Latest News
July 16, 2019 | Research
Heightened threat scenario: all the facts in the AV-TEST Security Report 2018/2019
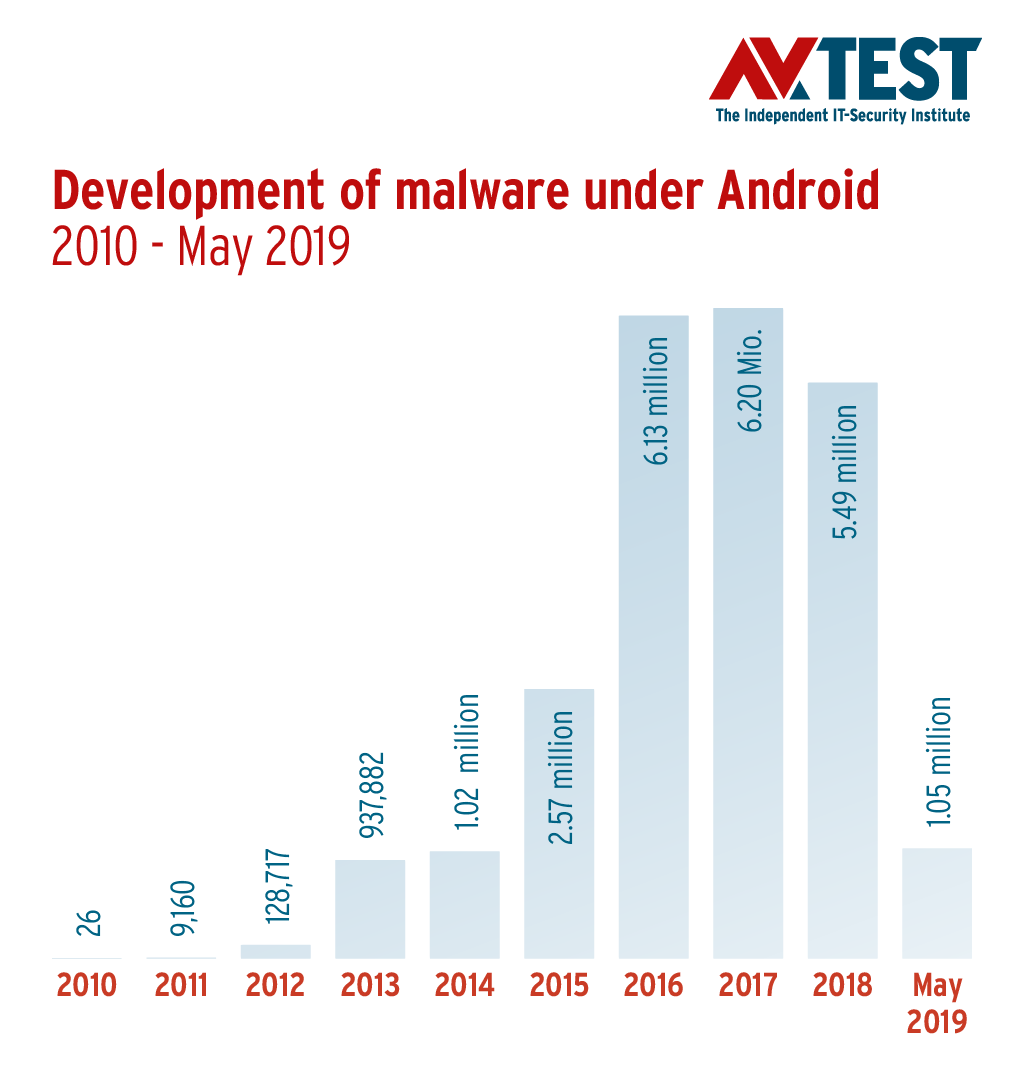
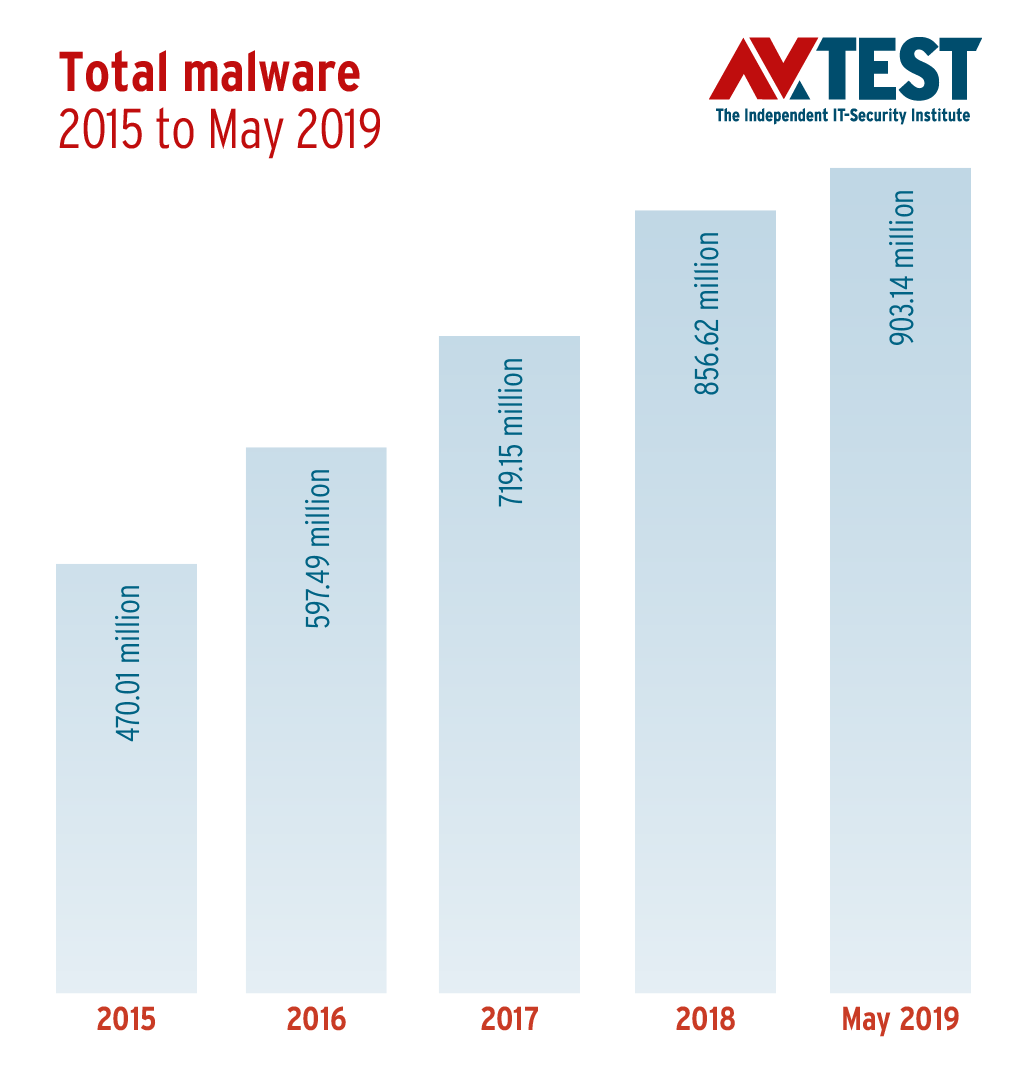
With massive increases in malware statistics, it was anything but quiet on the malware front. Windows and Android systems continue to be the focus of organized crime, yet the malware rate for Apple's macOS has nearly tripled. In 2019, the negative trend is expected to grow worse: In mid-May, the AV-TEST analysis systems recorded the 900 millionth malware program – a frightening record. All the more incomprehensible is the persistence of low protection levels of IoT devices, which are like open barn doors for attackers on the Internet.
Rising malware rate
Last year the development rate of new malware increased again for the first time in three years. With the increase in the new development rate, the threat scenario grew as well: Whereas in 2017, protection programs had to fend off an average of 3.9 malware programs per second, by 2018 that number had already increased to 4.4 per second and thus 376,639 new malware samples per day! Considering the malware development rate of the first quarter of 2019, this trend will continue.
Windows remains the key target of attacks
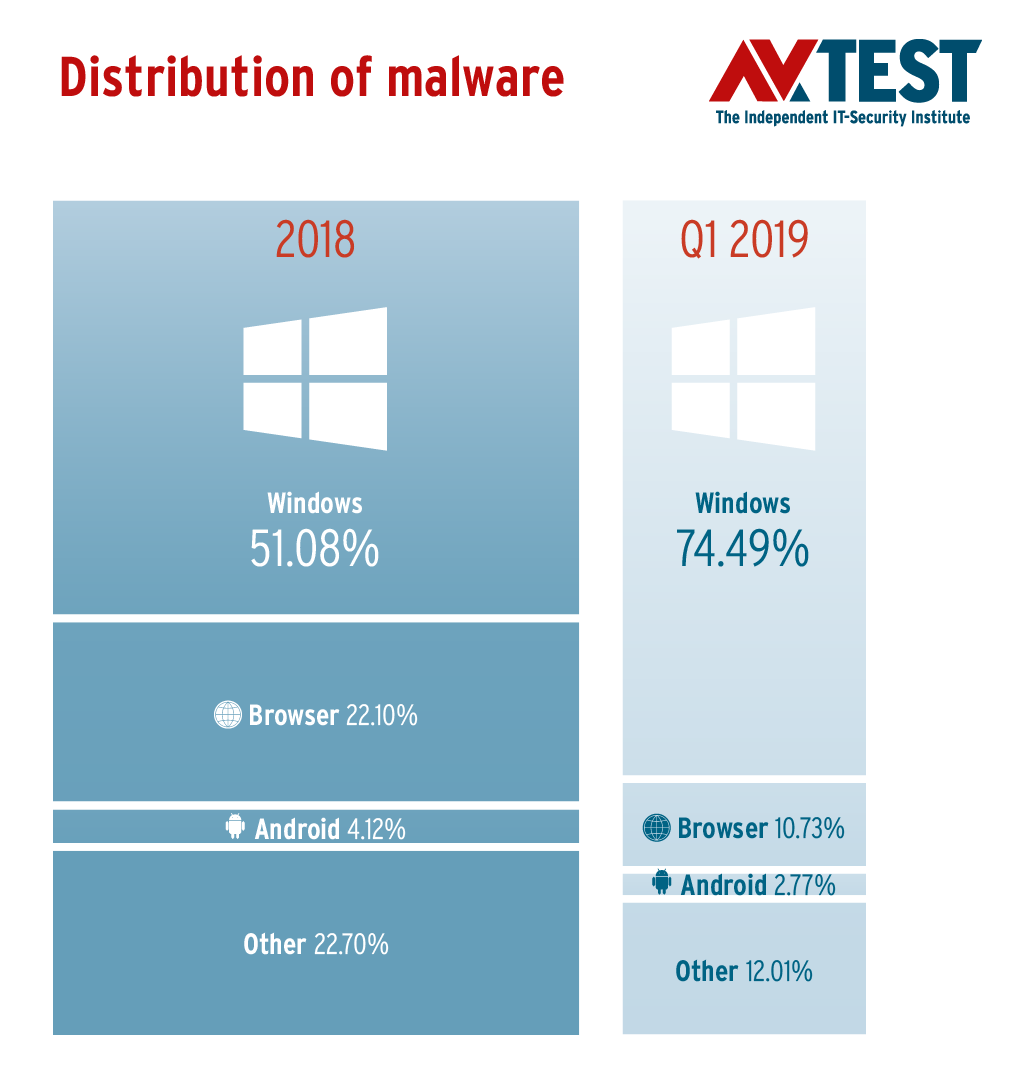
The malware industry continues to have mainly Windows systems in its crosshairs. More than half (51.08 percent) of all newly developed malware programs in 2018 targeted the world's most widely used operating system from Redmond. Due to the continuously increasing defensive performance from protection programs, not only for consumer users but also in the field of corporate computing, cybercriminals apparently felt it necessary to crank out new malware codes at a higher rate. Out of the necessity of remaining commercially successful with Windows malware, the malware industry had no choice but to continuously optimize its products.
For Windows attacks, once again in 2018, cybercriminals deployed Trojans as their first tool of choice by a large margin before other classes of malware. This is hardly surprising, as Trojans, both in terms of functional variety and opportunities to distribute them, are unsurpassed by any other class of malware. Last year, these universal tools from cybercriminals comprised nearly 2/3 of all malware programs developed for Windows (62.51%). By a wide margin, they are followed by classic computer viruses (21.06%) and Internet worms already in a distant third place (6.62%).
Frightening record
Over nine hundred million malware programs are already registered in the AV-TEST Institute's database.
Windows remains under fire
51% of all malware programs in 2018 targeted the world's most widely used operating system from Redmond.
Crypto miners supplant ransomware
At the beginning of last year, the AV-TEST Institute announced the "age of the crypto miners" based on the statistics of the first quarter. And the forecast for ransomware measurements also turned out correct. And thus, digital blackmail by means of ransomware declined in 2018, which is the good news. On the one hand, the anonymity of digital currencies continues to ensure criminals a high level of security in bilking victims, and the use of ransomware requires far less overhead compared to the business with other malware programs. On the other hand, the business model lives and dies with the willingness of the involuntary customers to pay. And that is precisely what appears to be declining in private households. Contrary to the ransomware trend, the use of crypto miners increased sharply in 2018 as expected, yet was subject to severe fluctuations. The proliferation of new malware samples for the mining of digital currencies, thereby exploiting third-party resources, found its high point in the first quarter of last year. The detection systems of AV-TEST recorded over 180,000 samples in March 2018.
macOS malware almost tripled
Whereas the rate of new malware developments for Android, the largest mobile device operating system, experienced a slight lull in 2018, the sample numbers of new malware for macOS nearly tripled. In terms of percentages, the share of Mac malware, with 0.15% of the overall total of newly developed malware programs, was negligibly low. It should not be forgotten, however, that the 94,966 new malware samples in the year 2018 face off against a massive number of Apple devices without sufficient virus protection. Because just as with mobile devices under Android, with respect to the installation rate of effective protection programs on Apple computers, there is lots of room for improvement. In 2018, the AV-TEST Institute's detection systems discovered an average of 7,913 new malware samples per month for Apple's operating system. In total, 94,966 Mac malware samples were tallied last year.
IoT devices to a large degree unsafe
Basically, IoT devices and services offer a variety of attack vectors: The main targets of criminals are the user devices themselves, connected apps and mobile devices on which the applications for controlling IoT devices usually run. The back end of the manufacturers used by the server structures and device connectivity, as well as the transmission paths of essential and other recorded data are further gateways for digital attacks. Nevertheless, IoT devices with inadequate IT security continue to take the market by storm. And for the growing number of unprotected devices, a flood of malware is already waiting, which currently mostly want to commandeer their concentrated and networked computing power.
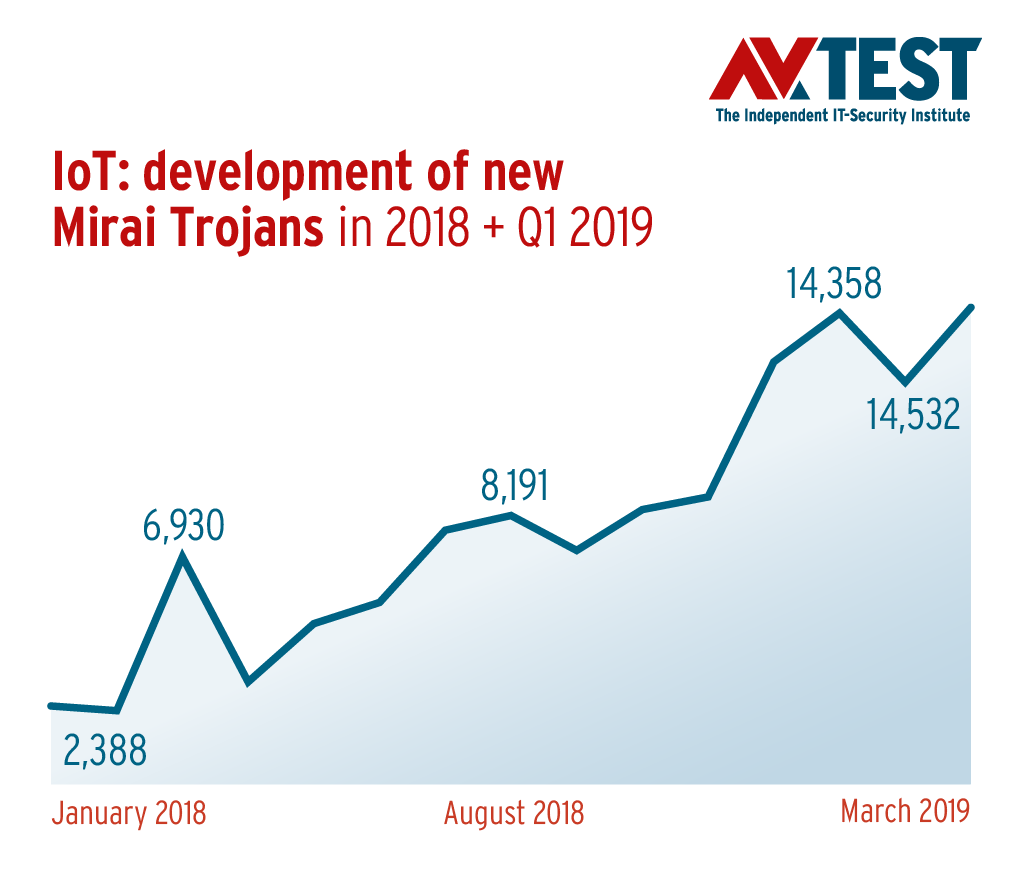
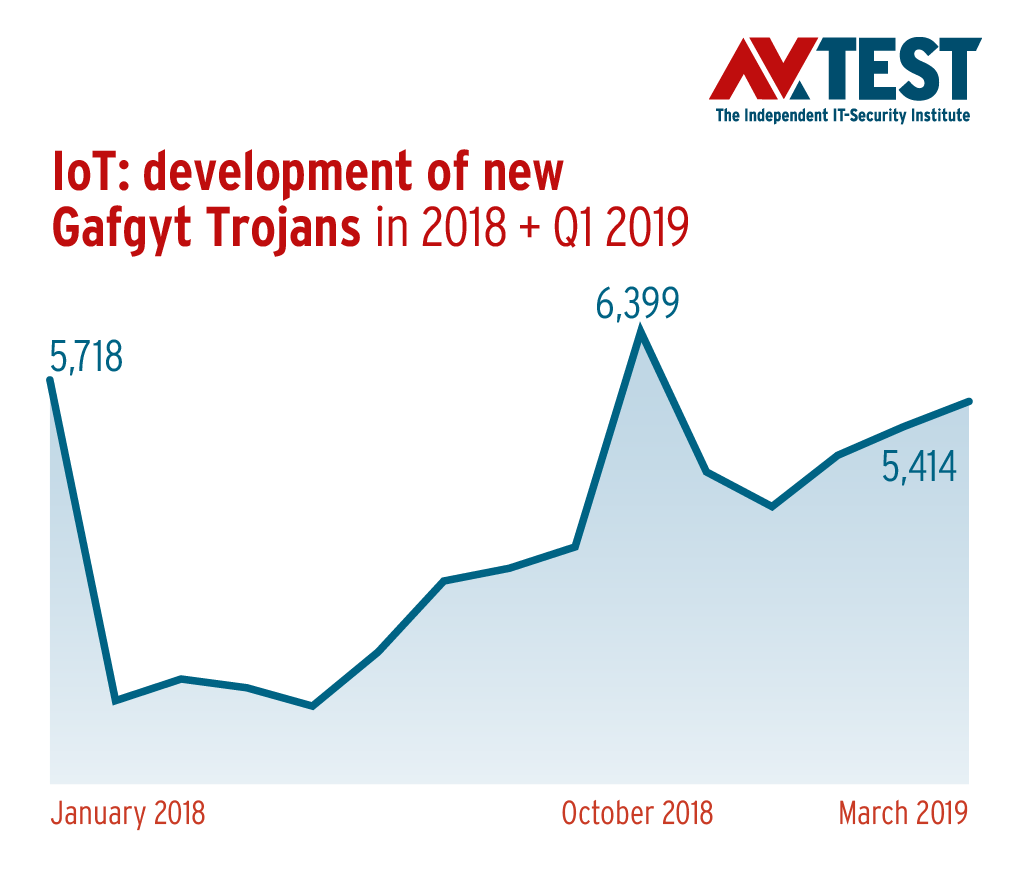
Mirai, a malware sample known for years, accounted for more than 40 percent of the total malicious code for IoT devices (41.19%) in 2018. Unfortunately, the steep development curve of Mirai samples does not indicate a commensurately high learning curve for device manufacturers, who should have been aware of these dangers since October 2016 at the latest. However, a response does not appear to be forthcoming, and criminals accordingly continue to deploy Mirai successfully for attacks on IoT devices and connected infrastructure. The sample numbers of the main malware for IoT devices have been exploding since the beginning of last year. With 78,186 variants, Mirai clearly led the ranking, followed by IoT Trojans such as "Vit" (37,807 samples), "Gafgyt" (36,769 samples) and "Tsunami" (2,959 samples).
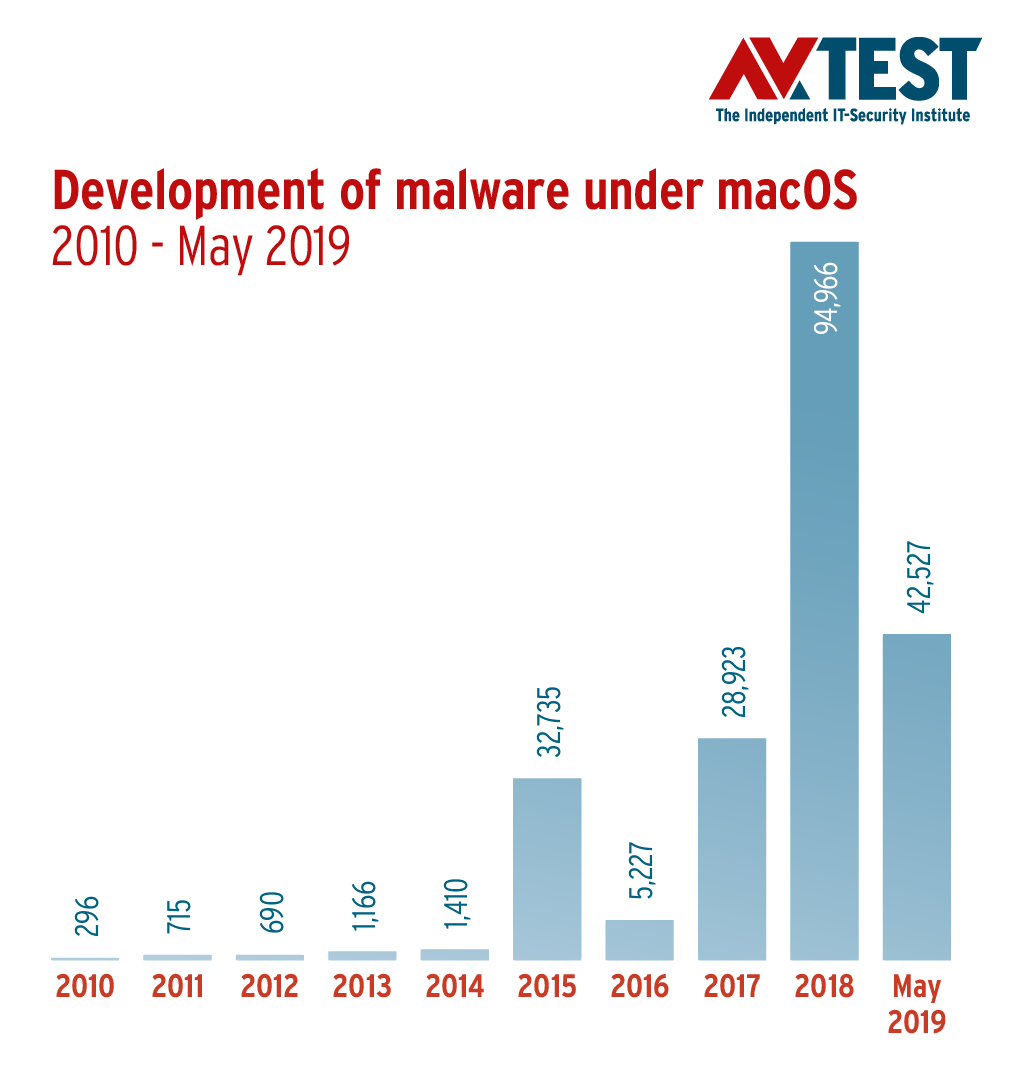
Mac malware
In 2018, the AV-TEST's detection systems discovered an average of 7,913 new malware samples per month for Apple's operating system.

Crypto miners surpass ransomware
The detection systems of AV-TEST recorded over 180,000 crypto miner samples in March 2018 alone.
Download the complete report for free
Additional information and detailed metrics on the proliferation of malware and other malicious applications are provided in the comprehensive Security Report by the AV-TEST Institute. You can download the report here free of charge.
Download Security Report 2018/2019
Regular tests of smart home products and information on IoT devices with certified security can be found in our IoT Security Blog.
Would you like to know which protection program and which security app offers the best possible protection for your devices? AV-TEST offers you information on detection rates, usability and performance of all known security solutions, also free of charge. You can look up the results of the tests carried out monthly.
If you would like to regularly keep up to date on information from our institute concerning all aspects surrounding the topic of IT security, such as tests on smart-home products, wearables, fitness trackers or health apps and parental control applications, you can receive prompt and current information via our monthly security newsletter.