Latest News
November 11, 2019 | Internet of Things
Hells Bells – Five Video Doorbells Put to the Test
Using your smartphone to see who's at the door when you're not at home: Retrofit-capable video intercom systems based on Wi-Fi are becoming a ubiquitous feature in the entranceways of many homes, providing a sense of security. But how secure are these IoT devices themselves, and how do the manufacturers handle the privacy of their customers, not to mention that of their neighbors? The AV-Test Institute examined five video doorbells in terms of security and privacy, uncovering dangerous deficiencies.
Jam-packed with detection features
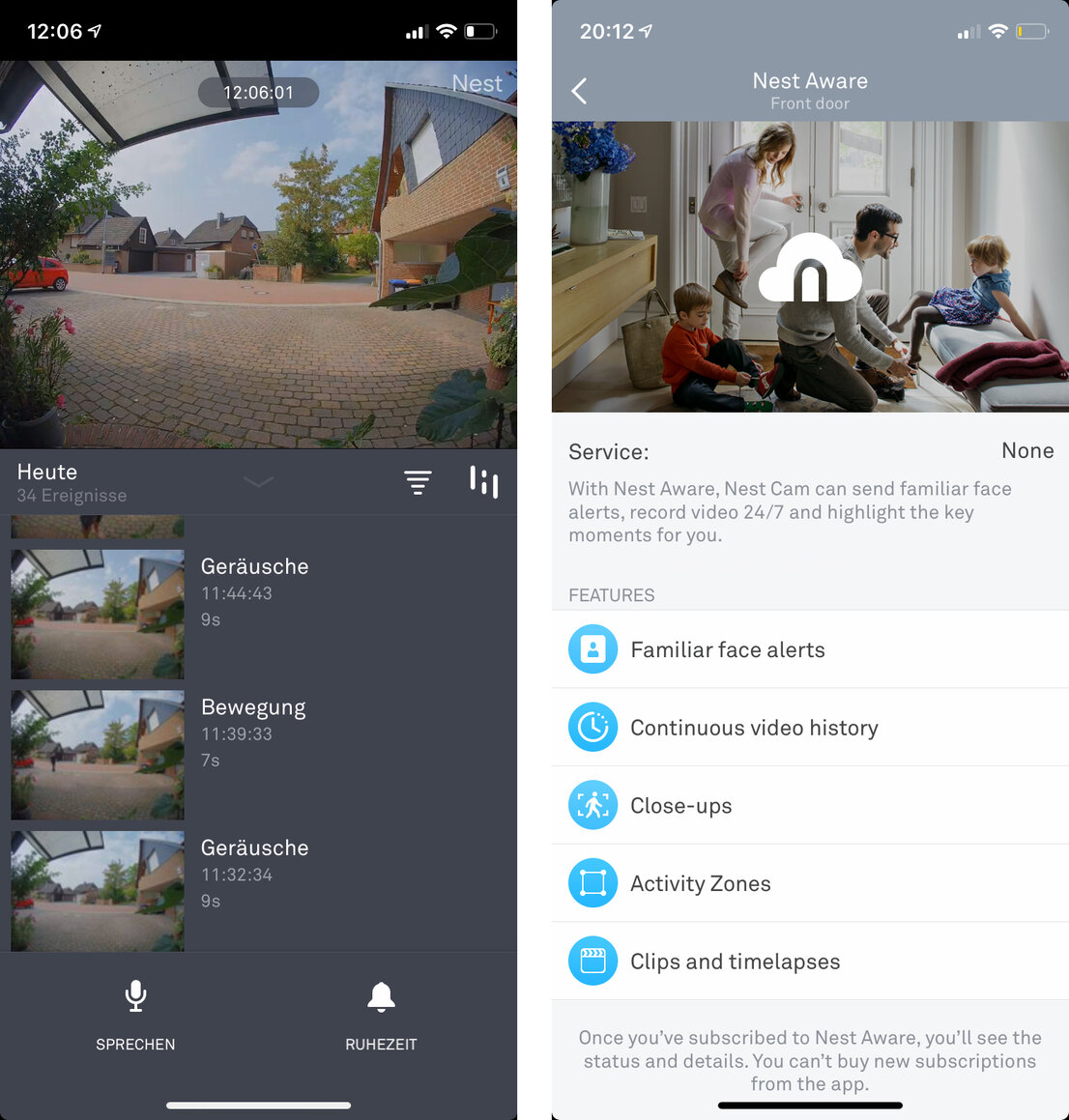
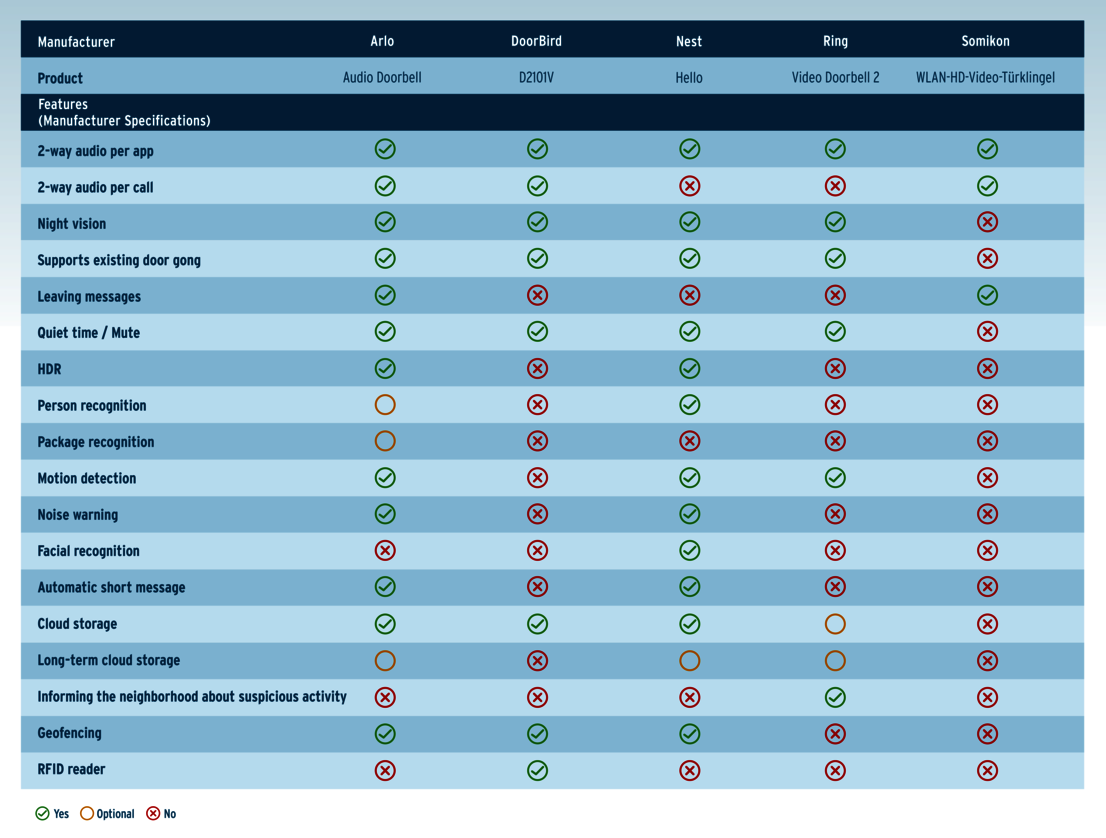
The days are over when children could get away with ringing doorbells and running away. Because today, more and more smart doorbell systems, equipped with a HD camera, sound and movement detectors, can already send a message with a photo to your smartphone if anyone even approaches your door. The cameras on these video doorbells record everything that happens outside your front door and promise "streaming around-the-clock and continuous video recording" in the highest resolution. Using infrared night vision, the corresponding apps receive high-definition photos and videos even in the dark. One of the doorbells tested also offers facial recognition and even announces the person standing at the door, based on the biometric visitor scan. On demand, the recording devices will store photo and video material seamlessly on cloud servers, which the manufacturer offers along with the video doorbells, partly at an additional charge.
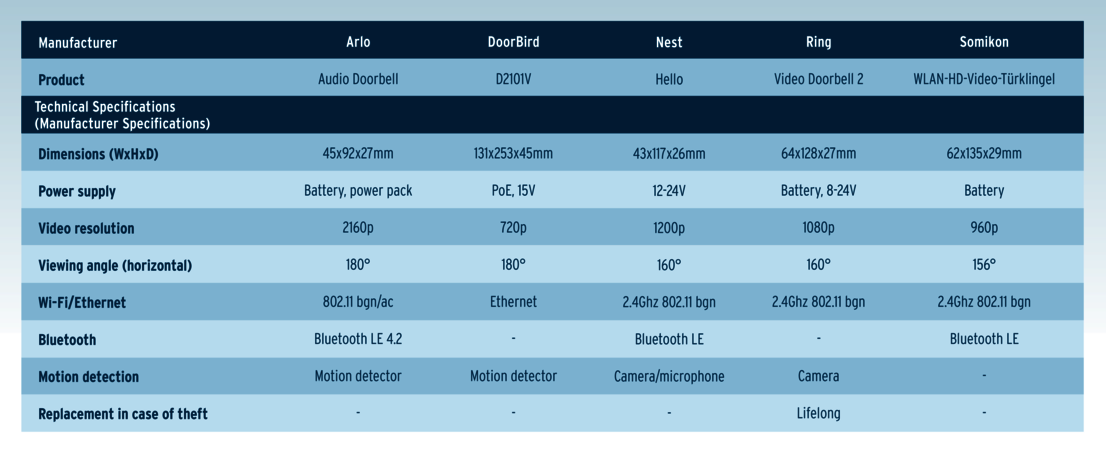
The following devices were evaluated in the IoT lab of the AV-TEST Institute:
In addition to the security aspects highly touted by the manufacturers, video doorbells like these naturally also offer many practical benefits. Unlike traditional intercom systems, some devices are equipped with sophisticated communication features. Given a speedy Internet connection, the app allows 2-way communication with visitors with practically no delay, and visitors in turn can leave voice messages for residents. For delivery services, the video doorbells partly provide for preset responses such as "Please leave the package in front of the door.", which can be transmitted at the push of a button. One tested product also offers package detection. If orders are delivered and left within the scanning range of the camera, users in the United States, at least, will receive an appropriate note. And coupled with a smart door lock, the front door opens automatically for family members, workmen and delivery services. Given an appropriate level of trust, an expected package can then await the customer securely inside the door, instead of at the neighbor's or in front of the door.
Not least due to the comprehensive control capabilities of the video doorbells, users are forced to trust in the security of the products themselves, however, along with that of their manufacturers. Because a continuous hair-trigger video doorbell with data storage in the cloud naturally records not only visitors but also the residents of the home itself. Whether this trust is justified in terms of the recording, forwarding and storage of generated data, was evaluated by AV-TEST engineers in the categories of local and external communication. Also on the test bench: the security of connected apps and online services, as well as manufacturers' handling of user data.
Local communication: DoorBird wide open in the network
Attacks on local communication enable hackers to intercept data, and in the case of video doorbells, for example, this involves spying on film and video material or gaining access to the device settings. This can be achieved by malware infection or manipulation of smartphones that communicate with the video doorbell via Bluetooth or Wi-Fi in the local network. Three of the five devices evaluated – namely those from Nest, Ring and Somikon – are not vulnerable to such hacking scenarios, as they do not communicate within the local network. Only the Audio Doorbell from Arlo, as well as the D2101V from DoorBird do communicate within the local network. Whereas Arlo does almost everything right when exchanging data – only domains resolved via the DNS server were able to be traced, which is unnecessary, but also non-critical – the DoorBird communication turned out to be an easy target of attack: Because the D2101V streams not only data but user names and passwords unencrypted and easily intercepted in the local network. This means: Attackers with access to the local network also receive full access to photo and video files, along with control of the video doorbell. Thus, it is possible for attackers to gain remote access to the camera in order to spy on residents.
External communication: photo and video data unencrypted in the web
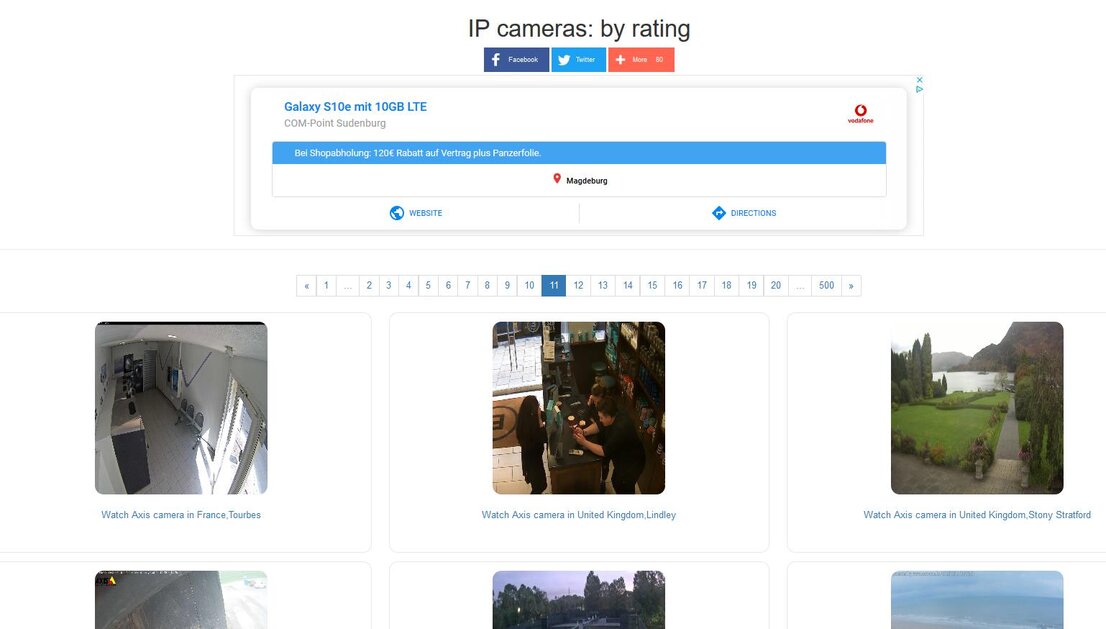
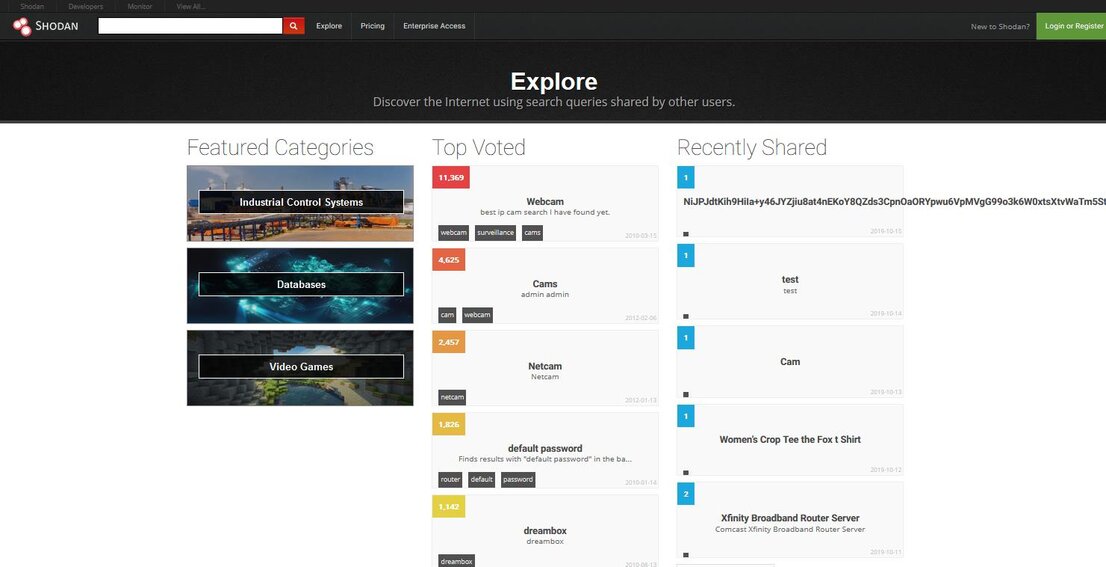
Far more nefarious, however, is the risk of poorly protected online communication. A wide variety of hacking scenarios could be played out via poorly protected web access points: from eavesdropping, spying and manipulating, right down to geo-tracking of cameras. Websites such as Insecam.org or Shodan.io demonstrate the opportunities that relevant vulnerabilities can offer anonymous hackers working remotely. As manufacturers of IoT products really ought to be aware of these hacking scenarios by now, all suppliers really should have done their homework in this area, which is critical to the security of their customers. This applies in particular to products such as video doorbells that are promoted as improving the security of their users. In addition, with images, video and audio recordings, movement profiles as well as biometric detection, these devices collect data that is extremely critical and deserving protection. And they record this type of information not only from buyers and residents but also any person moving into the recording range of the device.
In the IoT lab from AV-TEST, only three out of five products within the scope of the quick tests performed were equipped for known security vulnerabilities: The video doorbells of suppliers Arlo, Nest, and Ring demonstrated proper defensive measures, for example. Standardized attacks on login data of connected cloud services proved ineffective, due to sufficient protection mechanisms against ploys such as man-in-the-middle attacks. Reasonable authentication requirements and features, such as rejection of trivial passwords, account lock-outs in case of faulty log-in attempts, and the use of two-factor authentication, safely blocked most of the attacks staged in the lab. All three products also use encryption technology currently considered sufficiently secure for data transmission between the video doorbell and the app. In addition, product updates were also done via encrypted connections and were therefore not easy to dupe using manipulated files.
DoorBird and Somikon: easy prey for attackers
With the products from manufacturers DoorBird and Somikon, it was a different ballgame: At least both manufacturers do encrypt access to connected online accounts. But the video and audio transmission between the device and the cloud connection, as well as between the cloud and the app, is not fully encrypted with DoorBird. Accordingly, this offers attackers the opportunity to intercept the unencrypted data stream. Apart from such clear security gaps, DoorBird's D2101V also lacks useful security features such as two-factor authentication.
The WLAN-HD-Video-Türklingel doorbell exhibited only a slightly better defensive posture. The Somikon video doorbell also transmits data partially unencrypted, making life easier for attackers. The video doorbell broadcasts unprotected over the Internet not only preview screenshots for the app but also user data and information about the smartphone. Meaningful features, such as two-factor authentication, account lockouts in case of faulty login attempts and the protection of updates, are also missing here. For attackers, both products offer far too many vulnerabilities to be recommended.
App-secured?
In the security check of the respective apps, DoorBird proved to be better equipped against attacks. The apps of Nest and Ring also made an impressive showing. With the Arlo app, IoT engineers found potential vulnerabilities that were introduced by third-party program modules, but which are easy to clean up. Somiko's app programmers have more work cut out for them, however. The application stores data unencrypted on the test smartphones, including screenshots. In addition, the app contains a considerable amount of third-party code and tracking modules that collect lots of user data. The app on the smartphone captures information about installed applications, for instance, and then forwards it to the Chinese manufacturer.
Privacy and data security concerns
When it comes to cameras, especially if they are installed outside your own four walls, protection of your own data is not the only issue. After all, even persons unable to consent to visual recording prior to entering the camera area will find themselves within the angle of view of the devices. Different national rules apply accordingly to such data recording in different countries. In Europe, especially in Germany, the EU General Data Protection Regulation (GDPR) would appear to be one of the most complicated regulatory regimes when it comes to the unsolicited recording of data or registration of persons without their explicit consent. Posting a sign that is clearly visible before visitors enter the recording area of the camera is considered an absolute minimum. In addition, cameras are only allowed to record the user's own private property at best, but not public entrances or the neighbor's property. Additional rules concerning the permissibility of camera recordings and processing, storage and erasure of data also need to be observed.
Ring: the police are watching as well
In the United States, by contrast, the legal limits are much broader and are apparently interpreted quite excessively by Ring and Amazon alike. According to various press sources, Ring is said to have enlisted at least 200 police agencies to market its video doorbells, which actively promoted the cameras to citizens, offering them at discounts and in some cases, even giving them away. In return, police departments were said to have been granted access to surveillance videos created by private cameras via the "Neighbors" app. In addition, for each app download, Ring reportedly credited police department accounts towards the purchase of additional video doorbells. With this dubious offer, Ring/Amazon seems to be quite successful in the United States at marketing its video doorbells, as the map of participating police stations indicates on Google Maps. All buyers will have to decide for themselves to what extent they wish to trust a provider maintaining data protection practices such as these, given that the same company recently was subject to criticism due to its secretly exploiting the data of its digital assistants, as well as indoor cameras.
At least in terms of privacy policies with regard to the video doorbells evaluated in this test, Ring has a clean slate. The manufacturer provides detailed information about the many tracking modules contained in the app and provides exhaustive information about the large amount of data the app collects about users and forwards to Amazon. As a Google subsidiary, Nest also provides extremely detailed information in its privacy statement concerning the data generated, collected, evaluated and forwarded, as is the normal policy by the parent company. Due to comprehensive sensor technology, such as facial recognition, there is also an increased need for clarification here. While Google does indeed provide sufficient information about the relevant features as well as data storage and use, it also claims to be a mere order processor and shifts all data protection duties onto buyers and users.
In its privacy statement, the manufacturer Somikon grants itself extensive rights for data collection and use, which raise clear doubts as to compatibility with the EU General Data Protection Regulation. The app thus requires extensive access to the smartphone and contains many modules for data transfer to Chinese companies. Even far worse was the DoorBird privacy policy, which makes no mention whatsoever of the product and its data collection options, but refers instead exclusively to the company. The company fails to meet its duty to provide its customers information as to the type of data collection, use and storage. This is totally at odds with the current legal situation and therefore had to be punished by the testers, who issued a rating of "insufficient". By contrast, Arlo's privacy statement offered no cause for complaint.
Conclusion: three out of five devices can be recommended
Three out of the five video doorbells evaluated, the Arlo Audio Doorbell in combination with the "Ultra" camera package, Hello from Nest and Doorbell 2 from Ring, earned the top score in the security quick test from the AV-TEST Institute. The current report on deficiencies in data protection at Ring's parent company, Amazon, is mentioned here for the sake of completeness, but it is not an integral part or criterion of this test procedure. Somikon's WLAN-HD-Video-Türklingel doorbell scores only one out of three stars due to security flaws in the test category of external communication, as well as vulnerabilities in app testing and data protection, and therefore it cannot be recommended. Even worse is the D2101V from DoorBird, which shows gross security deficiencies in almost all evaluated test categories and was therefore not awarded any of the possible three stars.