Latest News
December 03, 2018 | Parental control
Parental Control: Are the Protection Mechanisms of Operating Systems Enough?
The experts from AV-TEST have examined the dangers facing children using PCs running Windows or MacOS and mobile devices with Android, iOS and Fire OS from Amazon. Each system offers a free option of parental control. The lab evaluated the extent to which this protection is helpful and where it fails spectacularly.
If a child we know or one of our own children were approached on the street or even touched by a stranger, the alarm bells would go off immediately, and we would spring into action. In the digital world, the stranger is not visible, and parents also seldom have a constant overview of what children are doing on a PC or on a mobile device. This is where existing operating systems offer their help in the form of special protection settings for children or with free add-on software. If we take the sales claims seriously, then all we need to do is install and set up the software, and everything is fine. But the lab experts from AV-TEST did not accept that at face value. They wanted to get to the bottom of it, which is why they evaluated and examined the issue of parental control from a totally fresh perspective.
These digital danger areas pose a threat to children
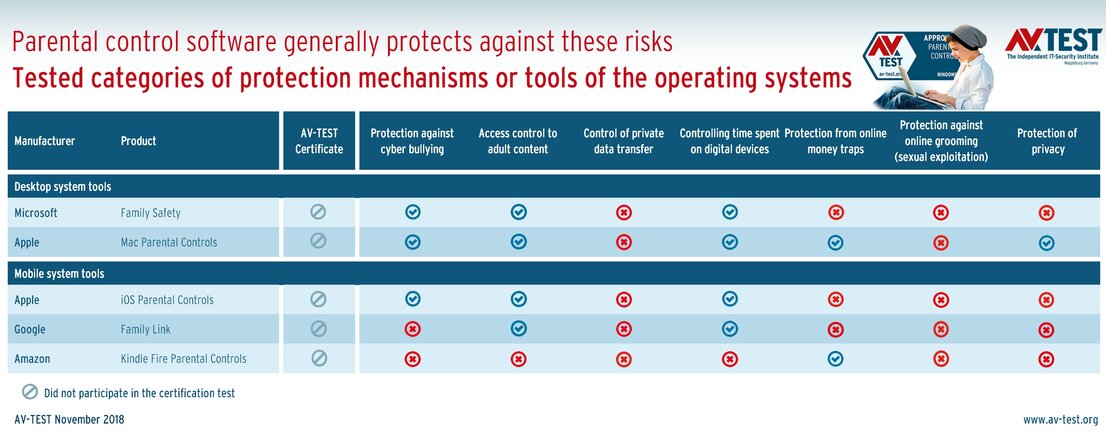
Each software package comes with many settings and tools that are directly comparable. But what is their actual purpose? Is it even meaningful to make a comparison? In order to better illuminate this issue, the lab first analyzed the dangers, defined scenarios to be protected and then categorized the individual protection functions of the system according to the danger areas. Here is what it looks like in practice:
7 danger areas requiring protection or supervision
Each of the following items defines a top-level category for a danger area.
- Protection against cyber bullying
- Access control to adult content
- Control of private data transfer
- Controlling time spent on digital devices
- Protection from online money traps
- Protection against online grooming (sexual exploitation)
- Protection of privacy
The various tools and add-on packages of operating systems were examined and categorized according to these items. Only if an item was truly fulfilled, even by several program functions, then the lab was satisfied and issued a positive rating.
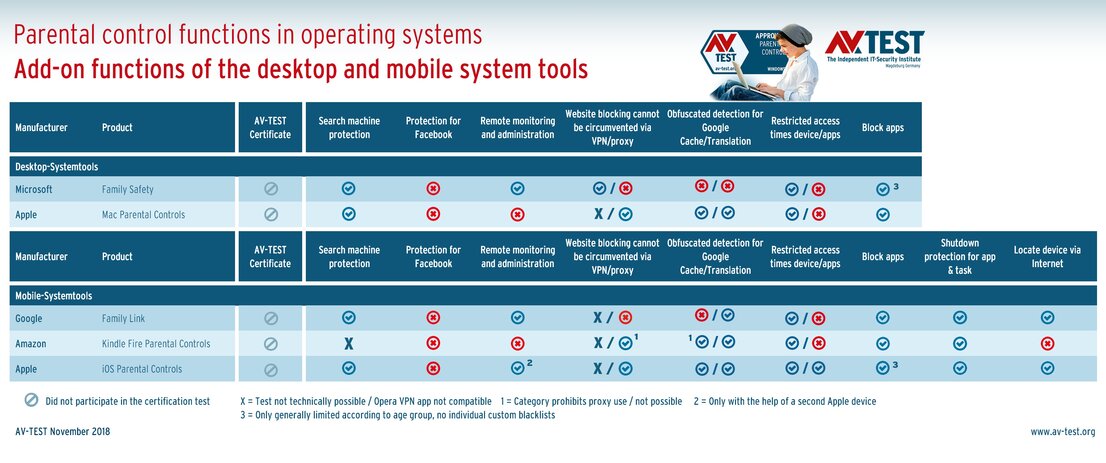
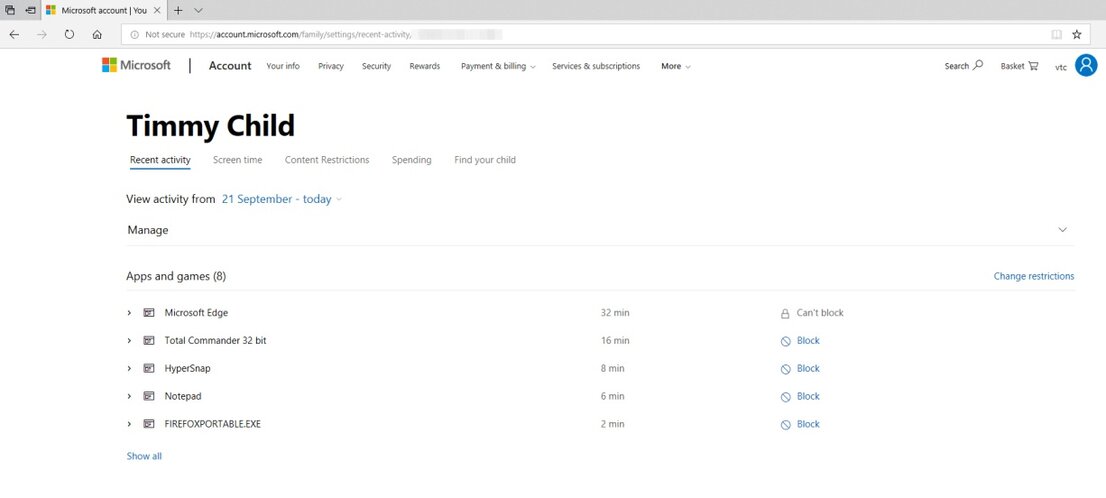
Test candidates: Microsoft, Mac, Android, iOS & Amazon
The test evaluated the following: Windows 10, MacOS High Sierra, Android 8.0, iOS 12 and Fire OS from Amazon; that is an adapted Android system. Each system has internal functions, and the desktop systems have add-on software. The exact product names were: Microsoft Family Safety, Mac Parental Controls, Google Family Link, iOS Parental Controls and Kindle Fire Parental Controls.
The protection systems often have the same configuration: a person or a child is defined based on their age in the system, then a pre-set profile with settings is loaded. Sometimes, it is possible to make a few adjustments to individual items. Many parents without expert knowledge will tend to rely on the profiles to cover everything.
The initial impression was that the testers were satisfied in some areas with MacOS, with Windows and iOS following by a larger margin. Google with Android is hardly reliable, and Amazon protection on the Kindle is a shadow of itself. In most cases, it simply does not work or is unusable. The system suppliers do fulfill some rules, which is reflected in favorable rankings in the table. However, they mostly only offer the necessities. Just how superficial and mostly lackluster the functions are can be seen in the statements in the individual danger areas.
Protection against cyber bullying
The important topic of bullying is often even covered in schools. In the discussion, cyber bullying is a recurring theme, which unleashes the same psychological violence as physical violence in normal bullying. Functioning parental control ought to enable time control and physical location of the device, as well as protection of the profile and activities via a social media check. A very important aspect here includes the report functions, as even without defined content, they quickly draw a pattern of the social media where the communication threatens to careen out of control. Microsoft and Apple MacOS, along with iOS, fulfill some requirements well, whereas by contrast, Google and Amazon practically offer none at all. None of the systems tested offer a function for checking social media!
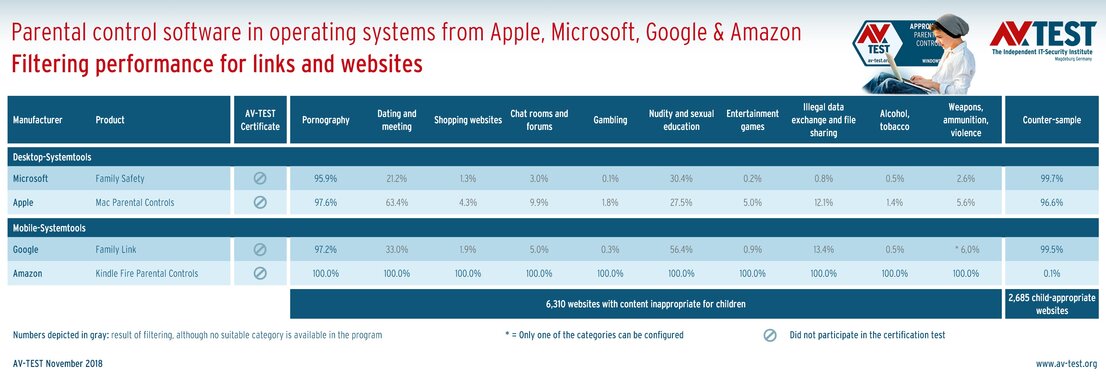
Access control to adult content – the bitter truth
As the Internet is often seen as an uncontrollable source of content, special attention is placed on the filtering of websites and links by the parental control functions. The relevant table shows the results. The iOS system is not found in it, as iOS technically prevents the test. In all other systems, it is striking that they only recognize the category of pornography, neglecting all others. All of them except Amazon do a good job fulfilling this limited task, even in the counter sample with websites suitable for children. Thus, children are indeed relatively well protected against pornography, yet they are allowed to continue accessing gaming sites, hanging out on dating and meeting platforms, unrestrained shopping, surfing on illegal platforms and downloading data, as well as chats & forums on all smutty topics. In this area, there would seem to be a consensus that the systems simply function poorly in terms of “filter performance for links and websites”. Amazon’s Kindle is in fact so secure that it simply prohibits all websites – even the good ones. In real terms, this means: the activated function prevents browsing by almost 100 percent and is therefore useless. It seems reasonable to suspect that most users would therefore simply shut down the function, leaving children completely unprotected out there on the web.
The test lab continues to expect of parental control that when a search engine is launched, the internal “safe search” function will automatically be launched. Thus, with Safe Search, Google, for example, will not display certain web search results, especially those with pornographic content. The function is native to the parental control functions of the operating systems, yet they only arbitrarily switch them on and off. Microsoft, for example, does not like Google and does not activate the protection there. If you are searching with Bing or Yahoo, however, then safe searching runs automatically. Apple has its protection functions exactly reversed, exclusively preferring Google.
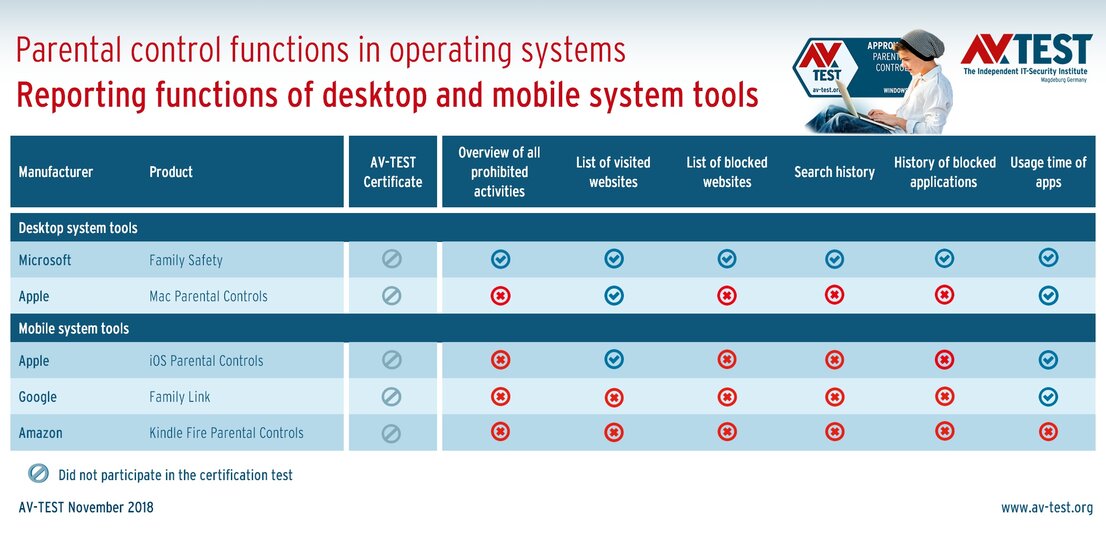
Ideally, the protection systems ought to precisely record what was searched, found and blocked. The report functions of the operating systems do partially record searches, but the information is so sparse that any further analysis provides hardly any overview.
Control of private data transfer – when children become data leaks
Children share large amounts of information, especially via social media, and in the process, they do not realize that they often divulge very personal details. Sometimes, much information on the entire family travels over the Internet. To prevent this, a control function ought to automatically react as soon as personal details such as an address, phone number or the school name are entered. And there needs to be a predefined option of blocking websites, so that children cannot be easily lured onto platforms or into chat rooms. In case it happens anyway, the control function should in turn intervene when personal data is entered. In particular, a social media control is necessary in this context, as that is an area where personal information can quickly leak out. All these activities still ought to be easily found in a well-structured report.
The protection functions of the systems fulfill the requirements quite deficiently or not at all. None of the parental control systems provide a control function against private data being divulged, nor is there a social media control. That is why all evaluated systems fail in these categories. In the area of website filtering, only the term pornography is blocked – the rest is freely available. This also includes all conceivable types of chat rooms and forums.
An additional blatant weakness: the report functions do indeed exist, but they only provide rudimentary reports on subcategories such as the websites visited. There is no search history or list of blocked access attempts.
The fact that reporting functions can indeed contain lots of information in a good layout is demonstrated by special parental control software from other manufacturers. The test results from AV-TEST will follow shortly in the news section.
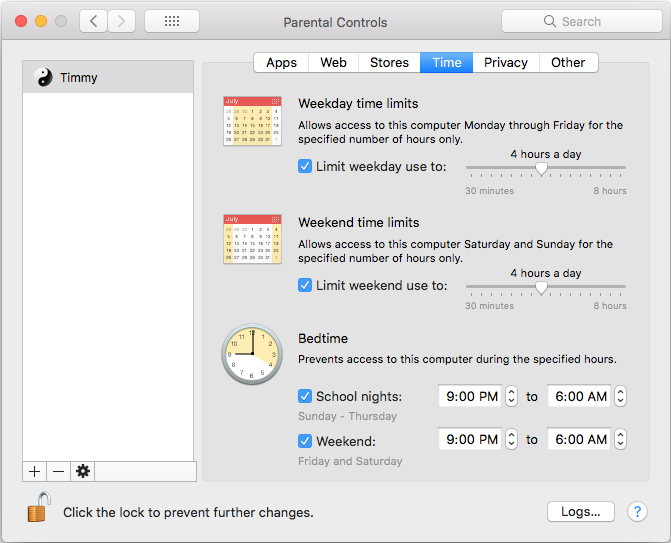
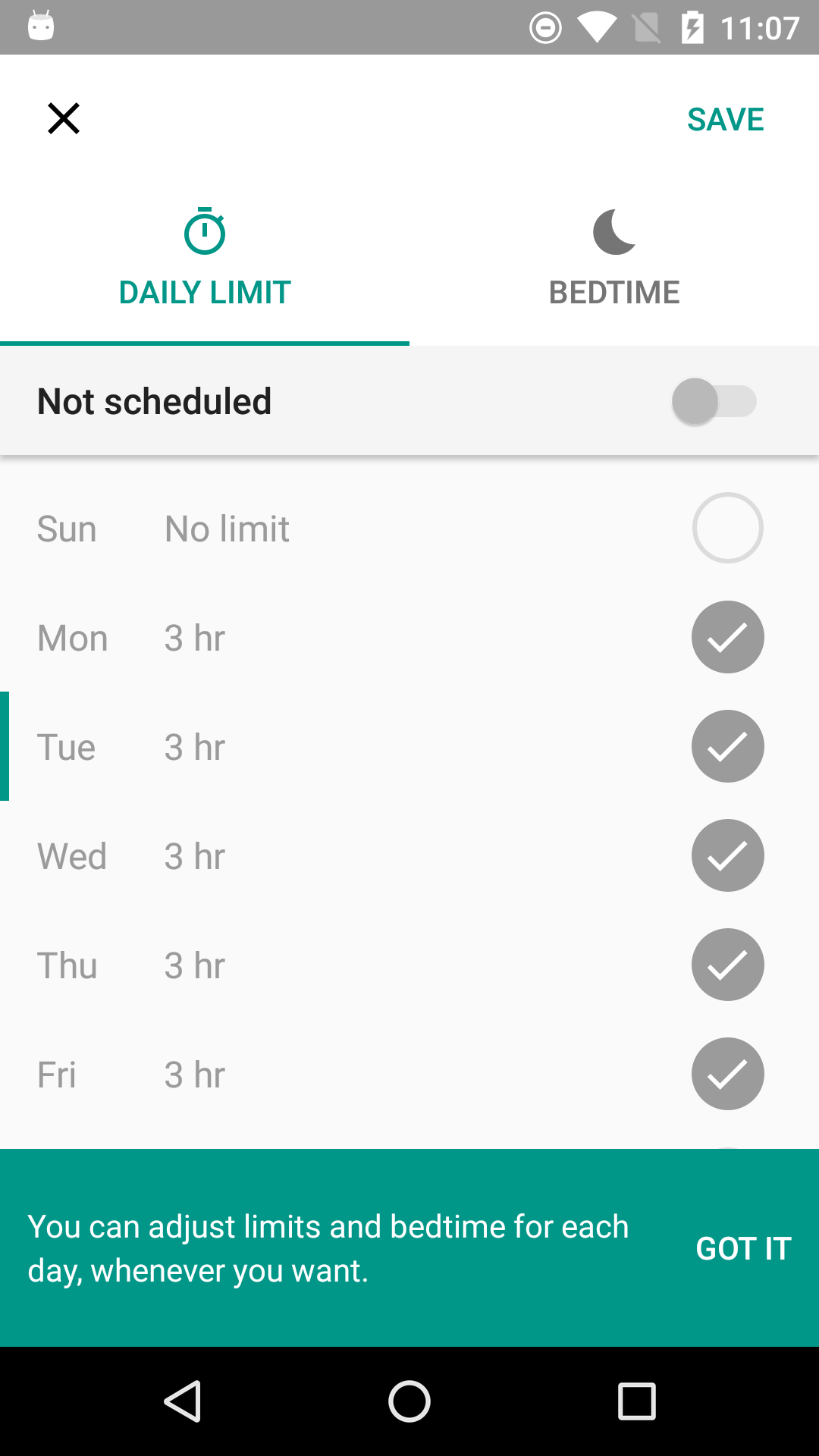
Controlling time spent on digital devices – or is something going on behind your back?
Some children are like that: you give them an entire bag of potato chips, and it’s suddenly empty and the child feels sick to his or her stomach. Many children do not know their limits, and they consume accordingly. That’s also the way it is in the digital world. Minutes turn into hours, homework is neglected, or it is already much too late in the evening. For this, the systems generally offer an adjustable usage time for a device. A selected profile often manages the times for the child. That is what the testers also expected in this case. They are still calling for the option of an app control. Yet this is seldom provided. Usually, only the time spent on the device can be influenced by a profile. A child often plays on particular websites, so naturally it ought to be possible to block selected websites as well. Finally, an internal report function should list the history or the prohibited actions.
While the usage time can be relatively well managed with the operating system solutions, there is no dedicated app control. The blocking of websites only functions as a standard feature for pornographic websites. Other websites have to be painstakingly registered by hand via blacklisting and whitelisting. This means that there is a list for allowed websites and for forbidden URLs. But when a short link or another technical hack is involved, the lists are quickly circumvented.
The testers were somewhat satisfied with all systems and tools. The report functions, however, are only rudimentary and plain vanilla in this area as well. The above-mentioned, still acceptable results, do not pertain to Amazon Kindle Fire, however. It only offers some control over usage time.
Protection from online money traps – quick Euros
Many websites try to earn a quick Euro by selling children something. Usually, it doesn’t involve large sums, as kids would have difficulty coming up with the money, and it would attract attention. In fact, it involves small sums that are paid directly or per prepaid system involving voucher codes purchased at a filling station or convenience store. This allows for anonymous shopping, even if it is totally unsuitable for the child. Parents may not be able to prevent the purchase of voucher codes, but they can prevent their use. To do so, parental control must in turn control apps and regulate the access to websites, e.g. gaming sites where digital add-on tools can be purchased. Advertising luring children into commerce pages ought to be automatically prevented per ad blockers.
The result in the test is sobering: There is only an app control for MacOS and Google Android. For the remaining systems, there is only a general installation ban for apps, which can be switched on or off. The blocking of websites here once again only functions for pornography or for individually-defined websites (blacklisting). For Amazon, by contrast, everything is blocked, as the websites cannot be launched anyway. Only MacOS offers an ad blocker – all other systems lack an adequate tool in this category.
Protection against online grooming (sexual exploitation)
A very important topic is cyber grooming, or translated: online requests of a sexual nature. In this, mainly adults pretending to be a child will approach children on platforms for the purpose of “grooming” them. This means flattering them and thus preparing them so as to initially develop a close, then intimate, digital friendship. The disguised adult often tries by means of conversations and digital gifts to glean more and more information about a child. Once the child has spilled out all their problems, the would-be friend purports to offer help or exploits the secrets learned for purposes of blackmail. Usually, nude photos of the minor are requested, right down to a personal meeting and subsequent child abuse.
This topic is extremely precarious, especially in case of mobile devices, as they are normally accessible around the clock. Some studies document the constant online presence of children by means of mobile devices – even secretly from bed.
Here, experts are demanding that parental control software provide social media control, in particular, but no system offers it. Moreover, there ought to be a control function that automatically reacts if the child has entered predefined personal information. It would be desirable to have an analysis function that automatically recognizes and is able to classify the content of an image. All recorded information should be subsequently available in a report.
All parental control functions of the operating systems fail in this difficult area. Image analysis is already technically possible, but no system includes it in its range. However, no parental control software to date tested in the lab has offered this feature.
Some products available on the market already offer all other functions. A relevant test from AV-TEST will be issued shortly.
Protection of privacy – no help for data thieves
The theft of personal data almost always has only one motivation: Attackers seek to obtain access data and passwords. Identity theft for online attacks or fraud is also a frequent objective. In doing so, attackers use traditional malware-infected e-mails, hijack web servers and distribute banners with malware or request the entry of personal data, access details and passwords on phishing websites.
Naturally, this area of protection is important not only for children but in fact for all users of a device. If a mobile device is only used by a child, however, the child absolutely needs the support of software protection. Because some adults are capable of spotting a counterfeit e-mail containing a malware link. Children are more unwitting in this respect and more likely to simply click or type away.
That is why experts call for a traditional layer of defense against malware within child software, an ad blocker and a function that protects personal data. A function for locating the device is also considered helpful.
The systems from Windows, MacOS and iOS have internal tools intended to protect against malware attacks. Windows does indeed offer this function with the protection tool, Defender, but it offers neither an ad blocker nor does it protect personal data. MacOS and iOS do a somewhat better job in this respect. They offer privacy tools and MacOS even features an ad blocker. Google and Amazon fail to offer any of these functions. Device location naturally only makes sense for mobile devices. That is why iOS and Google also offer it. It is not available for Amazon with Fire OS.
Conclusion: The protection functions of the operating systems only provide half-hearted protection
The test of parental control functions within the systems or with their add-on tools indicates how patchy and imperfect the protection is. The providers of operating systems offer basic protection in some areas – and none at all in other areas. The testers give a plus rating where protection is at least included for the 7 danger areas stated. However, merely including protection is not always enough. The best examples of this are the reporting functions. The systems offer them, yet the content and information quality are more than limited. When filtering websites, while pornography can indeed be blocked, violence, weapons and gaming remain available without any barriers. For the most important area of parental control, the protection against online grooming (sexual exploitation), the systems fail across the board. Things are not much better also in terms of the protection of personal data.
This is not sufficient to properly protect children.