Latest News
March 14, 2016 | Repair tests for Windows
Special antivirus tools put to the test: performance of system rescuers in an emergency
Special antivirus tools are the typical rescue tool of choice after a malware attack. The lab at AV-TEST tested 5 popular special tools for almost a year to see whether they can reliably rescue infected Windows PCs from malware and repair everything again.
Special antivirus tools
can also come to the rescue in an emergency – 5 of them are also included here in the endurance test.
With special antivirus tools, many systems infected by malware can be rescued, cleaned up and completely repaired. At least that's what the manufacturers and many users on the web claim. The labs at AV-TEST wanted to get to the bottom of it, that's why 5 special tools were tested for almost the whole year in 4 elaborate rounds of tests. Each of the 5 clean-up tools was required to scan a total of 53 systems, remove the malware and repair the damage. All of the malware used in the tests were already known to the scanners of the tools. After all, the object was to examine the repair performance and not the detection ability.
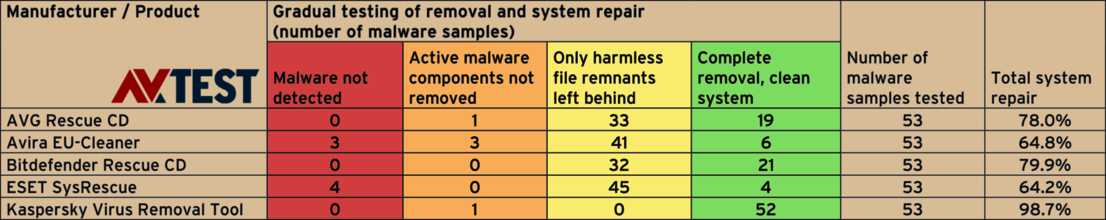
Special antivirus tools in the 2015/2016 repair test
All 5 of the tools tested usually do a good job; with 52 out of 53 cleaned up systems, the Kaspersky Tool performs the best.
Kaspersky Virus Removal Tool
The freeware tool cleaned up 52 out of 53 test systems – the best performance throughout the year.
Comprehensive test regimen for clear results
Testing 53 malware specimens per tool doesn't sound like a lot. But in fact, the contrary is the case. Because for each individual evaluation, the testers had to infect a Windows PC with a malware specimen and document its changes. As most of the malware detects virtual machines, then behaves differently, only normal PCs were used in the test. In the evaluation, each system had to be booted up with a special tool. Afterwards, the detection and clean-up were activated, everything was manually operated, and later the quality of the recovery was rated. In total, this involved 265 individual test procedures with extensive manual labor.
Powerful helpers to the rescue
The test included the following five tools, which are available as freeware on the web:
• AVG Rescue CD
• Avira EU-Clean
• Bitdefender Rescue CD
• ESET SysRescue
• Kaspersky Virus Removal Tool
The results are good, even if some tools in the test did not recognize individual known threats; this was the case with ESET SysRescue and Avira EU-Cleaner. They did not recognize 3 or 4 of the threats, and therefore could not perform any additional operations. In terms of overall system repair, the tools demonstrated decent performance with a rate of almost 65 percent.
This was exceeded by the tools AVG Rescue CD, Bitdefender Rescue CD and Kaspersky Virus Removal Tool. However, in one instance each, AVG and Kaspersky failed to remove the active malware threat components despite detection. Only the tool from Bitdefender is capable of surmounting the two hurdles of detection and removal error-free.
Kaspersky cleans up 52 out of 53 systems
The tools, however, should actually remove not only the most important components of a malware specimen. At the same time, they should also remove the entire file garbage that has been created. In this category, only the tool from Kaspersky Virus Removal Tool does a great job and leaves no garbage behind in 52 out of 53 tests. This correlates to a clean-up rate of 98.7 percent. With all the other tools, there were still file remnants in 32 to 45 tests out of 53.
All in all, however, the other tools also achieved a good result, as they are almost always able to rescue the user from an emergency situation.
The table as an overview
For easier comprehension, the table containing the tested tools has been divided into the following segments:
1. Was the malware detected?
2. Were the active components completely removed?
3. Did any harmless file remnants remain, and were all the changes to the system reversed?
4. Did the security or clean-up software perfectly remove and repair everything?
The last column of the table shows the percentage of total system repair. Here Kaspersky Virus Removal Tool is the clear front-runner with 98.7 percent. Bitdefender Rescue CD follows with 79.9 percent and AVG Rescue CD with 78 percent.
If users don't want to have any close calls with their Windows system in the first place, then they ought to install a security suite. The recently published endurance test "Here is how security suites repair your system after a malware attack" demonstrates that with a good Internet security suite, the risk of a successful malware attack drops almost to zero. Even then, if a suite only recognizes an infiltrating malware specimen too late, the clean-up and repair rates for some products are around 100 percent.
Special case: attacks by ransomware and cryptolockers

Maik Morgenstern, CTO AV-TEST GmbH
A wide variety of malware specimens were used in the test, including Trojan horses, worms or password stealers, but no cryptolockers. They are an extremely difficult special case.
First, it is important to know that ransomware and cryptolockers are almost identical. Experts tend to use both terms interchangeably. Ransomware is used to describe all malware threats that seek to extort money, and in doing so, lock up some function on the PC and partially encrypt the data. Cryptolockers also seek to extort money, but almost always encrypt all the data. The 53 malware specimens used in the test involved droppers, viruses, worms, downloaders, password stealers, back doors, and Trojan horses. Ransomware and cryptolockers were not tested, as these malware threats do not hide in the system, instead they usually immediately trigger an encryption and send the corresponding unlocking code over the web. Accordingly, there is no primary benefit to a clean-up tool's already knowing the malware specimen. The tool must also have the matching base code for unlocking the system. Many manufacturers use a different approach for cryptolockers or ransomware:
Initially, they send out unprotected, yet specially monitored PCs onto the web, to purposely snare a cryptolocker they are seeking. The malware immediately begins the encryption and sends the unlocking code over the web. Using this method, the code is then not only intercepted but also traced back to its storage server. With this method, some manufacturers have found entire servers full of unlocking codes and sent them out to the extorted users. Once the decryption code is available, the experts attempt to evaluate the code and encryption program and to crack the algorithm. If successful, a tool with a type of master key is created and distributed to affected users free of charge.
Sometimes the experts also get lucky: Virus authors are repeatedly prone to bugs in the implementation of the encryption. This allows the encryption tool to be cracked more easily.