Latest News
April 29, 2014 | Internet of Things
Test: Smart Home Kits Leave the Door Wide Open – for Everyone
Smoke detectors in the form of Internet alarms, burglary warnings sent by text message and lighting and heating controlled via smartphone apps are all now possible thanks to smart home components. Nevertheless, as the major test recently carried out by AV-TEST shows, all of the ingenious features praised by providers of such components come at a cost, with security mostly falling by the wayside.
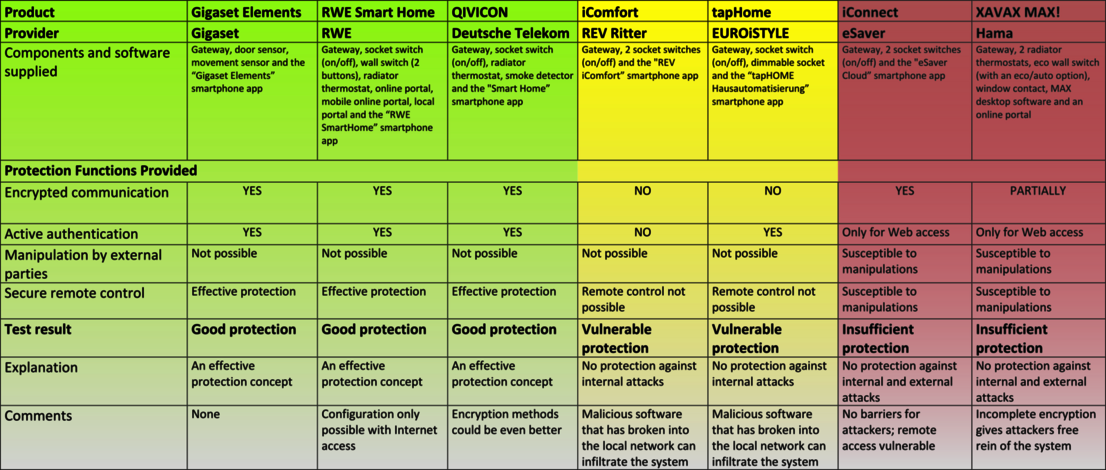
The overall result of the “The AV-TEST Security Test on 7 Smart Home Starter Kits”
In the major security test carried out by AV-TEST, Gigaset Elements, RWE Smart Home and QIVICON were the only smart home solutions to deliver a convincing performance. These sets use encrypted communication and offer effective protection against unauthorised access.
Unfortunately, the first major test carried out on starter kits for smart home solutions gave the experts at AV-TEST no reason to give the all clear. Only 3 of the 7 kits tested are well secured against attacks, while the rest are poorly protected against internal and, in some cases, external attacks. As a result, when unprotected smart home devices connect to the Internet, intruders can sneak in through the back door and attack the home network. The minimally protected smart home devices will therefore soon be ambushed by Trojans that, in the case of a successful attack, will not hide in the PC, but, for example, in the smoke detector’s memory.

RWE Smart Home from RWE
This basic set aims to save energy, but certainly didn’t scrimp on security in the test, instead exhibiting a well-functioning protection concept. (Picture © RWE AG)
Is the smart home concept completely insecure?
The basic idea behind smart home technology, namely aiming to enable all household components to be remotely monitored and controlled in the future, is, of course, very good. All components that can access the home network and therefore may also be able to access the Internet are potentially vulnerable. This does not, however, mean that they are also potentially insecure.
The latest test carried out by AV-TEST proves that some providers haven’t just taken a slapdash approach and thrown their devices onto the market, but instead have worked to develop a security concept.
The test focused on the following smart home kits, which are primarily sold by large companies but also offered exclusively. Although the kits do not all complete the same household tasks, they are still comparable:
• iConnect from eSaver
• tapHome from EUROiSTYLE
• Gigaset Elements from Gigaset
• iComfort from REV Ritter
• RWE Smart Home from RWE
• QIVICON from Deutsche Telekom
• XAVAX MAX! from Hama
3 Secure Products vs. 4 x Insecure Products
The results of the test will hopefully persuade some manufacturers to improve their products.
The Gigaset Elements, RWE Smart Home and QIVICON sets proved to be well secured against attacks and unauthorised access in the test.
The iComfort and tapHome sets, on the other hand, are not protected against attacks within their own network, while the iConnect and XAVAX MAX! kits are rather powerless against attacks within their own network and external attacks.
The following report provides a brief explanation of the individual weaknesses identified in the test. The detailed test results, the test scenarios used and the individual values recorded, right down to bit measurements, can all be viewed in the over 40-page-long AV-TEST study report, which can be found here (only available in German):
Download Test (PDF, only available in german)
The Tasks Controlled by the Smart Sets
The kits are able to complete a variety of different tasks in a smart home and can be categorised as follows:
- Control systems for electricity, heating and security:
RWE Smart Home and QIVICON - Monitoring systems for windows, doors and rooms:
Gigaset Elements - Control systems for switched sockets:
iComfort, tapHome and iConnect - Switch systems for light, heating and electricity:
XAVAX MAX!
The different tasks completed by the kits soon reveal the kind of horror scenario that may occur if an external attacker were to take over the system. Such an attacker may, for example, take control of the heating function and turn it down so low that the water pipes freeze and burst in the depths of winter.
Given that attackers are, however, generally more interested in obtaining money or valuable data, a number of other scenarios are more likely, for example an attacker using a kit's up-to-date plans for switching devices on and off in order to ascertain when the residents of a house will be at home and when they will be out. If the security monitoring function for windows and doors can also be switched off, breaking into the house is plain sailing for burglars.
Another likely scenario would be for all connected devices to use the home network to attack other devices and take them hostage by blocking access to them and declaring that users can allegedly only regain access by paying a certain amount. This is the method used by attackers such as police Trojans, which block PCs and all of the data stored on them.
Where can the weaknesses be found?
When examining the security of the smart home kits, the testers attempted to identify their weaknesses. They therefore analysed the protection concept used by each starter kit, focusing on the encryption used in communication activities, active authentication, manipulation by external parties and the kits' secure remote control. These are particularly important factor as all of the sets can ultimately be operated via smartphone app or via browser using WLAN or the Internet.
Encrypted Communication
The communication activities used when the kits are controlled in the local network and when a firmware update is installed should always be encrypted. This should also be the case when the components are controlled over the Internet or the firmware update is carried out directly online.
The Gigaset Elements, RWE Smart Home and QIVICON sets all complete their communication activities without any security issues. iConnects uses encrypted communication, but this can easily be bypassed. The concepts from iComfort, tapHome and XAVAX MAX!, on the other hand, are a complete let down in terms of encryption, failing to use any secure communication.
Active Authentication
Although the products can actually be expected to require authentication when a user accesses devices, this is not a standard feature in all of the kits tested. The iComfort kit requires no authentication. Although the iConnect and XAVAX MAX! sets require authentication when accessed via the web, they fail to use any barriers whatsoever on an internal level and can therefore be labelled as negligent.
The tapHome does indeed internally require a username and password, but this is virtually useless given that its communication is unencrypted, meaning that anyone can capture these login details.
Only the Gigaset Elements, RWE Smart Home and QIVICON sets again displayed a flawless performance in this area, as was also the case in terms of their encrypted communication.
Manipulation by External Parties
The fact that some of the devices tested do not use encrypted communication means that they may be at risk of being injected with a malicious code or suffering from an even more perfidious attack in the form of infected firmware. Both of these scenarios would enable hackers to quickly access the devices and in doing so, achieve a firmly installed back door into the home network.
Secure Remote Control
Remote control is a particularly important aspect of the smart home concept. After all, the users of such systems ultimately want to be able to control their components via smartphone app or browser. The iConnect and XAVAX MAX! candidates yet again failed to impress when it came to their remote control function, with both sets revealing glaring weaknesses. The iComfort and tapHome kits are not at risk in this area because they do not offer any remote control function at all.
The three sets from Gigaset Elements, RWE Smart Home and QIVICON also displayed a secure performance in this area and therefore proved their worth with an error-free protection concept throughout the entire test.
Summary: A High Level of Security Is the Trump Card
As already mentioned at the beginning of the test report, an insecure smart home kit may provide intruders with a back door leading into your home network. It is therefore essential that these products offer a high level of security. Unfortunately, however, such kits do not have a security standard as can be found in other network devices such as WLAN devices or routers.
The only summary that can be drawn from the test results is that at present, only the Gigaset Elements from Gigaset, RWE Smart Home from RWE and QIVICON from Deutsche Telekom sets can be recommended.
The manufacturers or distributors of the iConnect, tapHome, iComfort and XAVAX MAX! starter kits need to revise their products in terms of security in order to bring them up to scratch.
A Look into the Future
None of the sets tested currently offer a function that enables the transmission of sound and images. When carrying out the test, the testers did, however, already discover a number of preparations for interfaces for webcams with microphones. Access to suitably equipped kitchen appliances such as fridges and coffee machines is also likely to be introduced in the very near future. After all, such functions are a piece of cake for the technology used in the sets. The thought that an unauthorised party could access all of these devices, however, sends shivers down the spines of some users.
On top of this, market researchers currently expect smart home products to achieve global sales of over 15 billion dollars by the year 2015. This may sound like a lot, but it was only recently that Google already purchased the company Nest Labs for 3.2 billion dollars. Given that Nest Labs produces controllable smart home components in the form of thermostats and fire alarms, the search engine giant is sure to raise the pressure in this area.