Latest News
October 30, 2018 | Internet of Things
Being Secure Rather Than Just Feeling Secure: 13 Security Starter Kits Put to the Test
The days are growing shorter. For some people, it prompts the urge to spend the evening hours reading a book, while others are concerned about burglars, whose heinous craft is made easier after sundown. While police crime statistics (PCS) do indeed indicate a decline of 23 percent in the number of burglaries, many people have a growing need for security. Many manufacturers of smart home products offer relevant security packages. The AV-TEST Institute evaluated 13 of them.
Smart home packages for burglary protection are now available at affordable prices, e.g. as "Smart Home Starter Kit Security". These smart home base stations are intended to make the owner's four walls not only more comfortable but safer. In fact, most of the components fulfill several functions at once: When opened, smart window and door contacts send not only burglary warnings to the user's smartphone, in communication with networked thermostats, they also prevent unnecessary heating, thus saving energy costs. Smoke detectors used as sirens warn occupants of fire danger, yet at the same time they can also scare away burglars. Motion sensors provide for dimmed lighting when going to bed at night, but they can also shine glaring light on burglars. On the other hand, the IP cameras contained in some starter kits are used mainly for surveillance.
Unlike traditional alarm systems, the devices tested here are smart home base stations with an additional alarm function. In the IoT lab of the AV-TEST Institute, 13 of the latest smart home systems with a burglary protection function in the price segment from 50 up to and exceeding 400 Euros had to show their stuff. The testers evaluated the devices not only in terms of burglary protection and signaling but also in the area of IT security and data protection. The test revealed that the most expensive products are not always the best. The most economical product from a discounter, for example, successfully fended off many of the testers' attempted attacks, whereas significantly more expensive products offer at best a feeling of security, due to woeful deficiencies, e.g. in tamper protection.
The following products were put through the rigors at AV-TEST:
Focus on IT security and alarm functions
All the smart home starter kits evaluated here offer additional functions alongside the security features examined. The participants in this test, however, are exclusively products that feature security functions as a "security starter kit". That is why the testers evaluated not only the IT security of the smart home products but also the failsafe protection of the base station and the delivered components as an overall system. Because in the function as an alarm system, heightened requirements apply for smart home bases in the IoT test labs of AV-TEST. Thus, the security kits were required not only to measure up in the standard test categories of security of external and local data communication, app security and data protection, but were additionally evaluated in the practical test in terms of reliability of security components, their failsafe protection, along with their ability to thwart sabotage attempts.
In addition, the security experts at AV-TEST examined the products in terms of their offering key security features and the option of upgrading the starter kits as needed within the owner's own four walls. However, the relevant function table served exclusively as a guide and did not enter into the IT security rating of the products.
External communication: unsecure updates and ancient gaps
In this test category, the IoT experts determine whether the data communication between the IoT device and the connected online services is adequately secured through encryption. For data transfer, this includes not only device-server communication but also the security of the update function. The test regimen also looked at web applications and how well they were protected through secure authentication procedures. In the test of the smart home security starter kits, the communication channels of the base stations were not the only elements subjected to scrutiny, due to the vast array of possible hacking scenarios. The testers also evaluated the vulnerability of accompanying hardware components, such as IP cameras, window contacts, motion and smoke detectors, in terms of manipulation and sabotage attempts.
The security kits from Bosch, Blaupunkt, Devolo, Gigaset, iSmartAlarm, Medion and Telekom (Qivicon) showed no weaknesses in this test category, whereas the other half of the test field did. In most cases, inadequately protected update functions offered attackers an opportunity for manipulation. The Fibaro product, for example, obtained updates via unencrypted http connections, whereas communication with the base was secure per https.
For D-Link, the communication of individual components, in particular the unsecure communication of several camera models, proved to be a clear vulnerability. This can be exploited by hackers, both via the local Wi-Fi and on some models via the Internet. In the worst case, hackers can gain control of the unsecured camera in the network for spying on the premises. The fact that relevant security deficiencies still exist is baffling, especially because AV-TEST alerted the manufacturer to it already in January of last year. D-Link would do well to quickly remedy the known severe security deficiencies for the protection of its customers.
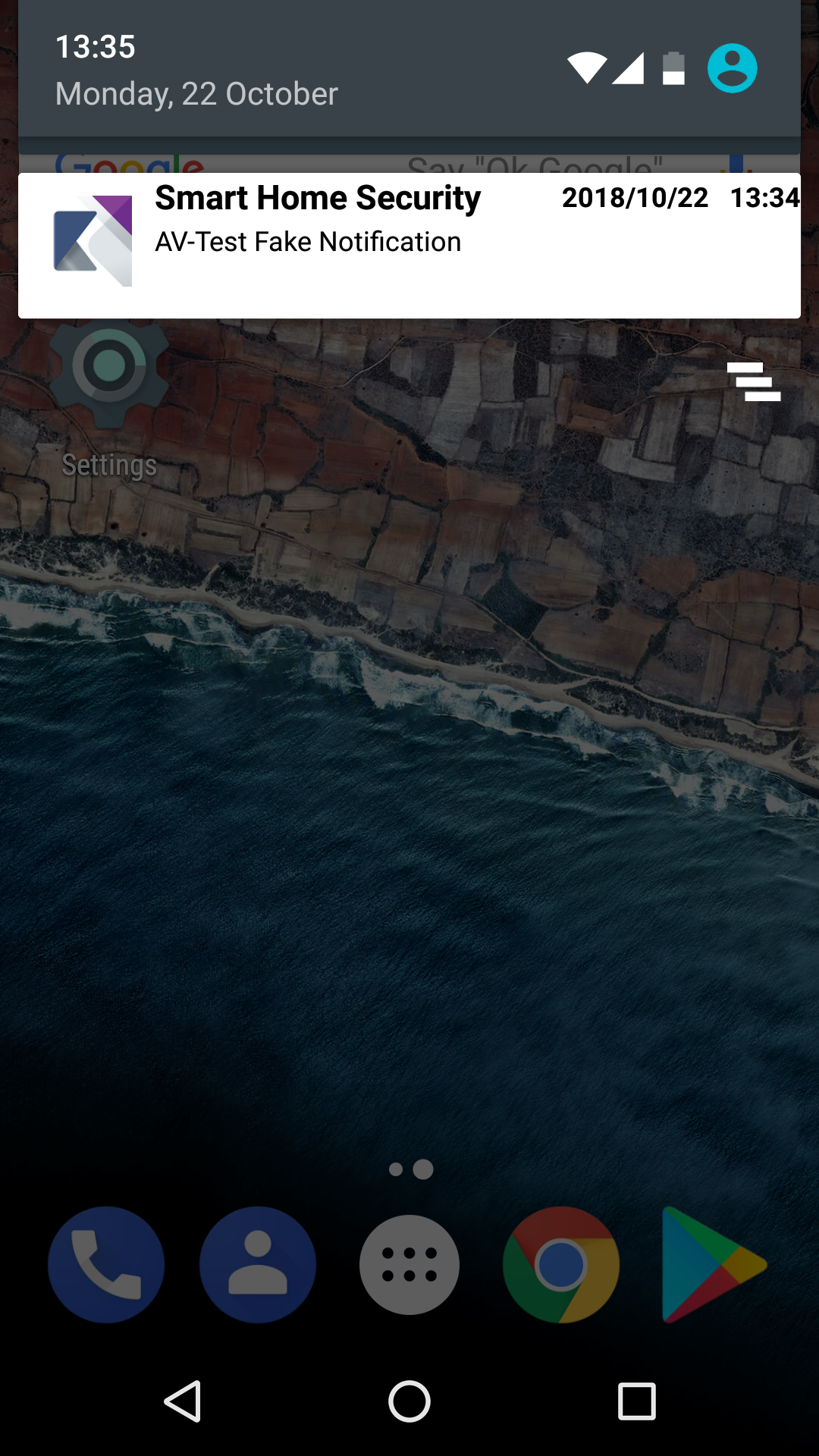
The products from König, Panasonic and Xiaomi exhibited even more egregious security leaks. In the "Smart Security Kit" from König, not only firmware updates but also security notifications were sent via unencrypted connections and could thus be intercepted, manipulated or blocked, for example. On Panasonic's "KX-HN6011", the encryption proved vulnerable for so-called downgrade attacks. Due to implementation errors, this method allows attackers to reset what is actually secure encryption back to an unsecure version status (downgrade to SSL 3.0). For the "Mijia 5 in 1" from Xiaomi, on the other hand, the testers, using an unencrypted connection, were successful at intervening in the process of changing the password. Although the password was not transmitted in plain text, interceptable information nonetheless provides hackers unnecessary clues that can be used towards manipulation attempts.
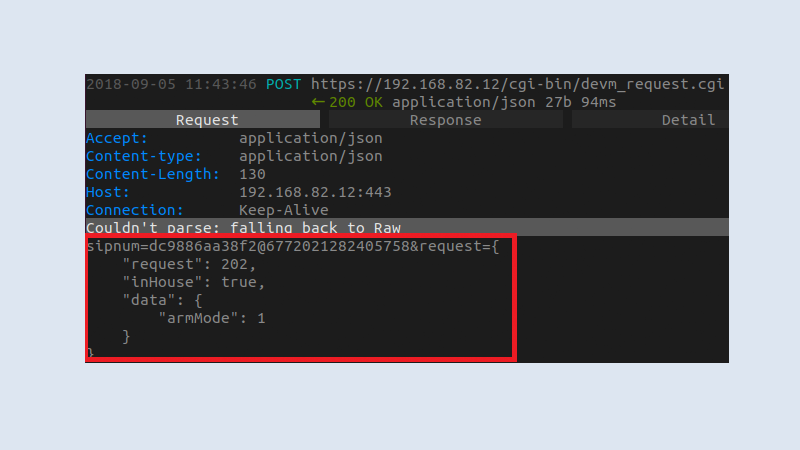
In the test, Panasonic's smart home system
proved vulnerable to downgrade and replay attacks, making it possible to partially control and manipulate the functionality of devices. The reason for this is that established connections rely on outdated implementations of the encryption protocols used in the process.
Local communication: man-in-the-middle attacks and missing encryption
Virtually all products withstood the evaluation of local communication between headquarters and apps without major issues. Five products, specifically those from Blaupunkt, Devolo, eQ-3, Gigaset and iSmartAlarm, do not offer relevant communication at all. For the products from Bosch, Medion and Telekom, the data transfer per Wi-Fi or Bluetooth proved to be secure. Only Fibaro, König, Panasonic and Xiaomi revealed vulnerabilities, and in the case of König and Panasonic, they were in fact significant.
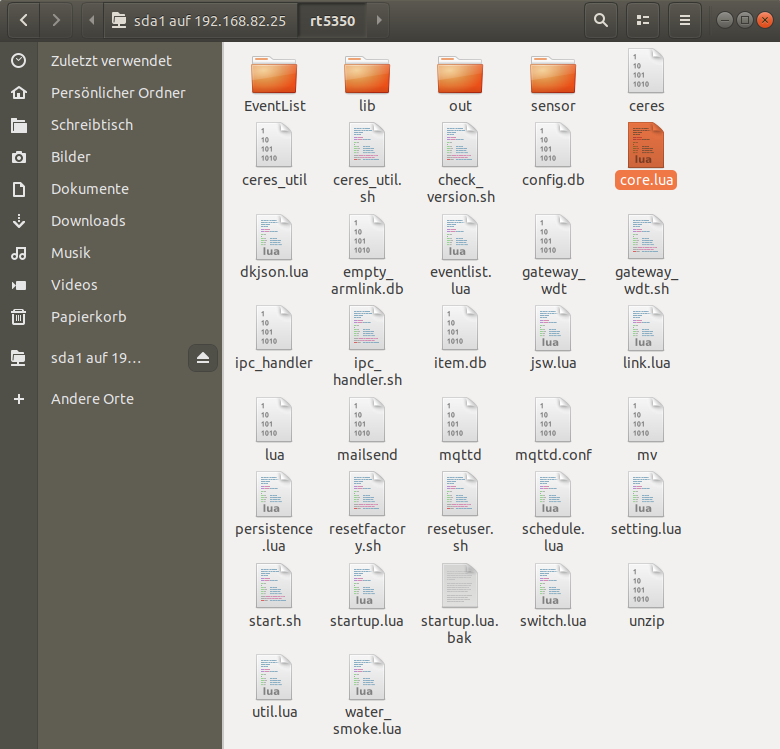
Thus, König provides network sharing in the internal network via the hopelessly antiquated and unsecure SMB Share 1.0 network protocol. The version deployed, already several years old, is notorious in its vulnerability for critical security gaps. Recently in 2017, devices with the outdated network architecture proved vulnerable to cyberattacks of the WannaCry ransomware. But it was not only the use of outdated communication that irked the testers. They also had to discover that König delivers the product as standard with the login details "admin/admin" alongside what is already an unsecure communication channel, without even allowing the user to make the urgent change of the user name and password. For attackers, "security settings" like those on an alarm system are practically an invitation. In the network sharing provided, there are also core components of the system which can be edited in plain text. That is why it would be possible using very easy means to deactivate the siren or the signaling in case an illegal entry was detected.
But it gets worse: The device comes shipped with factory defaults offering attackers wide-open Telnet, FTP and web server ports. Unwitting customers would not be aware of this sloppiness at the expense of security, however. And these gaps, which are apparently unknown to the manufacturer, can only be closed by means of a manually performed firmware update, which was not available, however, at the time when the test was performed. It should also be mentioned that attackers could also exploit this due to the lack of security along the transmission channel or reset the system at any time due to the vulnerabilities in internal communication.
Similarly poor protection is found in model "KX-HN6011" from Panasonic. In Wi-Fi communication, the manufacturer does indeed rely on encrypted connections, yet these were easy to circumvent for the testers using standard tools that anyone can obtain on the Internet. Using basic man-in-the-middle attacks, it was possible in the AV-TEST laboratory to not only monitor but also manipulate the system. In doing so, the testers circumvented the login procedure without any knowledge of the user name and password, and were able to shut down the alarm function.
"Home Center Lite" uses unencrypted http connections for internal communication, and the same applies to the app control. The manufacturer Fibaro is urgently called upon to make improvements here, so that attackers will no longer be able to read out the authentication on the website of the manufacturer and thus abuse intercepted login data for attacks.
App security: security app with secret data forwarding
In terms of security for the apps themselves deployed to control security starter kits, most of the manufacturers delivered solid workmanship. Most of the apps stored the sensitive user data in encrypted form or otherwise in secure areas of the test smartphones running under Android and iOS. Blaupunkt, Bosch, Devolo, eQ-3 and Telekom also secured the communication of their apps with enhanced certificate validation against man-in-the-middle attacks (certificate pinning). With respect to the Android app from D-Link, the testers were able to gain access to all elements of the firmware. This information, however, could not be used for direct attacks.
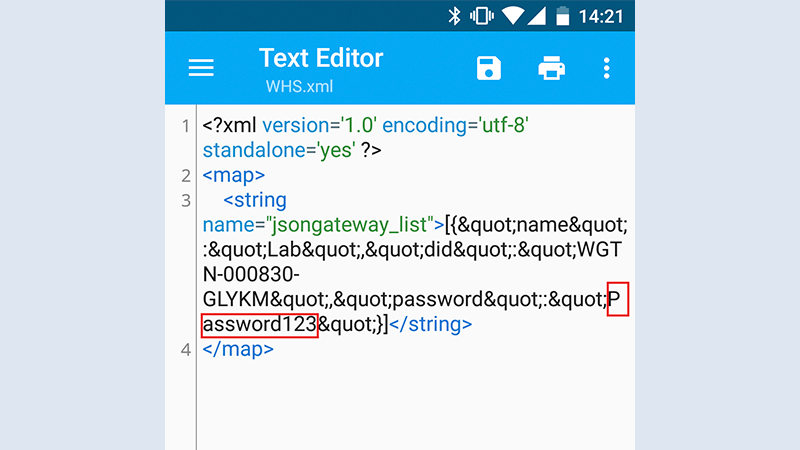
Even the brightest light casts shadows. And the shadow once again falls on the manufacturers König and Xiaomi. The Android app for König's smart home set, along with the other software of this product series, commits critical errors in several places in the handling of sensitive data. But it gets worse: Sensitive information such as the password to the smart home system is stored in plain text in the app data. While access to this memory area is only possible on rooted smartphones, the unsafe storage method of data in the app nonetheless underscores the poor impression created by the overall package from König in terms of security.
The Xiaomi app also exhibited clear weaknesses, spilling out critical information during the analysis of the Android log files (Logcat). Among this information, the testers also found "secure tokens", which actually are intended to guarantee the secure transfer of sensitive data. If these fall into the hands of potential attackers, however, this security mechanism can be turned around. But the disclosure of sensitive data occurs through the app of the Chinese provider not only in case of an attack. In the IoT lab at AV-TEST, the Xiaomi app also revealed countless data transfer modules to other data-hungry companies, including Facebook, Alibaba, Adobe and many more. For security and data protection reasons, experts generally take a critical view towards modules of this kind, as the user has no idea which data is used, where the data is flowing and what happens to it. In the view of AV-TEST, at least, such modules don't belong at all in the app of an alarm system.

AV-TEST evaluates IoT devices
in comprehensive security tests. You can find the latest tests in our blog (www.iot-tests.org).
Half the manufacturers do not take data protection seriously
In the test category of data protection, 7 out of 13 providers fulfill the expectations of the testers with a "good", one with a "satisfactory", rating. However, violations of the existing GDPR in effect throughout Europe since the end of May of this year are not a minor offense and can be sanctioned accordingly. For this reason alone, Blaupunkt, Gigaset, iSmartAlarm, König and Panasonic ought to take their information duties and their customers' right to information far more seriously. All these manufacturers completed the data protection evaluation with an "unsatisfactory" rating, which is why they ought to quickly adapt their privacy policies on their website, in the apps, in the installation procedure and in the instruction manuals of the devices to the current legal status.
Mishaps in tamper protection
The security starter kits scored more poorly in the test category of "tamper protection". Only a single product earned the test rating of "good" in this category. Five were "satisfactory", seven, by contrast, showed deficiencies in tamper protection. It should not be forgotten here, however, that the test candidates do not involve professional alarm systems but rather smart home systems with security functionality.
Amazingly, of all participants, the "Smart Security Kit" from König made an impressive showing with a well-devised concept. It involved the device that was otherwise conspicuous in all other test categories mostly due to major security deficiencies. The König device informed its owner of all attacks mostly successfully carried out in the IoT lab of AV-TEST due to what was otherwise a weak security concept. Even if power to the device was cut off, the tamper protection remained standing, a feature that other manufacturers would do well to emulate. The "Smart Security Kit" then drew the necessary power from the buffer battery and reliably sent out a warning signal to the test smartphone.
In the security kits from Fibaro, Gigaset, iSmartAlarm, Medion, Panasonic, Telekom and Xiaomi, by contrast, there is room for improvement in terms of protection from sabotage. Fibaro, for instance, offers no prevention or signaling functions whatsoever against attempted attacks, although the "Home Center Lite" has relevant sensors built-in. Gigaset affords a latency time of over 15 minutes for important warning signals, e.g. when batteries are removed. If it even notices manipulation on the door and window contacts at all. Because these can be defeated with a simple trick. The contact works with an accelerator sensor that does not trigger during slow movement. This is no longer acceptable for preventing attacks. While the Medion device does indeed detect the failure of components after several minutes, also keeping track of it in a log file, it does not notify the user. The devices from iSmartAlarm, Panasonic, Telekom and Xiaomi do not provide any notification if attackers shut down, disassemble, open or destroy components. Thus, thieves could cut the power and steal the base station itself out of the house.
In systems exhibiting at least satisfactory results in this test category, manufacturers ought to remedy easy errors and fortify their products with additional useful functionality. If they do so, they will then be able to do justice to the customer promise of reliable home security. One example of this is the "Q 3000" from Blaupunkt: In the test, the system proved well-armed against standard acts of sabotage, sounding an alarm when the motion sensor was removed, for example. The device keeps working even during loss of power, as it has a buffer battery. Yet the buffer battery has a cut off switch with which the entire system can be knocked out. As a result, what is actually a good tamper protection concept can be taken to absurdity with one push of a button. The door contacts of some manufacturers do in turn signal if the housing of the modules is opened, however, the alarm does not sound during disassembly. As these contacts are often only glued in place in order for the door and window frames not to be damaged, the tamper protection urgently needs to be expanded to disassembly.
Conclusion
The test indicates that smart home base units with a corresponding well-devised security concept are also suitable as an alarm system, whereby once again it needs to be emphasized that they are not full-fledged alarm systems, only smart home bases equipped with upgrade functionality. Accordingly, the test field reveals significant differences among the solutions available. In the AV-TEST Institute's quick test, five out of the 13 security starter kits turned out to be secure, thus earning three out of three possible stars: "Smart Home" from Bosch, "Home Control" from Devolo, "Homematic IP" from eQ-3, "SmartHome" from Telekom as well as "P85754" from Medion.
Due to slight deficiencies, five additional security starter kits receive only two out of three possible stars, yet it ought to be possible for "Q 3000" from Blaupunkt, the "Home Center Lite" from Fibaro, "smart home" from Gigaset, and "ISA1G" from iSmartAlarm to correct these deficiencies without major expense. The same applies to the "DCH-107KT" from D-Link, for over a year, however, the manufacturer has already known about security gaps, without which a better rating would have been possible.
With some gross security deficiencies and only one star, the "KX-HN6011" from Panasonic as well as the "Mijia 5 in 1" from Xiaomi cannot be recommended for monitoring one's own four walls. Owing to extreme security deficiencies, the "Smart Security Kit" from König fails this security test with zero out of three possible stars in nearly every category, and in the view of the testers, the product name is an actual misnomer.