Latest News
August 26, 2020 | Research
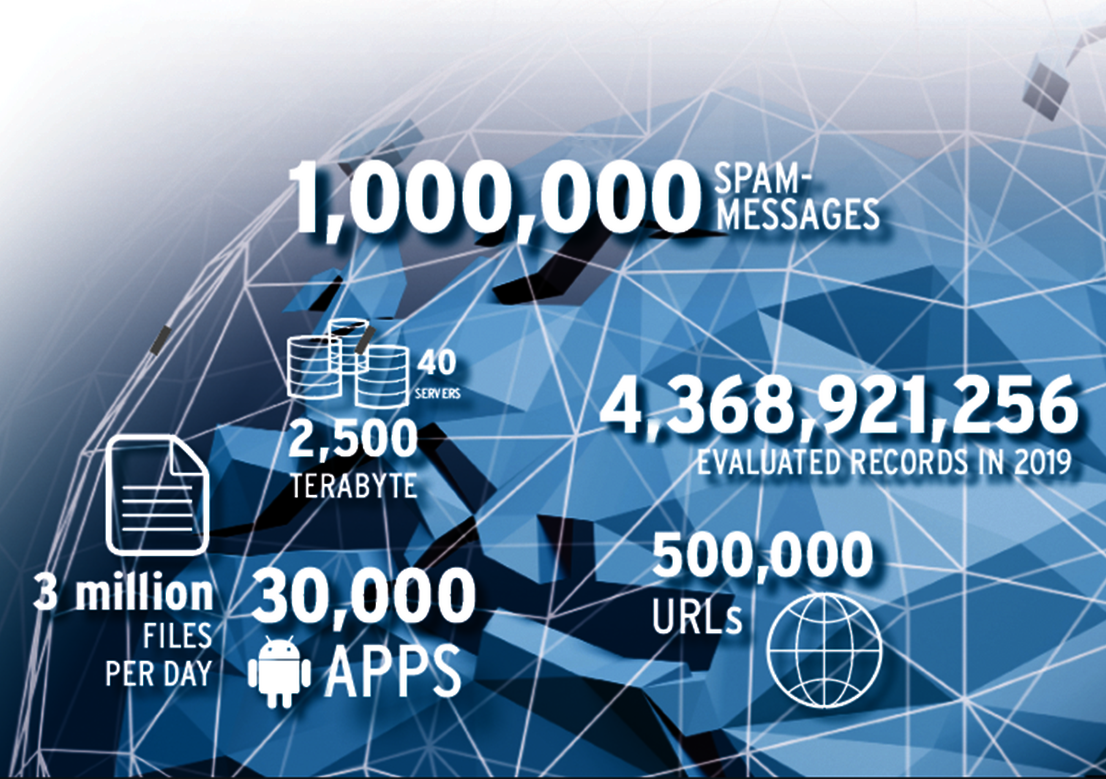
Facts & Analyses on the Threat Scenario: The AV-TEST Security Report 2019/2020
The new trend in the malware industry observed in 2019 clearly continued in 2020. The development of malware programs is divided up into two areas: While on the one hand the automated production of mass malware for broadly-based online attacks continues to grow sharply, on the other hand cybercriminals are increasingly developing sophisticated malware for specialized attacks on companies and critical infrastructure. The answers to all questions on current developments in the threat scenario can be found in the AV-TEST Security Report 2019/2020.
Massive attacks on Windows with mass malware
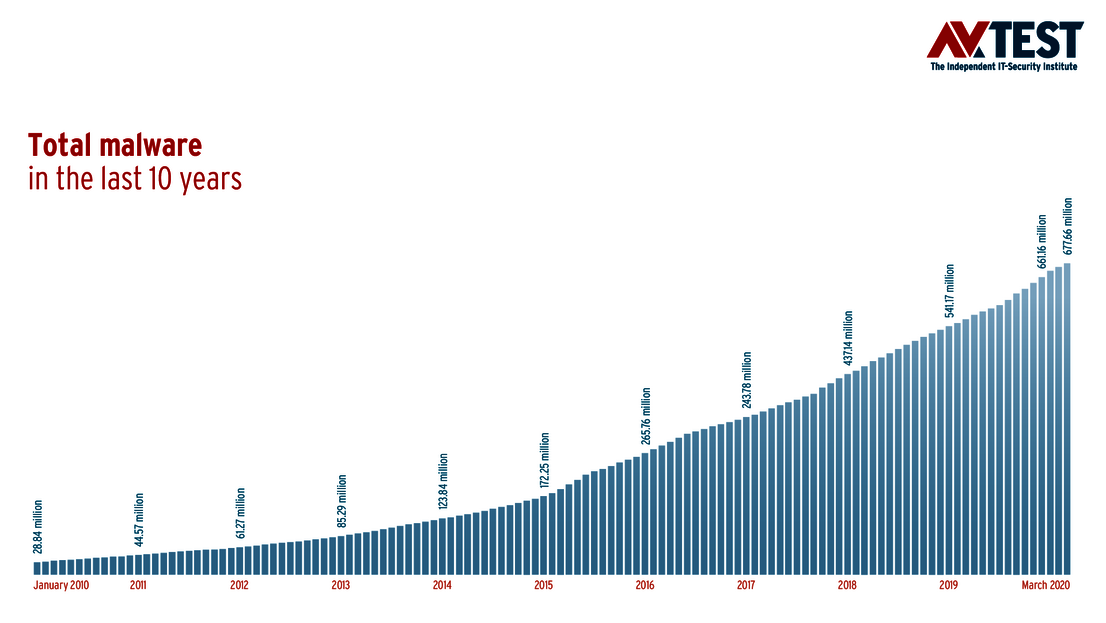
In 2019, the use of mass malware, i.e. malware programs created automatically, reaped considerable profits for cybercriminals. Accordingly, the rate of this malware, distributed mainly per e-mail and over the Internet, grew sharply. With more than 114 million (114,312,703) newly-developed malware applications, the malware industry broke the sound barrier in 2019 and was more active than ever before. The analysis of the latest detection statistics for the first quarter of 2020 indicates that this year will also see significant growth rates: Already in the first quarter of the current year, the AV-TEST systems have registered over 43 million newly-programmed samples. Accordingly, by the end of 2020, there will be an anticipated explosion of newly-developed malware applications, which could level off for the entire year at more than 160 million samples. As a result, the threat scenario posed by mass malware could reach a new dangerous peak in 2020. Currently, the development rate of new malware is at 4.3 samples per second!
A precipitating factor for this dramatic development can be viewed as a positive, because among other reasons, the mass development of new malware samples can be explained by the high level of protection currently provided by security products. This is true especially for protection solutions for Windows systems. Because the majority of all malware still targets the operating system most widely used by far around the world. In 2019, over 78 percent of malware codes newly-developed by cybercriminals targeted Windows systems. In the first quarter of 2020, this value continued to increase to over 83 percent
Android and MacOS systems running around without protection software
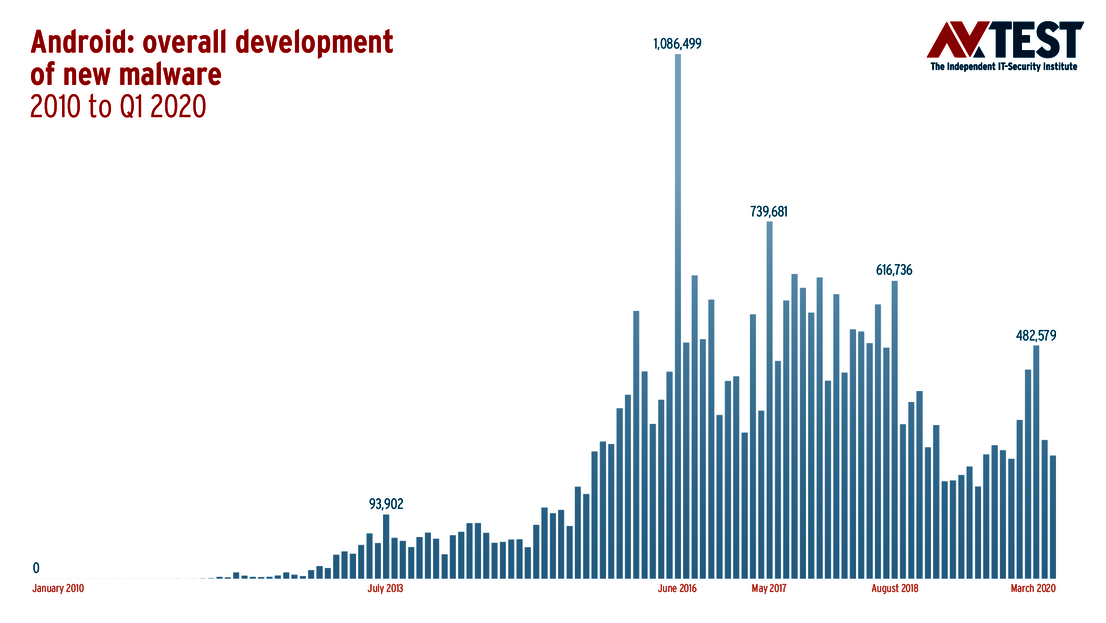
The AV-TEST systems registered a slight decline in the rate of newly-developed malware on the most widely-distributed mobile operating system from Google. The operating system reached its peak in malware growth in the year 2017 with 6,201,358 newly-programmed samples. Since then, the number of new Android malware samples has been declining, in 2019 reaching the lowest level in three years with 3,170,140. Although this trend is actually welcome, falling malware statistics do not automatically mean a diminished threat scenario for users of Android devices. Moreover, the trend of the first quarter of this year already indicates a resurgence of malware trends for Android.
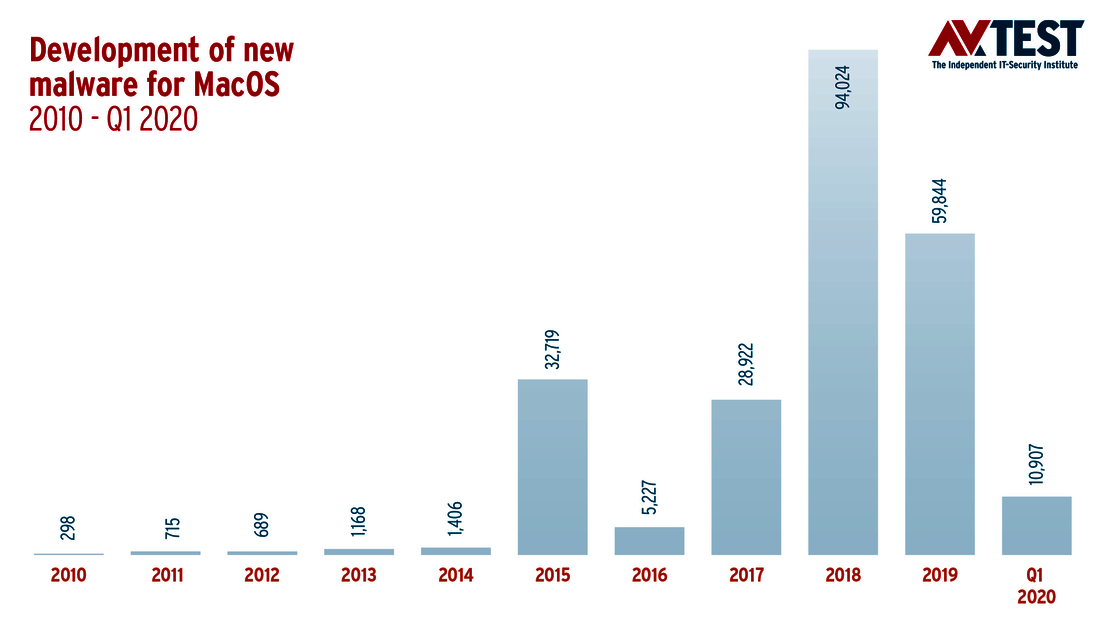
For MacOS as well, the detection systems of AV-TEST in 2019 indicated declining, yet persistently high malware statistics. Whereas the previous year, with over 90,000 newly-programmed malware applications represented a glaring milestone in the trending history of MacOS malware, new developments reached approximately half that number in the subsequent year, remaining below 60,000. If the statistics of the first quarter in 2020 continue, an additional decline can be anticipated. At least statistically, the number of new malware samples for Apple computers is expected to level off at roughly 40,000 new samples towards the end of the year.
This development is to be taken with a grain of salt, however, as it does not automatically equate to a diminished threat scenario. Both operating systems, not only Google's mobile system Android but also Apple's MacOS, compare negatively with Windows in the sense that the deployed user devices are largely operated without effective protection software. Notably, as evidenced by regular tests by the AV-Test Institute, there are a large number of even free apps and antivirus solutions for both systems, with which a decent level of security could be reached.
APT: trend towards targeted attacks
The massive increase in targeted attacks by means of Advanced Persistent Threats (APTs) can hardly be quantified for various reasons: First, these types of tactical attacks are strategically prepared long in advance and staged against companies and organizations that manage extremely valuable information. Moreover, such attacks, normally leveled by state-organized attackers against ministries, research, and production facilities as well as financial firms and other institutions of a country, are seldom made public. It is a fact that companies in particular are increasingly required to introduce special defensive measures against targeted attacks on their digital infrastructure. The AV-TEST Institute responds to the increase in already known APT attacks with a testing and certification program of security solutions aligned with the MITRE standard. You can find information on the tests for evaluating effectiveness in fending off APT attacks on our website.
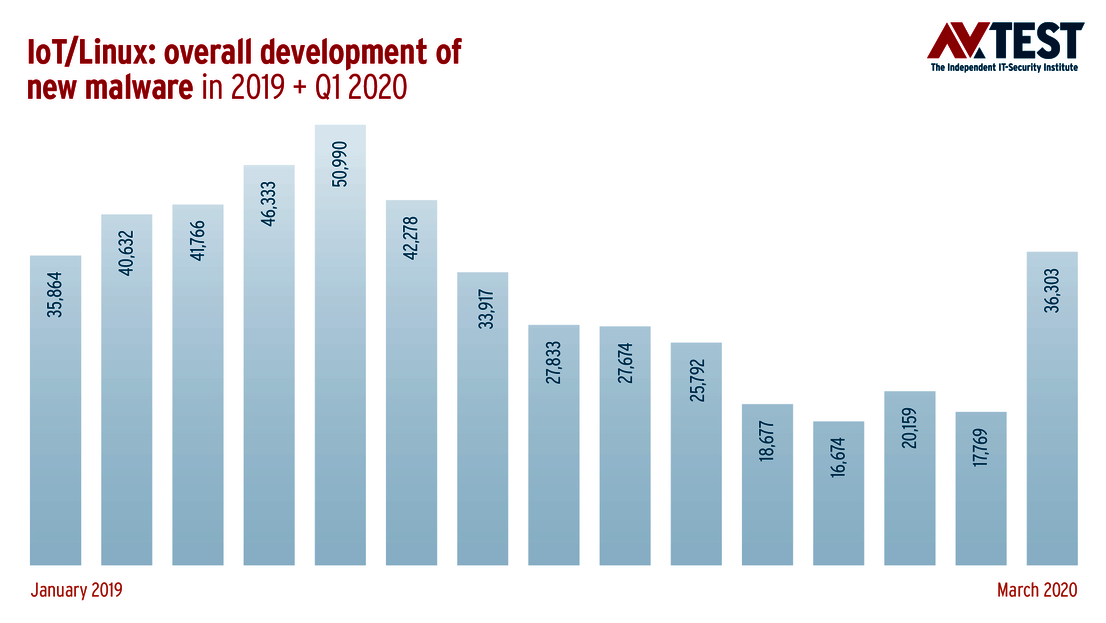
IoT malware threats: doubling of the malware rate
In the report last year, the warning from the IoT lab was already unequivocal: “In the race for lucrative market shares, the industry continues to develop multitudes of IoT products without a sufficient security concept and frequently disregarding even absolute minimum standards of IT security.” Hardly anything has changed, and therefore, especially at the beginning of last year, the AV-TEST systems saw exponential growth in malware rates for IoT-typical Linux and Unix versions. This trend was already forming at the beginning of the year 2018 in the detection data of the AV-TEST systems; its growth curve in 2019, however, surpassed even the most pessimistic forecasts. Whereas the analysis of new Linux malware samples for 2018 already indicated a total figure of 188,902 newly-programmed malware samples, the AV-TEST systems in 2019 registered 408,430 new samples, more than double.
The IoT detection figures of the current year continue to show alarming growth: Thus, the rate of Trojans used to infect IoT infrastructure increased from 40 to over 65 percent, And the increase in the rate of newly-developed crypto miners had more than quadrupled.
AV-ATLAS supports suppliers with real-time data on IoT attacks
With the launch of the IoT section in the AV-ATLAS Threat Intelligence Platform (av-atlas.org), the AV-Test Institute now also offers real-time threat analyses of virtually all relevant IoT platforms, to guide users and to support manufacturers. The website, available free of charge, offers a query capability both for information on past and current attacks, including logins used, originating servers, type of attacks and the commands used in the process, along with the malware deployed and its precise analysis.