Latest News
June 25, 2019 | Antivirus for Android
The Best Extra Features in Security Apps for Android – What They Have to Offer!
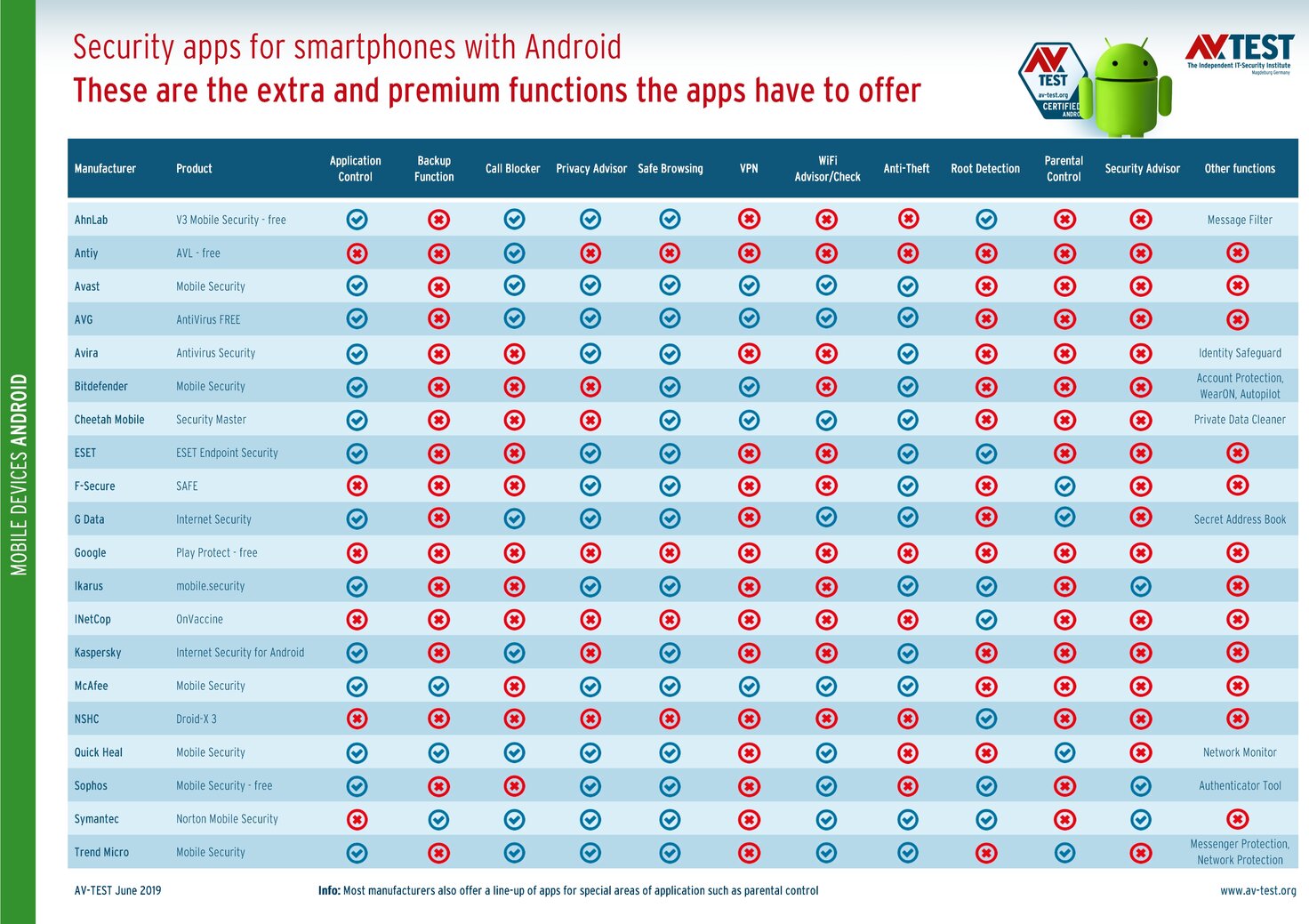
Each Android smartphone ought to use a security app against viruses of all kinds. The checks performed by AV-TEST reveal the most secure apps, but they say nothing about their extra features. Here is an overview of what the apps have to offer in addition to security.
Every two months, the AV-TEST laboratory evaluates how up to 20 Android apps match up in terms of security. The tests focus mainly on the categories of protection, usability and performance. Any additional extras or special functions provided by the tools are not taken into account by the laboratory. This is because some apps come equipped with very different functions – others offer almost none. That is why there is no comparison. Nonetheless, the lab took a look at the additional functions of the apps – without additional testing or evaluation. Here's an overview of all the goodies the apps have to offer.
Guardian angel, Swiss army knife or both
Most apps have many more functions in the mix than just their protection functions for detecting and deleting infected or dangerous apps. A freshly-installed security app often offers many wonderful features. However, depending on the app provider, these are not always available free of charge. Some manufacturers have premium features that can usually be used for 15 or 30 days free of charge. Afterwards, the protection often continues to work, but nothing else does. There are also apps, however, that can be used free of charge and even come with additional functions.
About a dozen functions can be found in many apps – even if the manufacturers use different names for their tools. The table shows an overview of the extra features for each app. Some, however, can only be used without restrictions in the premium version. Here are the extra features often available:
- Application Control
- Backup Function
- Call Blocker
- Privacy Advisor
- Safe Browsing
- VPN
- WiFi Advisor/Check
- Anti-Theft
- Root Detection
- Parental Control
- Security Advisor
Naturally, there are even more functions. These can be found in the table under "Other functions", such as Message Filter, Identity Safeguard, Account Protection, Smartwatch Security, Private Data Cleaner, Secret Address Book, Network Monitor, Authenticator Tool, Messenger Protection, and Network Protection. Even in this list, some of the additional small functions are missing that cannot all be listed.
This what is behind the functions!
The suppliers often refer to the functions using names that are not always meaningful to the user. Here you will find a brief explanation of each extra function.
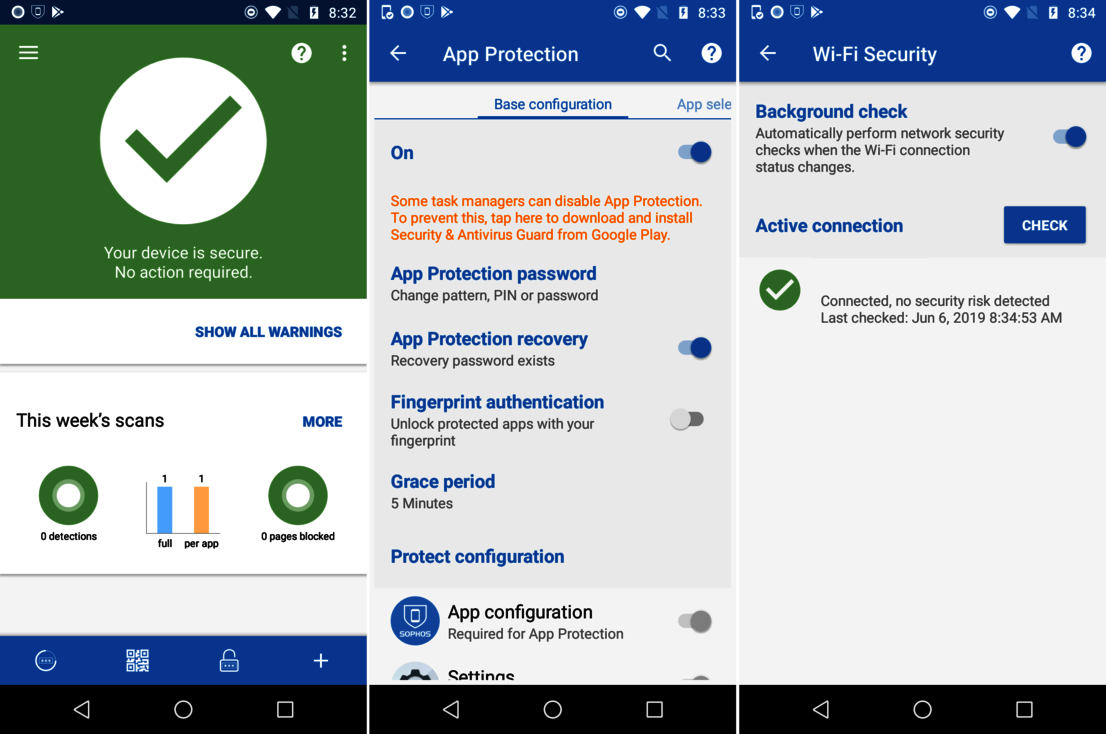
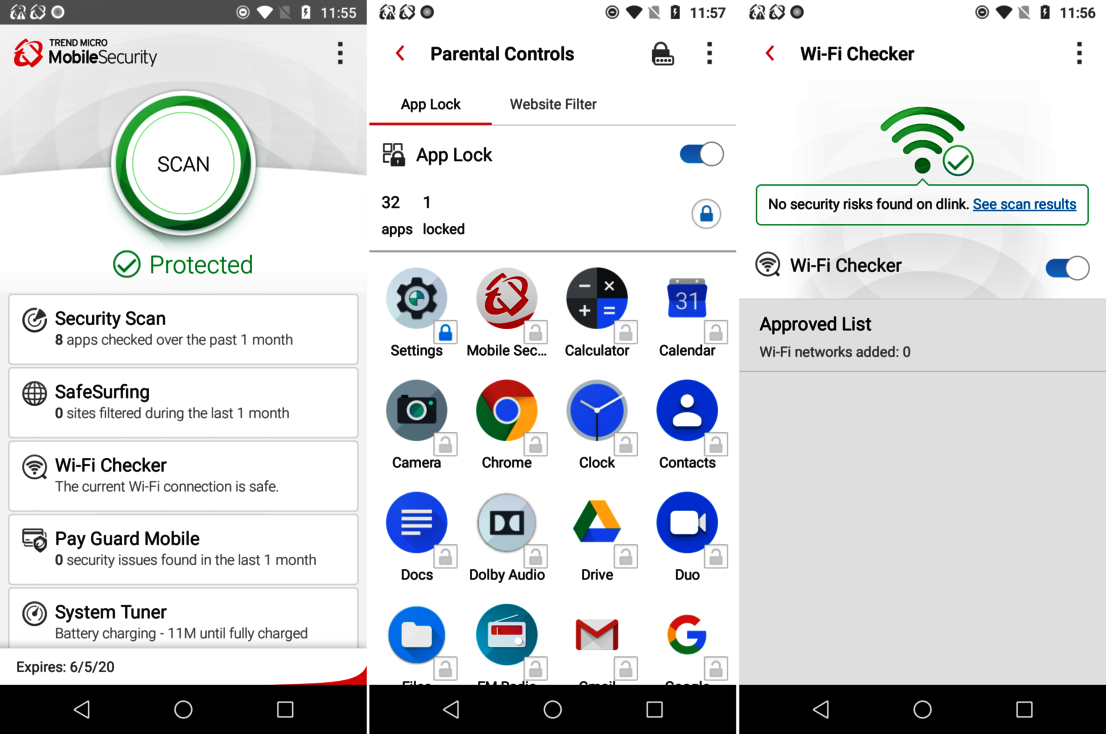
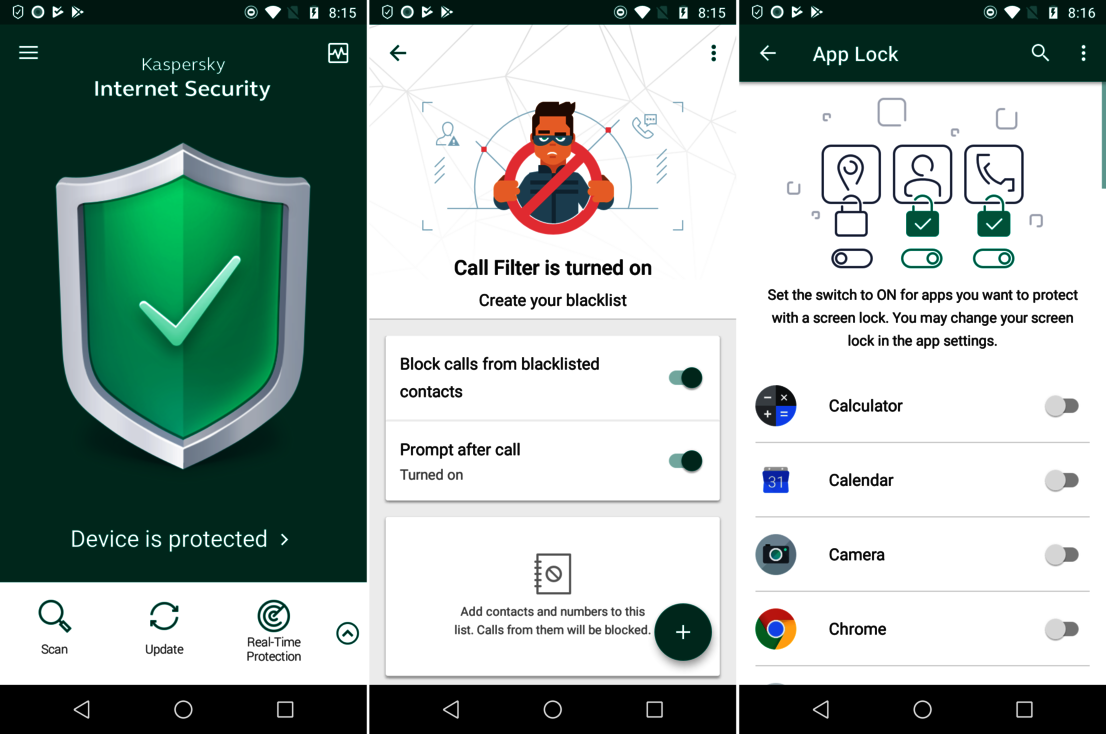
App Control
Some smartphone manufacturers have integrated this function into the Android system, but unfortunately not all. With app control, the launch of an app can be prevented, usually by means of a password query previously defined for the app.
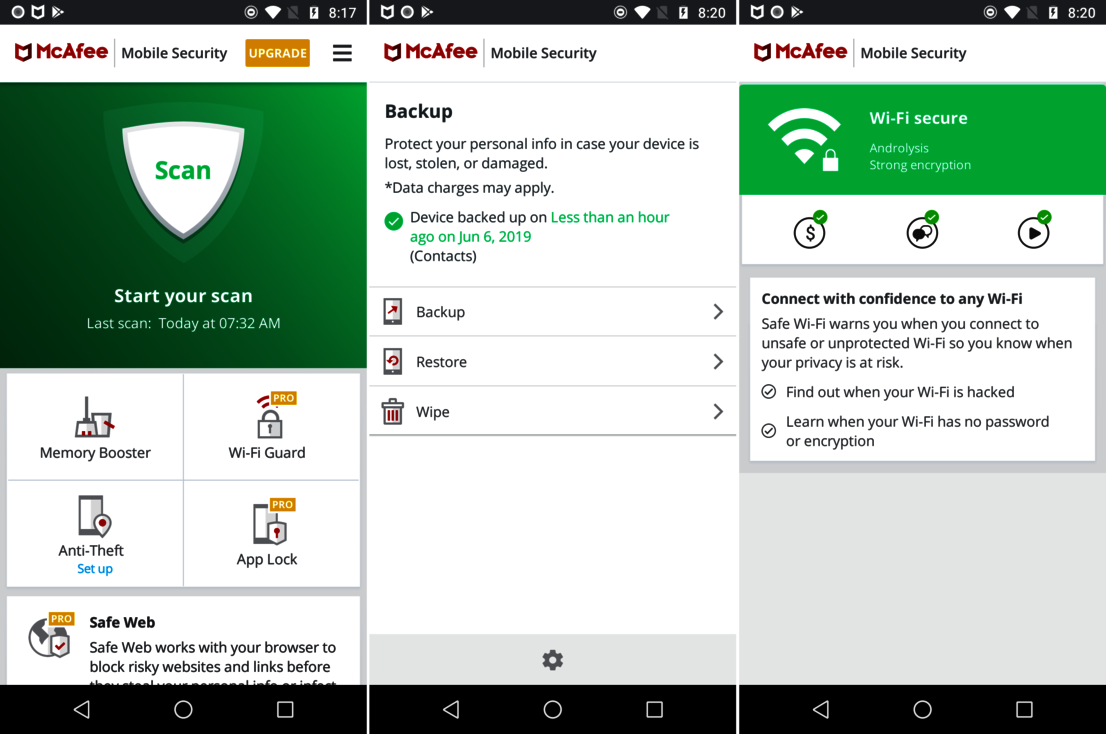
Backup Function
While it is not possible to back up the entire Android system, it is possible to make a backup of all private data and many settings. Only a few apps offer data backup onto a memory card or cloud storage.
Call Blocker
This function is self-explanatory. Many device manufacturers offer this function in their phone tools. If it is missing there, it is very useful to have it in the app.
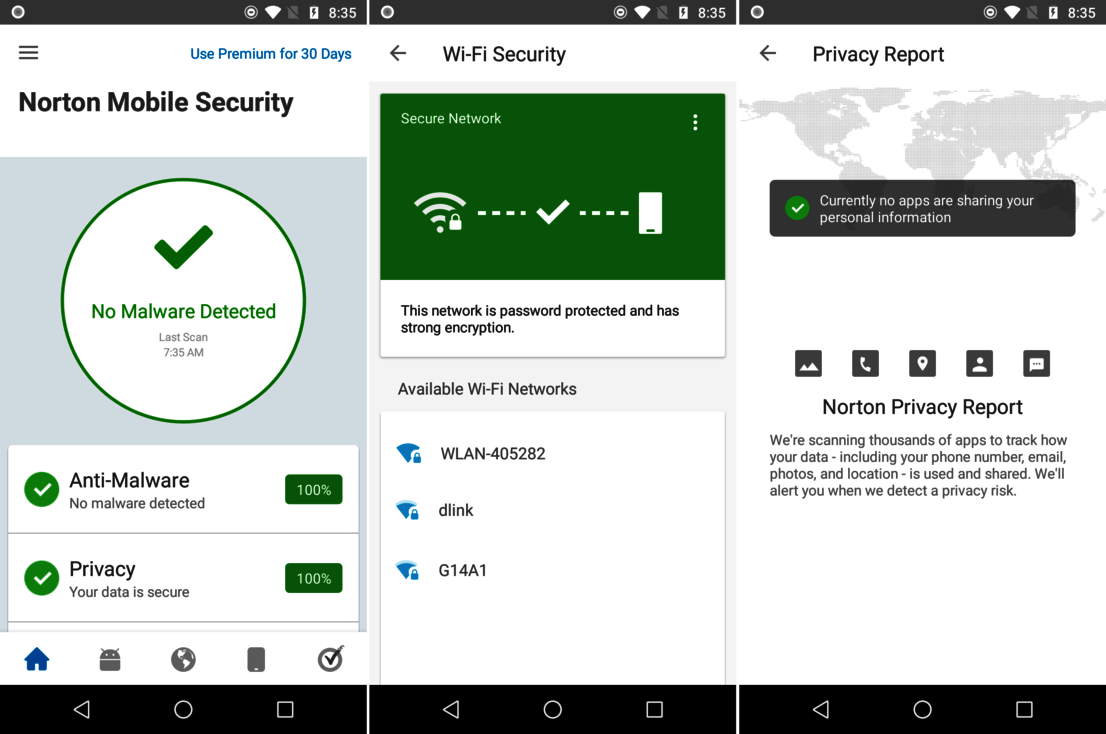
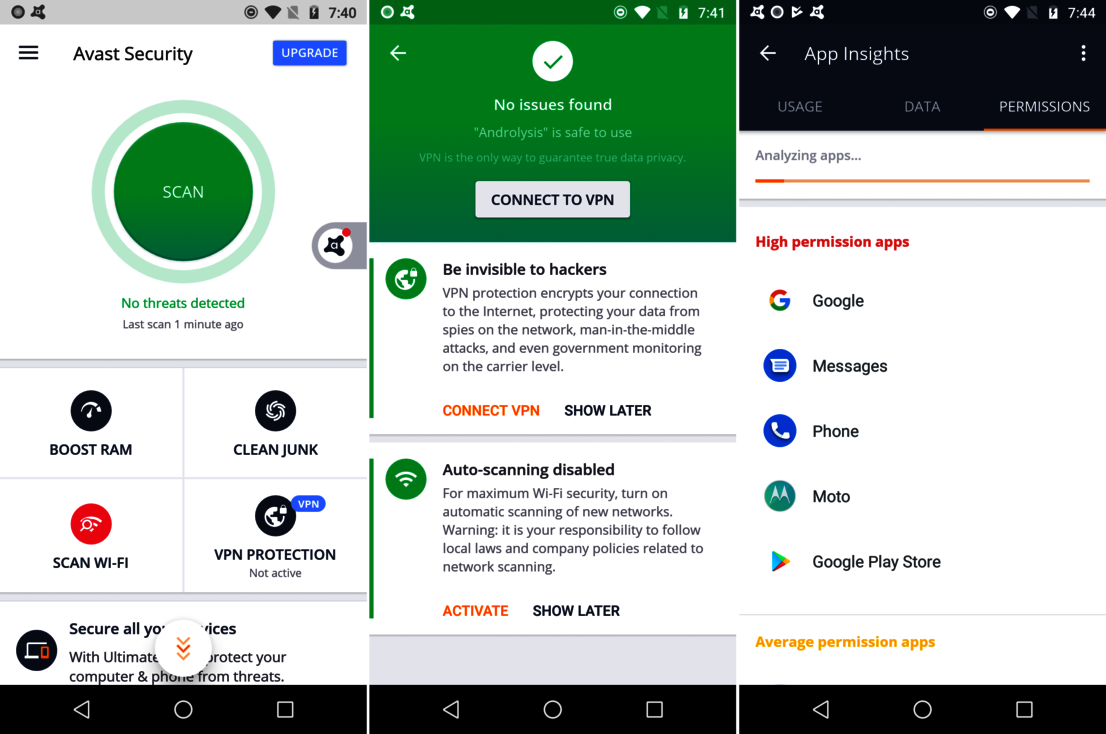
Privacy Advisor
This function is sometimes interpreted completely differently by manufacturers. This tool normally examines the installed apps and retrieves information from a manufacturer database as to how inquisitive the apps are. The mini programs are then found in a risk list and can be quickly removed with one click. Other manufacturers monitor the access to the user's data, such as documents, and sound a warning when someone tries to access them. One glance at the support pages will quickly clarify how the app provider handles the protection of customers' privacy.
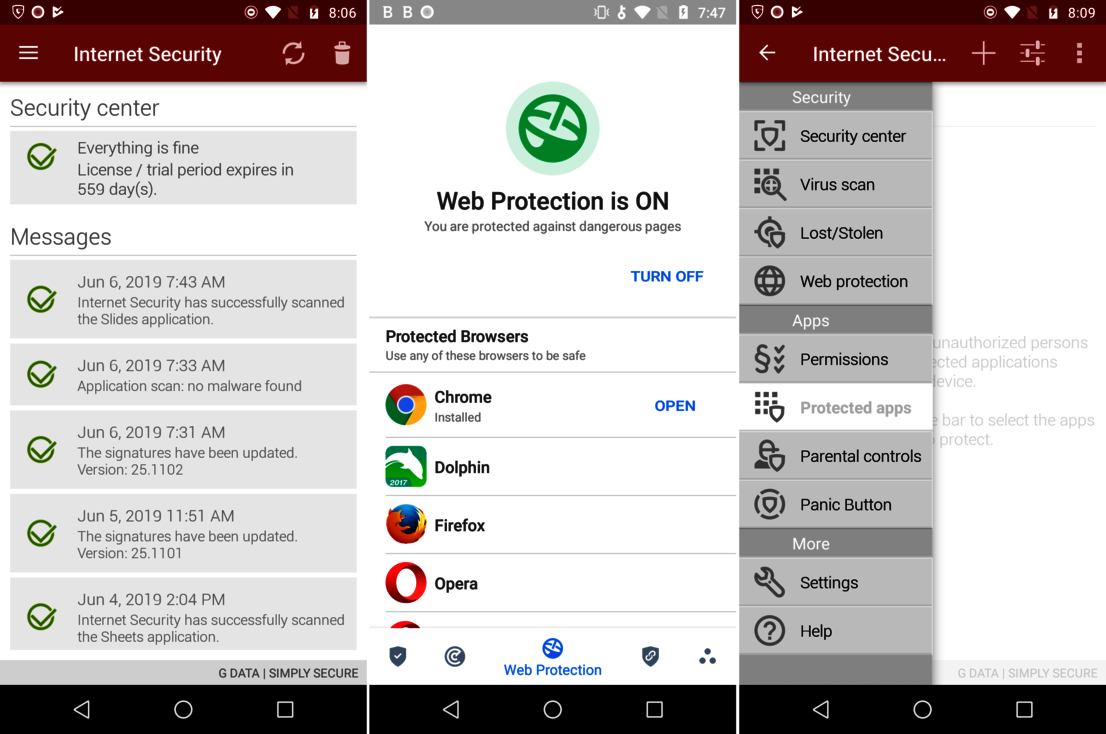
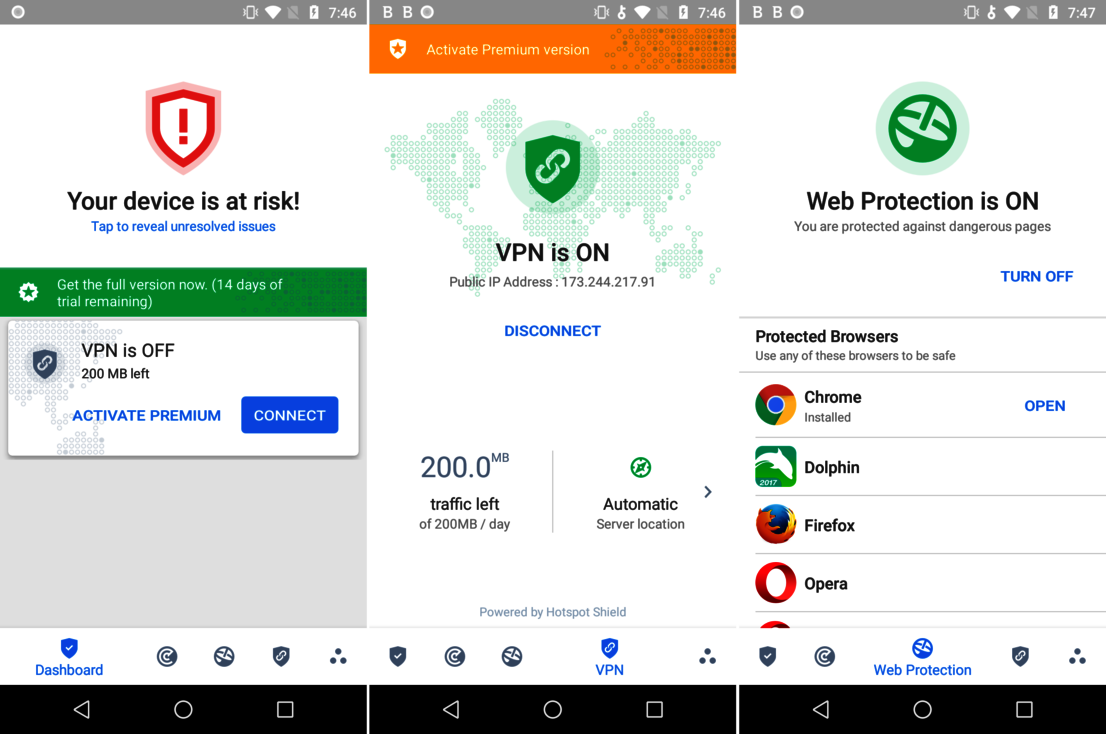
Safe Browsing
As the name implies: surfing on the Internet is examined and secured. This is also provided partly by mobile browsers used, such as Chrome, Opera or Firefox, for instance. In addition, Google has its own safe-browsing function in the search engine. The manufacturers offer a reputation score for safe-browsing in search results or detect infected web pages that are offered, and they prevent access. Because Google is not always up to date on all websites that have currently been hijacked – but the security providers are.
VPN – Virtual Private Network
Via VPN, it is possible to safeguard access in an open WiFi network. This works like a secure tunnel from the user device to the website. Everything in between can neither access nor see any part of the communication. As this technology is somewhat sophisticated, providers normally charge a service fee. This is the case with most security app suppliers. Free VPN is normally only available in test phases for apps with premium functions.
WiFi Advisor/Check
Various small services are combined under this function. Normally, the app warns the user against unknown WiFi connections and recommends switching on the VPN function – where available. The app also scans a currently connected WiFi connection for problems concerning the router, encryption and connection. Known WiFi connections are usually whitelisted and do not have to be checked over and over again. Open WiFi connections – at airports, for example – are always considered dangerous because they are unsecured. It is always conceivable that free WiFi is only used to lure people in. Non-protected, connected devices are then easy prey.
Anti-Theft
Many apps have included this function in the mix since the early versions. However, they have almost become superfluous, as Google offers them to each user with an account. Under Google Find My Device, a device can be located or locked, an alarm is activated, or data can even be deleted remotely. Those who don't trust Google, however, and shut off the function in their settings should rely on a security app with anti-theft functions. As soon as the device goes online, it can usually be located with the help of a previously created online account with an app provider. Some manufacturers also extend the anti-theft features. Some security apps, for instance, notice when the SIM card is replaced. The previous owner then receives the number of the newly inserted SIM via text message.
Root Detection
Younger users in particular think it is cool to root an Android device and thus be able to gain access to the highest administrator level. This level is normally blocked for security reasons, as otherwise hackers could practically have an unlimited field day on the phone. A rooted mobile phone disables the security structure of the Android system. Some security apps detect this and warn the user, as it is possible they have bought a used device and are not aware of the risk at all. The function tends to come from the business area, as rooted devices violate company guidelines.
Parental Control
The functions offered in apps in terms of parental control differ widely – to the extent they even exist. The Family Link offered in Google can be activated via an additional app. However, it offers only rudimentary functions to protect young users. Only a few other products offer protection and filter functions. The protection functions should always be tailored to the age of the child. The laboratory at AV-TEST performs this extensive check each year in a separate test. The latest test can be found online at: Parental Control Apps for Google Android, Apple iOS & Amazon Fire OS.
Security Advisor
Depending upon the security app, the Security Advisor is comprised of small tips and tools. The app mainly scans the Android settings and warns the user if an item has been activated or deactivated. If installation of apps from an insecure source is enabled, for example, and no longer switched off, the check notices this and warns the user. Of course, this is but only one of many warnings of the security apps. Just how extensive the checks are entirely depends on the app.
Other special functions
Some tools and features can be found only from a single supplier. These include functions such as a Message Filter, Identity Safeguard, Account Protection, Smartwatch Security, Private Data Cleaner, Secret Address Book, Network Monitor, Authenticator Tool, Messenger and Network Protection. Some tools are self-explanatory due to their name. Whether you really need them, of course, always depends on the user. Smartwatch security, for instance, is only of interest to a small group of users. An authenticator tool, on the other hand, is a different story. It is often required for 2-factor authentication. It is practical if it is already integrated into the security tool. If not, you can also use the Google Authenticator app.
Another interesting feature is the Identity Safeguard. It repeatedly checks in large databases of hacked accounts to see whether the user's e-mail addresses appear there and are thus perhaps compromised.
Here is a final tip: if you are not sure what is behind a function, you should quickly consult the manufacturer's user manual. It is normally found online and explains the actual capabilities of the function. Often, a boastful name such as Network Monitor turns out to be only an overview of all connections and the volume of data consumed. This is in fact a built-in feature that nearly every smartphone displays within the connection range.
Test reports from May 2019
Security apps for Android