Latest News
July 20, 2021 | More tests
Stopped in its Tracks: Stalkerware for Spying Under Android
More and more dubious apps offer their services for spying and stalking, in order to secretly surveil unwitting persons, acquaintances or (ex-)partners. With a good security app for Android, it's also possible to unmask these deceitful attackers.
The market for Android apps with which devices can be secretly monitored, tracked and spied on, is steadily growing. There is brisk demand for so-called spying stalker apps, as they can be used to monitor Android devices such as smartphones or tablets. The devious part: once installed, the monitoring software hides on the device or sometimes disguises itself as a harmless service or game app. The capabilities of these apps on the device are vast, as they often operate in admin mode, thus having the highest permissions on a given device. Those who are uncertain and feel monitored can help themselves. A good security app detects the monitoring app for spying or stalking. The lab at AV-TEST examined what these security apps are capable of.
Unmasked in the lab: stalkerware for spying
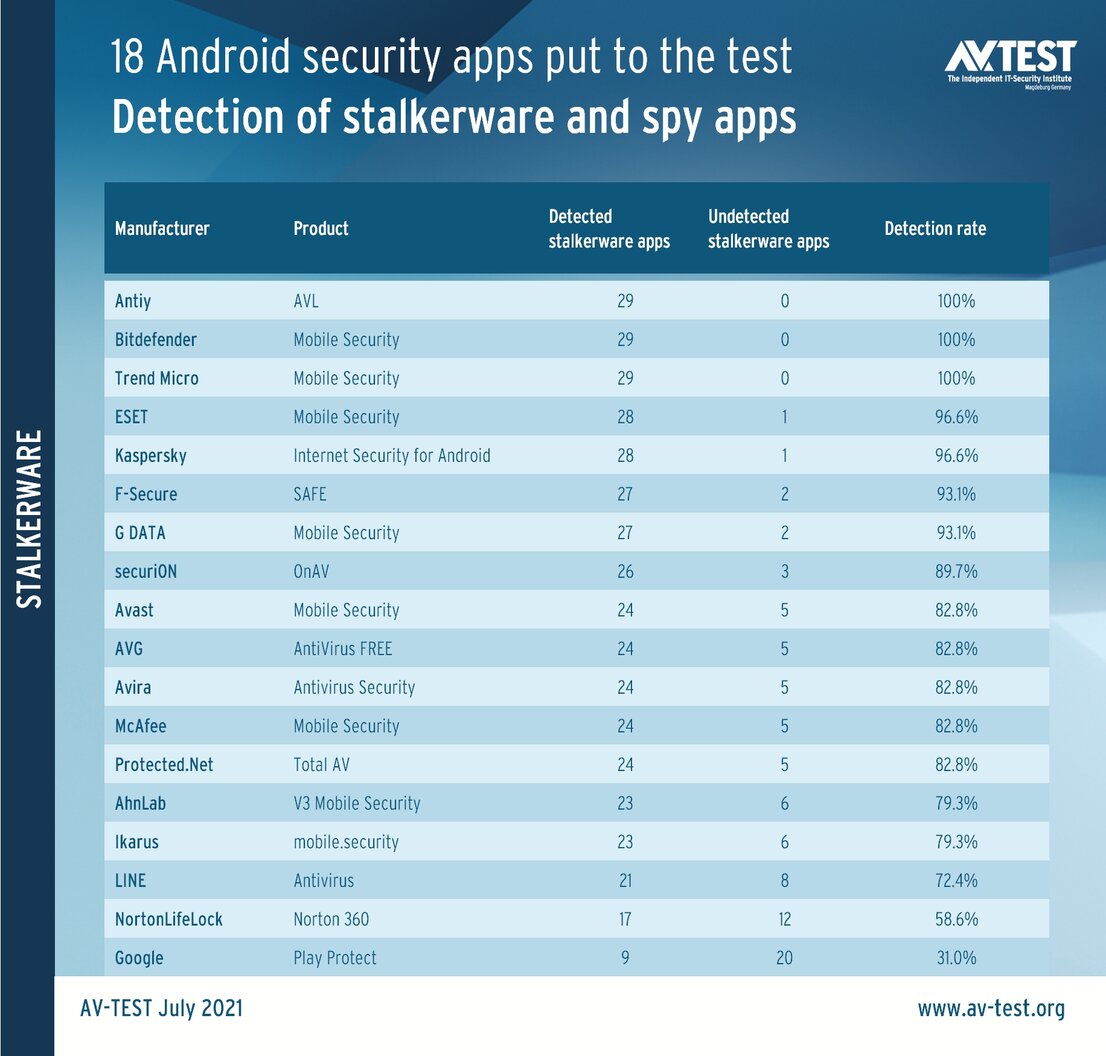
A total of 18 security apps for Android demonstrated in the lab how well they can detect spying stalkerware. Included in the test were the apps from AhnLab, Antiy, Avast, AVG, Avira, Bitdefender, ESET, F-Secure, G DATA, Google, Ikarus, Kaspersky, LINE, McAfee, NortonLifeLock, Protected.Net, securiON and Trend Micro.
In the test, the candidates had to detect stalkerware 29 times. Most of the apps did a good job at it. All 29 or 28 intrusive apps were revealed by the security apps from Antiy, Bitdefender, Trend Micro, as well as ESET and Kaspersky. Following close behind with a 93.1% detection rate were F-Secure and G Data.
The remaining field detected 89.7 to 58.6 percent of the stalkerware and spy apps. Android's internal Google Play Protect security app only reports 31 percent of these tools, which are actually forbidden.
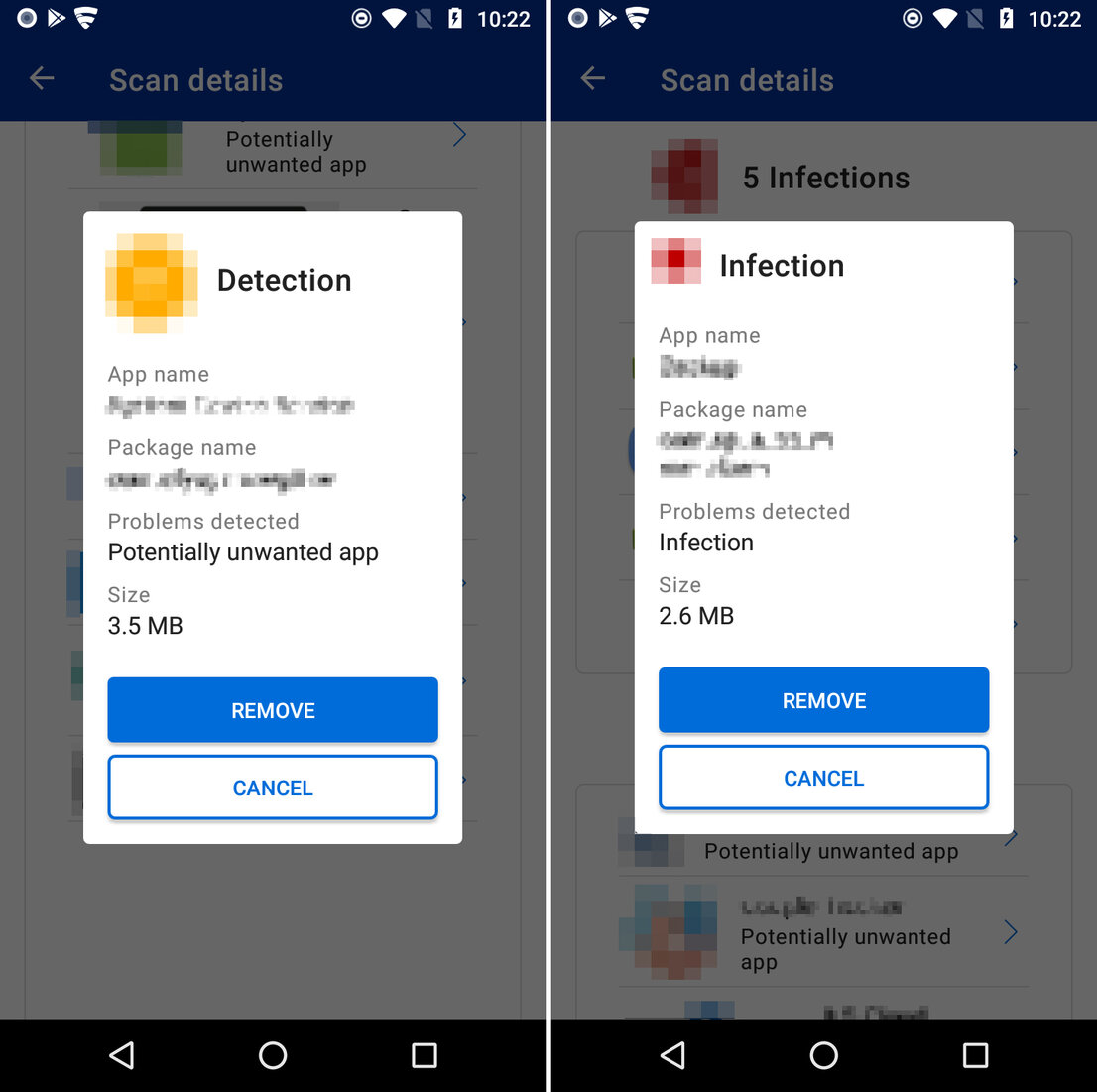
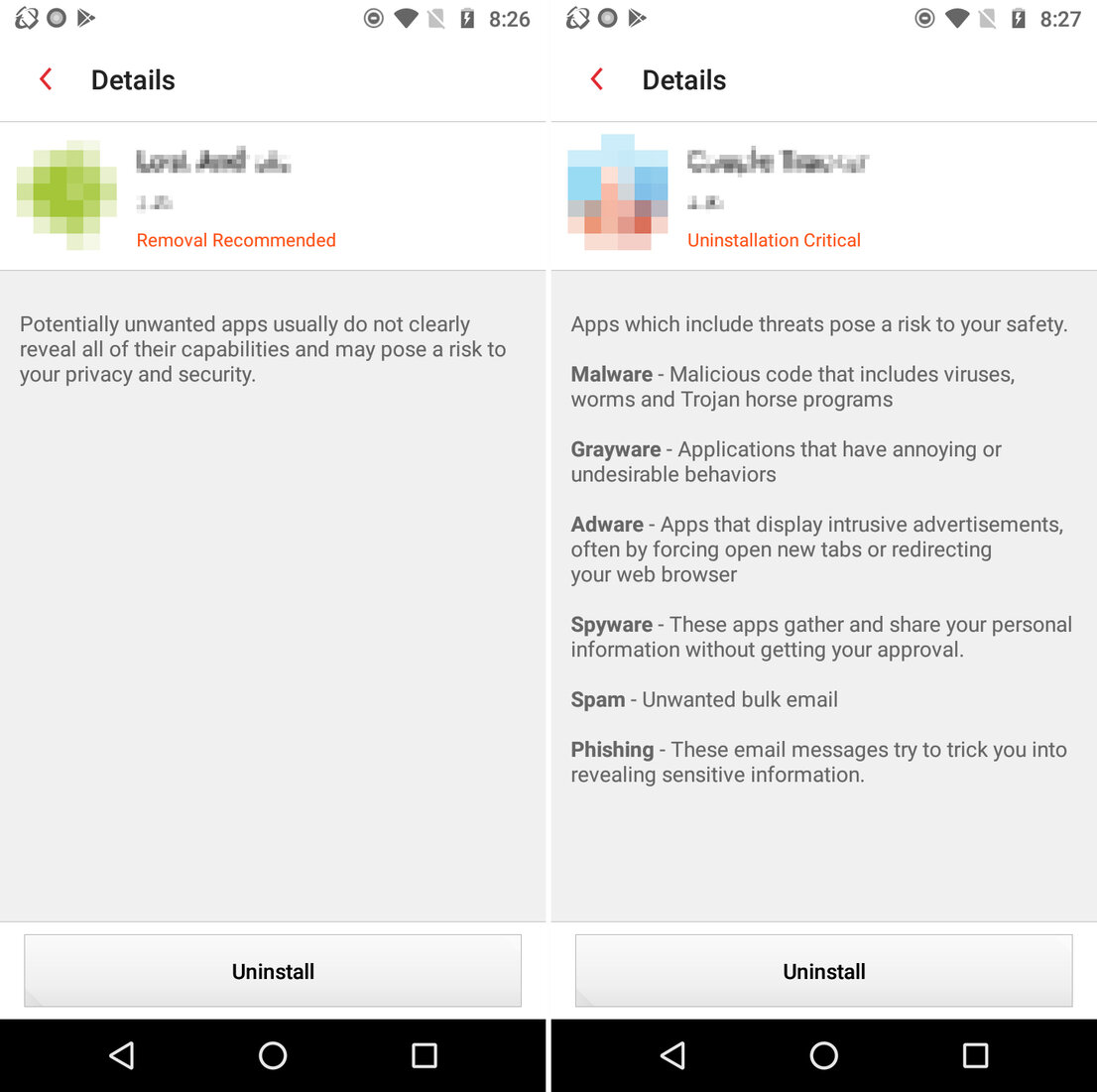
FYI: The security tools also often detect the stalkerware under other categories, such as PUAs (potentially unwanted applications), riskware, malware or simply infection.
Are spying stalkerware apps allowed?
The use of apps under this classification is naturally forbidden. But here is precisely where the problem lies: Who classifies an intrusive app as stalkerware? Unfortunately, there is no official arbiter for this. Worldwide, the national data security laws partly classify what is forbidden and what is not. The manufacturers of security apps are also partly guided by these laws and criteria. Manufacturer A detects an app as stalkerware, because it classified it as such. Manufacturer B does not classify the software as being very dangerous, so it leaves the app alone. Shedding some light on the whole subject is the association "Coalition against Stalkerware". This coalition against spying stalkerware is supported by many leading organizations and also by several security manufacturers, such as Avast, Avira, F-Secure, G Data, Kaspersky and NortonLifeLock. The website explains what stalkerware is, how you can find it and how to remove it. It also lists resources for victims to receive help from social services, associations or official agencies in many countries around the world. Because after all, stalking and cyberstalking is not only spying on a person's device. With the help of the information obtained, stalkers, acquaintances, partners or ex-partners almost always exert psychological pressure or mental violence on their victims. In the worst case, the victim is pressured to further dramatic steps.
The legal definitions for stalking vary widely around the world. Fortunately, in Europe, the penalties for stalking have grown increasingly more severe over the past few years – also in Germany: In June 2021, the law pertaining to the crime of cyberstalking or digital stalking has been expanded, explicitly establishing a criminal penalty for an attack with stalkerware. This is designed to more easily build a court case against perpetrators.
Even Google responded in October 2020, removing suspicious apps for spying and stalking from the Play Store.
How do you notice spying stalkerware?
Often there are initial telltale signs on an Android device that something is not quite right. Abnormalities include, for example:
- Unusual battery drain and slower apps
- Increased data usage
- Noises during phone calls
These all involve somewhat more technical conditions. If a stalker suddenly has information about a victim, whereby the source cannot be explained, this may also be an indication of spying software.
The use of a security app is recommended for the analysis of an Android device. The apps evaluated in the test are mostly very reliable at finding the spying tools. If the search is entrusted to a security tool, the search mode should be adjusted to the most sensitive settings. This might take longer, but it yields the best results. The search should use the highest-possible scan setting (usually deep, high or full). On some apps, the item "Activate detection of PUA/PUP/riskware" also needs to be enabled.
It is also possible to use multiple security apps in parallel on one Android device. This works well and often delivers even better results.
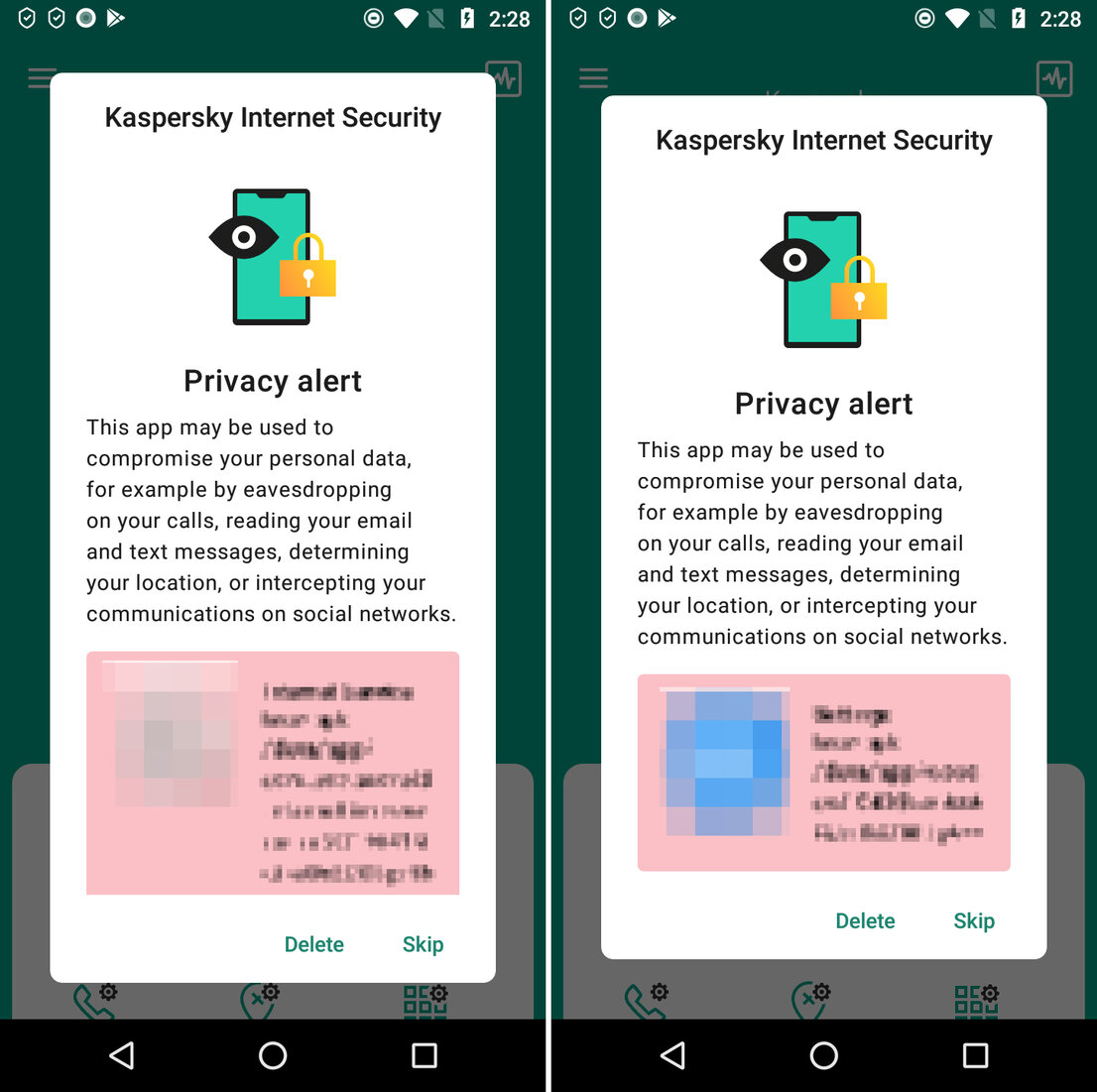
Trend Micro Mobile Security
The user is informed of the risk posed by the software detected 100 percent in the test and receives help on how to remove it
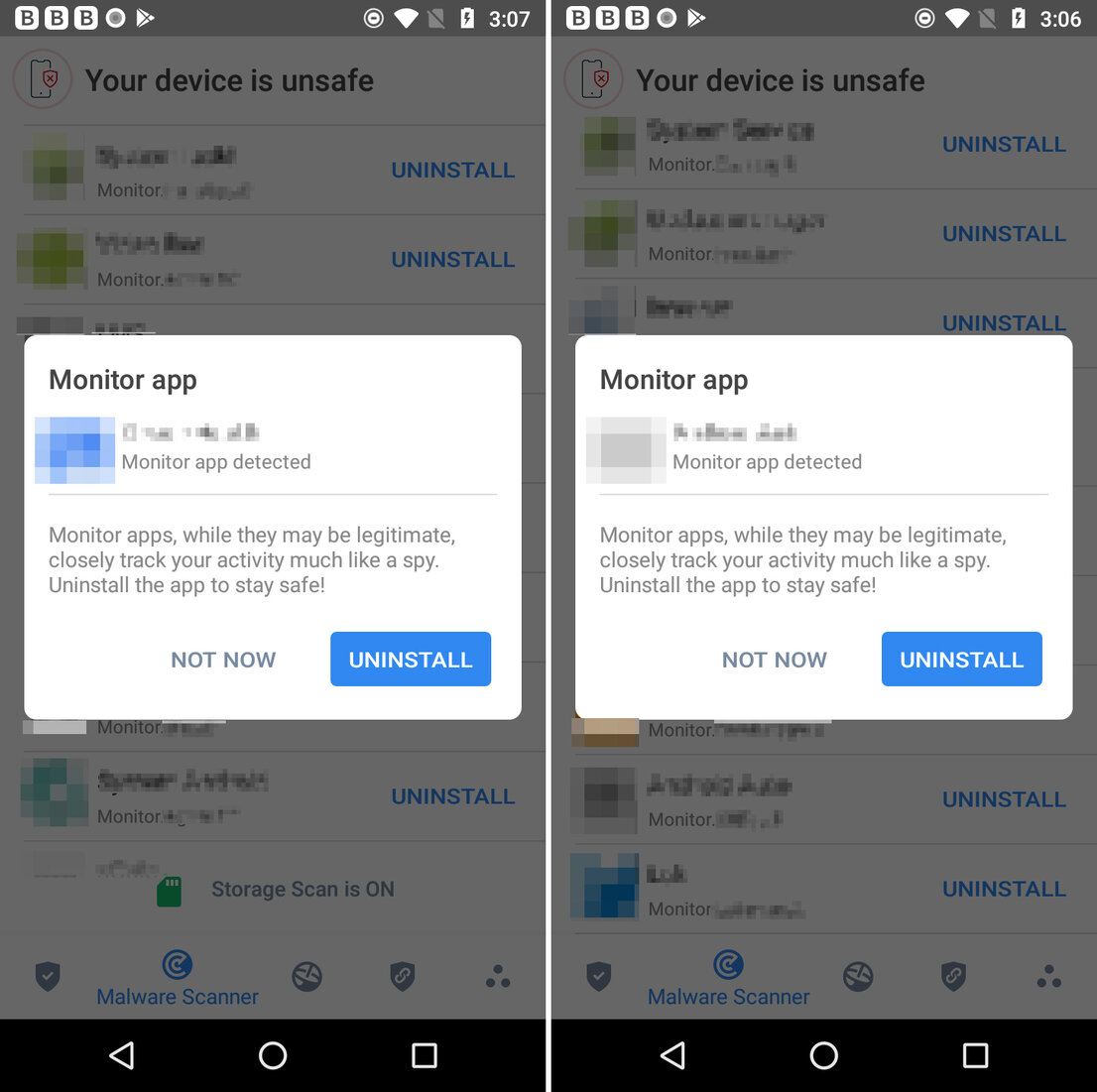
Bitdefender Mobile Security
The app finished the job in short order: it identified the apps in the test 100 percent as spyware, recommended "stay safe" and uninstalled the app
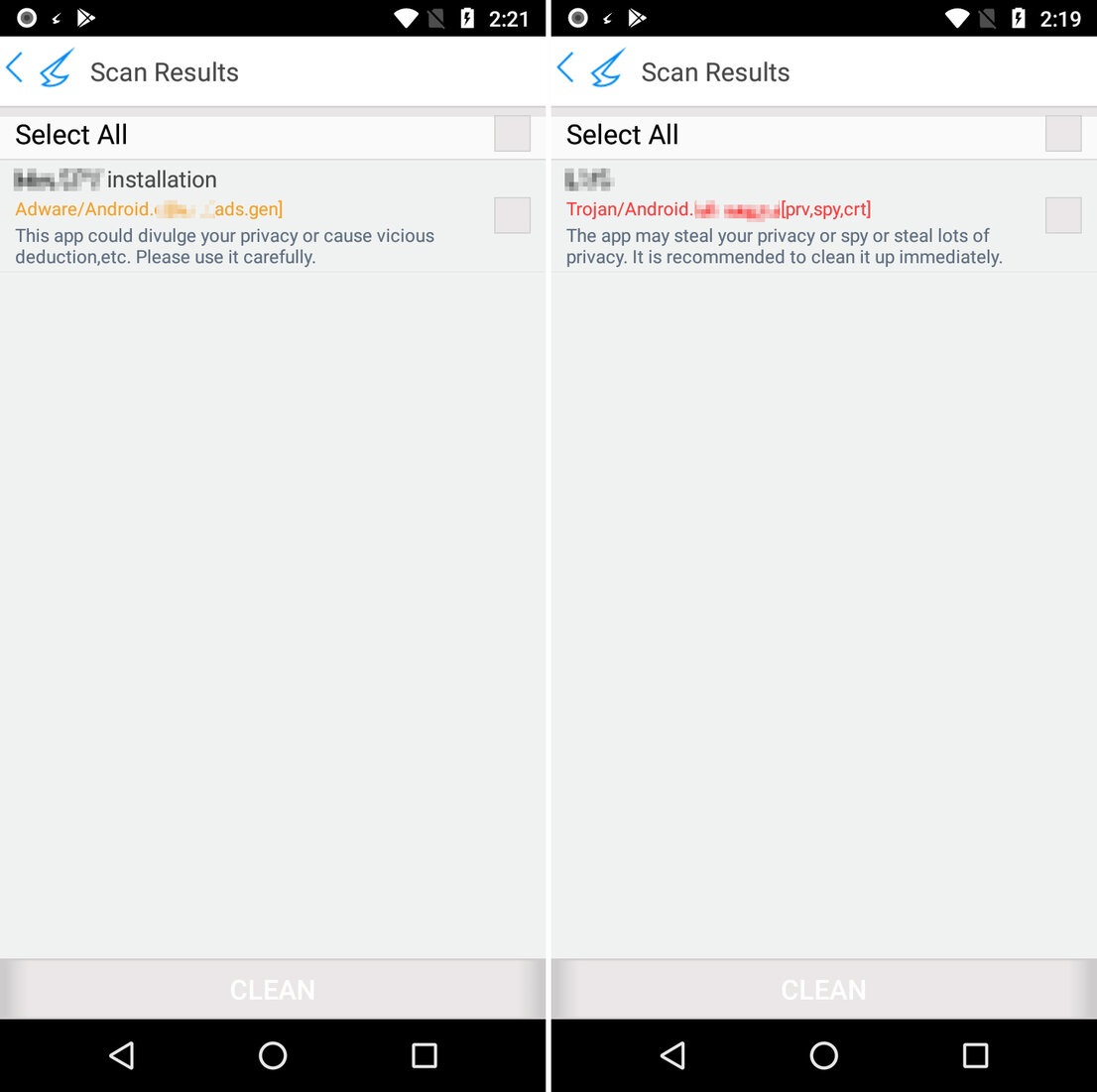
Antiy AVL
While the app did find all the stalkerware in the test, it was not very forthcoming with information – at least it also uninstalled the software
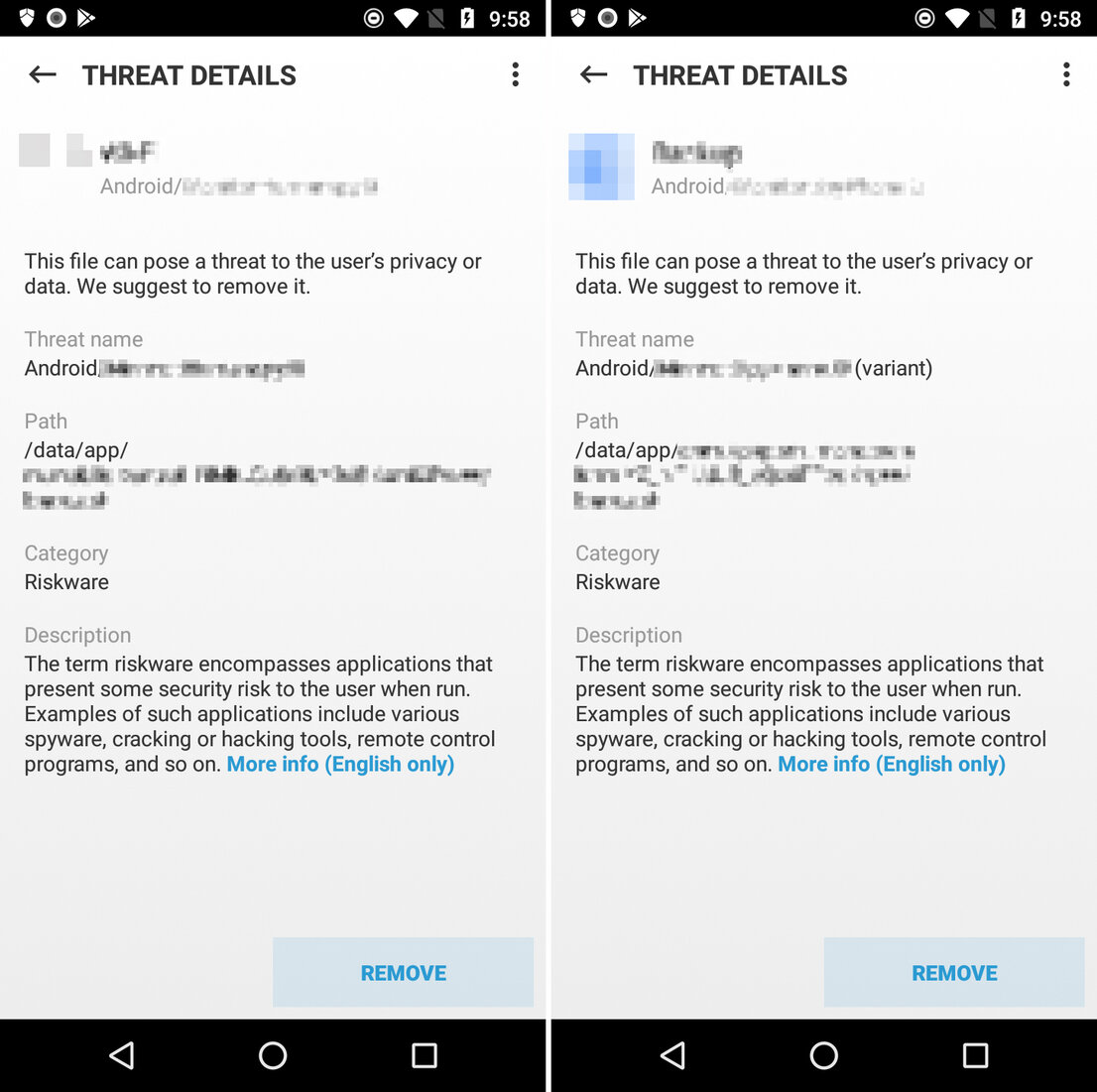
ESET Mobile Security
The security app detected the stalkerware 28 out of 29 times, provided lots of information on each find, classifying it and helping to remove it
Once discovered, should stalkerware simply be removed?
Anyone who finds spying stalkerware on their Android device with a security app must know that the spyware was normally previously installed directly on the device. This means that someone had direct access to the device and thus knows the unlock mode, and probably also the codes or passwords. Those wishing to press charges due to the discovery ought to save the device, along with the stalkerware, as evidence. In extreme cases, experts even recommend using a different smartphone with a new number. Security software also ought to be installed, taking advantage of all available technical security features of the device: e.g. screen lock pattern, PINs, fingerprint scanner or facial recognition. It is also recommended that the passwords for accounts and social networks be changed, as these could be known to the partner or ex-partner.
Those who need the Android device but do not require any evidence can also reset the device to factory settings. The device is then completely empty and needs to be set up again. But be careful in case of existing SD cards – something may still be lurking on them. That is why it is always wise to first format SD cards and then reset the device.
Analyses of stalkerware
ESET also examined in May 2021 the question of what constitutes stalkerware, and listed relevant privacy intrusions. Of the 18 stalker apps examined, more than half committed 10 to 20 violations of security or privacy and thus also of the GDPR or EU GDPR (General Data Protection Regulation).
Those who wish to protect themselves from these forbidden tools or reveal stalkerware that has already been installed are urgently recommended to use the best security apps from the test. Some of the apps evaluated are free; the best apps, e.g. from Bitdefender, Trend Micro, ESET and Kaspersky charge a small licensing fee. But even these apps can normally be used free of charge for a trial period during the first 14 days. And if they immediately unmask some stalkerware, they are more than worth the investment.
Technical tips on examining an Android device for stalkerware
Anyone somewhat well versed in the technical features their smartphone can run their own check to see whether spyware may be lurking on their device.
The commands tend to vary among devices, but most of them are quite similar. Many smartphones also offer a search function in the settings menu that will lead to the proper setting.
Enabled: System / Developer (options)
- Observation: Developer options are surprisingly available as a submenu item or have been activated.
- Consequence: Makes it possible to remotely control the device and install apps on the device.
Enabled: Apps or Security / Install unknown apps
- Observation: On an app (e.g. Chrome Browser), Install unknown apps or Allow from this source is enabled.
- Consequence: Allows the installation of apps from unofficial sources or download from a website.
Security / Device admin apps
- Observation: Unknown apps have admin rights.
- Consequence: Apps with admin rights can only be removed if the rights have been revoked. This prevents removal of an app via the Android Package Manager, as it has a higher permission level.
Input assistance / Service apps
- Observation: Unknown apps are entered as a service.
- Consequence: Allows the reading out and interaction with the Android interface, as well as from running apps.
Google or Security / Play Store or Play Protect
- Observation: Play Protect has been disabled.
- Consequence: Scans and warnings through Play Protect are prevented
Connection or Mobile Network / Data usage
- Observation: An unknown app is generating lots of network traffic.
- Consequence: A contractual data volume is quickly used up and the battery of the smartphone is depleted more quickly.
In an installed security app
- Observation: The installed mobile security app reveals deactivated scan options, "ignored" objects or apps defined as "safe".
- Consequence: "Ignored" objects or apps defined as "safe" are normally excluded from scans and no further warning is displayed for them.