Latest News
March 25, 2019 | More tests
Secure Passwords – It's a Snap!
Anyone can use secure passwords – it's easy as can be. And those who can only remember one difficult password ought to use it to access a password manager that keeps track of other passwords!
Statistics show how most users handle passwords: over 50 percent claim that they can remember passwords in their heads. Behind the statistic, however, is the bitter truth that most passwords are quite simple and used identically in many services. Only one in ten people uses a password manager that keeps everything safeguarded. But what is the right way to do it, after all?
Prioritizing passwords according to use
One thing is clear: you should always use digitally-generated passwords for secure access. In doing so, however, you need to prioritize where your password is used.
The generic 'whatever' password: it is usually used for simple forums or website logins not containing sensitive information, such as credit card details. A browser such as Chrome, Firefox etc. is recommended for quick access and for use alongside a password manager. For example, the new Chrome browser detects when an interface prompts the user to specify a password. Per right mouse click, Chrome proposes a password to the user. If you choose this option, Google Chrome then saves all access data, including the password. If users are logged in to Chrome with a Google account, these saved access details are available on all Chrome and Google account devices. The disadvantage: if a stranger has access to one device, they can read all passwords in the Chrome settings or even export them. Unfortunately, there is no master password. That's why: Chrome provides easy assistance, but it is not a true password manager or password safe!
The secure password via password manager
It is impossible to remember all the different good and secure passwords for multiple shops, services or social media accounts. It only works with a password manager. For a manager you really only need one very good password. Here is a good method for doing so: think of a sentence and memorize the initial letters of the words, such as "I go sailing at 10.08 and love surfing!" The password would be: Igsa10.08als!. This password has a length of 71 bits, and even a good PC would need more than 100 million years to calculate the 51 septillion possible combinations. You should use such a very good password as your master password for a password manager! So the longer the sentence, the more secure the password.
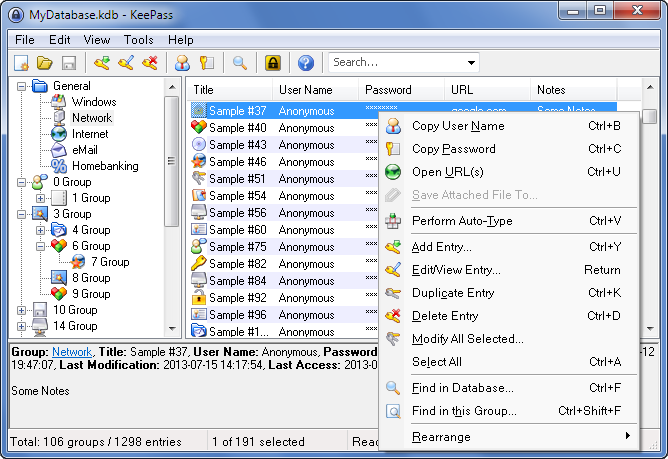
There are many good tools available as password managers. The open source software, KeePass, for example, is very popular as a freeware desktop program. In addition to the Windows version, there are also versions for Mac, iOS, Android and many other systems. The disadvantage of KeePass is that it requires the user to individually save the highly-encrypted password file in cloud storage to enable all systems to access it. This is where some expert knowledge and creative experimenting are called for.
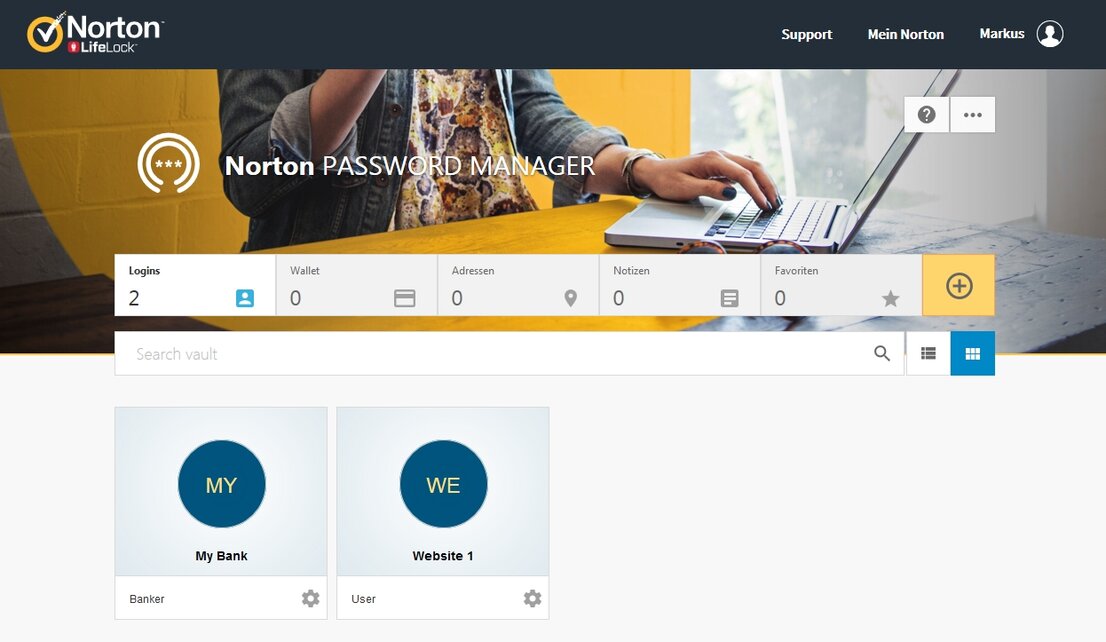
Norton Password Manager
The tool can currently be used free of charge if you create a Norton account
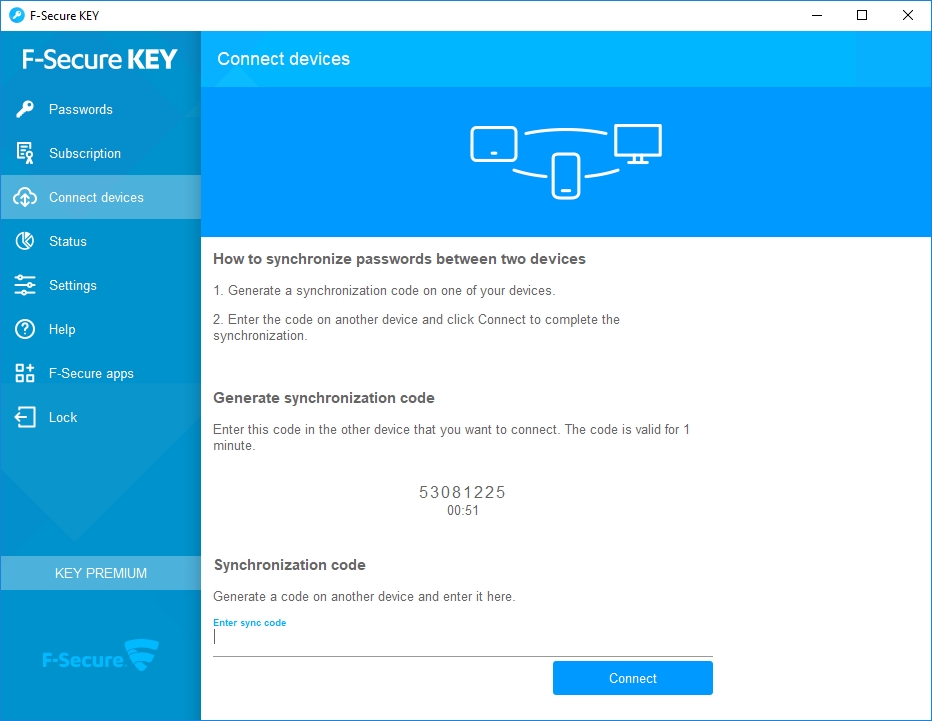
F-Secure Key
The password manager stores the details on the devices and only replaces the changes via the F-Secure cloud
Commercial and cloud-based password managers
Those seeking to use a password manager automatically and from one central place can sign up for the free basic service of LastPass. With the help of software and apps, the access details, including passwords, can be conveniently managed and utilized for multiple platforms and devices. Some security experts, however, criticize that password services are subject to repeated attack. As an alternative, password managers from security software manufacturers can be used.
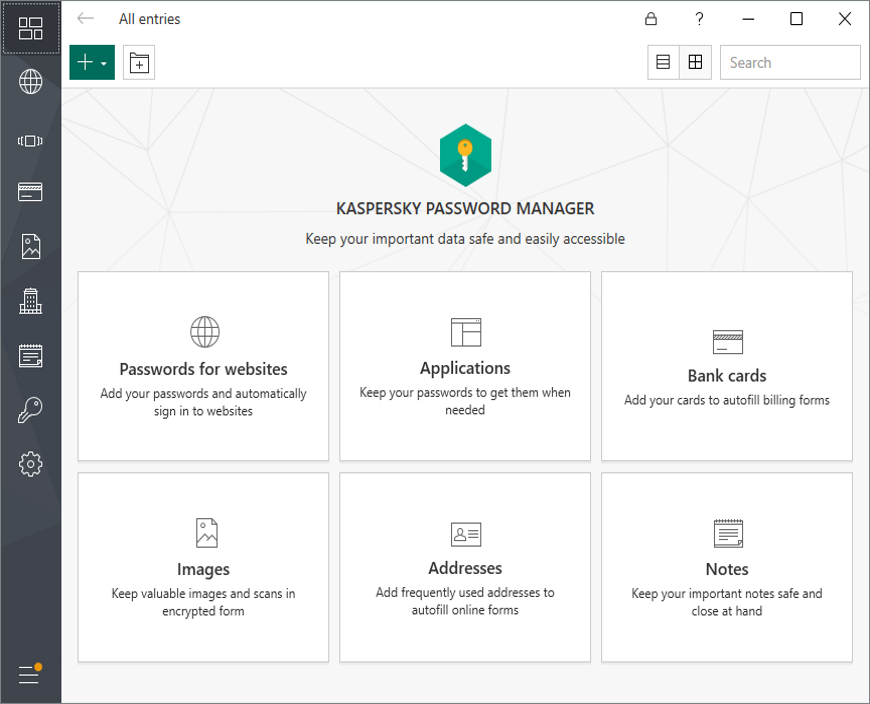
Many Internet security suites include a password manager in their most comprehensive package. Kaspersky or Symantec, for example. Naturally, the manufacturers also offer the password safes as a standalone product. For example, there is the F-Secure Key or McAfee True Key. Also available for use is the Norton Password Manager, relatively new and free of charge. The program is available for Windows, Mac, iOS and Android. Symantec stores the data encrypted in the cloud.
Two-factor authentication for more security
With the help of two-factor authentication, or 2FA for short, you can secure your passwords with a second lock. A user generally logs on to their service with a password and receives additional code query. For the second query, the system usually sends a generated code to a previously defined smartphone. Once the user enters this code, the second lock is also completed and they end up in their service.
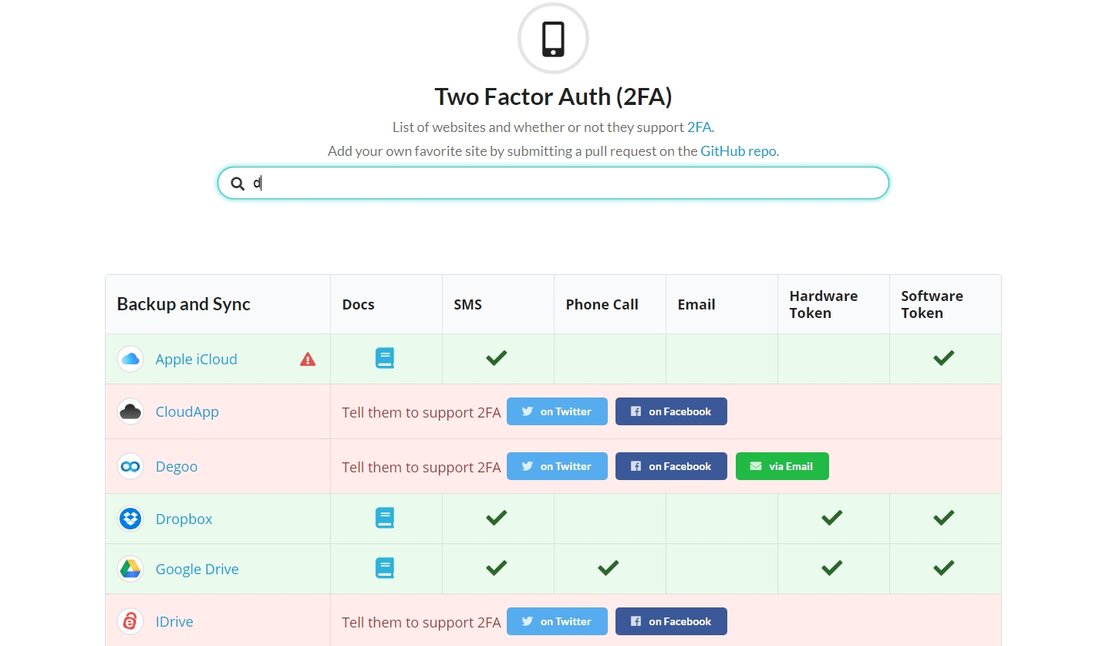
The system has two advantages: the actual password needn't be particularly strong as it is secured by a second device. Thus, in order to gain access, an attacker would have to have the password and the smartphone. Many services now offer two-factor authentication. Unfortunately, the answer to the question "How and where do you activate the 2FA?" is not always easy to find. There is help in this regard at the website, TwoFactorAuth.org, offering an overview of a vast array of Internet services and how you activate the 2FA feature in them. Where available, each service includes a reference to the documentation and how to activate the 2FA function: by SMS, phone call, e-mail, as well as hardware and software tokens.
Two-factor authentication offers better protection

Maik Morgenstern
CTO AV-TEST GmbH
As already explained in the article, extended protection with two-factor authentication (2FA) is a good feature.
However, users should not use only one device – such as their smartphone – for access and as the second factor. This in turn reduces security, as a breached smartphone can open all doors. It is better to use a combination of smartphone and a PC or tablet. With 2FA, a new device normally has to be registered only once with both factors. Dropbox, for example, remembers the device and its hardware ID. For accounts involving money or money transfers, for example, 2FA is always used for login. If you log on to a tablet, for example, a text message with an additional code is typically sent to the smartphone.
For some bank or trader accounts, the account for 2FA use must absolutely be confirmed with an authenticator app. The Google Authenticator app is often recommended for this. The app is designed for easy handling. A new account is simply created in the app. The provider then usually displays a QR code that transfers all further settings. Later, the app displays a 6-digit numeric code that changes every 30 seconds. This code must then be additionally entered within the time allotted for a successful login. A word of caution: the Google Authenticator details are only stored in the smartphone and not in the Google account. If the smartphone has a fault or is lost, the keys can no longer be used! If you use the Google Authenticator (or any other Authenticator app) for 2FA within a service, you will always see a series of emergency codes. These can be used as a substitute to gain access to your account. These emergency codes should always be kept securely in a password safe!