Latest News
September 22, 2016 | Research
Data Protection or Virus Protection?
How many private users read long and drawn-out privacy policies when buying or installing software anyway? Especially when it comes to security software. After all, these programs promise not only protection from cyberattacks but also greater privacy. The data experts of AV-TEST fought their way through the thicket of privacy policies. The analysis raises doubts as to whether users' unquestioning faith is justified.
Comprehensive protection requires comprehensive access
All manufacturers of security packages essentially promote their products among prospective consumers with slogans such as "protect your data and privacy" or "protect your identity". Given the current online threat scenario, Internet Security suites have evolved from pure virus protection with firewalls to complete protection solutions. It's no longer simply about defending computers and data against malware attacks and hacker threats. In the crosshairs of a wide range of attackers are also online accounts and social media profiles administered via PCs, tablets and smartphones, which need to be safeguarded against phishing attempts. What's more, advertising firms are pursuing Internet users ever more aggressively via tracking software, which secretly spies on surfing and user behavior as well as device configuration and other sensitive data (PUA).
That's why a good security application these days has to not only defend against threats but also prevent the unwanted outflow of sensitive data. In order to fulfill all these functions, security software requires comprehensive access to the system being protected – and thus to the personal data of its users. In light of the palpable threat, users likewise have no other option than to allow far-reaching insights into systems and stored data, putting their faith in the pledge of software companies to protect them. However, this should only occur under the assumption that these access rights will be used solely to detect and thwart possible threats.

Many manufacturers reserve the right to share customer data with other companies
Few if any communicate this as openly as McAfee (Intel Security).
Excessively long sentences, overly complicated choice of words
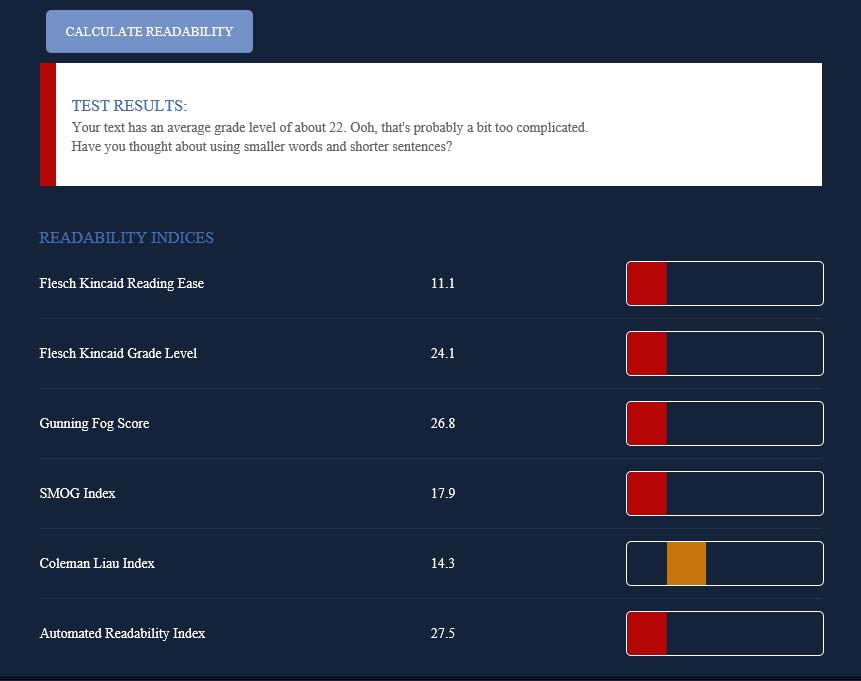
Readability tests such as the Readability Test Tool from webpagefx.com demonstrate that many privacy policies can hardly be understood by normal consumers. (Source: www.webpagefx.com/tools/read-able/)
For quite some time now, the IAPP has been calling for understandable
well-organized and, above all, brief privacy policies. (Source: iapp.org)
More than 50 percent do not care about general terms and conditions
As with any other software, the installation routine of a security application is preceded by the confirmation of general terms and conditions and a privacy policy. Only then can the software be installed and used. From that point on, the security pledge of the selected manufacturer goes into effect. According to a study published in 2014 by the Verbraucherzentrale Bundesverband (vzbv), the Federation of German Consumer Organizations, 53% of those surveyed agreed to general terms and conditions of a software program without even having read them. For software touting features that include the protection of personal data, the number of users clicking on the "accept" button without thinking twice really ought to be much higher. After all, users expect manufacturers to abide by their advertising claims, i.e. to protect their personal data.
26 security programs evaluated
In an elaborate analysis, the AV-TEST Institute evaluated the English-language privacy policies of 26 antivirus programs, thus providing a comprehensive market overview. In reality, only 24 privacy policies were evaluated, as two of the security packages did not include any policy whatsoever, neither on the manufacturers' websites nor during installation of the programs.
The study focused on the question as to what rights the suppliers of protection software presume vis-à-vis their customers in their privacy policy. In particular, the evaluation was made as to
• the type of data to which manufacturers assert a blanket legal claim,
• which rights they proclaim for the use of data,
• which rights they extend to their users, for example, in preventing, restricting or being informing about the collection of data.
In sifting through the many pages of legal statements, the privacy experts distinguished between the types of data collected. Providers demand access to data on the users themselves, for example, the usage behavior on the device being protected, as well as on the device itself. This angle explicitly examines the rights presumed by manufacturers for storing and using data. Determining whether this data is actually collected was not a substantive aim of this examination. These and other questions now require clarification in the following discussions with manufacturers.
Far more data collected than necessary
In almost every privacy policy examined, the manufacturers presume a vast number of access rights to data that should not be necessary for using a security software application. Instead, according to manufacturers' statements, they serve the purpose of product optimization, the marketing of products of the manufacturers or partner companies. Because each of the providers examined reserves the right per privacy policy to disclose recorded data to third parties.
In most cases, the nature of the data collected on users themselves includes the name, email address and buying or payment details, for example. Also of interest for manufacturers are additional contact details, including telephone numbers. These details are surely of interest in order to introduce additional products to the user, but they are hardly necessary for using the programs. Among other things, this proves it is not a given that this data is collected by all manufacturers.
Sexual preferences and fingerprints collected
Many providers, however, overshoot the mark by far: In examinations conducted by AV-TEST, manufacturers even allowed themselves access to biometric data stored on the user computer. Upon evaluating the programs, testers were at a loss to see why an antivirus program requires digital fingerprints. How information on the user's gender, occupation, as well as race and sexual orientation are intended to help in hunting down malware is probably difficult to explain, even for the resourceful marketing experts of manufacturers seeking access to this information.
Users under observation
Also in terms of recording user behavior, manufacturers tend to generously help themselves to data: 15 out of 24 manufacturers require access to the browser history of their users. Six want access to their search queries. Five providers reserve the right to sift through emails. No less than two reserve the right to full access to the personal address book. Furthermore, antivirus manufacturers are interested in social media data of their customers, including account data, as well as postings. One manufacturer even claimed the right to publish entries on behalf of users. Some also want to be involved in chat sessions, or even have access to the chat history.
Full device control
The easiest explanation for the massive data collection by manufacturers surely involves the information on the device to be protected and the applications running on that device. After all, this is precisely the area in which malware programs, disguised as normal applications, should be prevented from wreaking their havoc. That is why the collection of basic data such as IP address, device ID, operating system and installed software appear plausible, even if by far not all manufacturers demand access to such device facts in their privacy policies. The detection of GPS coordinates (5 out of 24 manufacturers) as well as WLAN positioning (4 out of 24 manufacturers) can be explained by functions for locating lost or stolen devices. However, users should also be aware that they pay extra for this device protection with the traceability of their own movement patterns.
In 10 out of 24 privacy policies, manufacturers reserve the right to compile "user statistics". It is not clearly defined, however, which data is collected here, i.e. whether it involves the use of the security program itself, use of the device or the collection of entirely different data. In this area, as well as in many other points, the specifications of privacy policies of all manufacturers are extremely vague.
Data protection requires clear understanding and transparency
The fact that hardly anyone reads general terms and conditions and privacy policies is not surprising. On the one hand, users are overwhelmed by the sheer volume of pages. In the course of this examination, an average privacy policy was 12 pages long. What's more, there is the appearance that manufacturers often do not want to be understood.
An additional readability test performed on the texts using proper analysis programs showed that many privacy policies were too complex. In other words: The policies were barely comprehensible for normal users. Long sentences and lots of technical terms make it even more difficult to understand what are already very long texts.
In addition, most manufacturers remain ambiguous in terms of important questions concerning the nature and duration of data storage. Where and how long is data stored? Is it encrypted, and if so, how? What data is disclosed to third parties, and what kind of partners of the manufacturers does this involve? Many manufacturers of security products failed to provide a satisfactory answer to all these questions in their privacy policies.
Less is more
In general, a word of advice to manufacturers can only be to author privacy policies that are shorter and more understandable. This is something the US-based International Association of Privacy Professionals, or IAPP for short has been demanding for some time now. In Germany as well, the Federal Ministry of Justice and Consumer Protection weighed in on this issue last year during the scope of the National IT Summit. Since its presentation in November, the Ministry has offered an appropriate sample template for such a compact and easy-to-comprehend privacy policy on its website.
Moreover, manufacturers of security programs that promise to protect the privacy of their users in cases where customer data is queried and stored can promote themselves through their own economy of data. On the one hand, the basic concept of data avoidance obviously goes hand in hand with the basic principle of the right to data protection. On the other hand, manufacturers could even promote the fact that they collect as few personal details as possible.
Less data, more protection

Anett Hoppe
IT Security Expert at AV-TEST
Most providers of security programs enjoy the trust of their customers and have substantial access to their systems and data. Anett Hoppe, IT Security Expert at AV-TEST, thinks they should honor this leap of faith through clear privacy policies: Many users assume that antivirus software not only defends the security of the user, but also protects privacy. Is that true?
Many users assume that antivirus software not only defends the security of the user, but also protects privacy. Is that true?
There have been no studies on this topic up to now. And we at AV-TEST do indeed receive regular inquiries by users who are confused concerning potentially suspicious emails or dubious functions of programs. By contrast, we receive inquiries into the handling of user data by the manufacturers of protection software and services mostly from companies and public agencies. Yet increasingly, some critical private users also ask who is attempting to do what with their data. In this light, the manufacturers of protection programs for consumers continue to benefit from their customers' vast leap of faith – which in some cases is unjustified, as our study indicates.
What data is recorded, and what happens to it?
Some of the recorded data is necessary in order for a protection program to do its job. By contrast, the relevance of gender and birth date for the functionality of an antivirus software program is something that even resourceful manufacturers may find difficult to explain. It is important to distinguish between data that a manufacturer wants to access according to the privacy policy and the data which the manufacturer actually records. Our study illuminates the rights presumed by manufacturers towards their customers.
What phraseology in the privacy policy should I pay attention to, and which criteria can I use as a guide?
First of all, it is recommended to bear data protection issues in mind when registering and configuring the product. This begins with the user's personal details during installation – often enough, not all the fields on the registration form are required and are only completed out of habit. Moreover, users should at least quickly peruse the privacy policy. Only by knowing these terms can the user determine whether an address book or private photos really should be uploaded onto a manufacturer's server.