Latest News
August 27, 2018 | Repair tests for Windows
Test: Windows Repair after a Trojan Attack
What happens after an attack by malware, e.g. a virus or a Trojan? Can Windows be cleaned up and recovered? The AV-TEST team got to the bottom of these questions: it tested 7 security packages and 5 special tools in terms of how they perform when disaster strikes.
Do you simply delete a well-functioning Windows system, reformat and reinstall everything? It's a nightmare scenario for many Windows users, as the time and effort is immense, and in the end, important applications are always missing. But what else can you do if a program containing malware code has now infiltrated and taken over control of your system? If you follow the advice of leading forums, a new installation of the entire system or PC is the only remedy. The clean-up and repair test from AV-TEST proves that there are far less labor-intensive alternatives.
Test: 12 programs when disaster strikes
What are the consequences of an attack by an application infected with malware code? Usually, it first commandeers the key elements of the Windows system. Some malware then lies inconspicuously in the background, as it is part of a botnet. Another code, for example, puts a constant load on the system CPU, as it mines for digital bitcoins. But the fact is, it doesn't matter what the malware code does – you simply want to get rid of it as quickly as possible. In doing so, the tools of Internet security suites or special tools serve as helpers in deleting malware samples and repairing their damage. But can they really deliver on what they promise? The lab at AV-TEST extensively tested 7 suites and 5 special tools under Windows 10 in the first six months of 2018 in terms of whether they remove the malware sample along with its benign components and repair the damage.
The test included these 7 Internet security suites:
- Avast Free Antivirus
- Avira Antivirus Pro
- Bitdefender Internet Security
- Kaspersky Internet Security
- Malwarebytes Premium
- Symantec Norton Security
- Windows Defender Antivirus
These 5 special tools were tested (all are freely available on the Web):
- Bitdefender Rescue Disk
- Heise Desinfec't 2018
- Kaspersky Virus Removal Tool
- Microsoft Safety Scanner
- Vipre Virus Removal Tool
Here is how the test works
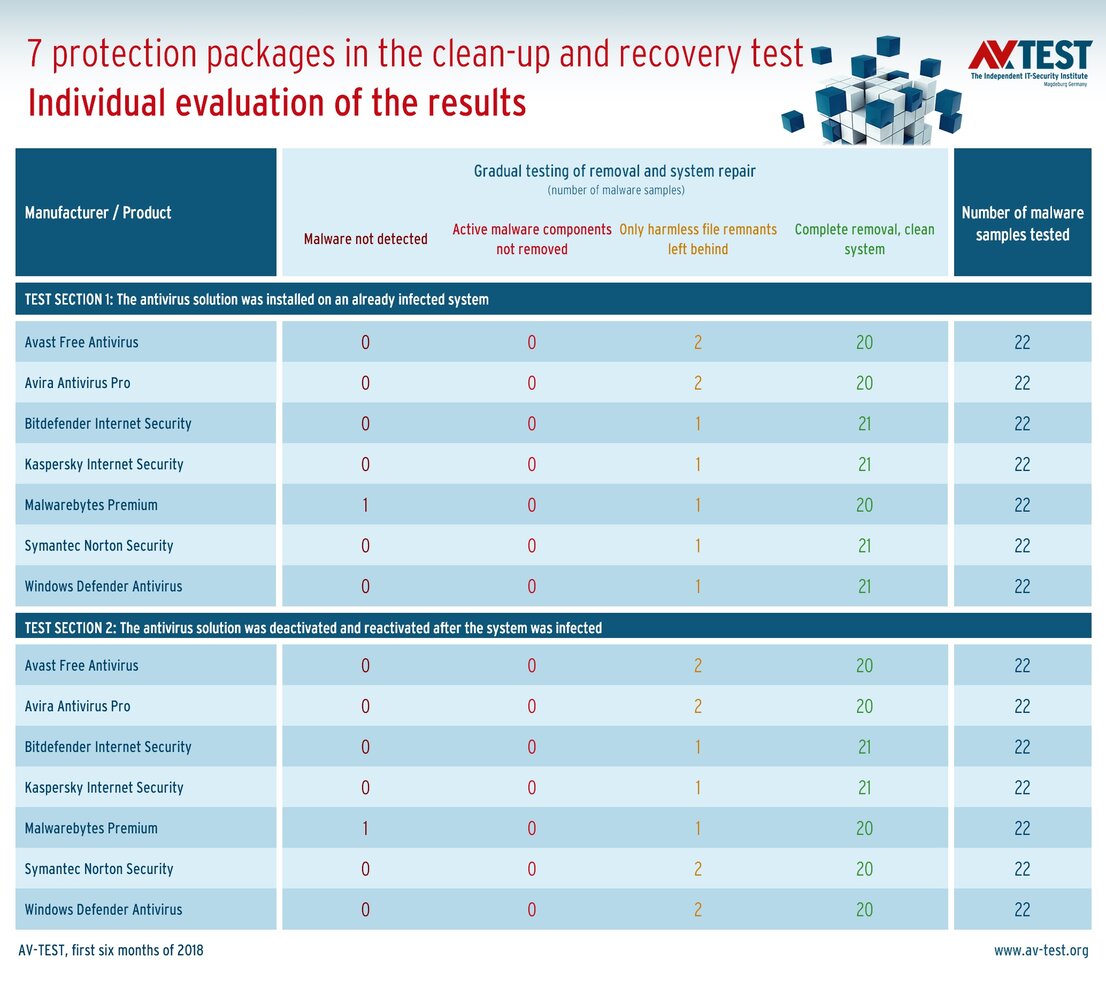
The overall test is always very time-intensive, as it requires quite a lot of manual labor, and the test routine is somewhat different for the suites and tools. In the initial test, the security suites are installed on an already infected system. This simulates the case where a user is working with an unprotected system and then tries to rescue whatever can be salvaged. In the second test phase, the suites are already installed, but are briefly deactivated and then infected with malware code. This simulates the situation where a security package does not recognize the attacker at first, only to discover and remove it later.
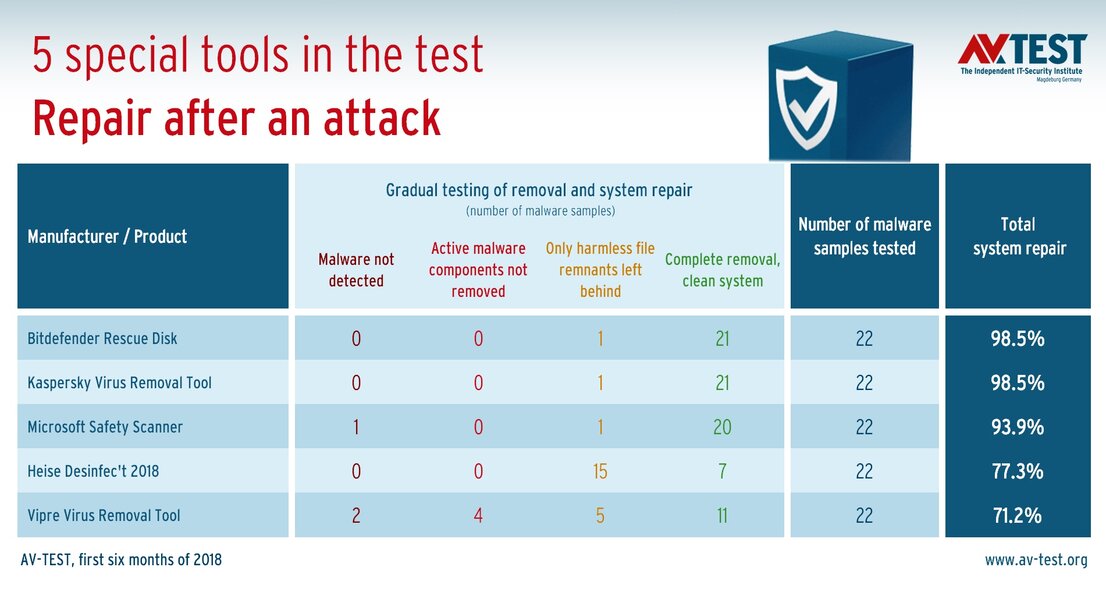
In the case of the special tools, a Windows system is initially infected with a malware sample and the tool is deployed. A boot DVD or stick is used in the process. The special tools then boot up in their own small operating system – usually Linux – cleaning up and repairing the Windows system from the outside, so to speak.
The final analysis
Whenever a test phase is completed, a Windows system is scanned bit for bit and compared to a reference system. In this way, the testers can determine whether the system has been restored to its original condition or whether perhaps the clean-up and repair were not successful. In doing so, the test team compiles the following results:
- The malware sample was detected or not
- The active, dangerous malware components have been removed or not
- The number of file remnants left behind, but still harmless
- The number of systems cleaned up completely
The result of the overall tests is really good. With one exception, the Internet security suites do an excellent job. But also among the special tools, there are some that can truly help in an emergency.
Bitdefender Internet Security
The security package demonstrated almost flawless work in all infected Windows systems
Kaspersky Internet Security
The suite helped perfectly in all test cases and left behind a harmless file remnant only once
Good software and tools as helpers
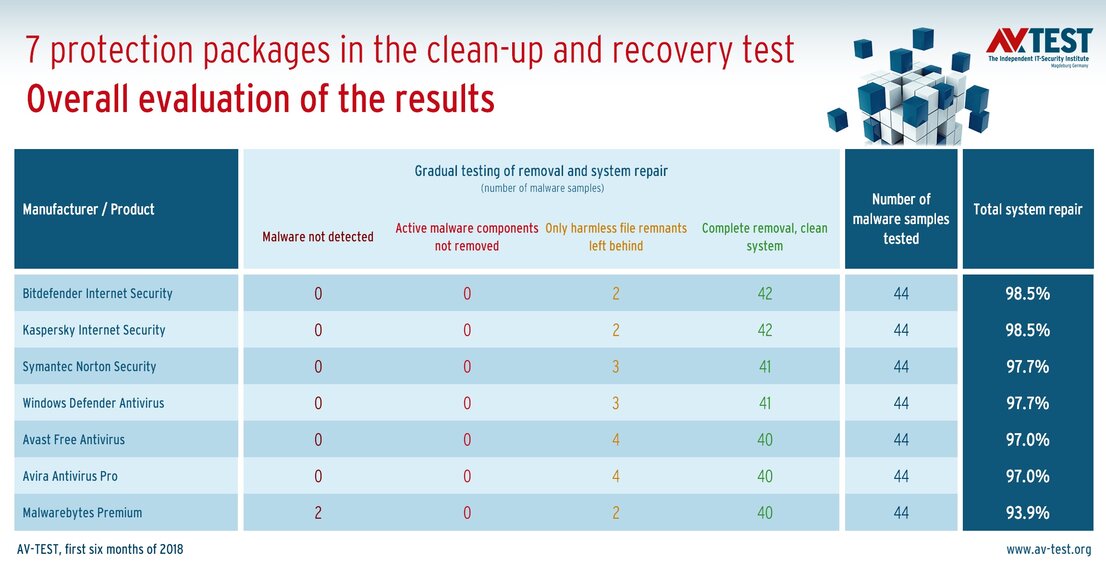
In terms of the protection security suites examined, there is a full playing field of reliable helpers. Among them, the products from Bitdefender and Kaspersky Lab came out on top. They cleaned up 42 systems flawlessly, and only in 2 cases did they overlooked a few harmless file remnants. Windows Defender and Symantec software followed close behind with 41 clean systems and 3 cases with harmless file remnants. The programs from Avast and Avira also performed well, perfectly cleaning up 40 systems and in 4 instances leaving simple file remnants behind.
Only the software from Malwarebytes was unable to clean up and repair Windows twice, as it was unable to detect the malware. In addition, there were 2 systems with harmless file remnants and 40 completely cleaned-up Windows platforms.
With respect to the special tools examined, the result for some did not turn out very well. In this area as well, Bitdefender and Kaspersky Lab deliver the tools with the best test results. For 22 examined attacks, both tools each perfectly cleaned up and repaired 21 systems. In one case each, a harmless data remnant was overlooked. The tool from Heise was indeed able to detect the malware code each time and delete the dangerous components, but it overlooked the harmless file remnants in 15 cases – in the end, it resulted in a perfect Windows system in only 7 cases.
The Safety Scanner from Microsoft was unable to detect one malware sample, and the Vipre tool missed a total of two. It is worth mentioning that the Microsoft tool did flawlessly clean the platform 20 times and only overlooked harmless file remnants once. The last-place finisher, Vipre, was unable to delete the active and therefore dangerous file components in 4 additional instances. The rest: 5 systems with file remnants and 11 clean systems.
Thus, overall the software packages or tools from Bitdefender and Kaspersky Lab have an edge in the business of cleaning up and repairing Windows systems.
Finally, here's a tip: If a PC is hit by ransomware or a cryptolocker, generally all data are encrypted immediately. A security software package or a tool can indeed delete the attacker after the fact, but normally cannot decrypt the data. That is why users should always make sure to create a backup on an external drive and disconnect it from the PC afterwards.