Latest News
June 29, 2021 | More tests
Secure Gateways for Corporate Users
Every data stream in or out of a company always flows through a gateway. The AV-TEST lab tests the security of gateways in the form of cloud solutions, VMs or even as hardware appliances, awarding them test certificates. This enables sales and product managers to achieve greater market acceptance for their gateway solutions.
A gateway plays a key role in the seamless protection of a corporate network. All data traffic, above all, anything involving "IP", seeking to exit or enter the network, is required to pass through this checkpoint. As a gateway is one of the most vital security elements, due to its exposed role, it ought to be capable of providing comprehensive protection to corporate users. In doing so, all incoming and outgoing connections and data flows have to be examined and evaluated, and appropriate measures have to be taken. Gateways are also essential in the implementation of security policies.
A wide field of manufacturers and solutions
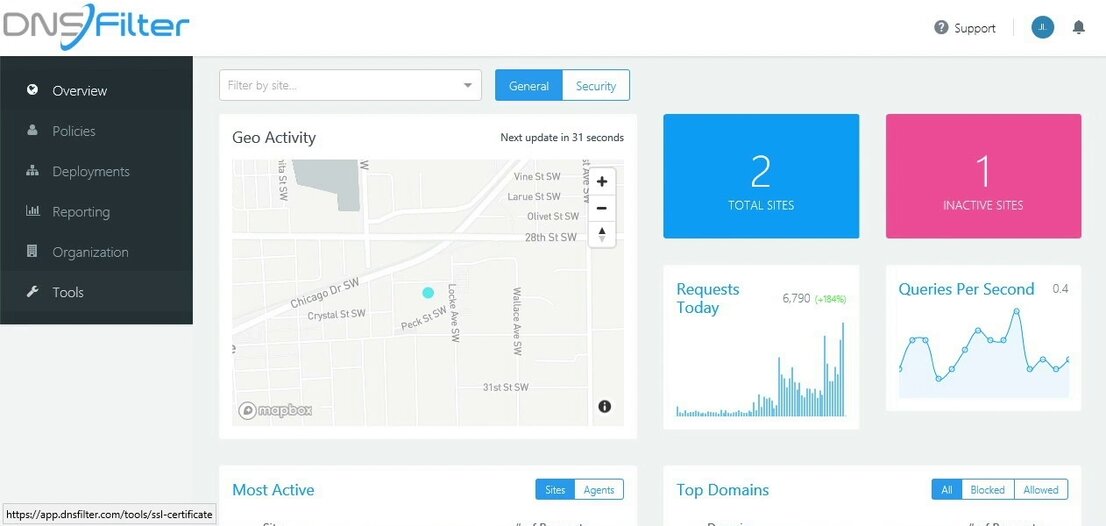
There are a vast number of manufacturers in the market, offering their solutions. Going by market researchers Gartner or Forrester and their surveys over the past few years, these are the companies competing in the market: Allot, Akamai, Barracuda, Broadcom (Symantec), Cisco, Content Keeper, DNSFilter, Forcepoint, Iboss, Infoblox, Kaspersky, McAfee, Menio Security, Netskope, Palo Alto, QI-Anxin Technology Group, Sangfor Technologies, Sophos, Trend Micro, Zscaler. This list of manufacturers is naturally not complete. It provides only a small overview of the market.

Validated security in gateways
The lab certifies the security of Secure Web Gateways (SWG) and Secure DNS
Secure Web, DNS, cloud or Internet gateway after all?
Unfortunately, it is not always easy for companies to comprehend which gateway is right for which tasks. After all, even experts are continuously confronted with a potpourri of terminology in the product portfolios of the manufacturers. The Secure Internet Gateway (SIG) is often listed, but it consists of three gateway elements: the Secure Web Gateway (SWG), the Secure DNS and the Cloud Access Security Broker (CASB). In addition, while SIGs are desired, they do not exist as a direct product, but only as a composite solution. CASB does not serve as a gateway either, rather it implements security policies between users and cloud applications, monitoring, managing and logging all actions.
Thus, gateways offered in the market for corporate networks almost always involve the Secure Web Gateway (SWG) and Secure DNS. The manufacturers mostly offer cloud solutions, virtual machines and in some cases solutions provided by hardware appliances. That is why the lab at AV-TEST focuses on testing and certifying these two product groups, which is extremely important for sales and quality assurance of the manufacturers.
Secure Web Gateway (SWG) and Secure DNS
The tasks and functions of Secure DNS can be explained in relatively easy terms. The DNS reputation query is one of the first security elements, and already fends off many attacks. Because Secure DNS checks whether a domain is legitimate or not, many hacking attempts are already detected and blocked when the connection is being established.
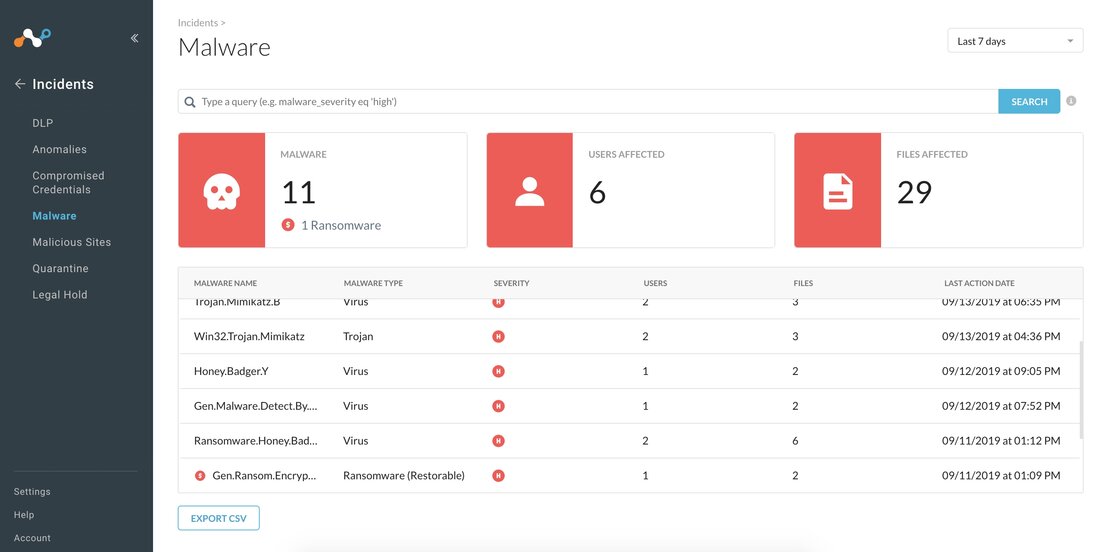
The tasks of a Secure Web Gateway (SWG), which has the DNS part already integrated, are much more comprehensive: URL filtering, real-time traffic evaluation, application control, data leak prevention, antivirus and anti-malware protection, control of encrypted traffic, network and messenger control, as well as botnet detection. E-mail security is frequently mentioned in this context, whereby this is mostly offered in separate e-mail gateways.
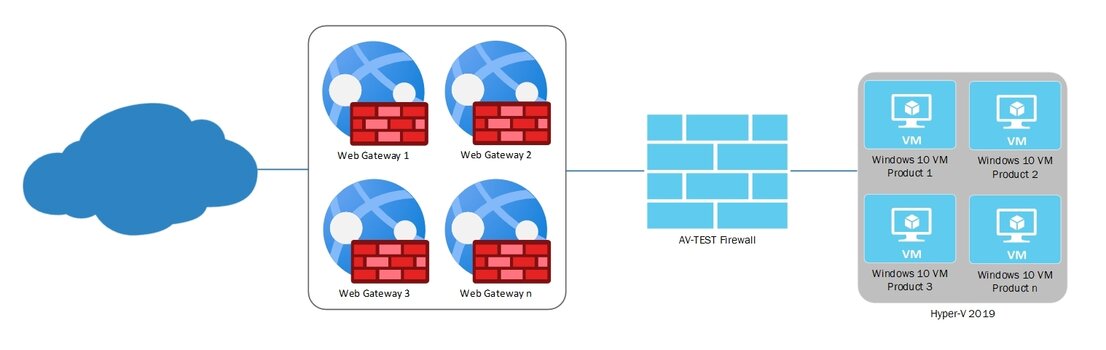
Test structure and methodology of the lab
All solutions evaluated by the lab at AV-TEST are subject to a pre-determined test methodology. The first test section, protection on the DNS level, is naturally used to test both product groups. In the process, the infrastructure of the Internet is utilized on the DNS level to block malicious and unwanted domains and cloud applications even before a connection is established within the scope of recursive DNS resolution. During protection on the DNS level, malware is thwarted at an early stage. Callbacks to attackers are also prevented when infected systems connect to the network.
During protection on the DNS level with a selective cloud proxy, only risky domain queries are redirected for more in-depth inspection of the web content. This occurs transparently via the DNS answer.
As web gateways have other tasks as well, the test goes further: A secure web gateway requires a full web proxy that will detect and verify all web connections. Unlike DNS-level protection, which only analyzes domain names and IP addresses, a web proxy sees all files, along with the complete URLs. This enables a more detailed examination and validation.
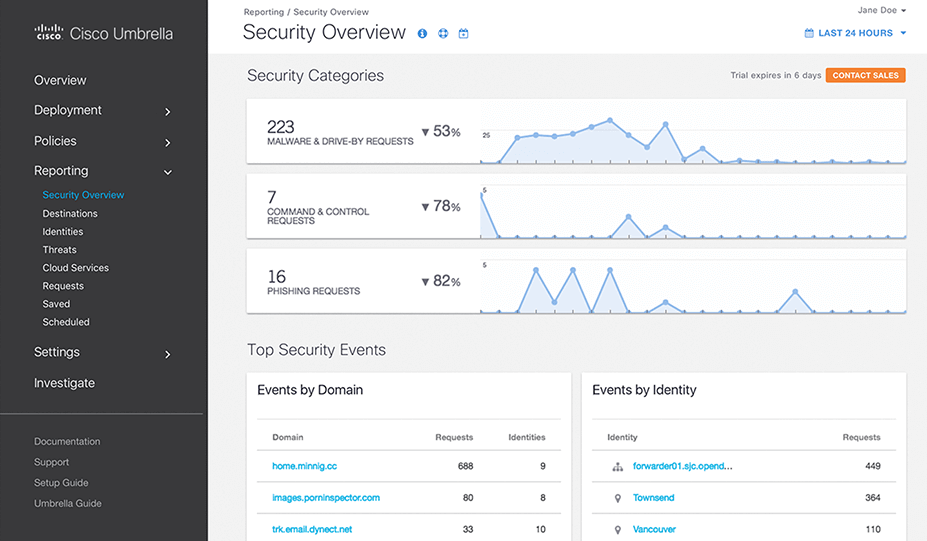
Cisco Umbrella Secure Web Gateway
An example of a SWG: The cloud-based Cisco solution scans all web traffic, offering antivirus and advanced malware protection, sandboxing, decryption, content control, and granular app activity controls
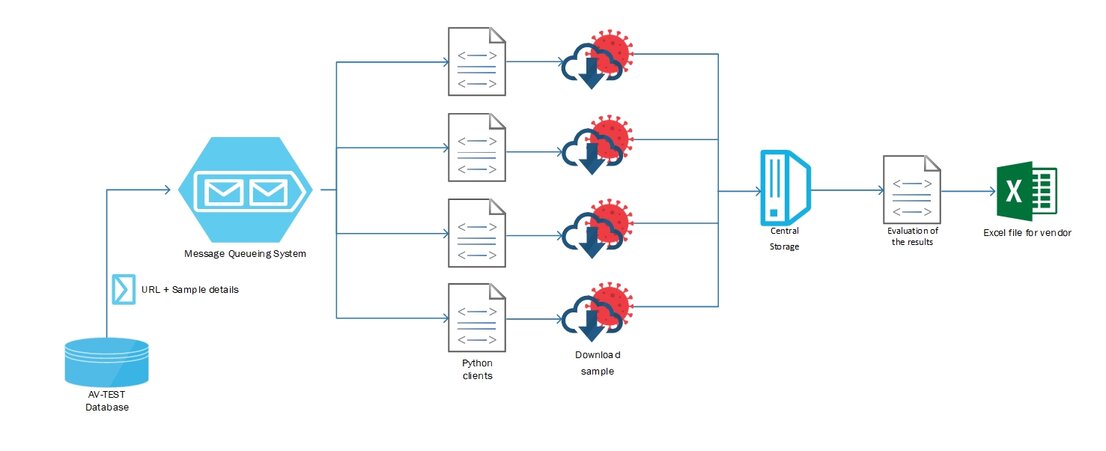
Only new and actual test cases in the DNS test
For a real-life test evaluation of Secure DNS solutions and Secure Web Gateways (SWG) in the DNS test area, the lab always uses only the latest samples, URLs and metadata. The lab constantly collects them with the aid of honeypots on websites or from e-mails.
Prior to a test, the lab analyzes all the samples to confirm whether they involve malware websites or phishing links. AV-TEST performs both static and dynamic analyses on samples to make sure that the domains are actively hosting malicious content at the time of testing and that they are exhibiting malicious behavior. The following are examined in the test:
- URLs referring to malicious PE files (portable executable files for Windows, .exe files)
- URLs with other malicious targets (non-PE files, typically HTML or PHP websites, including links to scripts such as JavaScript or VBS)
- Links to phishing websites
For reliable test findings, the lab normally harnesses several thousand test cases in each tested category.
Test structure for Secure Web Gateways
As the tasks and capabilities of a Secure Web Gateway (SWG) are more extensive, AV-TEST usually also tests their detection performance as soon as malware is downloaded. Also in the area of malware testing, the laboratory accesses its own, constantly updated malware databases and samples. Entire malware families can also be fed into the solutions to be tested, thus allowing for precise determination of their detection and protection performance.
Moreover, an enhanced check is run on URLs (including those IP-based), as well as a comprehensive false positive test (false alarms) during access of innocuous files, software and websites. In testing for false positives in software, the lab has been collecting files from the Internet and applications for many years, classifying them and adding them to a database. This constantly revised file inventory of innocuous files and their hash values has already grown to a few million samples and counting.
A similar approach is used in the false positive check when visiting websites. The lab maintains a constantly updated top URL list of thousands of harmless websites that are included in the testing.
If a manufacturer has additional wish lists in terms of the scope of testing, these can also be implemented, e.g. access to C2 domains or the launching of live malware on a client behind the tested gateway product.