Latest News
February 23, 2016 | Repair tests for Windows
Here is how security suites repair your system after a malware attack
Can a security suite completely clean up and repair a Windows system after an infection? In a sophisticated lab test throughout the year 2015, involving 4 test rounds, 7 products demonstrate their protection, clean-up and, above all, repair capabilities.
Especially with the popular drive-by downloads, you don't even need a false click: merely visiting the website is enough to download malware, and an unprotected system will become infected.
So what can you do? Is it at all possible to totally clean up and repair a system after a malware attack? There is an opinion making the rounds on the Internet, that you supposedly have to reinstall your system, otherwise you can't get rid of a Trojan virus. That statement is definitely false, as demonstrated by the current repair test with 7 security suites. During test, the laboratory subjected Windows systems to targeted infections with persistent attackers, followed by clean-up and repair, all year long.
The test included the following products:
• AVG Internet Security 2015
• Avira Antivirus Pro 15.0
• Bitdefender Internet Security 2015
• ESET Smart Security 8
• G Data Internet Security 25.1
• Kaspersky Internet Security 2015
• Microsoft Security Essentials 4.8
Security suites in the 2015/2016 repair test
Most of the programs fared very well, whereby the pre-installed security suites are most prepared to deal with infections.
Total results of the 2015/2016 repair test
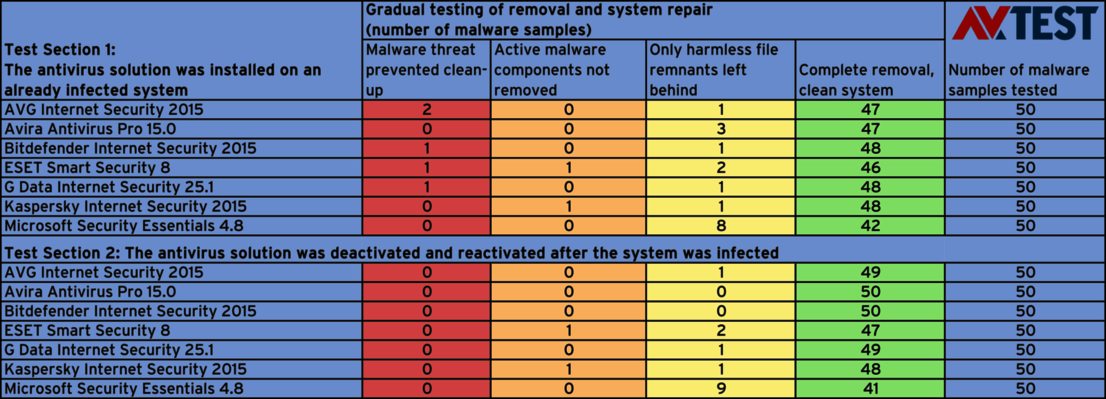
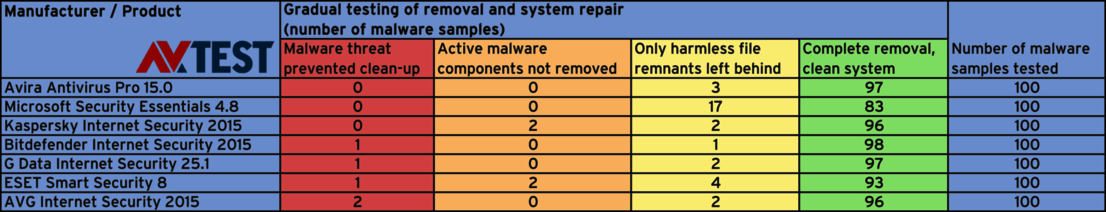
The 7 applications were tested in the lab with different attack scenarios in terms of their performance as clean-up and repair tools.
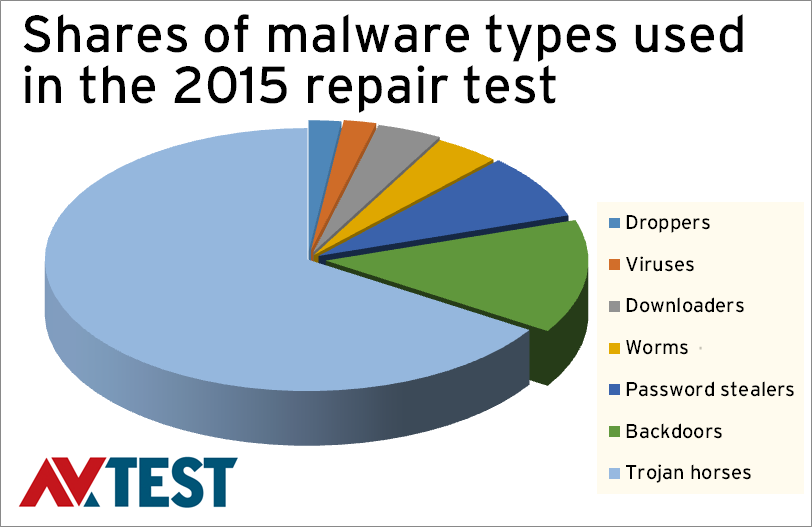
Malware types
The malware used in the test was selected by the lab in proportion to the everyday threat scenario.
Security suites are reliable helpers
The laboratory divided up the test into two segments. The first segment evaluated how well a security package works when installed on an already infected PC. Thus, for users who only resort to security software once an accident has already happened. Here you can have the additional problem that a malware threat may prevent installation. More on that later.
The second segment simulated that a malware threat has not yet been detected and is proliferating throughout the system. Once there is an update, the malware is detected, removed, and the system is cleaned up. As the samples used in the test were already known to all the test candidates, the infection was caused by de-activating, then re-activating, the security suite. The technical routine of the test is precisely explained below in the box, "Test procedure and background information".
Malware threat prevents clean-up
In the first part of the test, the Windows systems were left unprotected and became infected. The lab then tried to install the suites, clean up and repair the system.
Already during the first step, some sneaky malware specimens prevented the installation of AVG, Bitdefender, ESET and G Data. In these individual instances, there was nothing the suites could do. However: throughout the tests, the lab observed that the malware specimens are constantly advancing, detecting security applications and blocking their installation. So it is natural to expect that, for example, malware threat A may not block a suite now, but in a further iteration, A1, it may be capable of doing so in the near future.
For systems with preinstalled security software, the attackers didn't have a chance at blocking anything.
Active malware component left over
In both test scenarios, with installed suites and even with packages installed after the fact, nearly all the infected windows systems were cleaned very effectively in the test. Only the solutions from ESET and Kaspersky were not able to remove the active malware component in one out of 50 cases. The system thus remained infected.
All other products merely left behind harmless file remnants or useless entries in the registry. The lab does not consider this dangerous.
Installed suites help even in emergencies
The most important insight from the test: if a security suite is already installed on the system that becomes infected, the subsequent clean-up and repair task is significantly more successful than with systems without a protection package. The pre-installed Avira and Bitdefender applications, for example, were able to clean up and repair all 50 test systems 100 percent after a targeted infection. AVG and G Data were successful on 49 systems – each application left only one innocuous file remnant behind. It was also interesting to see how Microsoft performed with its Security Essentials. Whether pre-installed or used after the fact – as a rescue tool, it managed to clean all the test systems and only left behind non-infected file remnants 8 or 9 times.
Test procedure and background information
The latest endurance test took place throughout the year 2015, involving 4 test rounds. In two test scenarios, Windows systems were manually infected with 50 selected malware specimens.
During the entire test period, different classes of malware threats were repeatedly tested, as these are constantly advancing. The malware samples used were known to all the solutions at the various test periods and therefore were intended to be detected. In the test tables, clean-up and repair quality was recorded according to the following sequence:
- Did the malware specimen prevent clean-up?
- Were the active components removed completely?
- Were innocuous file remnants left behind, and were all the changes to the system reversed
- Did the security or clean-up software perfectly remove and repair everything?
Test procedure
The test was divided up into two typical infection scenarios.
- On one already infected Windows system, the protection software was installed and the subsequent detection and clean-up was performed. The existing malware specimens partially blocked the installation of the security suite.
- The installed security packages were briefly de-activated, the malware was loaded, and the protection was re-activated. Here, too, the detection, clean-up and repair were recorded.
The scope of the tests was vast. The lab did manage to automate some steps, but each clean-up of a system required lots of manual labor, as some of the steps involved confirming routines on the screen via mouse click. Given the 700 test scenarios, it was partially a very laborious undertaking. As a final step, the files sometimes remaining still had to be classified.
The endurance test was conducted exclusively on real hardware under Windows 7. Virtual environments were not used, as some malware samples detect whether they are in a simulated environment. In this case, they would behave differently. With real hardware, the scenario is as realistic as a user's everyday routine.