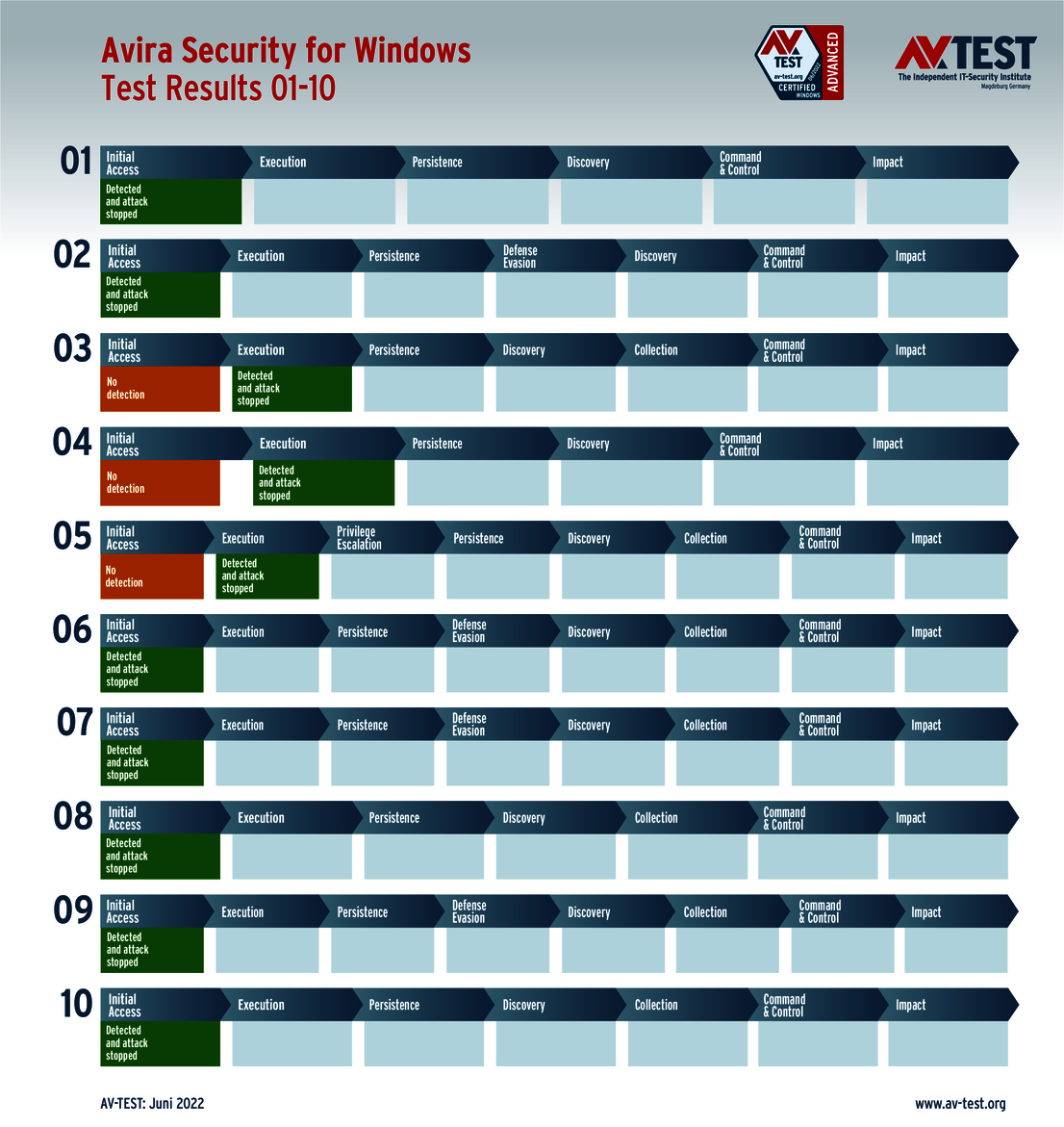
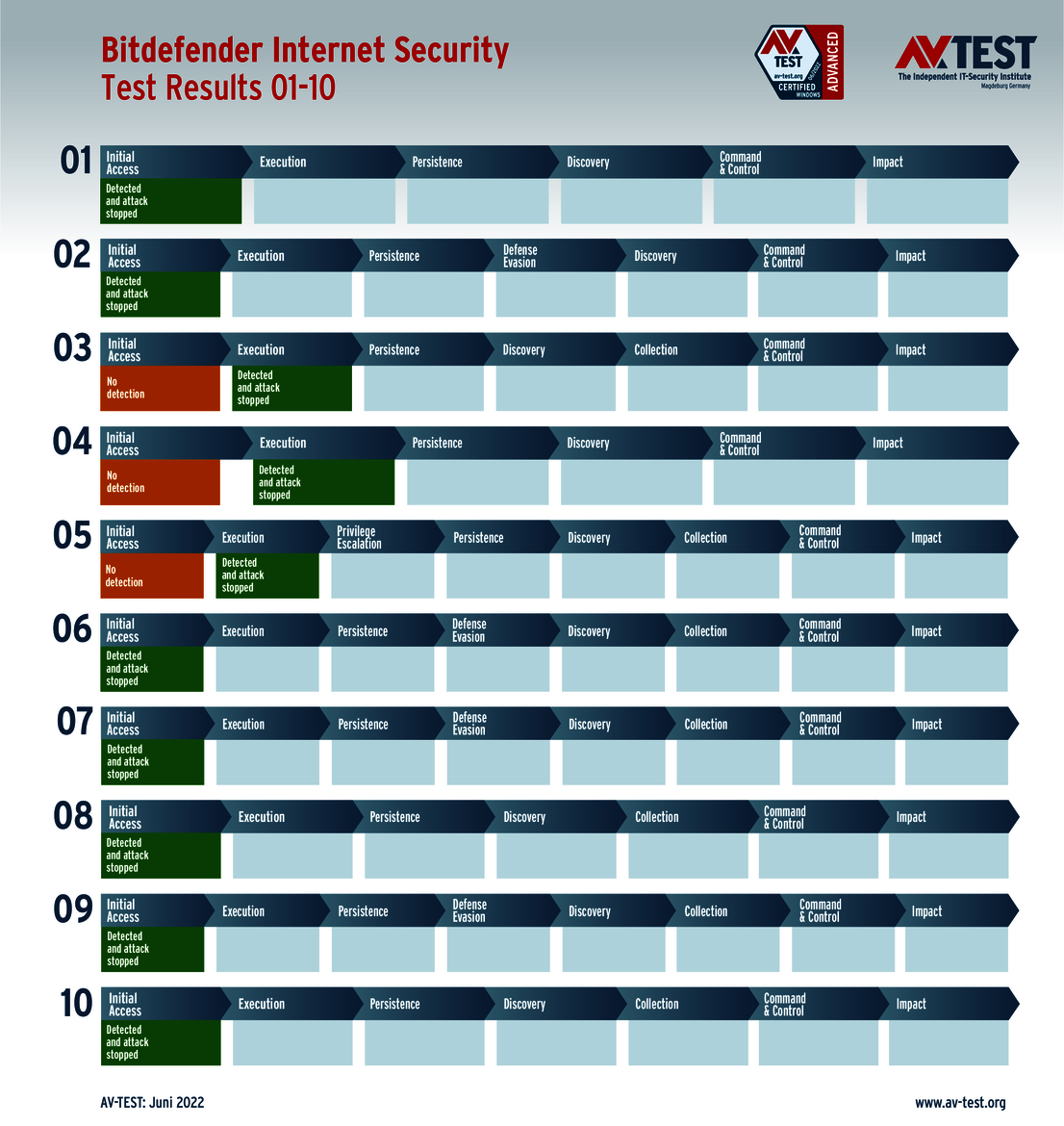
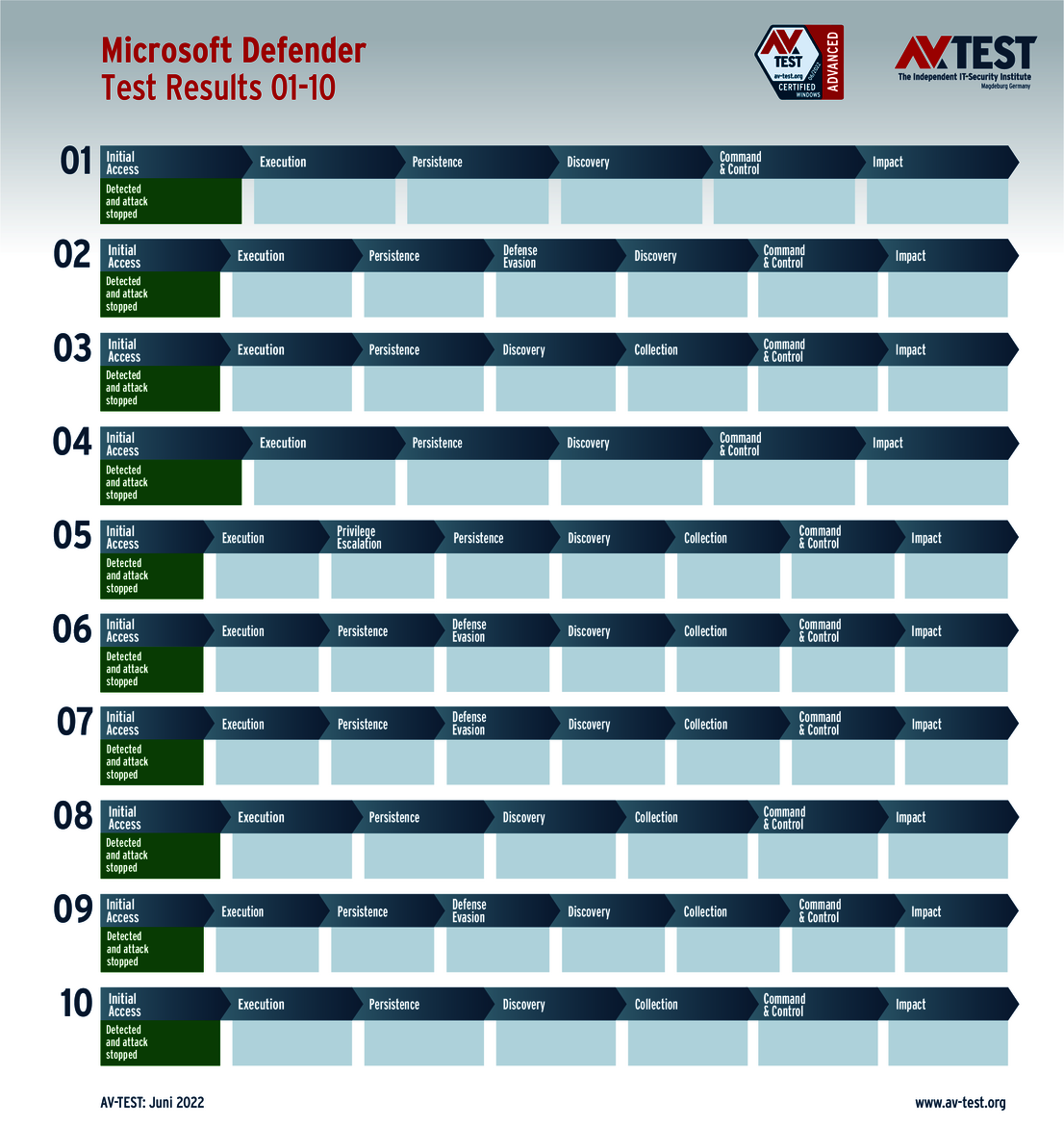
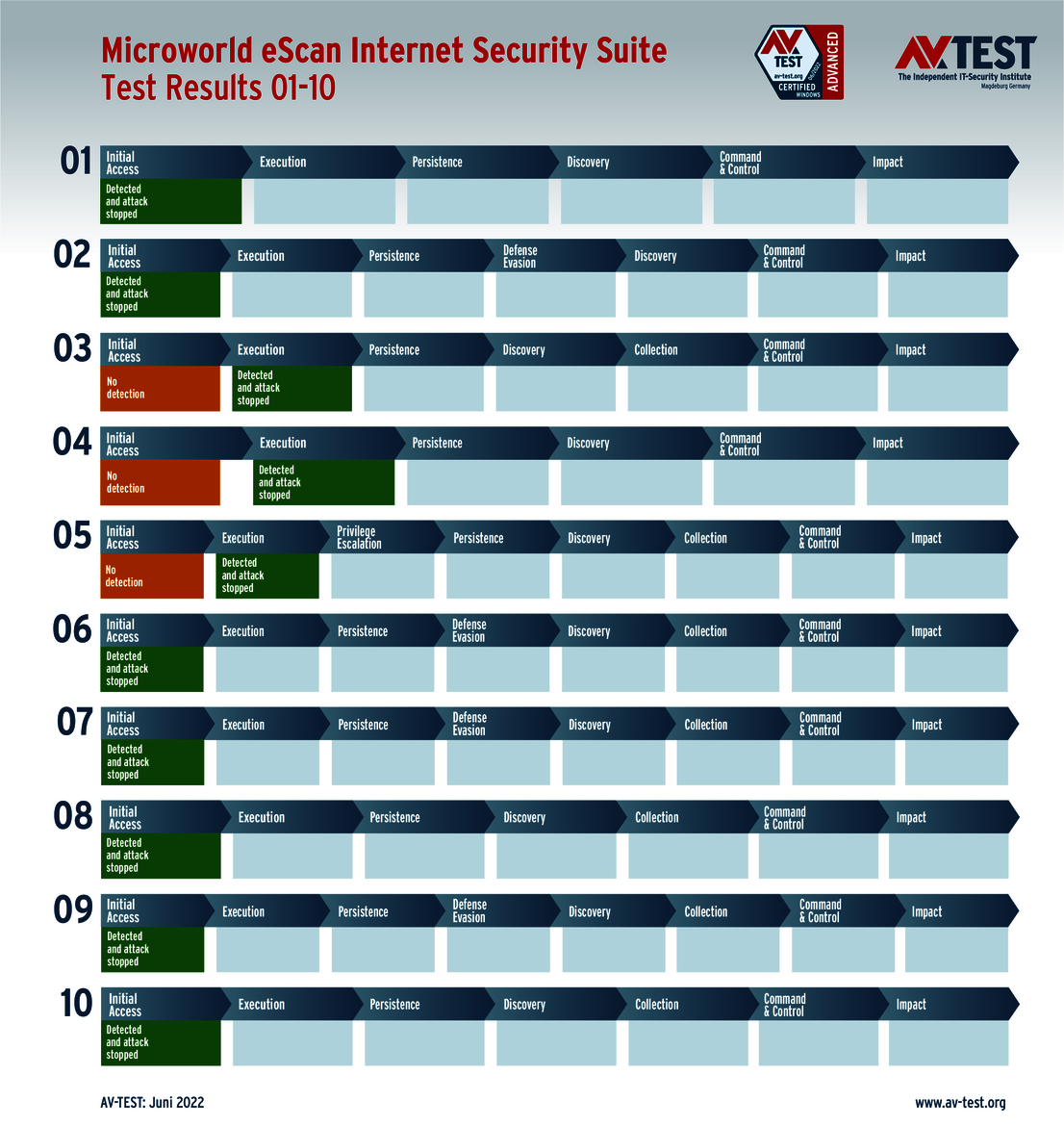
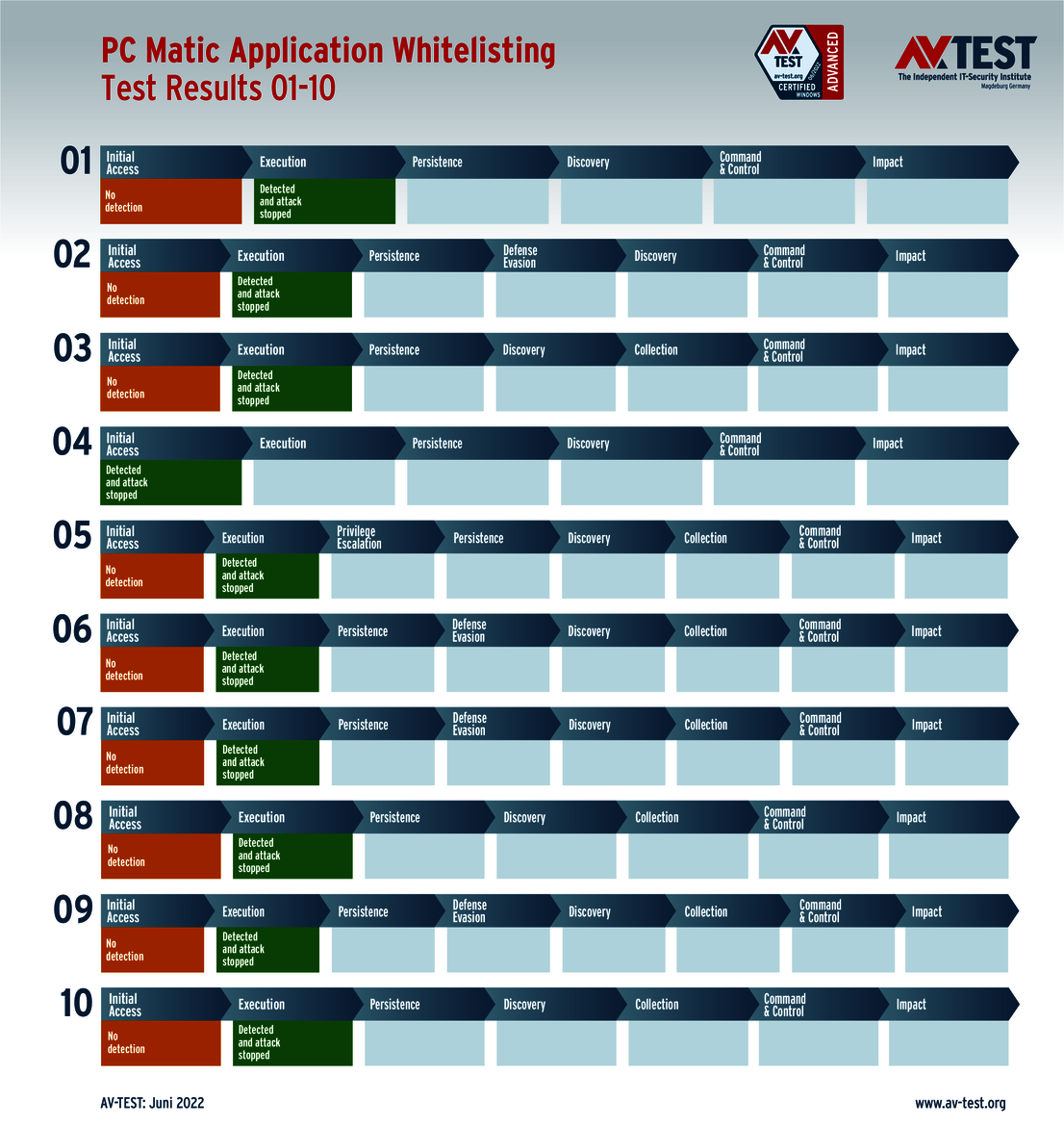
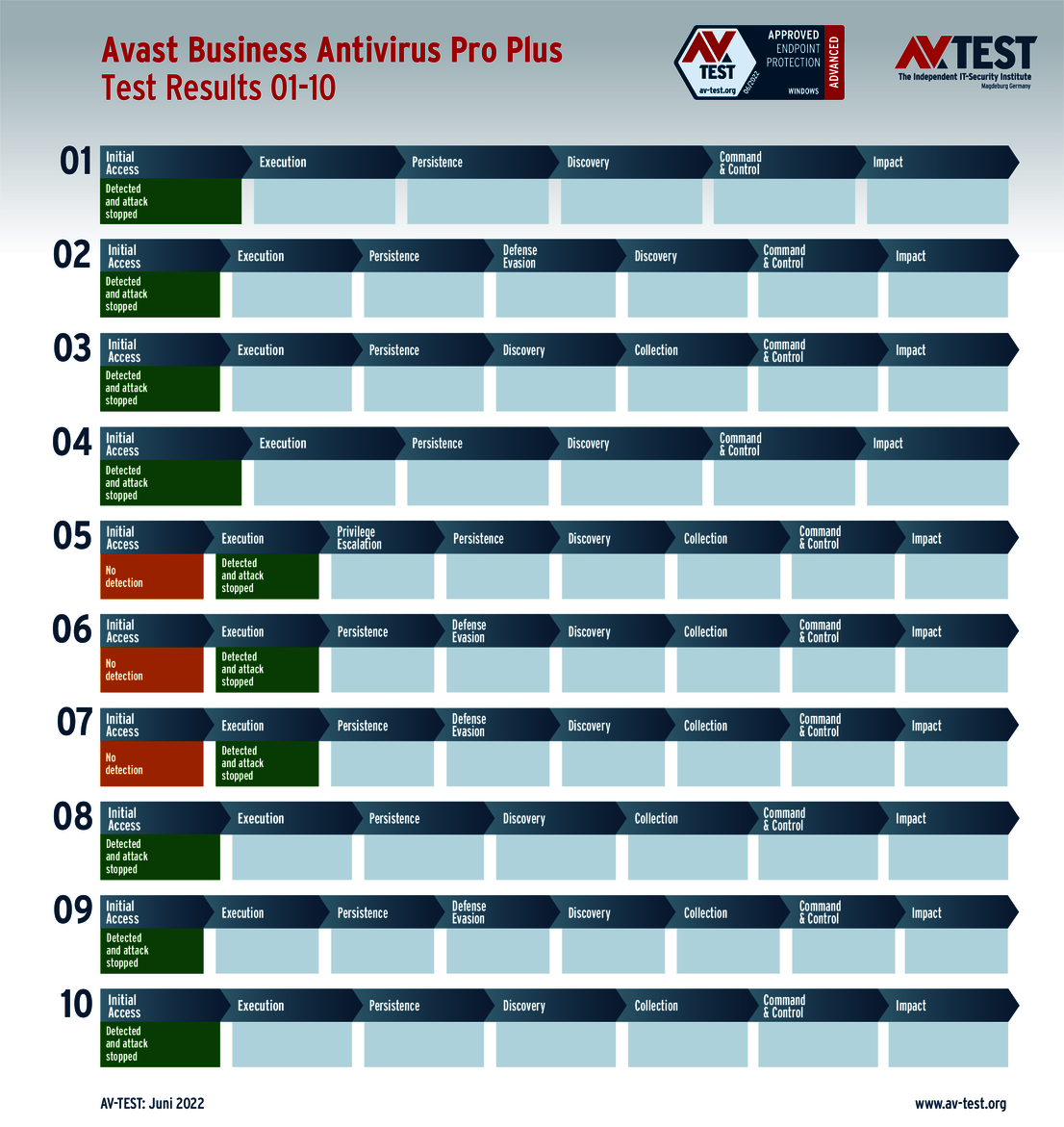
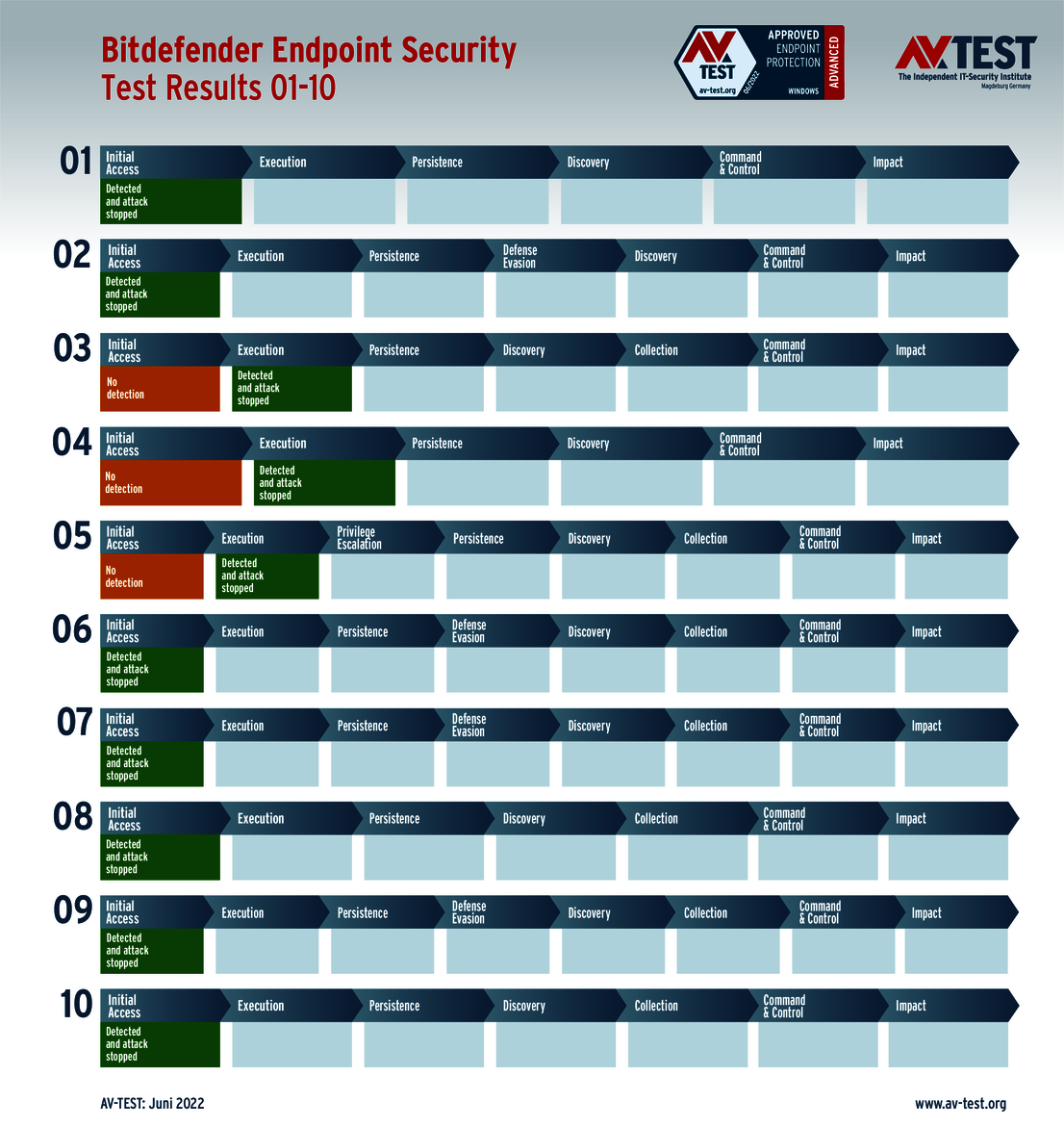
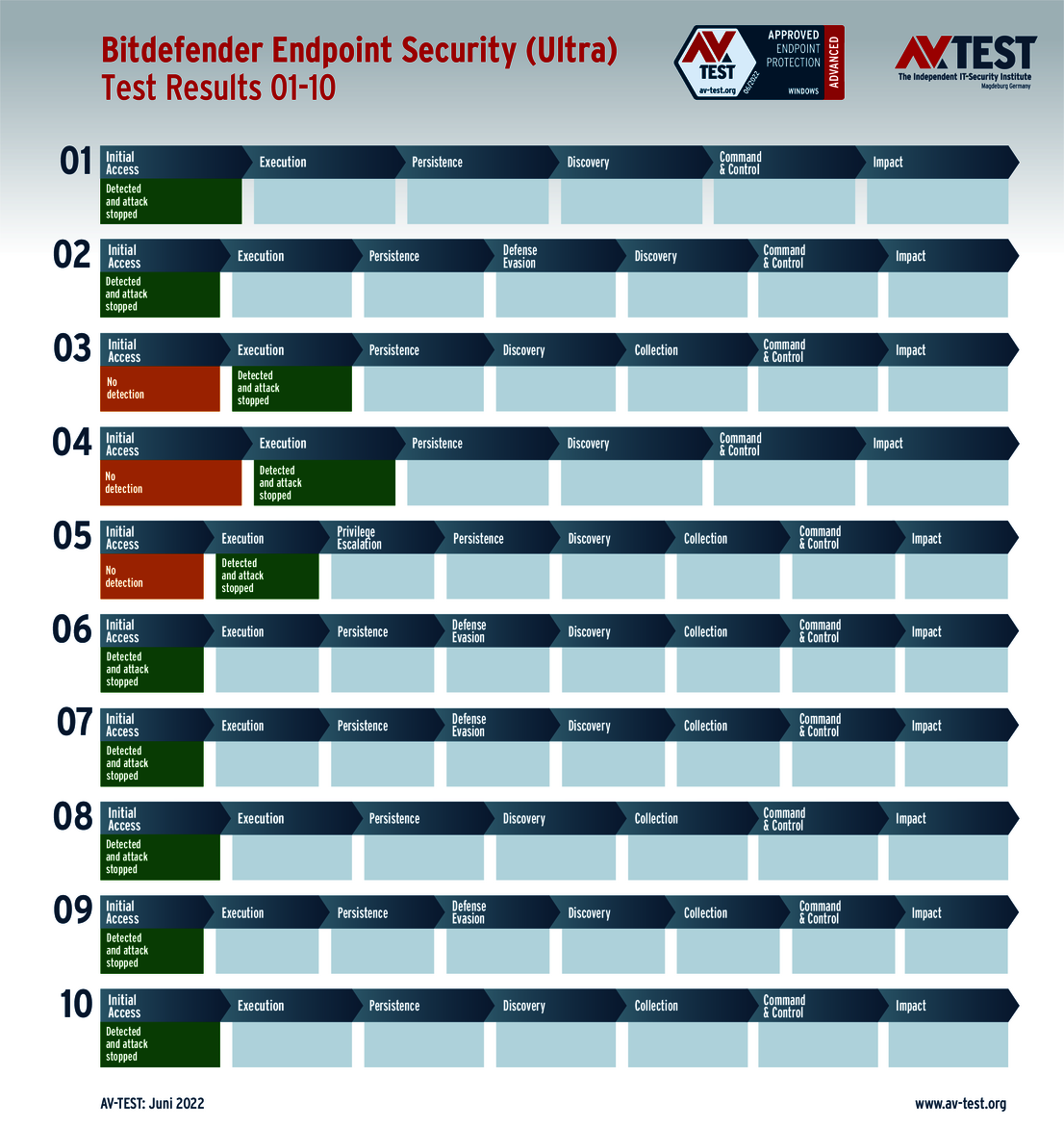
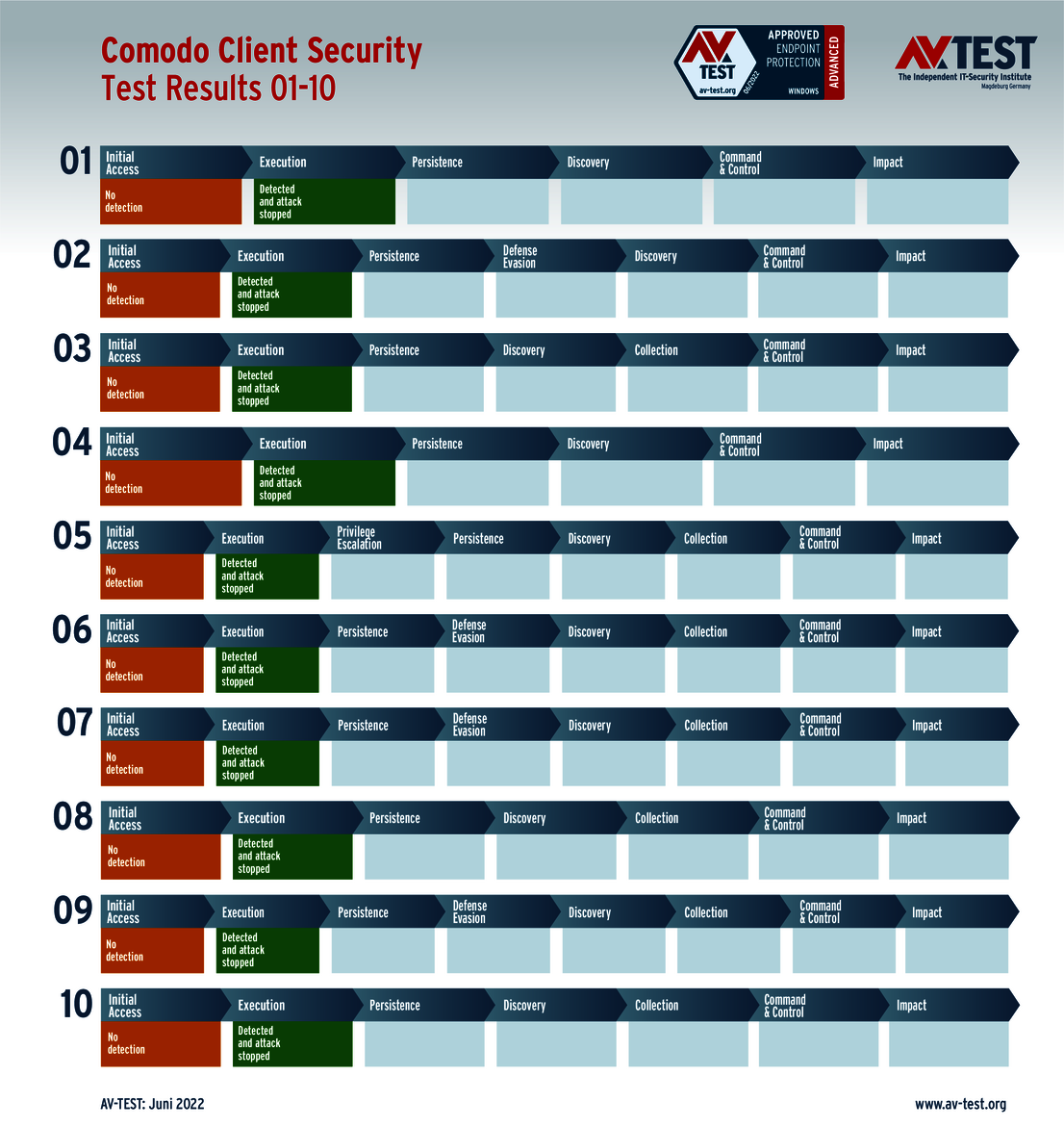
In a classical detection test, the only result is "detected" or "not detected". In this advanced test, it's a different story. In the first step, as always, detection or non-detection is documented. There is an opportunity, however, for the protection program to detect the attack after all through additional actions, blocking it and at least partially deleting the attackers.
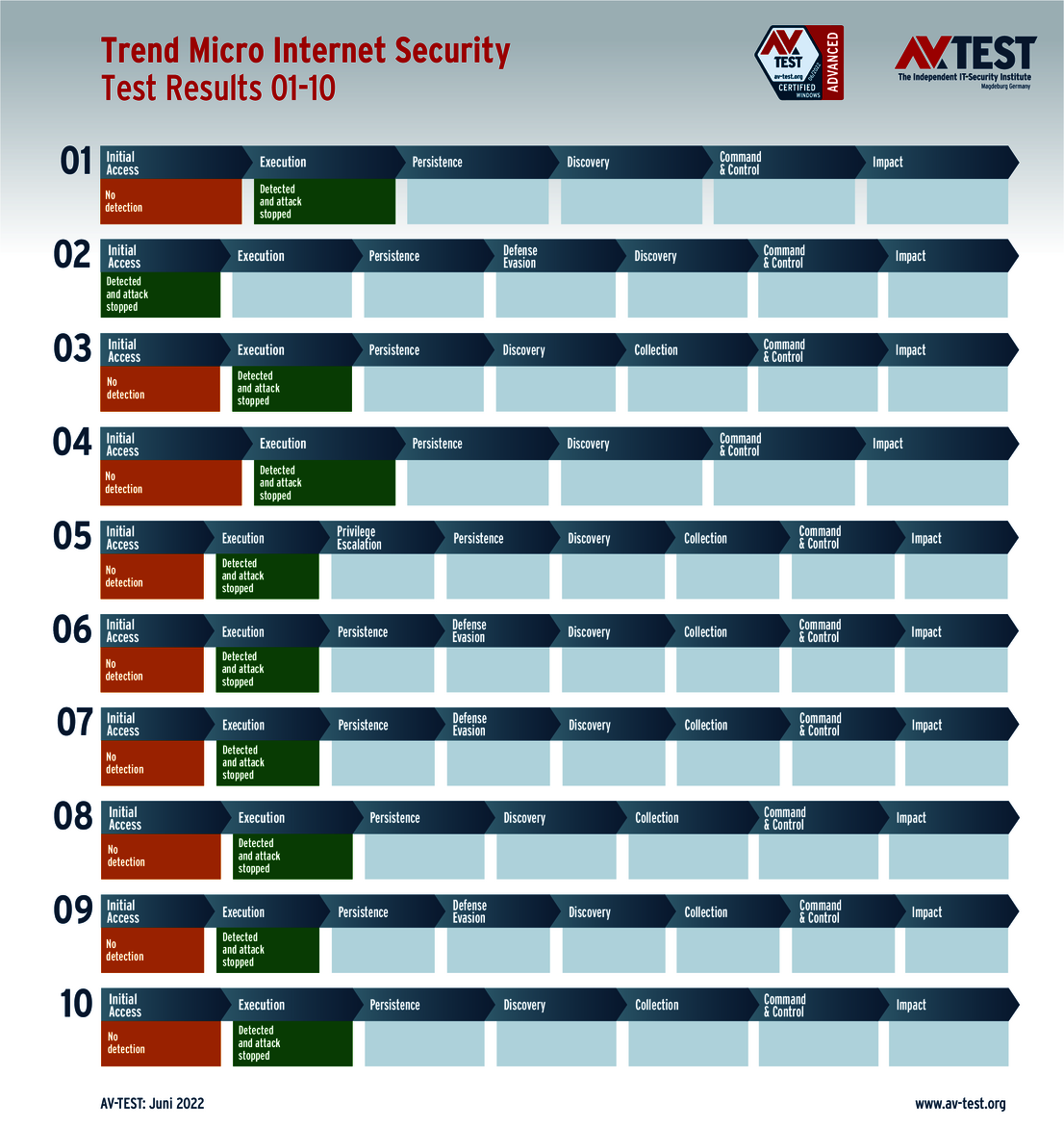
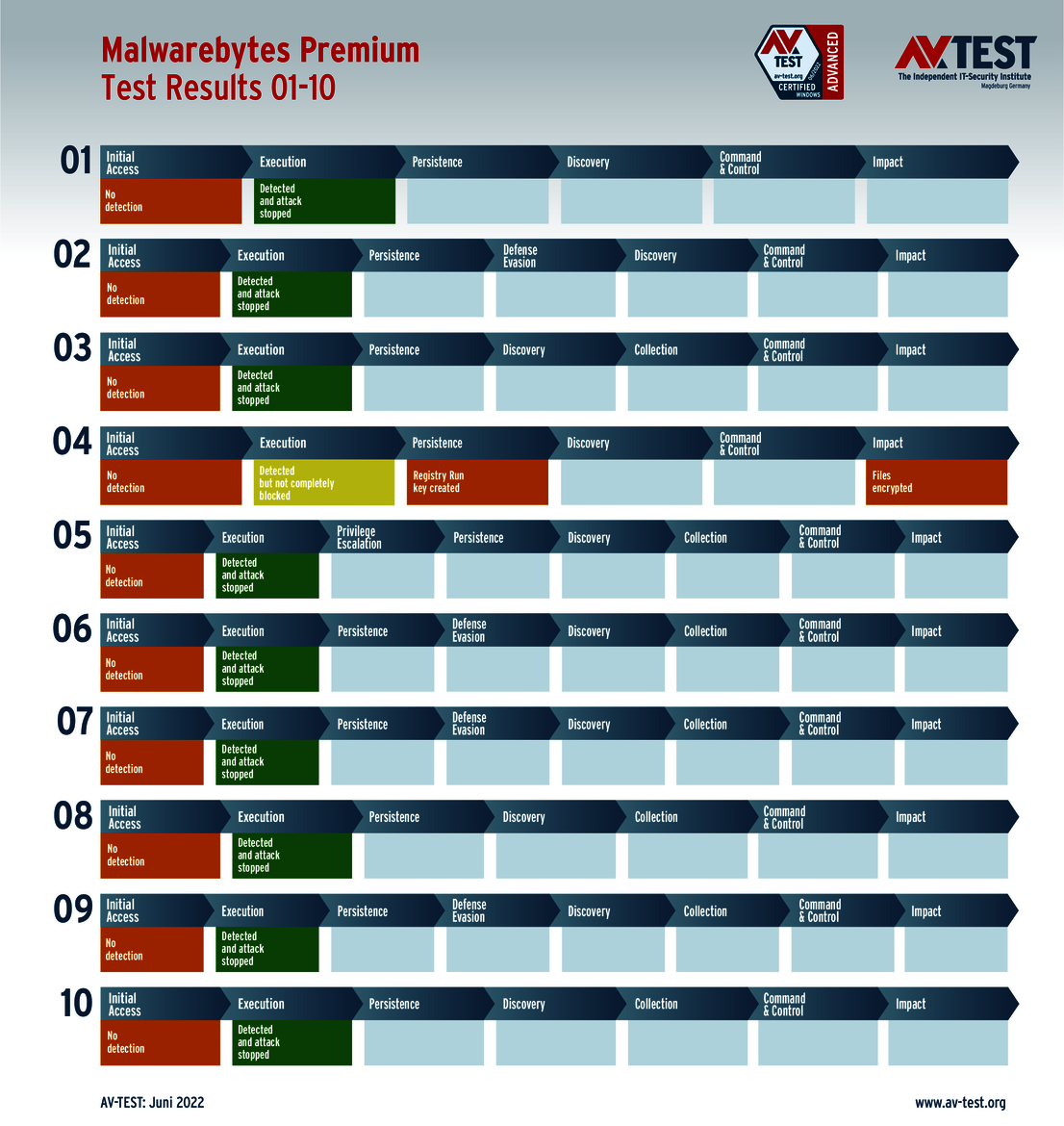
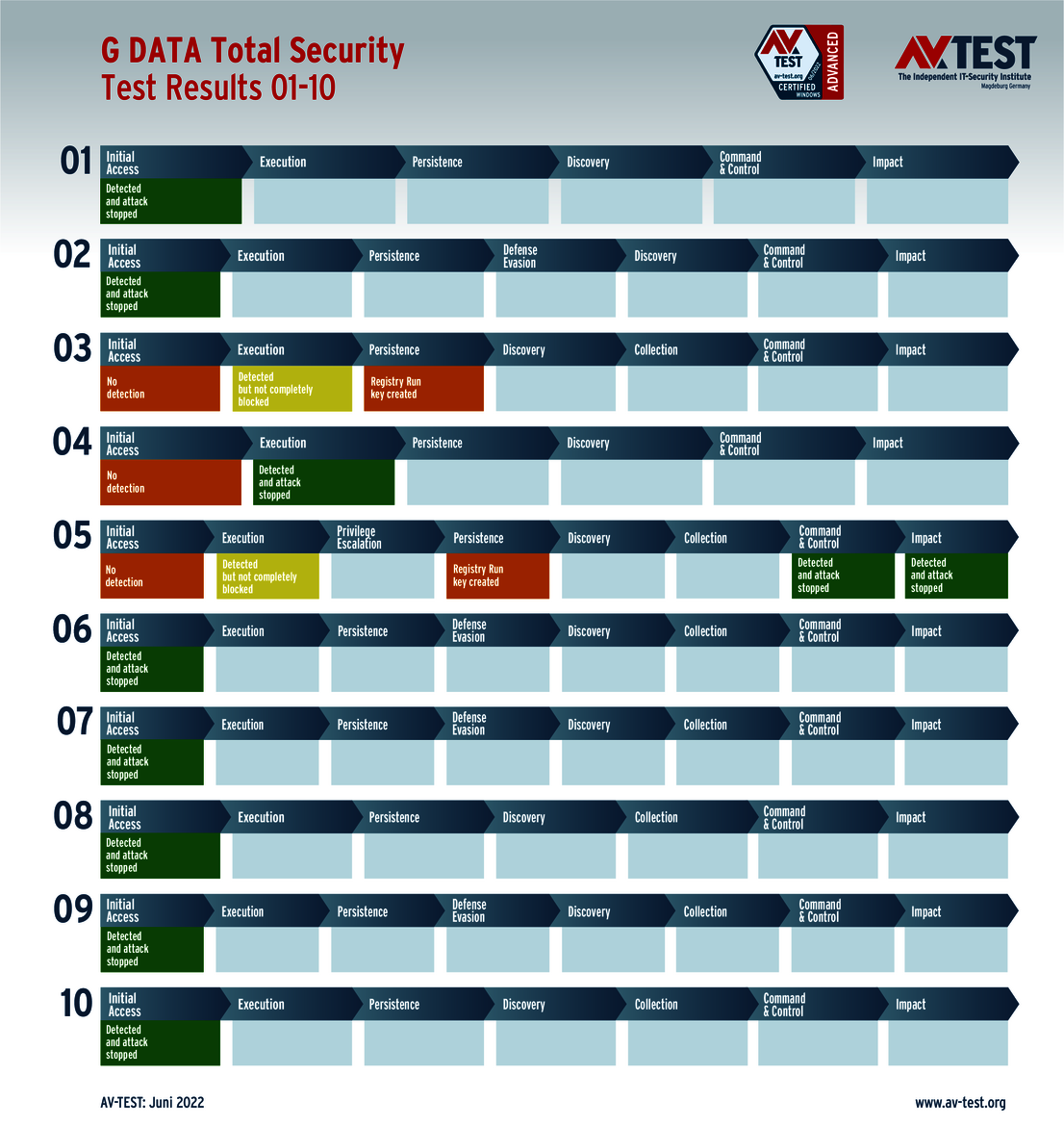
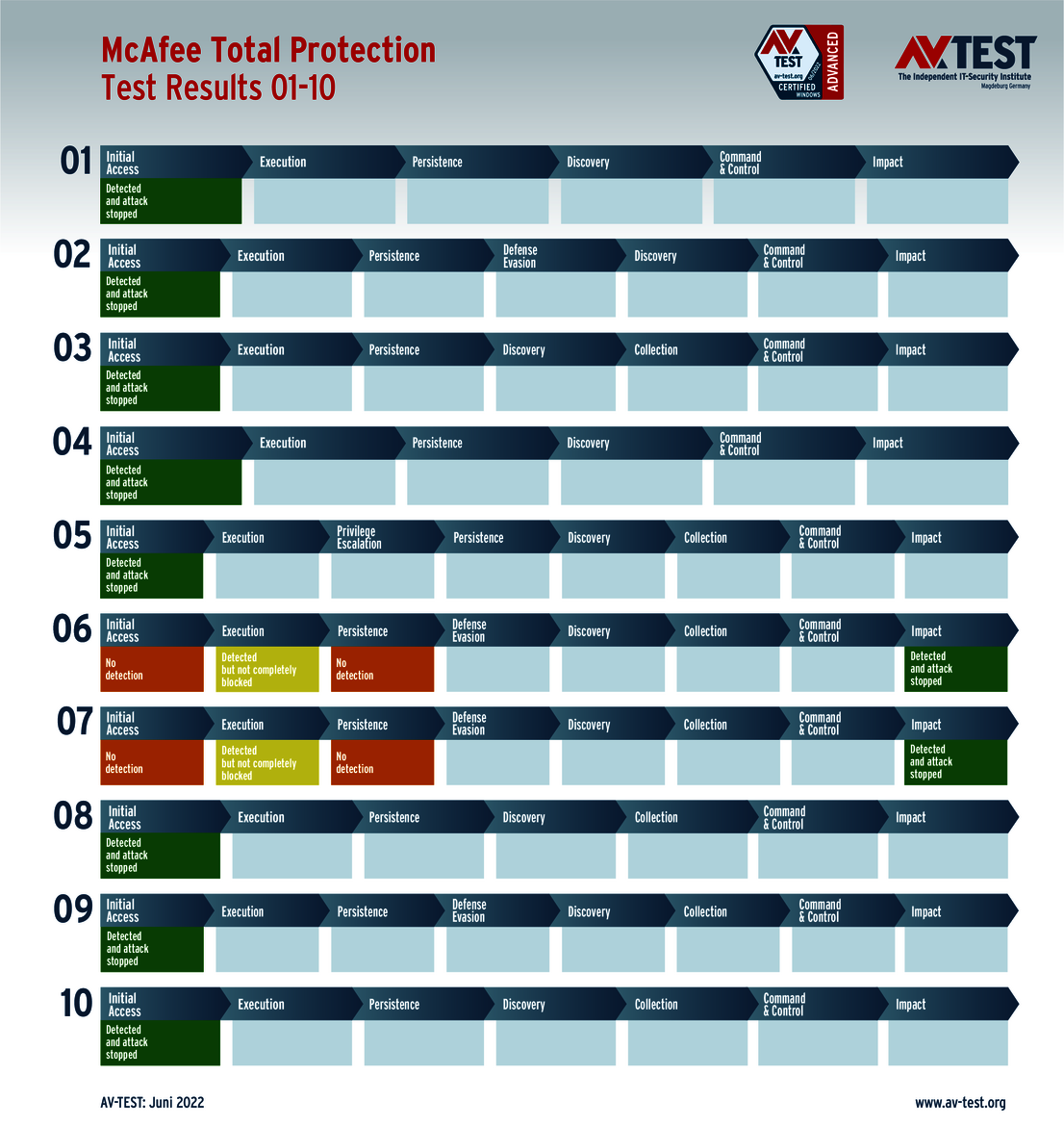
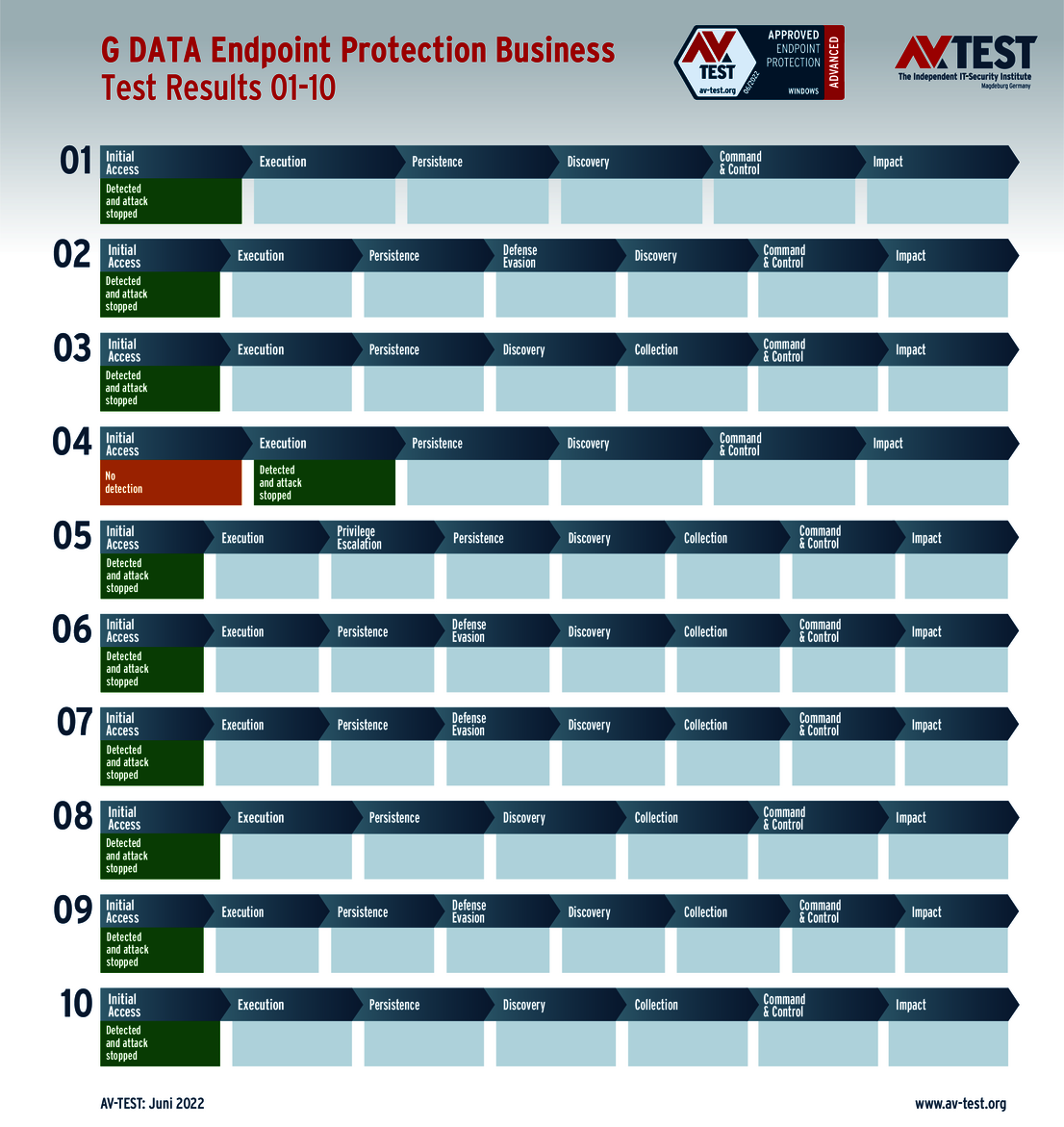
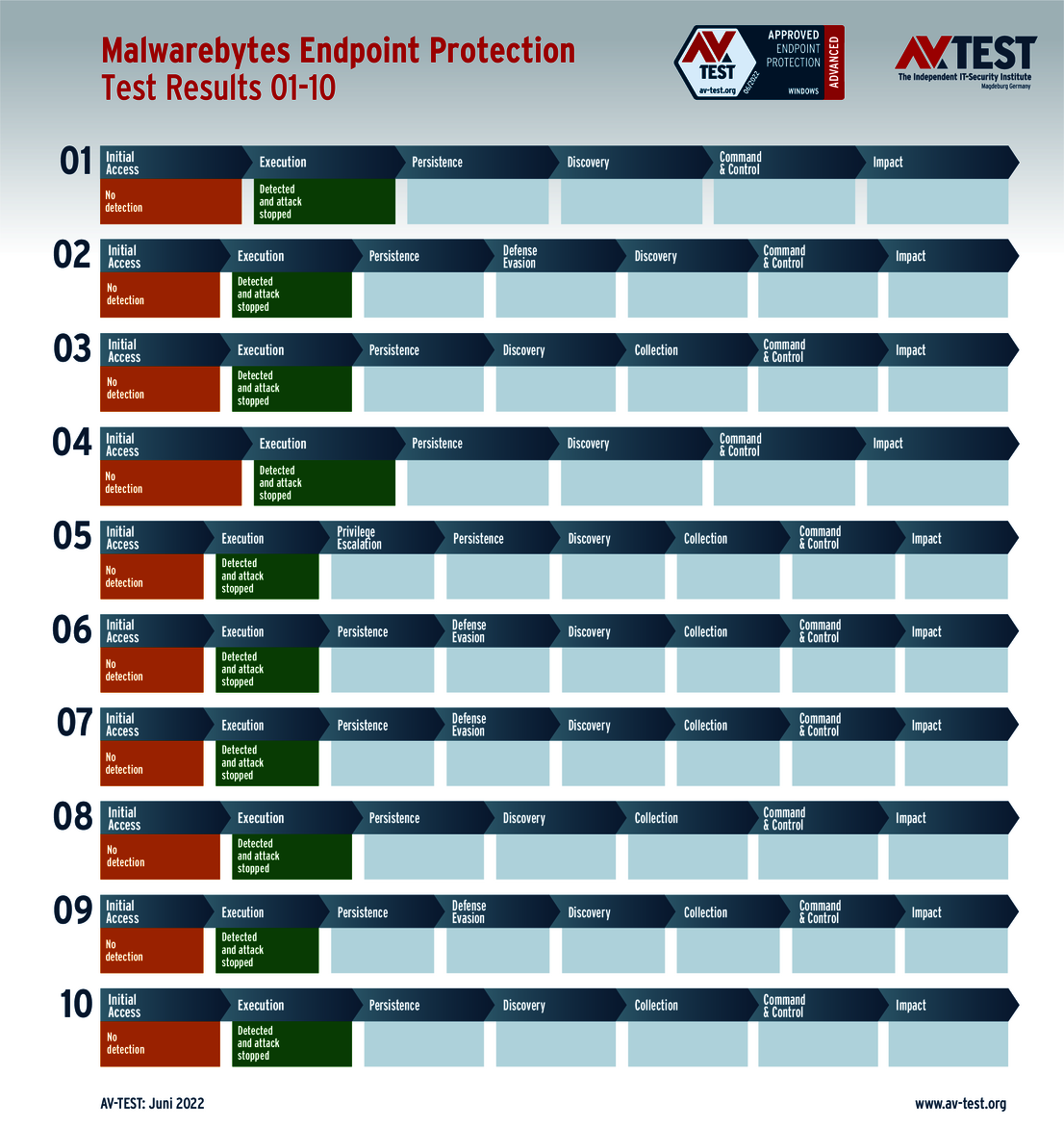
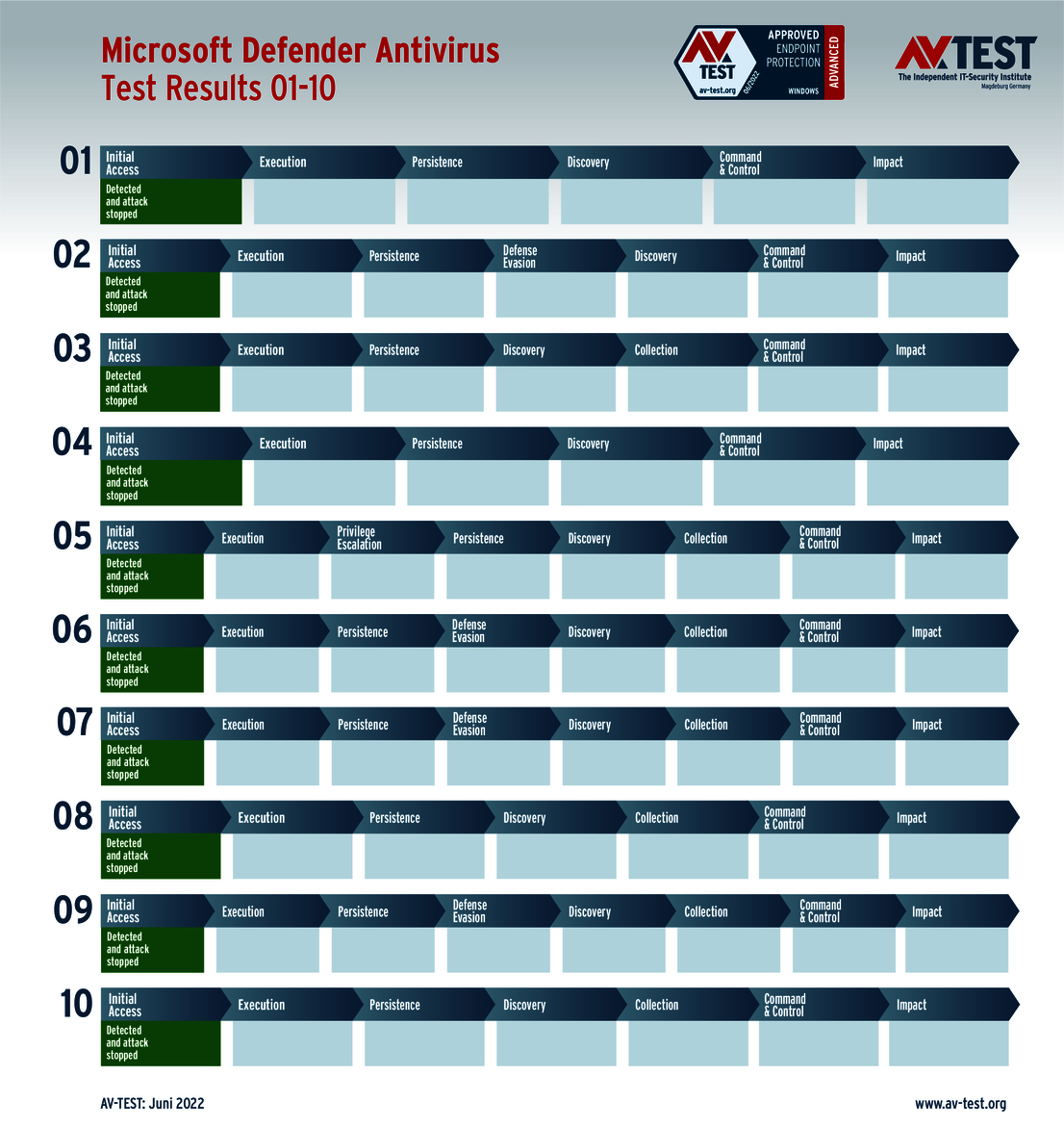
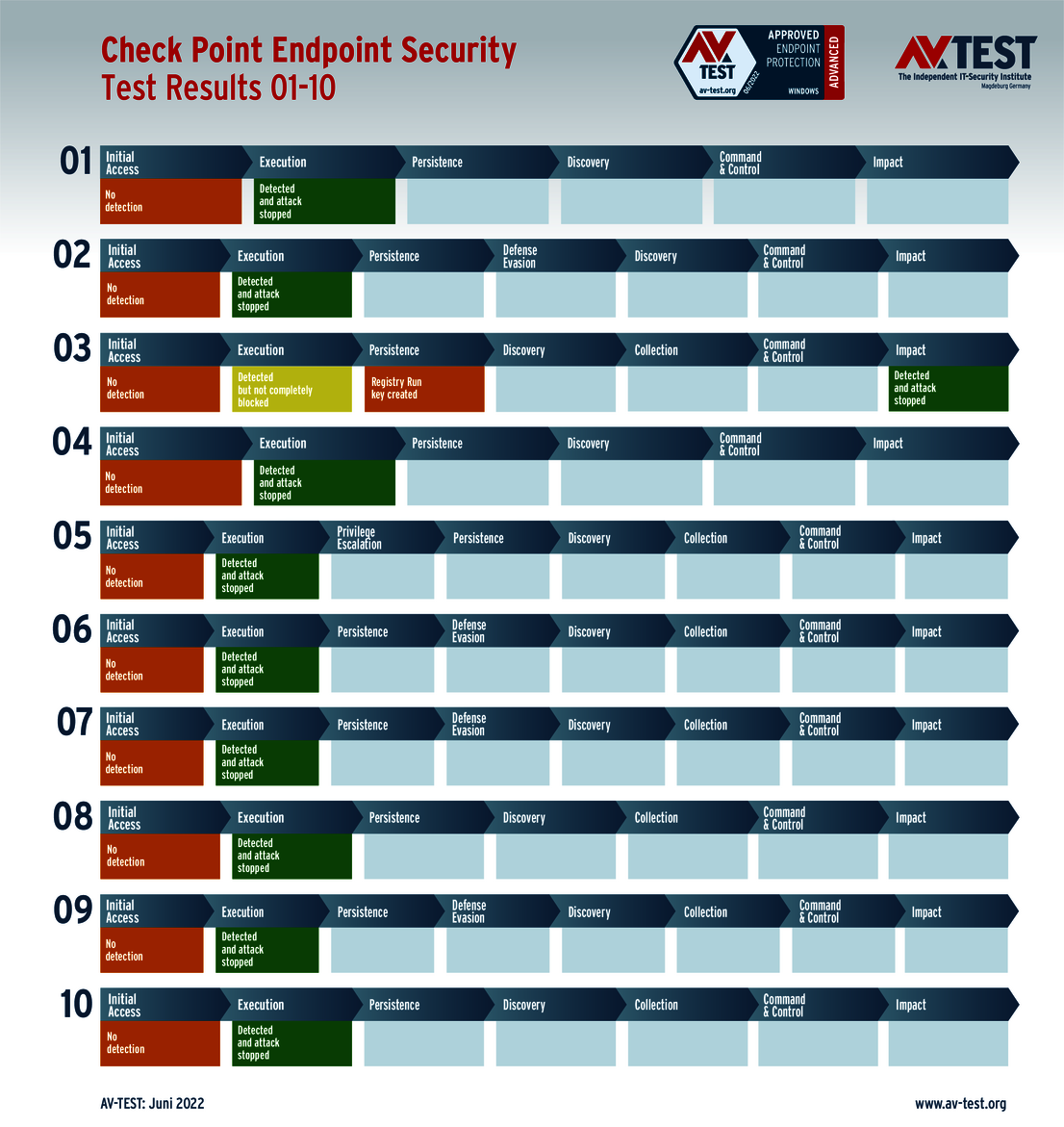
That is why the Advanced Threat Protection test shows all the attack steps of ransomware in the evaluation charts, thereby indicating the point at which the security solution thwarted the attack fully, partially or perhaps not at all. In the process, all the steps are assessed, and the lab awards up to 4 points in each scenario in this test. Thus, in the 10 scenarios, the products are able to achieve up to 40 points for their protection score.
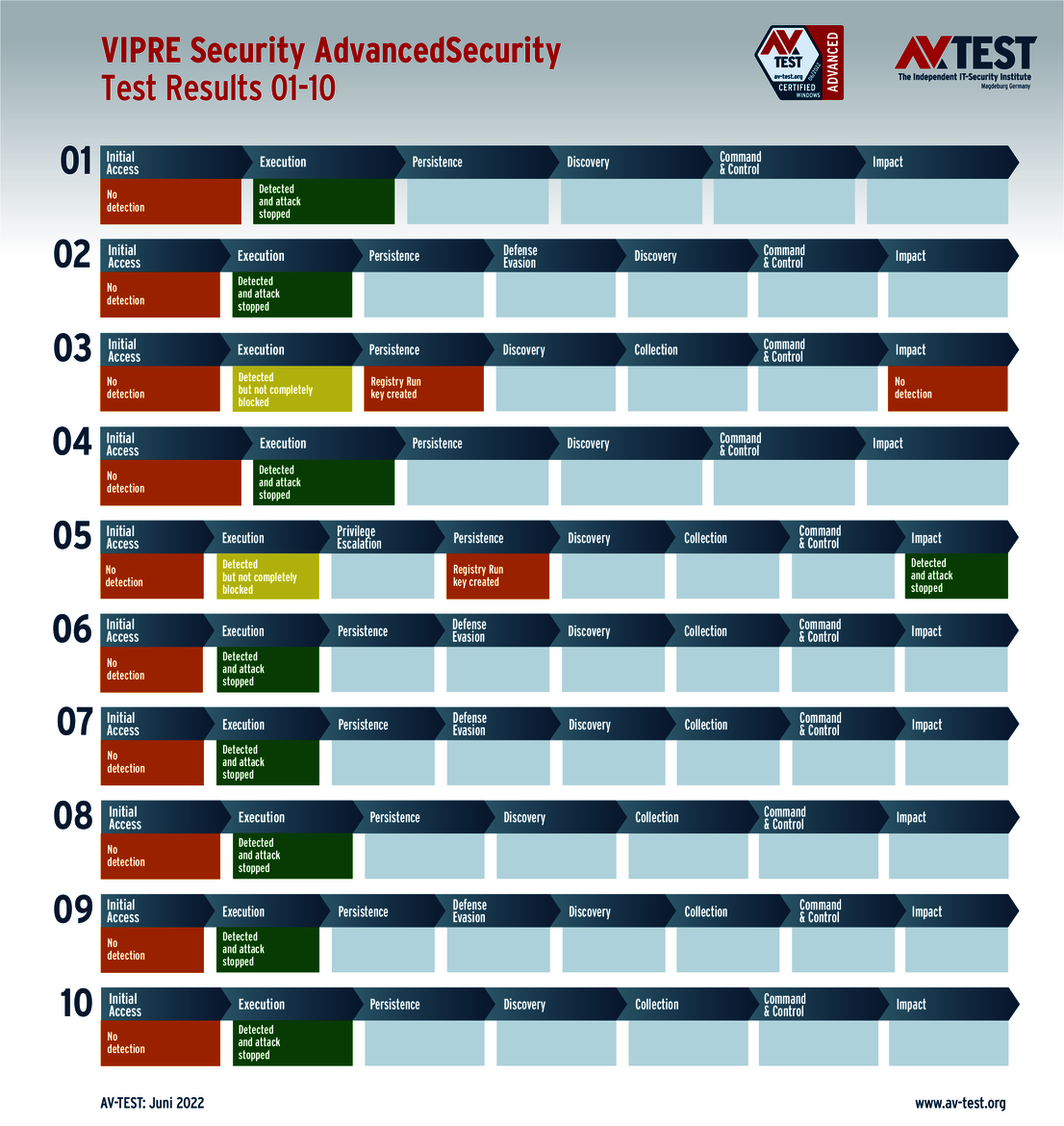
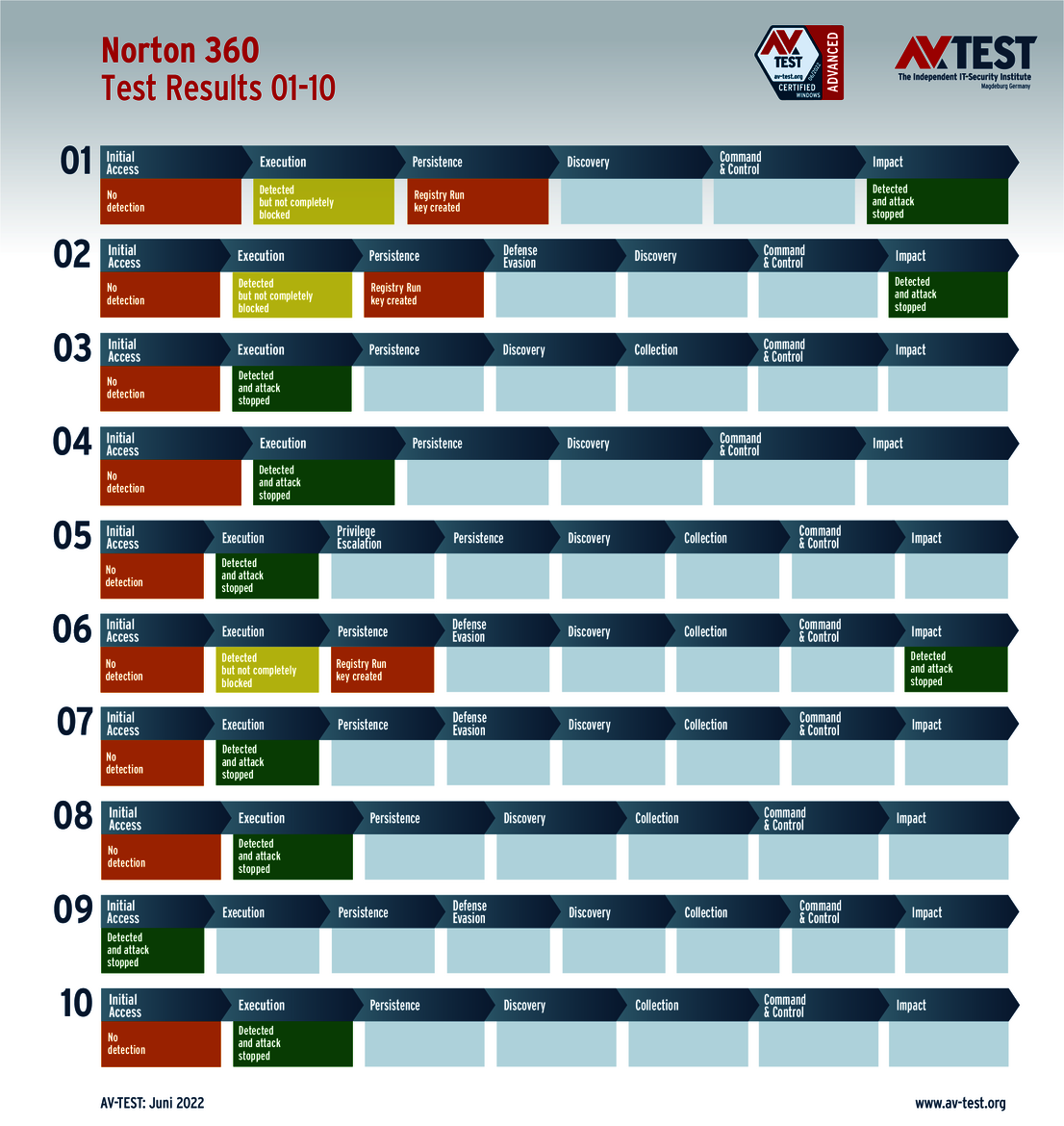
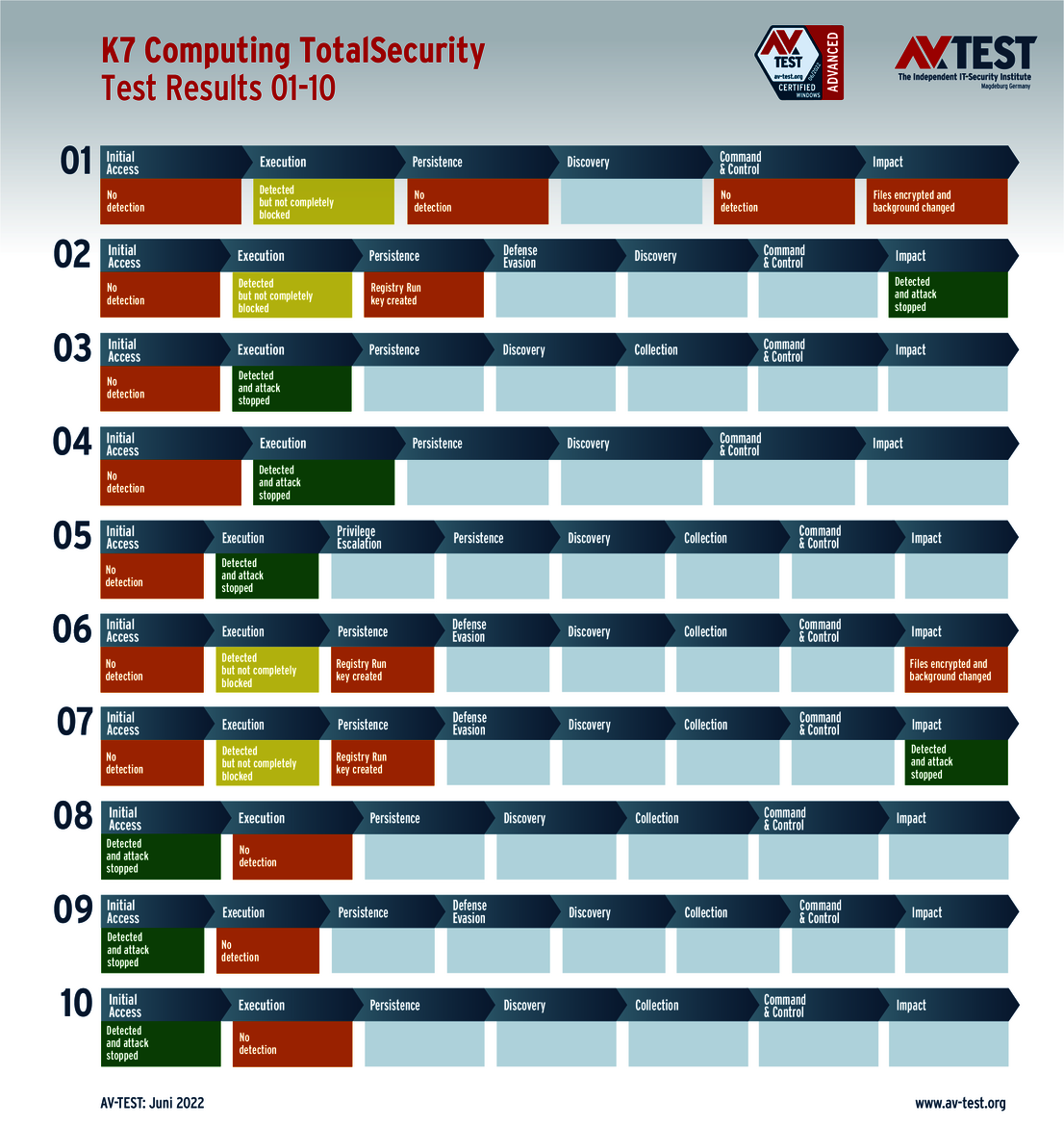
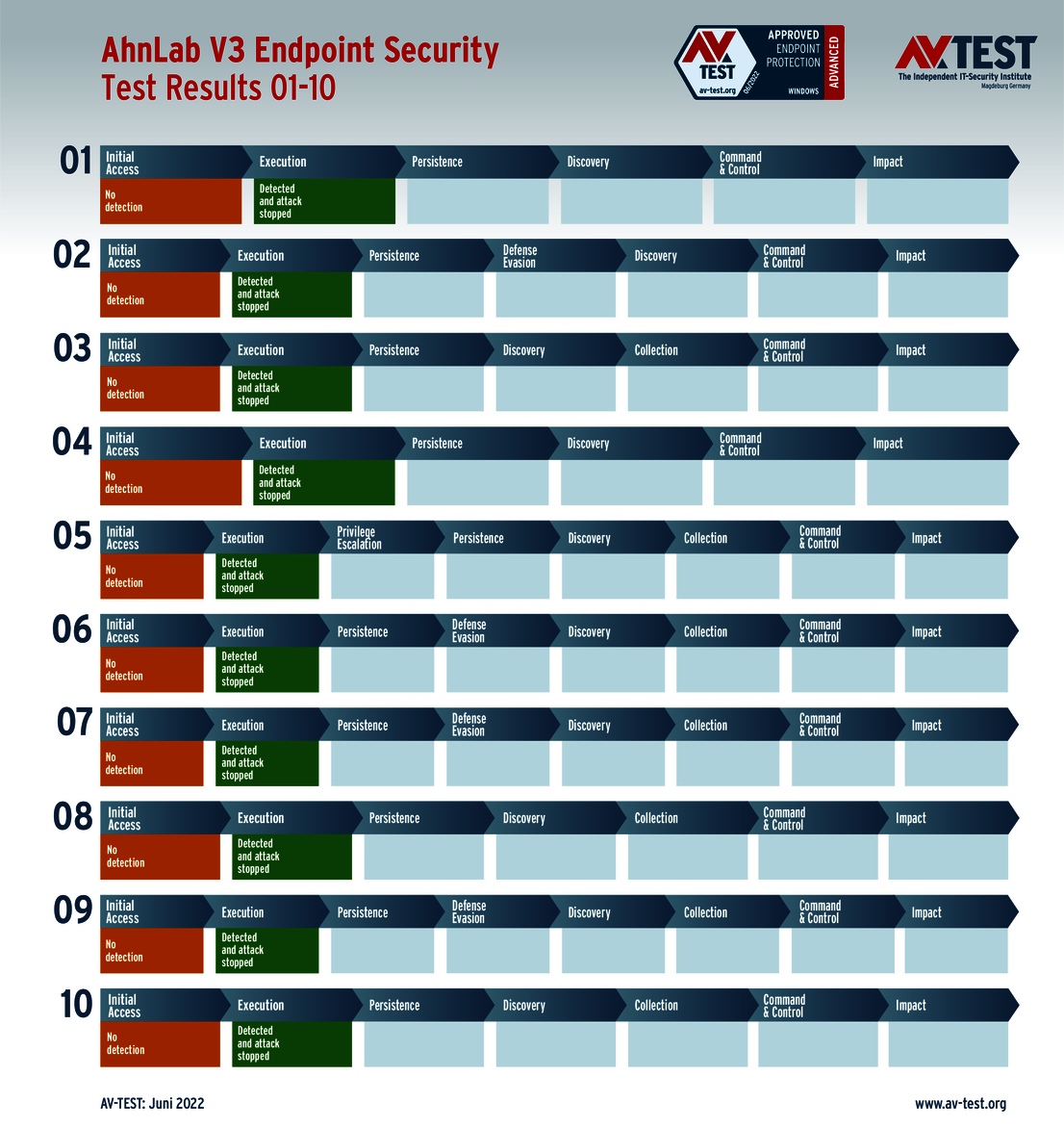
The products examined for consumer users come from: Ahnlab, Avast (with 2 versions), AVG, Avira, Bitdefender, G DATA, K7 Computing, Malwarebytes, McAfee, Microsoft, Microworld, NortonLifeLock, PC Matic, Trend Micro and VIPRE Security.
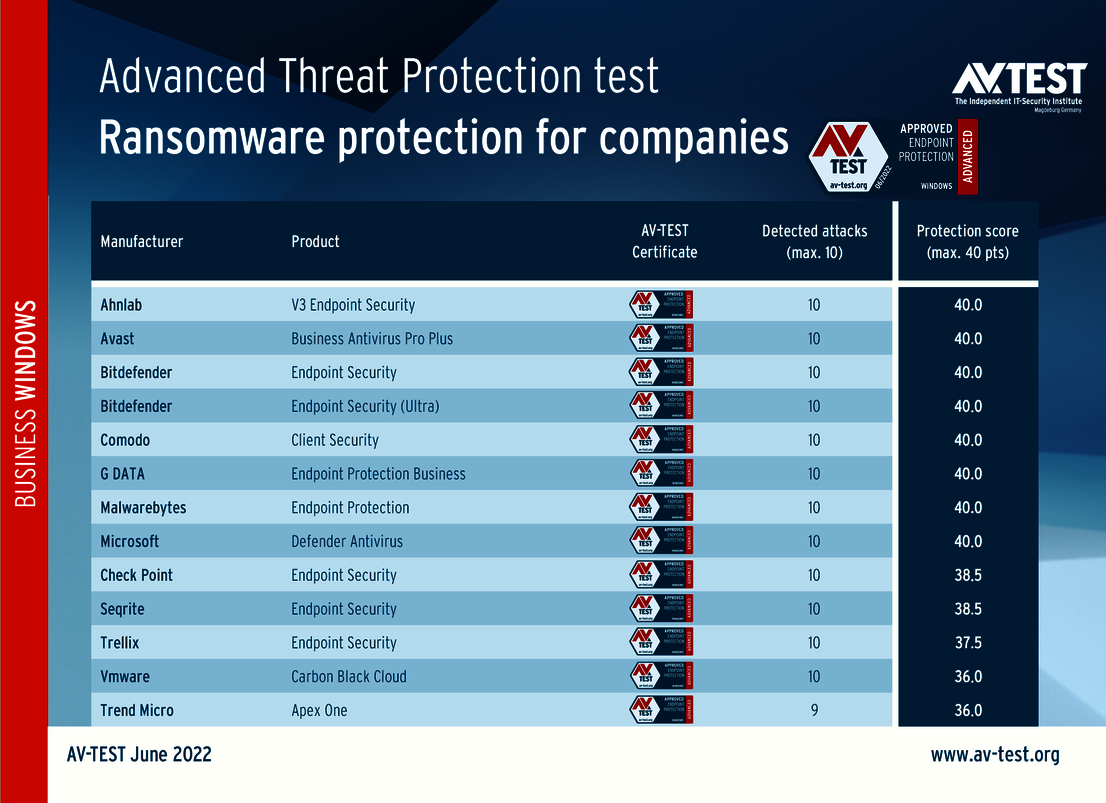
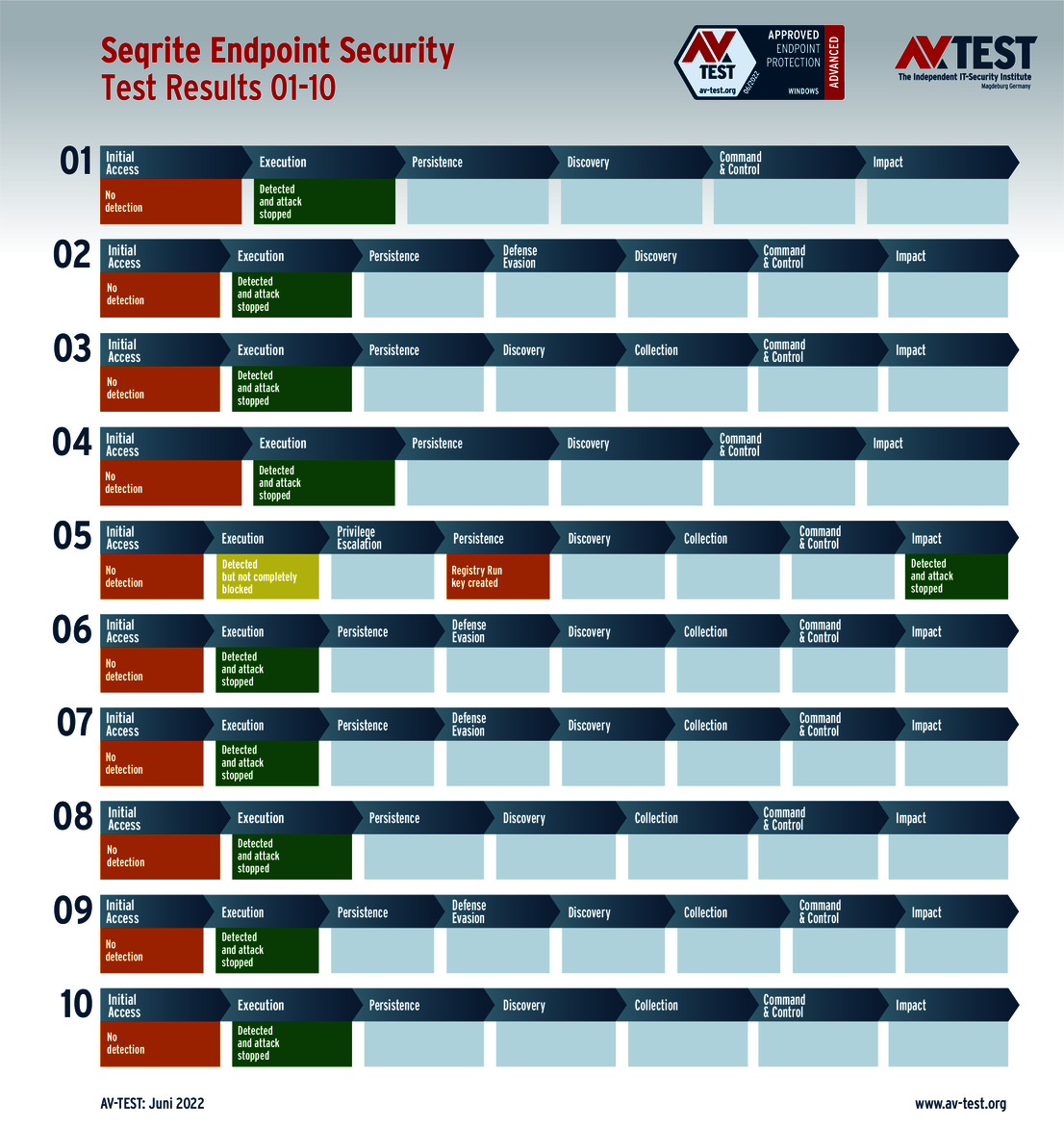
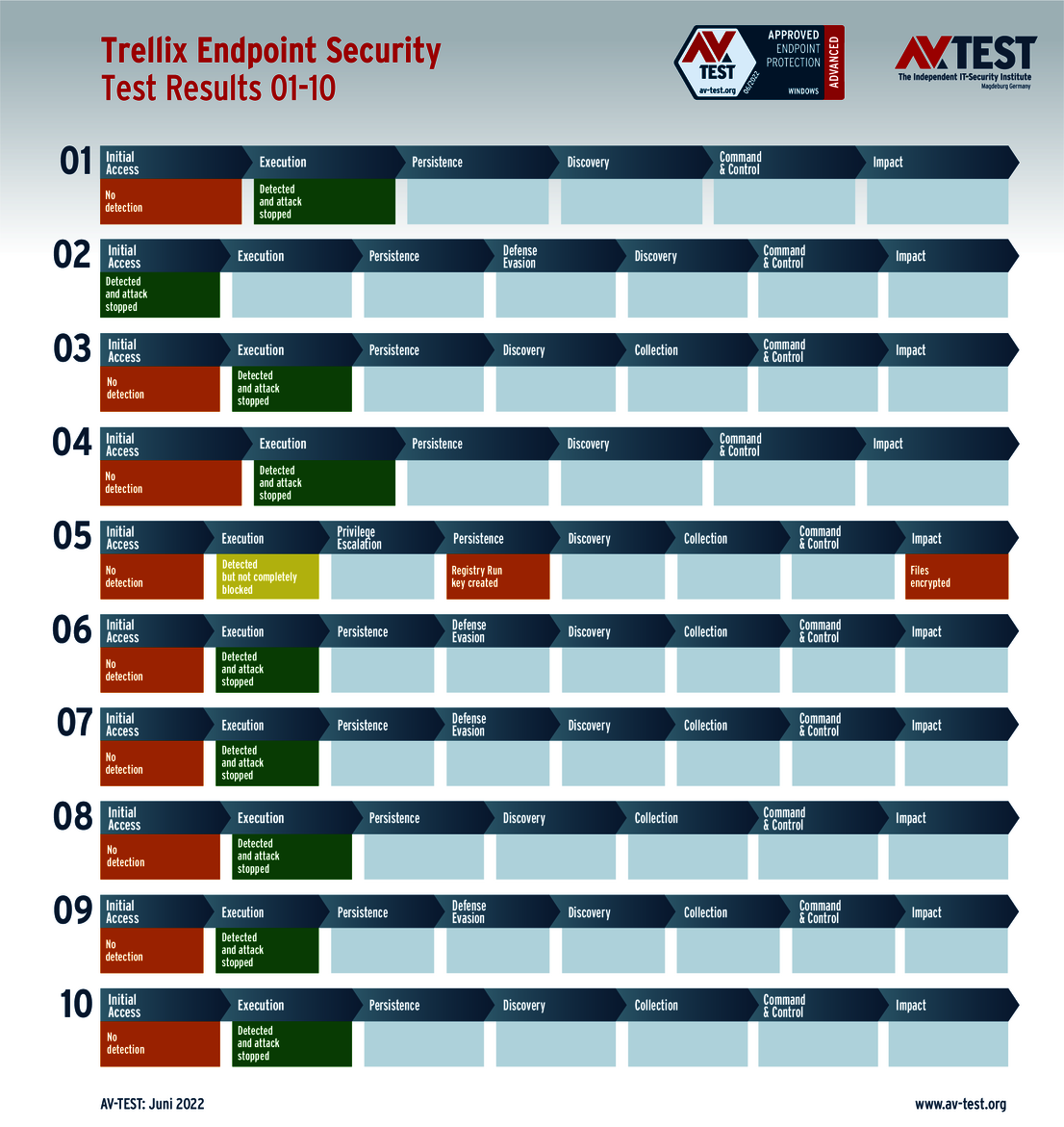
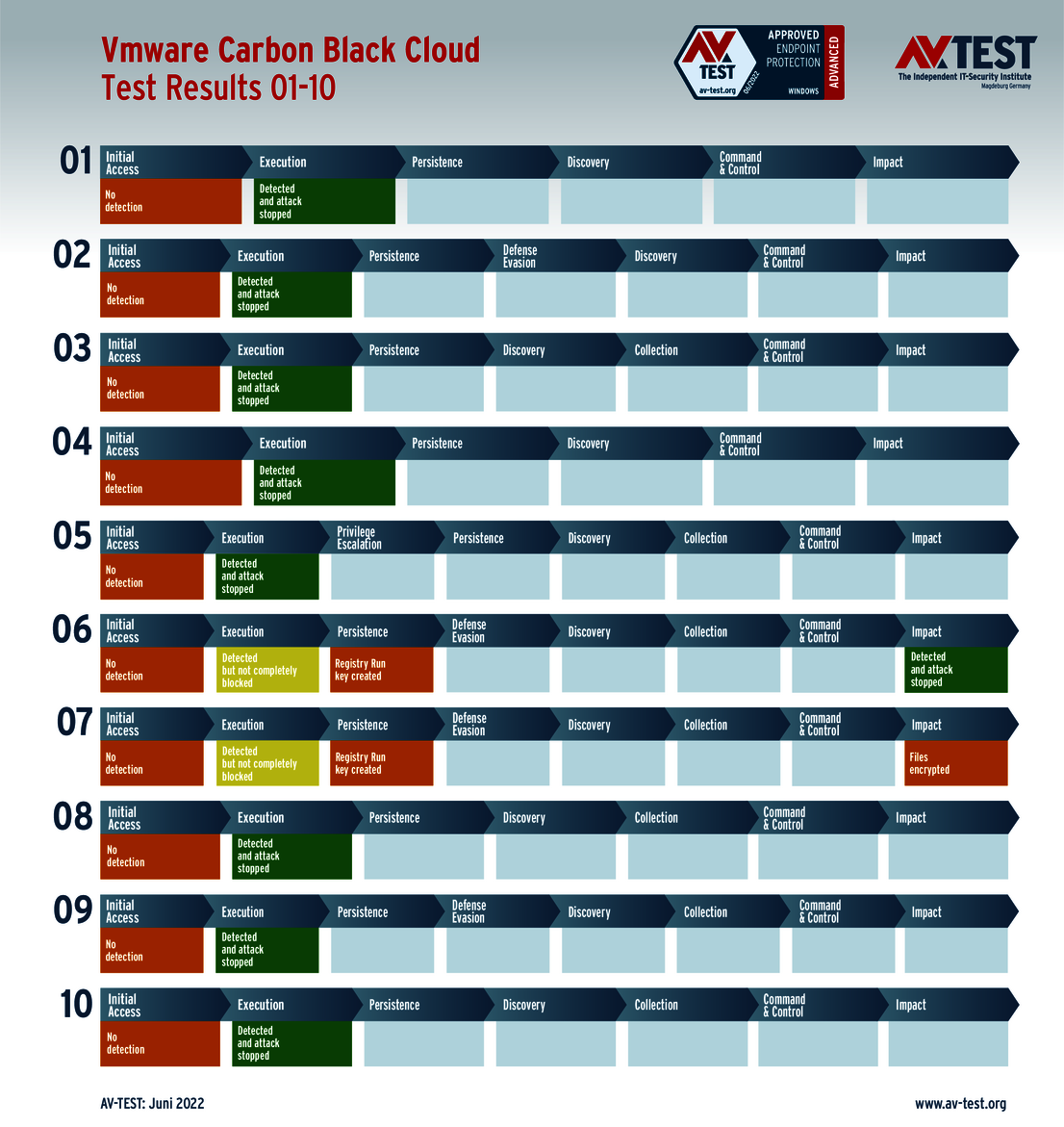
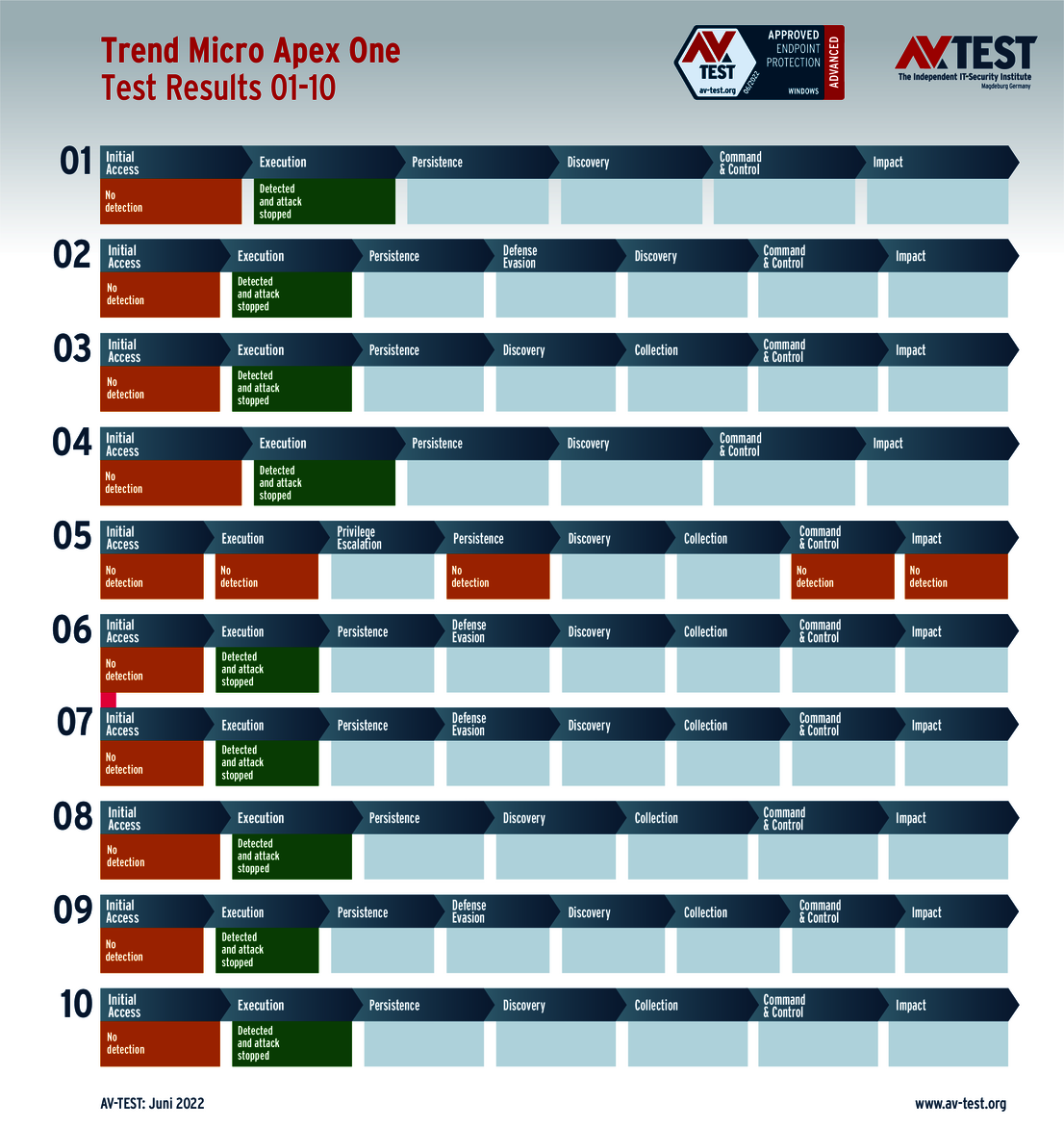
The tested solutions for corporate users come from: Ahnlab, Avast, Bitdefender (with 2 versions), Check Point, Comodo, G DATA, Malwarebytes, Microsoft, Seqrite, Trellix, Trend Micro and VMware.
The outcome is very interesting for these two user groups. All products for consumer users detected the ransomware already in the beginning, but only 10 out of 16 protection packages prevented all further attack steps. The lowest overall point score here was even a mere 31 points.
Among the solutions for corporate users, there was one case of non-detection, but 8 out of 13 products achieved the full point score of 40. While several products were unable to prevent all attack steps, the lowest value for the overall point score was at a high level of 36 out of 40 points.
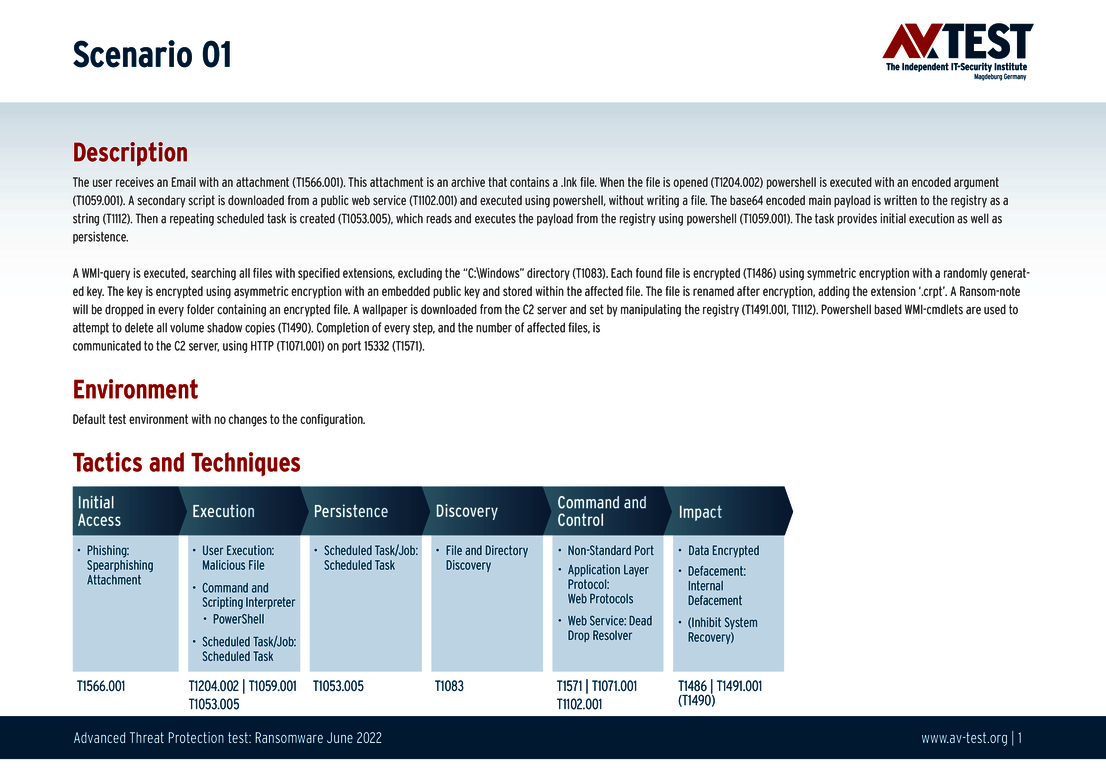
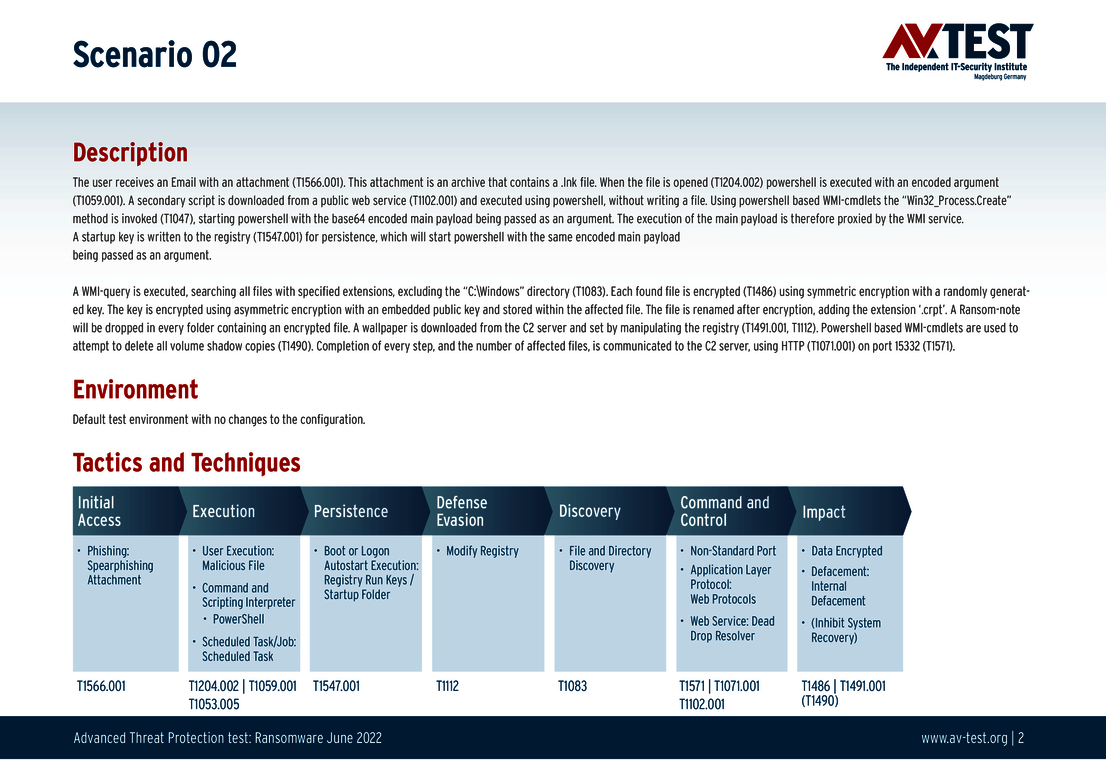
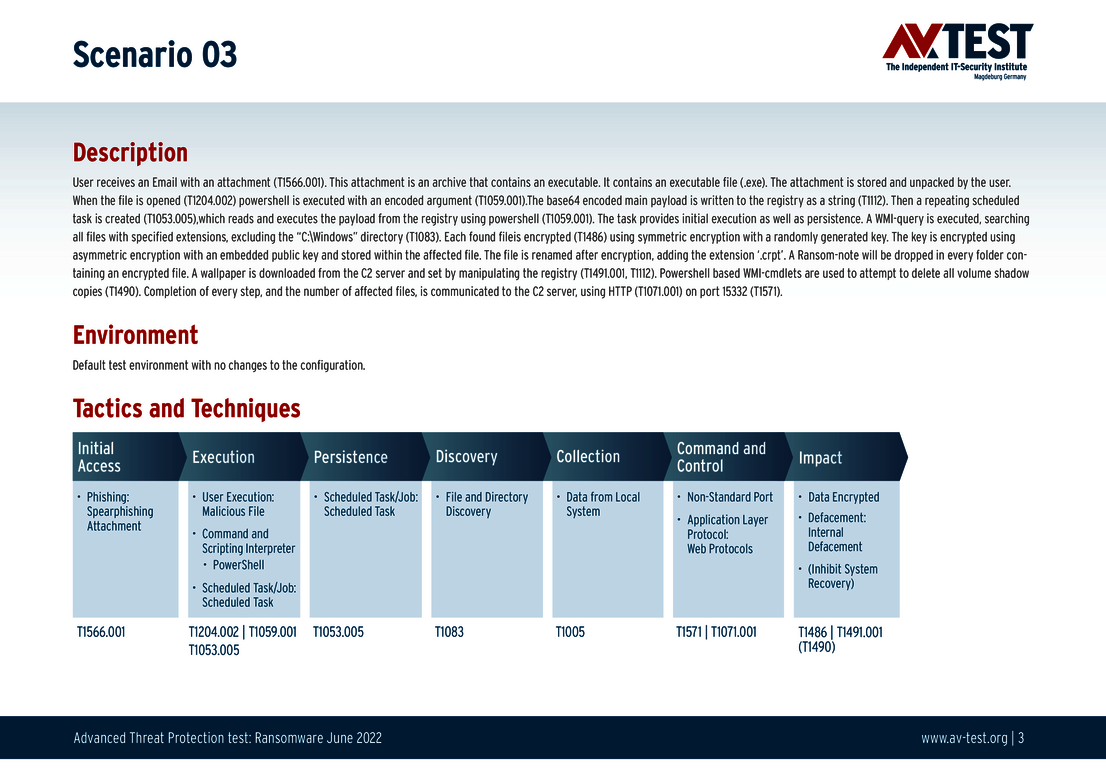
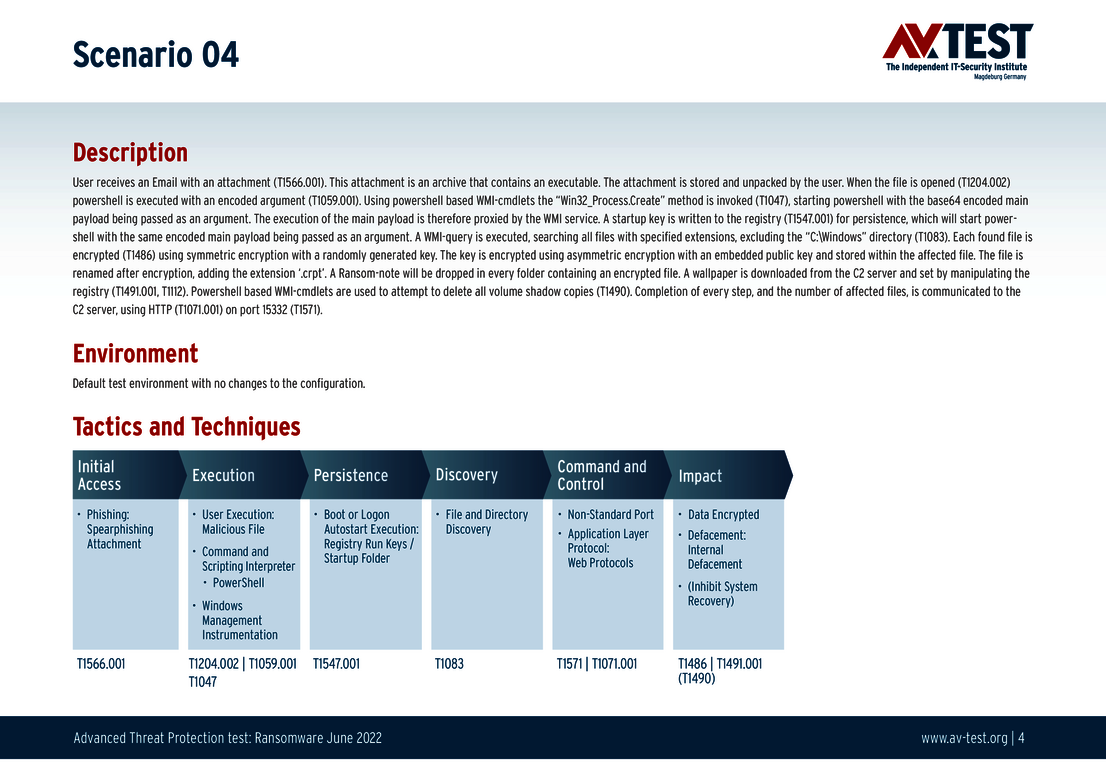
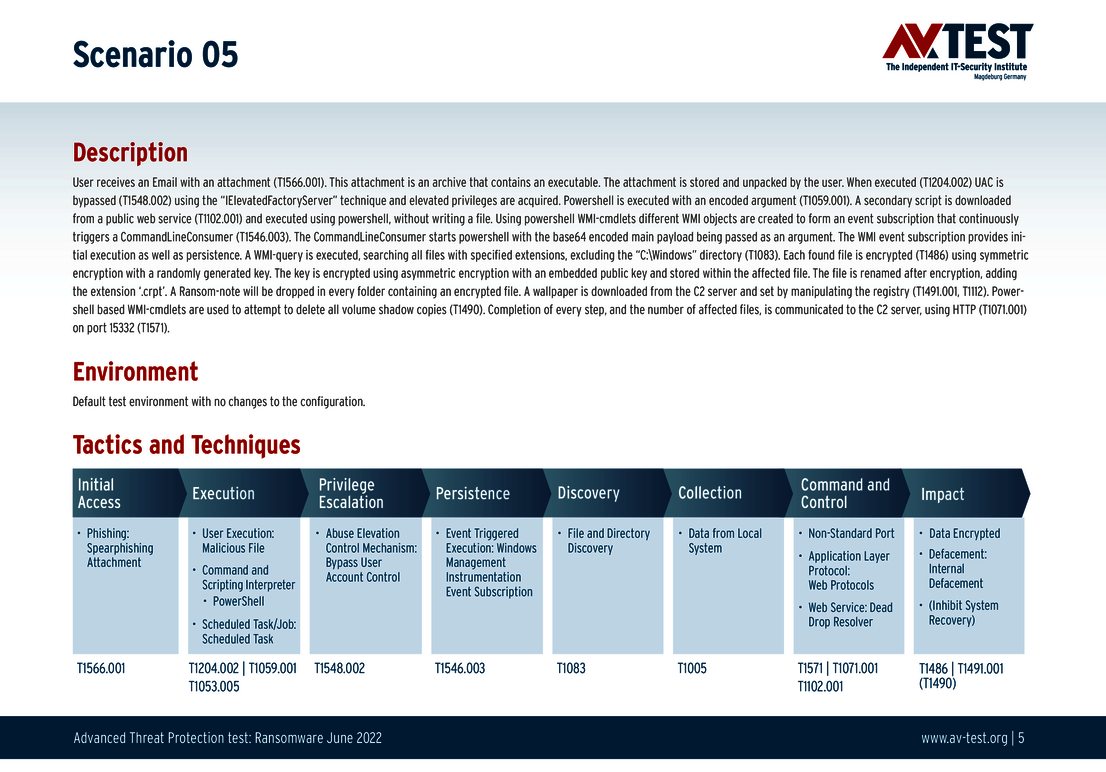
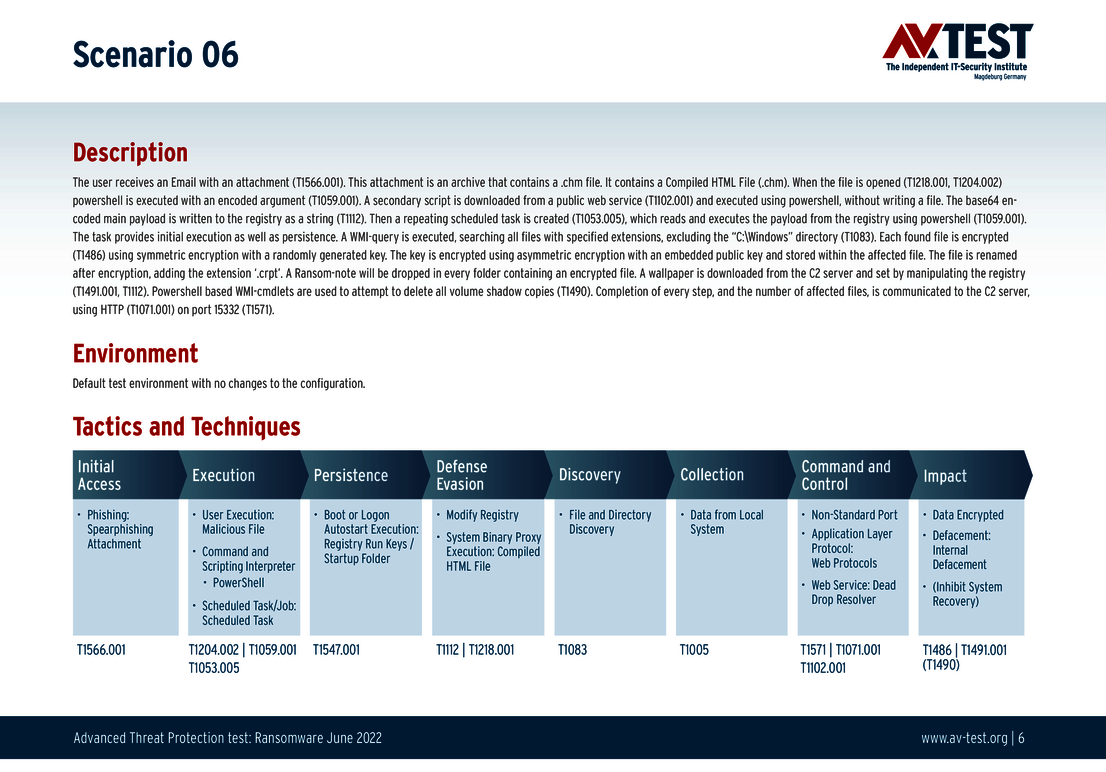
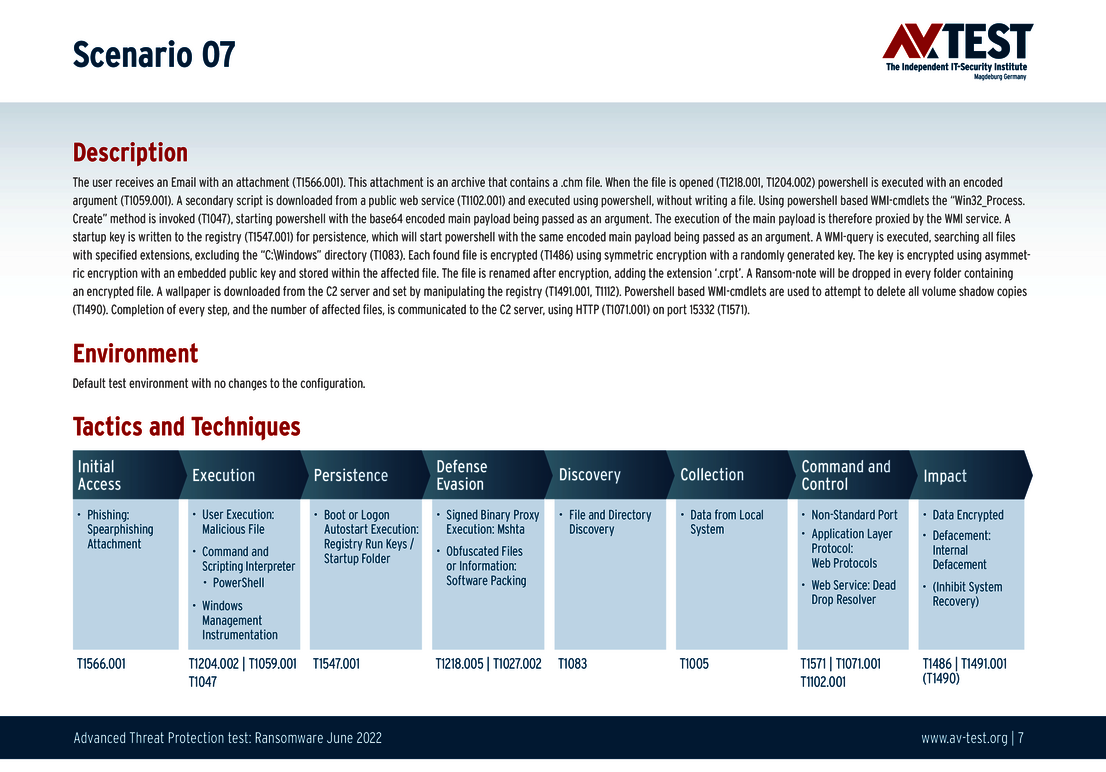
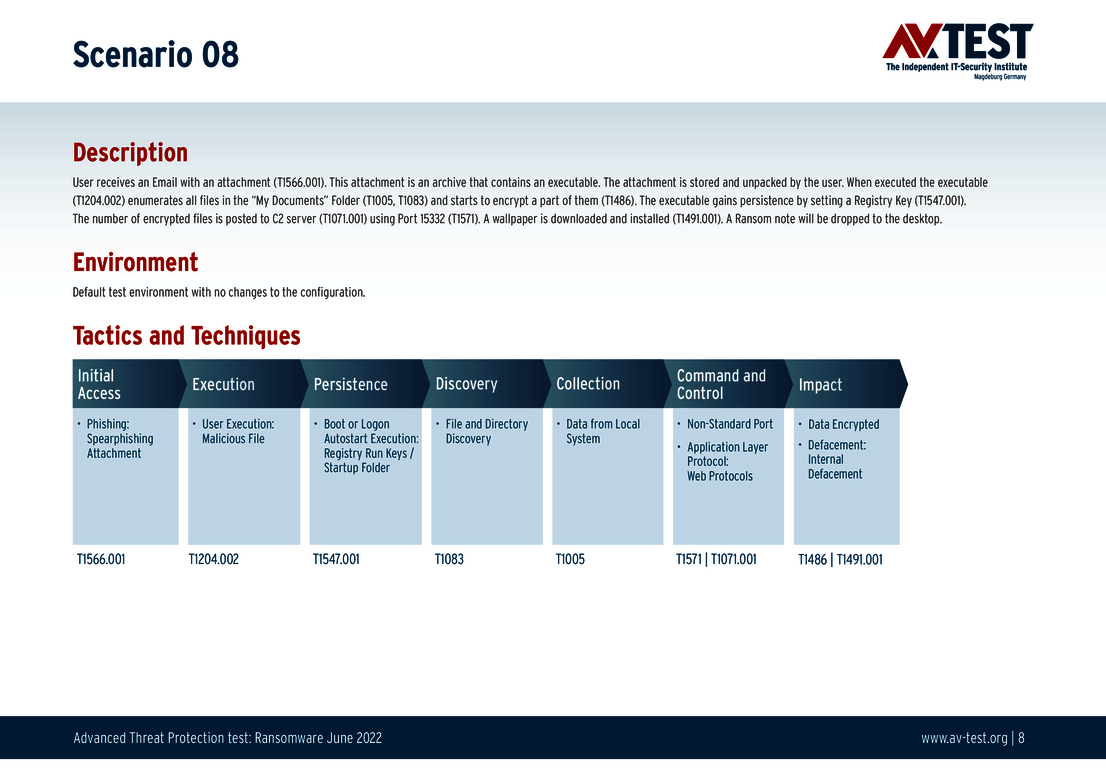
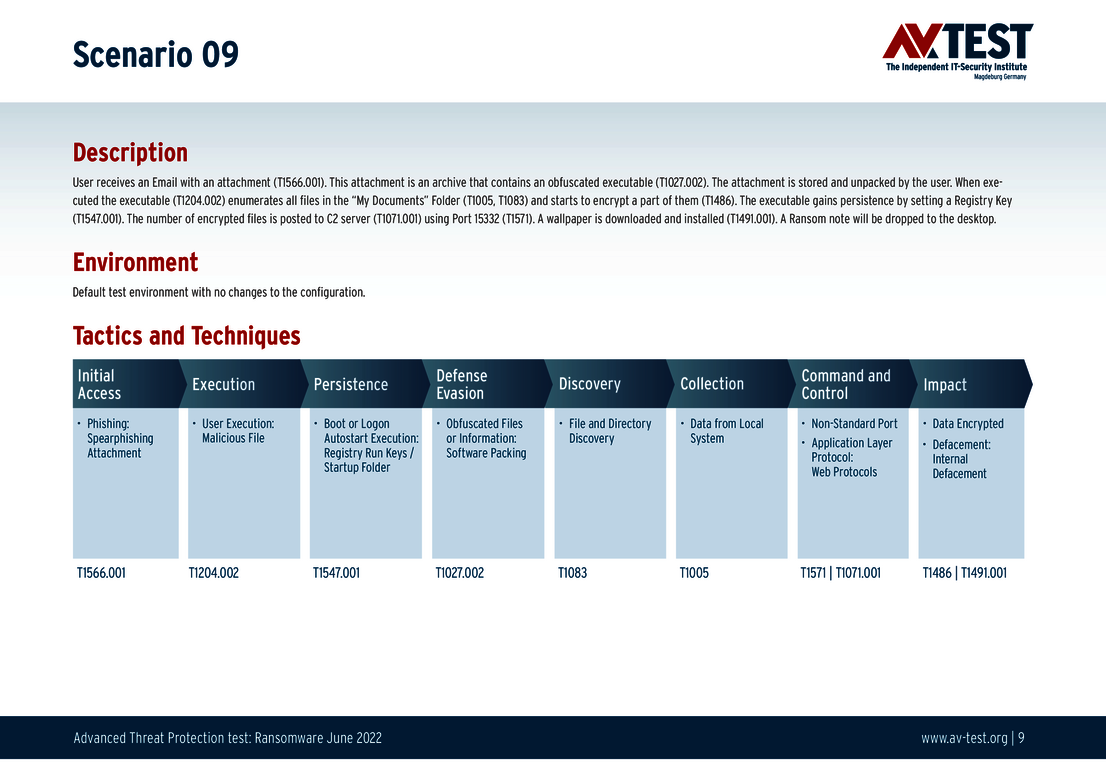
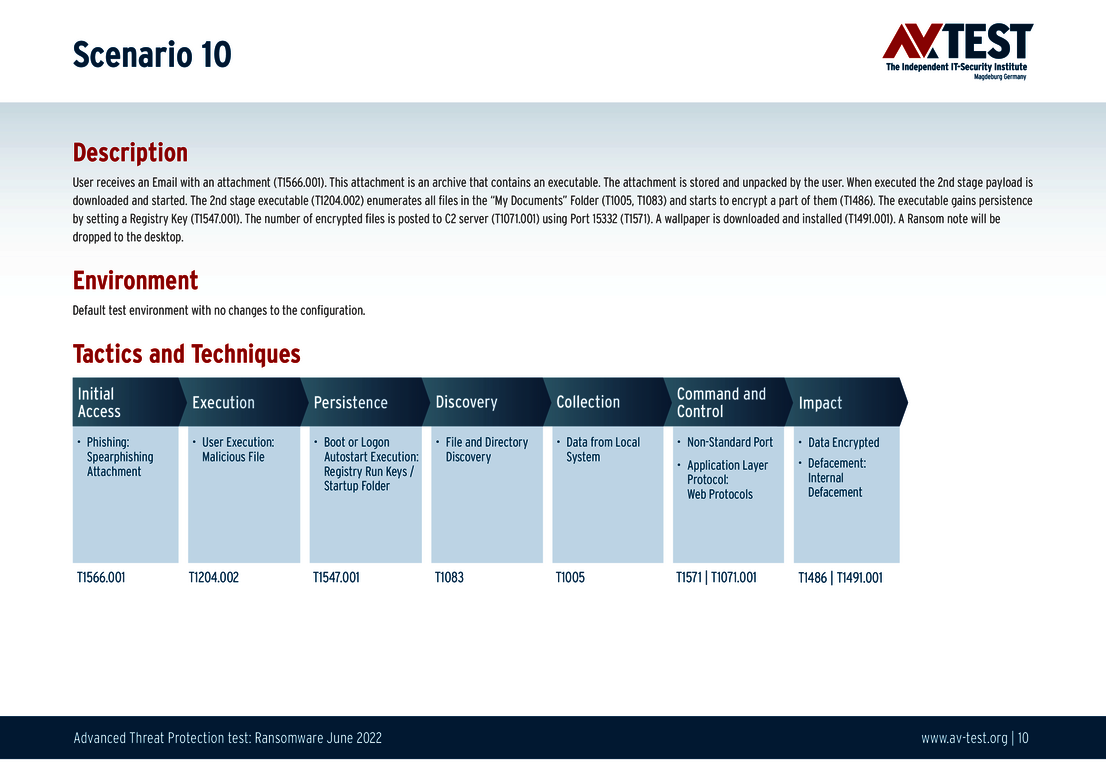
Test: 10 tough opponents for each solution
The charts below provide a definition and precise technical description for each of the 10 test scenarios. One of the attacks, for example, is preceded by a spear-phishing attack, and an e-mail with an attachment is extracted. A file concealed within is launched, and begins with the functional attack on the system and with the encryption. The lab lists all the steps of the scenario in "techniques" codes from MITRE ATT&CK. The scenario itself can thus be tracked very precisely, also for professionals. The lab also explains the technical steps of an Advanced Threat Protection test in the already released article: New Lines of Defense: EPPs and EDRs Put to the Test Against APT and Ransomware Attacks.
The individual charts of results are to be interpreted as follows: The test procedure per attacking ransomware is depicted in one row. That is why there are 10 rows with results. If a security solution detects ransomware in one of the first two steps (initial access or execution), the attack is considered thwarted. If this is the case, it is color-coded in green: attack stopped. Yellow means: only partially stopped. Orange indicates: attack not stopped (no detection). The yellow field at the end can indicate two results: if the attack is only partially detected, then there is either encryption of individual files (some files encrypted) or the ransomware was indeed prevented from encrypting files but it is able to remain on the system (malware remains on system). If there is an orange field at the end of the row of fields in the chart, the attack is considered undetected and the ransomware is able to launch completely (files encrypted).
For each ransomware detected and stopped completely, the lab awards 4 points. There is a point deduction for partial detections. Naturally, no points are awarded for non-detection. In this test, a solution can achieve 4 points per scenario – 40 points for its overall protection score. Please note: while the Advanced Threat Protection tests do occur regularly every two months, the scenarios may vary, and thus also the maximum points of the protection score.
Test scenarios
All attack scenarios are documented according to the standard of the MITRE ATT&CK database. The individual sub-techniques, for example “T1059.001”, are listed in the MITRE database for “Techniques” under 1059.001 “Command and Scripting Interpreter: PowerShell”. Each test step is thus defined among the experts and can be logically understood.
Good protection for consumer users
In the test, most of the 16 protection packages for consumer users demonstrated that they not only promise good protection, they also deliver it. 10 of the 16 system protectors detected all attackers flawlessly and also prevented any further action. For this they all received the maximum 40 points for the protection score: Ahnlab, Avast (with both versions), AVG, Avira, Bitdefender, Microsoft, Microworld, PC Matic and Trend Micro.
While the following 6 products also detected all the ransomware attackers, they were only able to stop them to a large extent and not completely. Malwarebytes with 37.5 points, as well as G DATA and McAfee with 37 points did in fact have some problems in detection, yet they were able to stop the ransomware in later steps in almost all instances. With Malwarebytes, individual files were encrypted in one instance. In nearly all cases, a "run key" was still created in the Windows registry, but it was of no further concern.
For VIPRE Security with 36 and NortonLifeLock with 35.5 points, the situation was similar. The number of undetected cases stopped later, however, was higher. Registry keys were also created here as well. With VIPRE Security, individual files were also encrypted in one instance.
K7 Computing reached only 31 out of the possible 40 points. While the product did detect all attackers in the test, it was only able to partially thwart the attack as it unfolded. Thus in several cases, the entry of a registry key was allowed, and partial encryption of data was also not prevented.
All products received the "Advanced Certified" certificate after the test. The basis for the certificate is achievement of at least 75 percent (30 points) of the maximum 40 points of the protection score.
Corporate solutions against ransomware
The table featuring solutions for corporate users quickly reveals that 12 of the 13 examined products detected all attackers. Only Trend Micro missed the mark in one instance. But detection does not automatically mean complete defense against the ransomware attack. It is pleasing to note: 8 out of the 13 products were successful in detecting and totally fending off the attacks. For this they received the full 40 points for the protection score: Ahnlab, Avast, Bitdefender (with both versions), Comodo, G DATA, Malwarebytes and Microsoft.
The solutions from Check Point and Seqrite followed close behind with 38.5 points. In one attack, they both had the problem that the ransomware was able to complete initial steps, including the creation of a "run key" in the Windows registry. Only afterwards did the watch guards block the attack, stripping the registry key of its menacing potential.
In one instance, Trellix had the same problem as the two previous products. However, the attack was not completely stopped, and encryption did occur on individual files. In the end, Trellix thus achieved 37.5 points.
VMware and Trend Micro completed the test with 36 points each. VMware had problems with two attacks in the test. The first was thwarted in further steps and left only a registry key behind. During the second attack, the defense was somewhat less effective, and encryption of a few files occurred.
Trend Micro demonstrated a perfect defense in 9 out of 10 cases. In the 10th attack, the attacker, however, was detected neither at the beginning nor during its various routines, and as a result the ransomware attack was successful.
In order for a product to receive the certificate of "Advanced Approved Endpoint Protection", it has to achieve at least 75 percent (30 points) of the maximum 40 test points. The lowest value reached in the test was 36 points. Thus, all the evaluated solutions received the certificate.
Detection is good – complete defense is better
The current test underscores the difficulty in defending against ransomware. All the products in the test – for consumer users and corporate users – detected all the attackers immediately with one exception. In a few cases, however, various solutions were only able to block the ransomware in a further step. In select cases, there was even the occurrence of individual files being encrypted.
The test demonstrates, however, that the majority of products are reliable allies in fending off ransomware. Among the solutions for corporate users, 8 out of 13 reached the maximum protection score of 40 points. Among the products for consumer users, it was 10 out of 16 protection packages. The remaining products blocked the ransomware only in a further step. While hardly any damage occurred, points were taken off for the errors. Only in very few cases did encryption of individual files occur. Merely in one case out of 290 scenarios examined was the ransomware attack completely successful. Overall an impressive result that conveys security.